好的,我现在需要帮用户总结这篇文章的内容。用户的要求是用中文,控制在100字以内,不需要特定的开头,直接写描述。 首先,我通读了整篇文章。文章主要讲的是Bitrefill遭受网络攻击的情况。Bitrefill是一家使用加密货币支付的礼品卡商店,他们遭受了来自朝鲜黑客组织Bluenoroff的攻击。攻击导致部分服务中断,暴露了用户的购买记录和一些敏感信息。 接下来,我需要提取关键信息:Bitrefill是什么?遭受了什么攻击?攻击者是谁?影响是什么?以及应对措施。 然后,我要把这些信息浓缩到100字以内。要注意用词简洁,涵盖主要事件和结果。 可能的结构是:Bitrefill遭受攻击,攻击者是朝鲜Bluenoroff组织,导致服务中断和数据泄露,但损失不大,并采取措施加强安全。 最后,检查字数是否符合要求,并确保内容准确无误。 </think> 加密货币礼品卡平台Bitrefill遭遇网络攻击,初步调查指向朝鲜Bluenoroff黑客组织。攻击导致部分服务中断,约1.85万条用户购买记录外泄。尽管损失较小且已恢复服务,但公司加强了安全措施以防范未来风险。 2026-3-19 17:15:17 Author: www.bleepingcomputer.com(查看原文) 阅读量:13 收藏

Crypto-powered gift card store Bitrefill says that the attack it suffered at the beginning of the month was likely perpetrated by North Korean hackers of the Bluenoroff group.
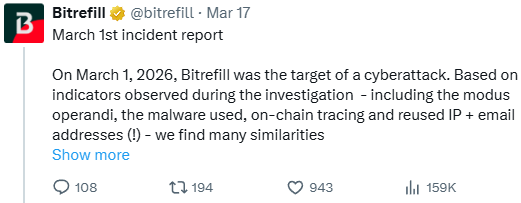
During the investigation, the platform observed indicators similar to previous attacks attributed to the North Korean threat actor, like tactics, malware, IP and email addresses.
“Based on indicators observed during the investigation - including the modus operandi, the malware used, on-chain tracing and reused IP + email addresses (!) - we find many similarities between this attack and past cyberattacks by the DPRK Lazarus / Bluenoroff group against other companies in the crypto industries,” reads Bitrefill's statement.
Bitrefill is a mid-sized e-commerce platform that enables people to pay in cryptocurrency for gift cards at stores in 150 countries. The gift cards can be used to pay for anything from clothing, food and groceries, health and beauty products to bills, services, gas, transportation, and electronics.
The platform supports more than 600 mobile operators and thousands of brands worldwide.
On March 1st, Bitrefill announced technical issues affecting access to its website and app. A day later, the company disclosed that it had identified a security issue and took all services offline.
Although user balances were not affected, the gradual restoration of all services still continues to this day.
The breach was discovered after Bitrefill noticed suspicious supplier purchasing patterns, exploitation of gift card stock and supply lines, and draining of some “hot” wallets.
The investigation the firm launched to determine the cause revealed that the attack originated on a compromised employee's laptop.
The attackers stole legacy credentials and used them to access a snapshot with production secrets, later escalating access to the larger Bitrefill infrastructure, including parts of the database and some cryptocurrency wallets.
About 18,500 purchase records containing customer email addresses, IP addresses, and cryptocurrency payment addresses were exposed in the breach. For 1,000 purchases, customer names were also exposed.
Although this information is stored in encrypted form, Bitrefill notes that the attackers may have obtained the decryption keys.
Bitrefill says this was the most serious cyberattack it has suffered in its ten years of existence, but it survived with minimal losses, which will be covered from its capital.
Ultimately, Bitrefill believes that attackers were after cryptocurrency and gift card inventory, not customer information.
BlueNoroff, also known as APT38, is a cluster of the Lazarus group that has been active since at least 2014. It typically targets financial organizations, with a more recent focus on the cryptocurrency industry, the objective being crypto theft.
Bitrefill says this was the most serious cyberattack it has suffered in the ten years of its existence, but it survived with minimal losses, which will be covered from its capital.
Meanwhile, it is expanding security reviews and pen-testing, tightening access controls, improving logging and monitoring, and refining automated shutdown mechanisms.
At this time, most of its services have returned to normal operational status, and customers aren’t required to take any action beyond treating incoming communications with extra caution.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh