好的,我现在需要帮用户总结一篇文章,控制在100字以内。用户的要求很明确,直接写文章描述,不需要开头语。首先,我得仔细阅读文章内容,抓住主要信息。 文章主要讲的是DarkSword这个新的iOS漏洞工具包,被多个威胁行为者用于窃取数据,目标国家包括沙特、土耳其、马来西亚和乌克兰。它利用了六个漏洞,其中三个是零日漏洞,能够完全控制设备。DarkSword针对的是运行iOS 18.4到18.7的设备,被怀疑与俄罗斯有关的组织UNC6353用于攻击乌克兰目标。攻击手法是快速窃取数据后清理痕迹。 接下来,我需要把这些关键点浓缩到100字以内。要确保包含DarkSword的用途、目标国家、使用的漏洞数量、影响的iOS版本以及攻击手法和背后的组织。 可能的结构是:DarkSword是一种新的iOS工具包,被用于窃取数据,针对特定国家的设备,利用多个漏洞实现完全控制,并且采用快速攻击和清理的方法。背后有俄罗斯关联的组织 UNC6353 使用。 现在开始组织语言: DarkSword是一种新的iOS漏洞工具包,被多个威胁行为者用于窃取敏感数据。它针对沙特、土耳其等国的iOS 18.4-18.7设备,利用六个漏洞实现完全控制,并迅速窃取数据后清理痕迹。该工具包被怀疑与俄罗斯关联的组织UNC6353用于攻击乌克兰目标。 检查字数是否在100字以内,并确保信息准确无误。 </think> DarkSword是一种新的iOS漏洞工具包,被多个威胁行为者用于窃取敏感数据。它针对沙特、土耳其等国的iOS 18.4-18.7设备,利用六个漏洞实现完全控制,并迅速窃取数据后清理痕迹。该工具包被怀疑与俄罗斯关联的组织UNC6353用于攻击乌克兰目标。 2026-3-19 14:3:36 Author: securityaffairs.com(查看原文) 阅读量:58 收藏
DarkSword emerges as powerful iOS exploit tool in global attacks

DarkSword, a new iOS exploit kit, is used by multiple actors to steal data in campaigns targeting Saudi Arabia, Turkey, Malaysia, and Ukraine.
Lookout Threat Labs discovered a new iOS exploit kit called DarkSword that has been used since late 2025 by multiple threat actors, including surveillance vendors and likely nation-state actors. The toolkit enables full-chain attacks to steal sensitive data from Apple devices and has been observed in campaigns targeting countries such as Saudi Arabia, Turkey, Malaysia, and Ukraine.
The exploit chain relies on six vulnerabilities, three used as zero-days, to achieve full device compromise:
- CVE-2025-31277 – JavaScriptCore memory corruption (CVSS: 8.8)
- CVE-2026-20700 – dyld PAC bypass (CVSS: 8.6) (zero-day)
- CVE-2025-43529 – JavaScriptCore memory corruption (CVSS: 8.8) (zero-day)
- CVE-2025-14174 – ANGLE memory corruption (CVSS: 8.8) (zero-day)
- CVE-2025-43510 – iOS kernel memory issue (CVSS: 8.6)
- CVE-2025-43520 – iOS kernel memory corruption (CVSS: 8.6)
Together, these flaws enable full-chain exploitation and complete control of targeted iOS devices.
DarkSword targets iPhones running iOS 18.4–18.7 and has been used by the suspected Russian-linked group UNC6353 against Ukrainian targets. It allows attackers to steal sensitive data, including credentials and crypto wallet information, then quickly exfiltrates it in a “hit-and-run” approach before cleaning traces.
The exploits appear to be linked to Coruna exploits, DarkSword enables near full device access with minimal user interaction, showing how advanced exploits are now available on a secondary market to a wider range of threat actors.
“DarkSword aims to extract an extensive set of personal information including credentials from the device and specifically targets a plethora of crypto wallet apps, hinting at a financially motivated threat actor.” reads the report published by Lookout. “Notably, DarkSword appears to take a “hit-and-run” approach by collecting and exfiltrating the targeted data from the device within seconds or at most minutes followed by cleanup.”
Researchers investigating Coruna uncovered related infrastructure linked to Russian actor UNC6353, including a similar domain used in attacks on compromised Ukrainian sites, even government ones. Malicious iframes loaded scripts to fingerprint devices and target specific iOS versions. Further analysis revealed a new exploit chain, later named DarkSword, discovered in late 2025 through joint research by Lookout, iVerify, and Google, confirming a distinct and evolving threat.
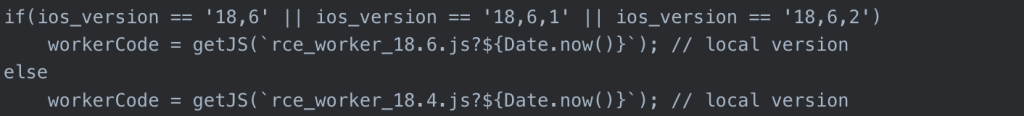
While it initially appeared that this may be another site distributing Coruna, upon closer inspection of the our researchers found that the iframe loads a javascript file called rce_loader.js, which is largely responsible for fingerprinting devices visiting the compromised site in order to determine whether to route the devices to the iOS exploit chain. However, the script was looking for iOS devices with OS versions 18.4 or 18.6.2, which are iOS versions that are not susceptible to the exploit chains used in Coruna.

Recognizing that this was a new threat, our researchers analyzed the code and began capturing all of the stages of the exploits.
“As opposed to many other previously reported cases of sophisticated attacks on mobile devices, DarkSword is not designed for ongoing surveillance.” states the report. “Once it finishes collecting and exfiltrating the targeted data, it deletes the files it created on the filesystem of the device and exits. Its dwell time on the device is likely in the range of minutes, depending on the amount of data it discovers and exfiltrates.”
According to Lookout, the actor behind the exploit, UNC6353, remains a largely unknown group but has used advanced iOS exploit chains in watering hole attacks on Ukrainian websites. Likely well-funded, it appears to rely on third-party or brokered exploits, possibly linked to Russian ecosystems. The group targets both intelligence and financial data, including crypto assets, suggesting dual motives.
Its infrastructure is limited but shows deep access to compromised sites. Poor obfuscation and signs of AI-assisted code suggest limited in-house expertise. Overall, UNC6353 is assessed as a capable yet not highly sophisticated actor, potentially a Russia-aligned proxy blending espionage with cybercrime.
DarkSword shows a troubling trend: advanced iOS exploit chains are being sold on a secondary market, letting even less skilled actors launch powerful attacks. These near zero-click watering hole campaigns are stealthy and bypass user awareness. Once infected, devices face full compromise, with risks to both personal and corporate data, highlighting the urgent need for faster patching and stronger mobile defenses.
“The discovery of DarkSword as the second iOS exploit chain found in the hands of this at least partially financially motivated threat actor reveals a worrying trend.” concludes the report. “There appears to be a secondary market for technically sophisticated exploit chains in which unscrupulous sellers are willing to serve buyers with little or no concerns for how they are going to be used. These groups can then easily customize these kits into malware for their specific purposes, possibly with the help of AI.”
Google GTIG experts found multiple actors using DarkSword since November 2025, and believes other surveillance vendors or threat groups are likely using the exploit chain as well.

“The use of both DarkSword and Coruna by a variety of actors demonstrates the ongoing risk of exploit proliferation across actors of varying geography and motivation.” concludes GTIG.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, DarkSword)
如有侵权请联系:admin#unsafe.sh