好的,我现在需要帮用户总结一篇文章的内容,控制在100个字以内。用户提供的文章详细介绍了几种暴力攻击的类型,包括在线攻击、离线攻击、字典攻击、混合攻击、密码喷射、逆向暴力攻击、凭证填充和彩虹表攻击。 首先,我需要确定文章的核心内容。文章主要讨论了暴力攻击的不同类型及其特点。接下来,我要提取每种攻击的关键点:在线攻击针对运行中的网站,离线攻击则需要访问数据库;字典攻击使用常见密码列表;混合攻击结合字典和随机组合;密码喷射测试单个常见密码在多个账户上;逆向暴力从已知密码开始寻找匹配账户;凭证填充利用被盗凭证尝试登录其他账户;彩虹表用于快速破解哈希密码。 接下来,我需要将这些信息浓缩成一句话,涵盖所有主要类型,并说明它们的差异和目的。要注意语言简洁明了,避免使用复杂的术语。 可能的结构是先总述暴力攻击的类型,然后分别列举几种主要类型,并说明它们的特点和用途。例如:“暴力攻击包括在线和离线两种方式,以及字典、混合、密码喷射、逆向暴力、凭证填充和彩虹表等方法。” 最后,检查字数是否在100字以内,并确保信息准确全面。 </think> 文章介绍了多种暴力破解攻击方式及其特点,包括在线与离线攻击、字典攻击、混合攻击、密码喷射、逆向暴力破解、凭证填充和彩虹表攻击等方法。 2026-3-19 09:15:15 Author: securityboulevard.com(查看原文) 阅读量:3 收藏
What are the different types of brute force attacks?
Brute force attacks come in several forms, each with unique characteristics and methods. Understanding these differences is crucial for effective prevention. Most attacks are credential-based attacks carried out by threat actors seeking financial gain or data theft.
Online vs. offline attacks
Online brute force attacks target a running website or mobile app. They’re convenient because you can send bots to any online website, but they can be quite slow because the hacker needs to wait for the targeted server to respond. Companies also tend to rate-limit their vulnerable endpoints, further slowing such attacks.
Offline brute force attacks are only possible when a hacker has gained access to a database file with encrypted information. Once a hacker gets their hands on such a file, they can try different keys to decrypt the information on their computer instead of on a distant server, which makes offline attacks significantly faster.
Dictionary attacks
Dictionary attacks use a predefined list of common passwords and words to guess the correct password. The hacker’s bots rotate through combinations of dictionary words to guess usernames and passwords. Dictionary attacks work because people frequently use dictionary words in their passwords.
Hybrid attacks
A hybrid brute force attack combines a dictionary attack with a basic brute force attack. When dictionary attempts fail, the attacker switches to systematic character combinations, trying every possible arrangement of letters, numbers, and symbols. This method is particularly effective because it targets both common password patterns and complex combinations.
Password spraying
Password spraying applies a single common password across multiple accounts. Instead of trying many passwords against one account, attackers flip the script—testing commonly used passwords like “Password123!” or “Summer2024” against thousands of usernames. This method stays under the radar by avoiding account lockout policies that trigger after too many failed attempts on a single account.
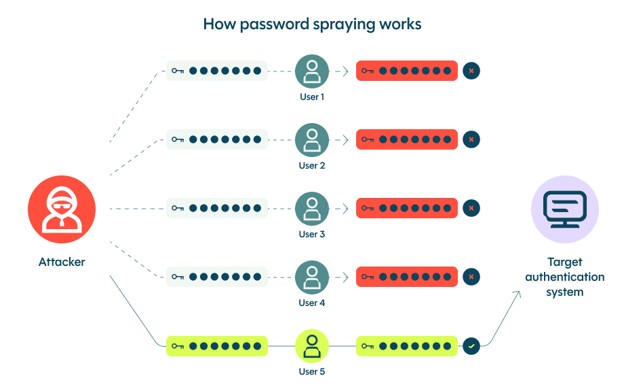
One password tested against many accounts
Reverse brute force attacks
A reverse brute force attack starts from a publicly known or leaked password. With that password, the hacker will use automation to search for a matching username, account number, or key. This method leverages passwords leaked from previous data breaches that can be found online.
Credential stuffing
Many users use the same credentials for multiple accounts.Credential stuffing exploits this by reusing stolen username-password combinations to gain unauthorized access to other accounts. Hackers use automated tools to try these stolen credentials across various websites until they find matches.
Rainbow table attacks
Rainbow tables are precomputed tables containing hash values used to crack passwords. Rainbow table attacks can crack hashes of passwords that have been hashed using various algorithms, including MD5, SHA-1, and NTLM. Attackers can quickly look up the corresponding plaintext for a given hash without the computationally intensive process of hashing all possible plaintexts.
如有侵权请联系:admin#unsafe.sh