好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,理解其主要内容。 文章主要讲的是phpMyAdmin和Adminer这两个工具。phpMyAdmin因为历史上的漏洞问题,常常被攻击者作为目标。而Adminer作为替代品,安全性更好,因为它不需要存储数据库凭证,而是直接使用SQL的认证机制。不过,Adminer也有弱点,比如无法轻松实现双因素认证,攻击者也在积极扫描寻找它的漏洞。 接下来,我需要将这些要点浓缩成一句话。要确保涵盖主要对比点:phpMyAdmin的不安全、Adminer的安全性及其优势和不足。同时,还要提到攻击者对两者的关注。 最后,检查字数是否在限制内,并确保表达清晰简洁。 </think> 文章对比了phpMyAdmin和Adminer两款数据库管理工具的安全性。phpMyAdmin因历史漏洞频遭攻击,而Adminer以单文件、无配置和更好的安全记录著称。它通过直接使用SQL认证避免存储密码,但易受暴力破解攻击,并缺乏双因素认证支持。近期攻击者对两者的扫描活动均有所增加。 2026-3-18 13:18:24 Author: isc.sans.edu(查看原文) 阅读量:15 收藏
A very popular target of attackers scanning our honeypots is "phpmyadmin". phpMyAdmin is a script first released in the late 90s, before many security concepts had been discovered. It's rich history of vulnerabilities made it a favorite target. Its alternative, "adminer", began appearing about a decade later (https://www.adminer.org). One of its main "selling" points was simplicity. Adminer is just a single PHP file. It requires no configuration. Copy it to your server, and you are ready to go. "adminer" has a much better security record and claims to prioritize security in its development.
So how does it deal with configurations for database connection parameters? The simple answer: It does not. Instead of using its own authentication or access control, Adminer simply asks the user to enter the SQL username and password they want to use to connect to the database. This is certainly not a terrible idea. Let the database deal with it! SQL databases have robust access controls, so there is no need to reinvent the wheel. Not having to store database credentials in a secrets file also removes several security headaches.
But... these credentials are, of course, still subject to brute-forcing. Adminer thought about that, and only allows 30 login attempts in 30 minutes. One may argue that this is "generous", but they thought about it. The main weakness likely represents users using weak passwords and relying on SQL authentication; there is no easy way to implement two-factor authentication. Adminer mitigates some of these issues with security plugins that implement OTP protection and other security features.
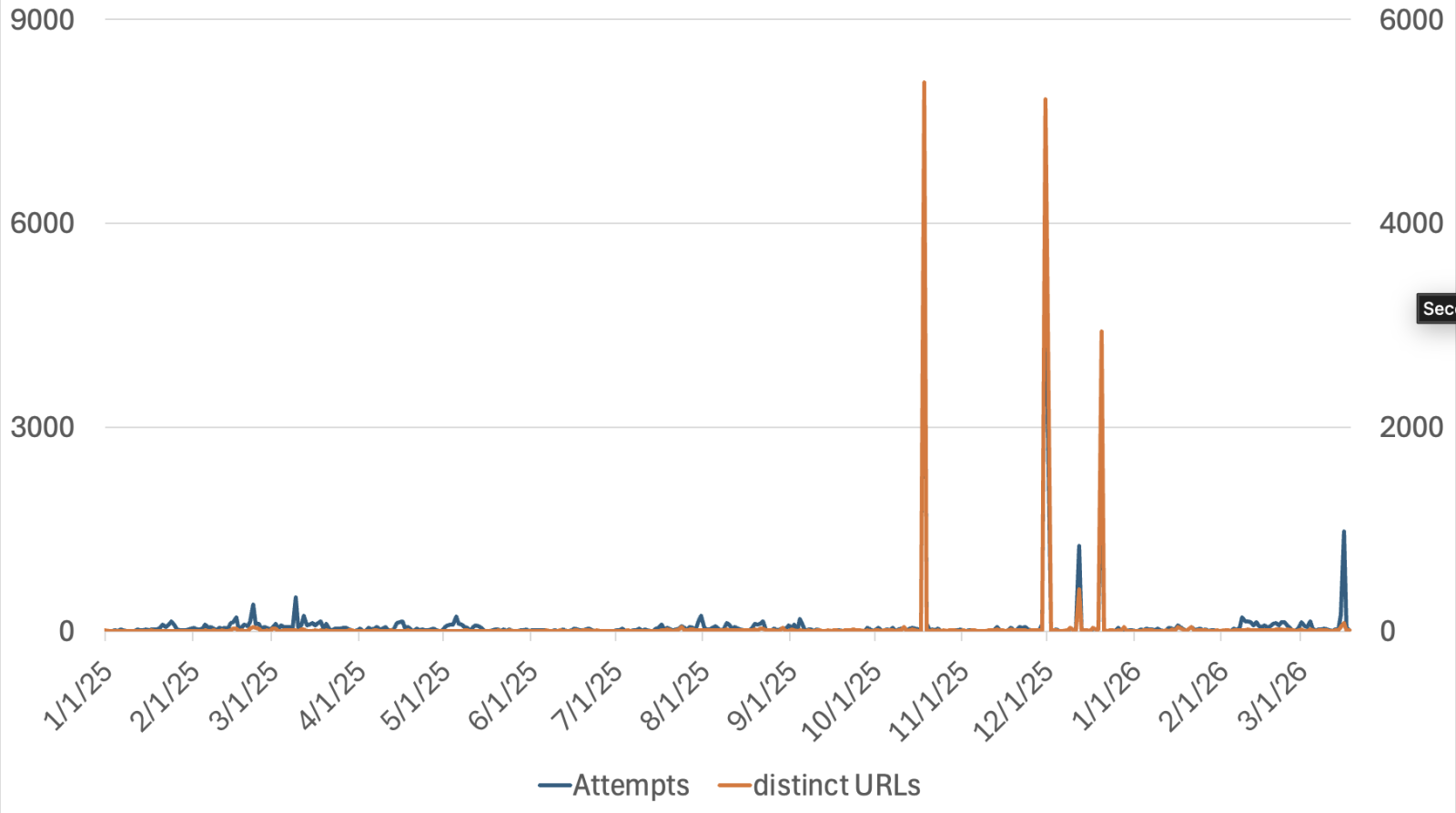
This likely explains why attackers are scanning for it, and they have been scanning quite aggressively lately:
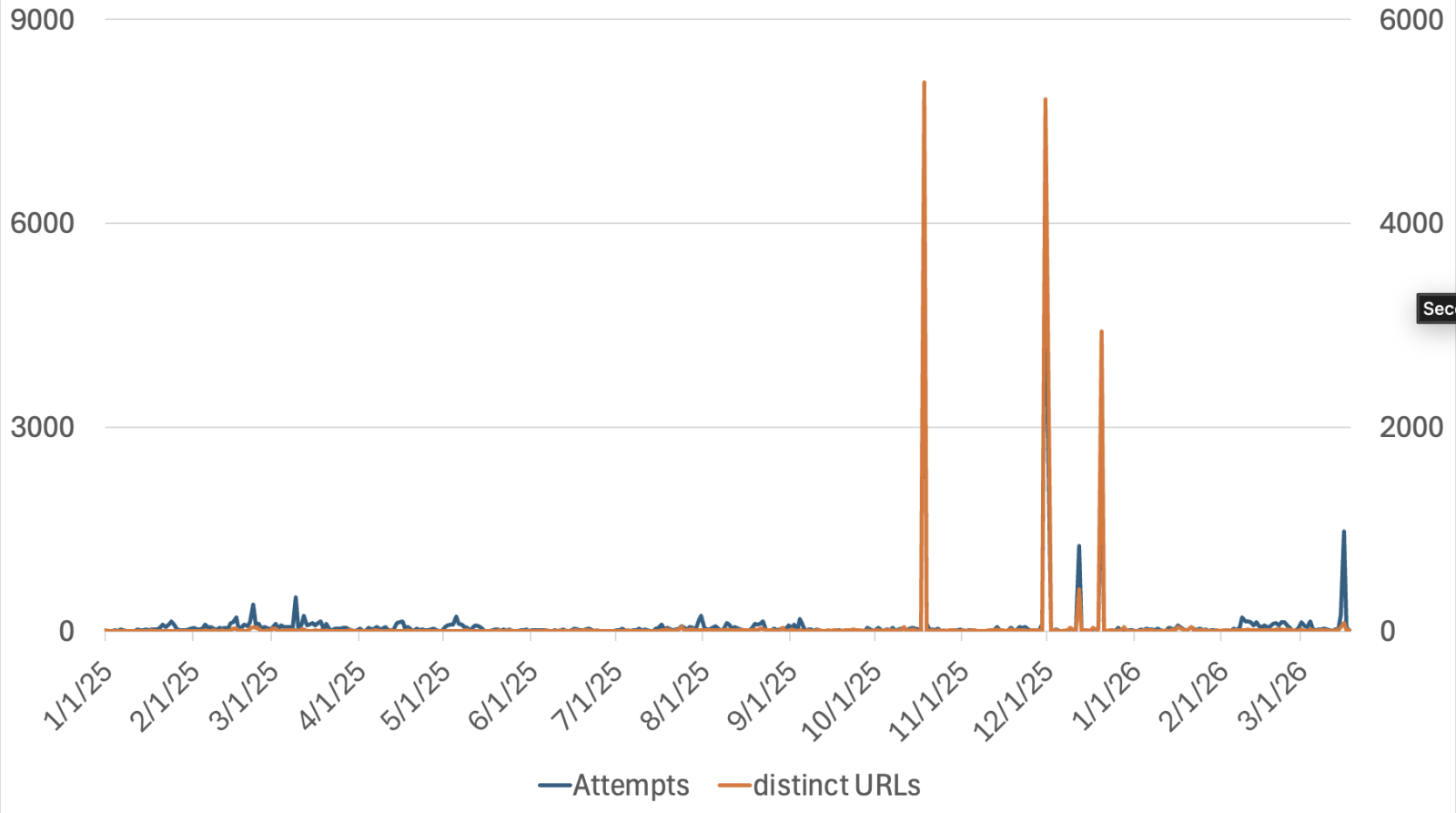
The increase in the number of URLs scanned is noteworthy. In phpMyAdmin scans, attackers often attempt to find obfuscated URLs used to host phpMyAdmin, such as "/pma/". For Adminer, attackers are scanning for different versions of the file. The filename released by Adminer includes the version number and the language or database type. For example, "adminer-5.4.2-mysql-en.php" is the English version for MySQL.
In short: Do not forget to read the security advice provided by Adminer, and you probably do not want to open Adminer to the internet.
--
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|
如有侵权请联系:admin#unsafe.sh