嗯,用户让我用中文总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我得仔细阅读这篇文章,理解主要内容。 文章讲的是ClickFix攻击活动转向macOS用户,并且使用基于ChatGPT的诱饵。Sophos的研究人员分析了三个针对macOS用户的活动,使用了MacSync信息窃取器。攻击者最初使用经典方法,后来利用ChatGPT对话和GitHub主题页面来提升攻击效果,并引入了复杂的跟踪基础设施。最终,攻击变得更加模块化、隐蔽和数据导向。 接下来,我需要将这些要点浓缩到100字以内。要确保涵盖攻击目标、使用的工具、战术变化以及结果。同时,语言要简洁明了。 可能会这样组织:ClickFix攻击针对macOS用户,使用ChatGPT诱饵和MacSync窃取器。战术从经典方法转向利用GitHub页面和多阶段加载器,提升隐蔽性。结果导致大量数据泄露和加密货币资产被盗。 最后检查字数是否在限制内,并确保信息准确传达。 </think> ClickFix攻击针对macOS用户,利用基于ChatGPT的诱饵和MacSync信息窃取器展开攻击。攻击者通过伪造OpenAI页面、ChatGPT对话和GitHub安装界面诱导用户执行恶意命令,逐步提升攻击隐蔽性和复杂性。最终导致大量数据泄露及加密货币资产被盗。 2026-3-17 09:19:49 Author: securityaffairs.com(查看原文) 阅读量:17 收藏
From Windows to macOS: ClickFix attacks shift tactics with ChatGPT-based lures

ClickFix campaigns are evolving, with attackers increasingly targeting macOS users and deploying more advanced infostealers, according to Sophos researchers.
ClickFix is a growing social engineering technique that tricks users into manually executing malicious commands, bypassing traditional protections. Once mainly targeting Windows, it is now increasingly affecting macOS, with recent campaigns deploying infostealers like AMOS and MacSync. Researchers note the evolving tactics, likely driven by both defensive measures and broader tech trends.
Sophos researchers analyzed three ClickFix campaigns targeting macOS users with the MacSync infostealer.
In November 2025, attackers relied on relatively “classic” ClickFix techniques. Victims searching for ChatGPT-related tools were lured via malicious Google-sponsored links leading to fake OpenAI/ChatGPT pages. These pages instructed users to copy and execute obfuscated Terminal commands, which ultimately downloaded and ran the MacSync infostealer. The approach was straightforward but effective, relying heavily on user trust and deception.
“Note the terminal command above, which when deobfuscated, downloads and executes a Bash script from a threat actor-controlled site:” reads the report published by Sophos. “The script requests the user’s password, then fetches and runs a malicious MachO binary (the MacSync infostealer) with user-level permissions”
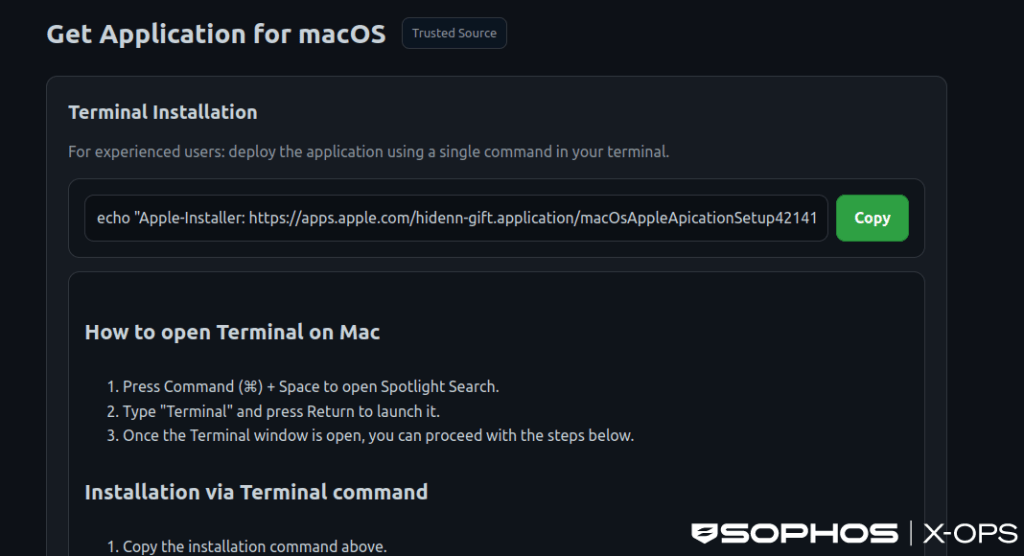
By December 2025, the campaigns became notably more advanced in their delivery and evasion tactics. Instead of redirecting users directly to fake download sites, attackers leveraged legitimate ChatGPT shared conversations to build credibility. These pages then led to GitHub-themed fake interfaces that mimicked legitimate installation workflows, encouraging users to run malicious commands. This technique helped bypass macOS protections like Gatekeeper and XProtect.
“The ChatGPT conversations appeared to be helpful guides like ‘how to clean up your Mac’ or install tools, but redirected victims to malicious GitHub-themed landing pages, which in turn used fake GitHub-themed installation interfaces to trick users into running malicious terminal commands (the ClickFix portion of the attack chain).” continues the report. “This can have the effect of bypassing macOS security controls like Gatekeeper and XProtect.”

At the same time, attackers introduced sophisticated tracking infrastructure, including JavaScript-based analytics, IP and geolocation logging, and real-time reporting via Telegram bots. This allowed them to monitor campaign effectiveness, which reached tens of thousands of user interactions across multiple domains.
By February 2026, the operation had evolved into a far more advanced and stealthy threat. While still relying on user interaction at the initial stage, the payload delivery shifted to a multi-stage, loader-as-a-service model. Instead of simple binaries, the malware used obfuscated shell scripts, API key-protected command-and-control infrastructure, and dynamic AppleScript payloads executed in memory. These enhancements significantly improved evasion against static and behavioral detection.
The latest MacSync variant performs extensive data harvesting, targeting browser data, credentials, files, SSH keys, cloud configurations, and cryptocurrency wallets. It also includes advanced capabilities such as chunked data exfiltration, persistence mechanisms, and anti-analysis techniques. Notably, it can tamper with Ledger wallet applications by injecting malicious code to steal seed phrases, enabling attackers to directly compromise cryptocurrency assets.
Overall, these campaigns highlight a shift from relatively simple social engineering attacks to highly modular, stealthy, and data-focused operations, reflecting both adaptation to defensive measures and increasing attacker sophistication.
“These three campaigns demonstrate a variety of tactics, and some changes to the traditional ClickFix model. While all three campaigns leveraged the use of GenAI-related lures in some way, a shift from malicious sites impersonating known legitimate companies to shared ChatGPT conversations represents an interesting shift in social engineering.” concludes the report. “Here, the threat actor leveraged two things which may have worked in their favor: hosting malicious content on a trusted domain (something the first campaign also utilized), and exploiting the relative novelty of ChatGPT conversations.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, ClickFix)
如有侵权请联系:admin#unsafe.sh
