嗯,用户让我帮忙总结一下这篇文章的内容,控制在100字以内,而且不需要用“文章内容总结”或者“这篇文章”这样的开头,直接写描述。好的,首先我需要仔细阅读文章,抓住主要信息。 文章讲的是Stryker公司遭受了一次网络攻击,攻击者利用微软的环境远程擦除了数万台员工设备,而且没有使用恶意软件。攻击者声称是Handala组织,他们还窃取了大量数据。Stryker确认医疗设备未受影响,但订单系统仍离线。调查由微软团队和Palo Alto支持。 接下来,我需要把这些信息浓缩到100字以内。关键点包括:Stryker被攻击、利用微软环境、擦除设备、无恶意软件、Handala声称责任、窃取数据、医疗设备安全、订单系统离线。 可能的结构:Stryker遭遇网络攻击,利用微软环境远程擦除设备,无恶意软件。Handala声称负责并窃取数据。医疗设备未受影响,但订单系统离线。 检查字数是否在限制内,并确保所有关键点都涵盖。 </think> Stryker遭遇网络攻击,攻击者利用其微软环境远程擦除数万台员工设备,未使用恶意软件。Handala组织声称对此负责,并窃取大量数据。Stryker确认医疗设备未受影响,但电子订单系统仍离线。 2026-3-17 08:5:55 Author: securityaffairs.com(查看原文) 阅读量:20 收藏
Attack on Stryker’s Microsoft environment wiped employee devices without malware

The recent cyberattack on Stryker wiped tens of thousands of employee devices through its Microsoft environment, and systems are still offline.
A recent cyberattack on medical technology giant Stryker targeted its internal Microsoft environment and remotely wiped tens of thousands of employee devices without using malware. The company confirmed that its medical devices were not affected and remain safe to use. However, electronic ordering systems are still offline, forcing customers to place orders manually through sales representatives.
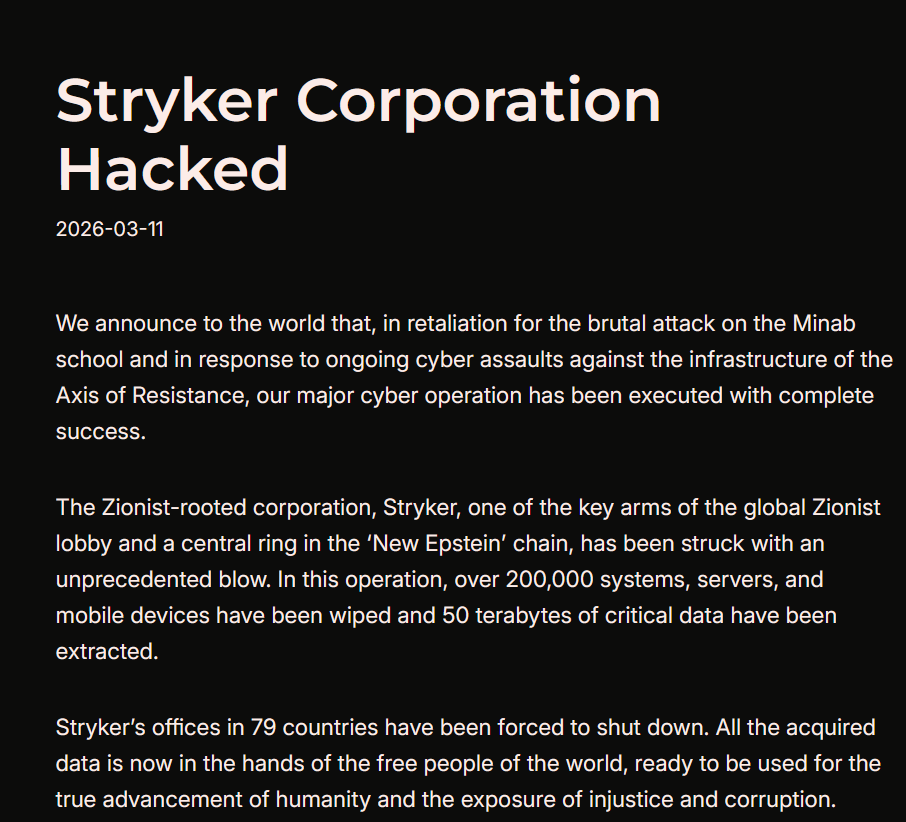
Last week, Pro-Palestinian hacktivist group Handala claimed responsibility for a disruptive cyberattack against medical technology firm Stryker.
The group claimed it wiped more than 200,000 servers, mobile devices, and other systems, forcing the company to shut down offices across 79 countries. The hacktivists also claimed they exfiltrated about 50TB of corporate data from the company’s infrastructure.
Handala appears as a pro-Palestinian hacktivist group but is widely seen as a front for Iran-backed Void Manticore, as reported by SecurityWeek. Known for phishing, data theft, extortion, and destructive wiper attacks, they also engage in info operations and psychological warfare. Since the Iran conflict began, they’ve targeted Israeli military servers, intelligence officers, and companies, stealing or wiping data.
Stryker Corporation is a leading U.S.-based medical technology company that develops and manufactures devices and equipment used in hospitals, including surgical tools, orthopedic implants, medical imaging systems, and hospital beds. It is one of the world’s largest medical device manufacturers. Stryker reported global sales of $22.6 billion in 2024 and has over 53,000 employees.
The group said that this attack “is only the beginning of a new chapter in cyber warfare.”
Stryker said the incident was not a ransomware attack and no malware was deployed. BleepingComputer, citing a source familiar with the incident, reported that the attacker used the wipe command in Microsoft Intune to remotely erase data from nearly 80,000 devices between 5:00 and 8:00 a.m. UTC on March 11. The action was carried out after compromising an administrator account and creating a new Global Administrator account. The investigation is being led by Microsoft’s Detection and Response Team (DART) with support from Palo Alto’s Unit 42. Stryker confirmed the breach was confined to its internal Microsoft corporate environment and did not affect any of its medical products or connected devices.
“All Stryker products across our global portfolio, including connected, digital, and life-saving technologies, remain safe to use. This event was contained to Stryker’s internal Microsoft environment, and as a result it did not affect any of our products—connected or otherwise.” reads the company’s update published on 03/15/2026 11:30 a.m. ET.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Handala)
如有侵权请联系:admin#unsafe.sh
