嗯,用户让我用中文总结一篇文章,控制在一百个字以内,而且不需要特定的开头。首先,我需要仔细阅读这篇文章,了解其主要内容和重点。 文章主要讨论了2026年冲突期间伊朗网络战能力的下降。看起来伊朗的民用互联网基础设施遭受了严重破坏,公共互联网连接几乎崩溃,但国家电信骨干网仍然部分运作。这意味着伊朗虽然在某些方面的能力受到了影响,但并没有完全丧失网络战能力。 接下来,我需要提炼出关键点:互联网连接崩溃、电信骨干网部分运行、网络战能力降级但未消失。这些是文章的核心内容。 然后,我要确保用简洁的语言表达出来,控制在一百个字以内。可能的结构是先描述现状,再说明影响。比如,“伊朗民用互联网严重受损,公共连接几乎中断,但国家电信骨干部分运行,网络战能力降级但未消失。” 最后检查一下是否符合用户的要求:中文、一百字以内、直接描述内容。没有使用“文章内容总结”之类的开头。 </think> 伊朗民用互联网严重受损,公共连接几乎中断,但国家电信骨干部分运行,网络战能力降级但未消失。 2026-3-16 21:58:23 Author: krypt3ia.wordpress.com(查看原文) 阅读量:21 收藏
Iranian Cyber Warfare Capability Degradation Amid the 2026 Conflict
March 16th 2026
Executive Assessment
The ongoing conflict involving Iran, the United States, and Israel has produced a significant degradation of Iran’s civilian internet infrastructure and a partial disruption of its domestic digital ecosystem. However, available technical indicators suggest that Iran’s core telecommunications backbone remains operational at the routing layer, enabling the state to preserve a limited but functional digital command environment. As a result, while Iran’s cyber warfare capability has likely been impaired in several operational dimensions, it has not been eliminated.
Public internet connectivity inside Iran has collapsed to extremely low levels. Monitoring organizations report that national connectivity fell to approximately 1 percent of normal traffic levels, indicating that nearly all civilian users have lost reliable access to the global internet. This near-total shutdown has dramatically reduced ordinary outbound traffic and commercial network activity. Despite the collapse in user connectivity, routing telemetry shows that several major Iranian telecommunications networks continue to originate prefixes and maintain upstream connectivity in global BGP tables. This pattern indicates that Iran’s national internet infrastructure has not been physically or logically disconnected from the global internet, but instead appears to be operating under a selective access model in which only approved networks and services retain external connectivity.
The persistence of routing announcements from key Iranian backbone networks suggests that the state retains sufficient connectivity to sustain government communications, maintain telecommunications control infrastructure, and potentially support offensive cyber operations. Consequently, the most accurate assessment is that Iran’s cyber warfare capacity has been degraded but remains operational.
Operational Environment
The broader strategic environment surrounding the conflict has placed extraordinary strain on Iran’s national infrastructure and governing institutions. Sustained military operations, including strikes on strategic facilities and logistical networks, have compounded long-standing economic pressures and intensified regional instability. At the same time, the psychological and administrative demands of managing a wartime posture have forced the Iranian government to prioritize regime stability, information control, and the protection of critical state systems. Within this environment of kinetic conflict and geopolitical uncertainty, Iran’s digital landscape has undergone a rapid and profound transformation.
One of the most visible manifestations of this shift has been the collapse of ordinary internet connectivity across the country. Network monitoring platforms that track global traffic flows observed a dramatic decline in Iranian outbound traffic during the escalation of hostilities. At several points during the blackout period, measurements suggested that the volume of traffic leaving Iranian networks approached near-zero levels. For the vast majority of the population, the practical effect has been a near-total severance from the global internet. Civilian users have lost access to foreign news sources, communication platforms, and cloud services, while businesses that depend on international connectivity have experienced severe operational disruptions. Universities and research institutions, which rely heavily on cross-border academic networks and digital resources, have likewise been isolated from the global research environment. In practical terms, the Iranian public sphere has been digitally enclosed within the country’s borders.

Yet beneath this apparent collapse of connectivity, the technical indicators present a more complex picture of Iran’s network state. While public traffic has all but disappeared, routing telemetry shows that several key Iranian telecommunications entities continue to maintain a presence within the global internet’s routing architecture. Major infrastructure providers—including the Telecommunication Infrastructure Company, the Iran Information Technology Company, and a number of large domestic internet service providers—remain visible in international routing tables and continue to originate IP address prefixes. The persistence of these announcements indicates that Iran’s international gateway infrastructure has not been fully withdrawn from the global network. Instead, the fundamental routing relationships that connect Iran’s backbone networks to foreign carriers remain in place.
This contrast between the near-total disappearance of public internet activity and the continued visibility of backbone routing announcements is analytically significant. If Iran had executed a full disconnection from the global internet—such as withdrawing routes from border gateways or disabling international transit entirely—these networks would largely vanish from global routing tables. The fact that they remain present suggests that the country’s telecommunications infrastructure is still technically connected to the broader internet, even though most users cannot reach it.
The most plausible interpretation of this pattern is that Iranian authorities have implemented a highly restrictive traffic control regime rather than a complete network shutdown. In such a configuration, routing announcements continue to propagate globally, preserving the structural connectivity of the national network, while internal filtering mechanisms strictly regulate which systems are permitted to exchange traffic with external networks. Through the use of centralized gateways, firewall policies, and selective routing rules, the state can effectively allow-list certain categories of traffic while blocking the vast majority of ordinary communications.
Under this model, the Iranian government retains the ability to maintain connectivity for critical institutions even as it denies access to the broader population. Government ministries, telecommunications management systems, state media organizations, and financial infrastructure can continue to operate with external network access when necessary. Diplomatic communications, international financial transactions, and certain strategic digital operations may therefore remain viable despite the broader blackout. Meanwhile, the civilian internet environment remains tightly constrained, limiting the population’s ability to communicate with external audiences, access foreign information sources, or coordinate digitally during a period of conflict.
In effect, the Iranian state appears to have transformed the country’s internet environment into a controlled wartime communications network. The architecture of connectivity remains intact at the backbone level, but access to that architecture has been selectively restricted. This approach allows the government to balance two competing priorities: preserving the operational integrity of critical national systems while simultaneously suppressing the uncontrolled information flows that typically accompany an open internet during periods of political and military crisis.
Structure of Iran’s Network Control
Iran’s national internet infrastructure is built around a highly centralized architecture in which the majority of international connectivity passes through a small number of state-controlled telecommunications entities. At the center of this system is the Telecommunication Infrastructure Company (TIC), the government-operated organization responsible for managing the country’s international gateways and overseeing much of the backbone connectivity that links Iran to the global internet. Rather than allowing dozens of independent carriers to interconnect freely with foreign networks, Iran’s connectivity model concentrates international traffic flows into a tightly controlled set of gateway networks. These gateways act as strategic chokepoints through which nearly all inbound and outbound data must pass before reaching foreign transit providers.
This structural design gives Iranian authorities a powerful mechanism for regulating national connectivity. Because external traffic is funneled through a limited number of controlled gateways, the government can influence the country’s entire internet posture by adjusting policies at only a handful of network nodes. Through techniques such as routing policy manipulation, traffic filtering, deep packet inspection, and bandwidth throttling, operators can shape or restrict data flows at the border of the national network without requiring the physical disconnection of the country’s underlying infrastructure. In effect, the centralized topology functions as a form of digital border control, enabling the state to determine what types of traffic are permitted to cross between Iran’s internal networks and the broader global internet.

Within this framework, the Iranian government can pursue a strategy of selective connectivity rather than total disconnection. Routing announcements may continue to propagate globally, preserving the appearance of an operational network at the routing layer, while traffic rules within the gateway infrastructure determine which systems are actually permitted to exchange data with external networks. By maintaining these announcements, the core telecommunications backbone remains technically integrated into the global internet, ensuring that critical institutional networks retain the ability to communicate internationally when required.
At the same time, the state can block or severely restrict traffic associated with ordinary users. Residential broadband networks, commercial internet service providers, universities, and private businesses can effectively be cut off from the outside world even though the backbone routes that serve them continue to exist. The result is a layered connectivity environment in which only certain trusted or strategically important networks remain externally reachable. Government ministries, telecommunications control systems, financial infrastructure, and other priority institutions can continue to operate, while the broader population experiences what appears to be a complete internet outage.
The current wartime blackout appears consistent with this model of centralized control. Although the visible effects resemble a nationwide internet shutdown, the underlying routing data indicates that the national backbone has not disappeared from the global internet. Instead, the evidence suggests that authorities are actively regulating traffic flows at the gateway level, permitting only a narrow set of approved communications while suppressing the vast majority of outbound and inbound connections. This approach allows the government to maintain operational communications for state institutions while simultaneously limiting the circulation of information among the population and restricting the ability of citizens to communicate with audiences outside the country.
Such tactics are not unprecedented in Iran’s information control strategy. The government has previously implemented similar measures during periods of domestic unrest, particularly during large-scale protests or politically sensitive events. During those episodes, authorities temporarily restricted or throttled international connectivity while preserving the functionality of internal networks and state services. What distinguishes the present situation is the scale and duration of the restrictions. The current disruption appears far more comprehensive than previous shutdowns, reflecting both the pressures of an active military conflict and the regime’s heightened concern about information flows during wartime.
Taken together, the centralized structure of Iran’s internet infrastructure and the state’s demonstrated willingness to manipulate connectivity provide a clear explanation for the present blackout conditions. Rather than a simple technical failure or the unintended consequence of infrastructure damage, the evidence points toward a deliberate strategy in which connectivity is selectively managed to protect state interests while limiting the population’s access to the global information environment.
Iranian Internet Backbone Status: ASN Connectivity Assessment
Routing telemetry and ASN reconnaissance provide an additional layer of insight into the operational state of Iran’s national internet infrastructure during the current wartime blackout. While civilian internet access inside the country has collapsed to near-zero levels, analysis of global BGP routing tables indicates that several major Iranian autonomous systems (ASNs) continue to advertise IP address space and remain visible within the global internet routing ecosystem. These findings reinforce the conclusion that Iran’s international backbone infrastructure remains technically operational despite the severe restrictions imposed on public connectivity.
Autonomous systems represent the fundamental routing domains through which internet traffic is exchanged between networks. Each ASN corresponds to a network operator—such as a telecommunications provider, government institution, or large organization that controls a block of IP address space and exchanges routes with other networks through the Border Gateway Protocol (BGP). Monitoring the presence or absence of these ASN route announcements provides a reliable indicator of whether a country’s backbone infrastructure remains connected to the global internet.
| ASN | Operator (English) | Operator (Farsi) | Network Role | Likely State / Military Use |
|---|---|---|---|---|
| AS12880 | Iran Information Technology Company (ITC) | شرکت فناوری اطلاعات ایران | National backbone routing, IP address management | Core infrastructure supporting government networks, national routing control |
| AS48159 | Telecommunication Infrastructure Company (TIC) | شرکت ارتباطات زیرساخت | Primary international gateway operator | Central international internet gateway used by state agencies and national telecom |
| AS58224 | Iran Telecommunication Company | شرکت مخابرات ایران | Major domestic telecom carrier | Civilian telecom, but also backbone connectivity for government institutions |
| AS31549 | Arya Rasana Tadbir | آریا رسانه تدبیر | Data center and hosting provider | Potential hosting for government services and controlled infrastructure |
| AS42337 | Respina Networks | شبکه رسپینا | Enterprise ISP and backbone connectivity | Corporate networks, some state enterprise infrastructure |
| AS201691 | Pars Online | پارس آنلاین | Major consumer ISP | Civilian network access, possibly filtered during blackout |
| AS44244 | IranCell Telecommunications | ایرانسل | Mobile telecom provider | Civilian mobile data networks, possibly restricted during wartime blackout |
| AS197207 | Mobinnet | مبین نت | Wireless ISP | Domestic broadband services |
| AS203207 | Fanava Group | فنآوا | Telecom and infrastructure provider | Government and enterprise communications networks |
| AS20511 | Afagh Andish Dadeh Pardis | آفاق اندیش داده پردیس | ISP / infrastructure provider | Regional connectivity and enterprise services |
| AS25184 | Afranet | افرانت | Data services and ISP | Hosting infrastructure and cloud services |
| AS34362 | Pishgaman Tejarat Sayar | پیشگامان تجارت سیار | ISP and infrastructure provider | Regional connectivity networks |
| AS64413 | Iranian Research Organization for Science and Technology | سازمان پژوهشهای علمی و صنعتی ایران | Academic and research network | Universities, research institutes, strategic research communications |
| AS41881 | Fanap Telecommunications | فناپ تلکام | Data center and network infrastructure | Financial networks and enterprise infrastructure |
| AS48434 | Asiatech | آسیاتک | ISP and hosting provider | Enterprise hosting and network infrastructure |
One of the most significant Iranian networks observed to remain active in global routing tables is AS12880, operated by the Iran Information Technology Company (ITC). This network, which has been active for more than two decades, continues to advertise multiple IPv4 prefixes and maintains peering relationships with other networks. (bgp.tools)
The continued visibility of this ASN suggests that critical elements of Iran’s national telecommunications backbone remain operational and capable of exchanging traffic with external networks.
AS12880 is widely understood to play a central role within Iran’s internet architecture. The Iran Information Technology Company functions as one of the principal state-controlled organizations responsible for national internet infrastructure, including backbone routing and the management of large segments of Iranian IP address space. As a result, this ASN likely supports a range of essential services including government communications, telecommunications management systems, and network infrastructure used by state institutions.
In addition to AS12880, several other Iranian ASNs associated with domestic telecommunications providers and research networks continue to appear in global routing registries. Examples include:
- AS15402 — Pishgaman Tejarat Sayar Company
- AS13231 — Baharan PLC
- AS15611 — Iranian Research Organization for Science and Technology
These networks collectively represent a mix of commercial telecommunications providers, academic infrastructure, and state-linked network operators. (whois.ipip.net)
Although their traffic levels may be substantially reduced under blackout conditions, the persistence of their route announcements indicates that they remain technically reachable from outside Iran.

The operational significance of these networks varies. Large backbone ASNs associated with state telecommunications infrastructure likely form the core of Iran’s international gateway environment. Networks operated by research organizations or specialized service providers may continue to function because they support critical institutional communications or technical services. Universities, research institutes, and state media organizations frequently maintain their own autonomous systems, allowing them to exchange traffic with both domestic and international networks.
From a strategic perspective, the continued operation of these ASNs provides the Iranian government with several important capabilities even during periods of severe domestic connectivity restrictions. First, they allow the state to preserve connectivity for essential government and administrative systems, including diplomatic communications, financial infrastructure, and telecommunications management platforms. Second, they enable selective international access for institutions that the government chooses to allow-list, such as state media outlets or research networks involved in strategic programs. Finally, these backbone networks provide the technical infrastructure through which Iranian cyber units can continue to interact with external command-and-control infrastructure or previously compromised systems abroad.
The persistence of these route announcements also suggests that the current blackout has been implemented primarily through traffic filtering and policy controls rather than physical disconnection of network infrastructure. In a full national disconnection scenario, Iranian ASNs would likely disappear from global routing tables as international gateway links were withdrawn or disabled. Instead, the available data indicates that the underlying routing architecture remains intact while the ability of most domestic users to generate outbound traffic has been restricted through filtering mechanisms.
For analysts monitoring the cyber dimension of the conflict, these ASN observations carry important implications. As long as core Iranian telecommunications ASNs remain visible within global routing tables, the country retains a functional backbone through which state institutions and cyber operators can maintain external connectivity. This infrastructure may be operating at a reduced capacity and under strict government control, but it still provides the foundational network layer required for communications, intelligence collection, and cyber operations.
Consequently, the ASN analysis reinforces the broader assessment that Iran’s cyber capabilities have likely been degraded but not eliminated by the wartime blackout. Civilian connectivity may be effectively severed, yet the persistence of key backbone networks demonstrates that the Iranian state retains sufficient connectivity to sustain essential government functions and limited cyber operational activity.
Effects on Iranian Cyber Operations
The collapse of civilian internet access across Iran, combined with the broader disruption of the country’s digital ecosystem, is likely to impose a range of operational constraints on Iranian cyber activities. While the state retains elements of its telecommunications backbone and selective external connectivity, the near-total disappearance of ordinary internet usage fundamentally alters the operational environment in which Iranian cyber units and affiliated actors must operate. The loss of widespread connectivity introduces logistical friction, reduces the availability of supporting infrastructure, and alters the network conditions under which cyber campaigns are typically planned and executed.
One of the most immediate effects of the blackout is the increased difficulty of internal coordination among cyber operators working within Iran. Offensive cyber campaigns particularly those involving multiple operators, distributed toolsets, and extended intrusion chains depend heavily on reliable communications among team members. Under conditions where public internet access is severely restricted and network traffic is tightly controlled, the ability of operators to exchange intelligence, share malware builds, coordinate targeting decisions, and manage ongoing operations becomes more cumbersome. Even if certain institutional networks remain connected through allow-listed pathways, the overall communications environment is likely to be slower, more constrained, and less flexible than under normal circumstances. This introduces friction into workflows that normally rely on rapid data exchange and collaborative coordination.

The disruption may also significantly reduce the volume of lower-tier cyber activity originating from inside the country. A substantial portion of disruptive cyber operations historically attributed to Iran has involved loosely organized patriotic hacker groups or opportunistic actors who operate with varying degrees of state tolerance or encouragement. These actors often rely on readily available infrastructure, open internet access, and widely accessible tools to conduct activities such as website defacements, distributed denial-of-service attacks, or basic intrusion campaigns. When broad civilian connectivity disappears, the technical conditions that enable such activity become much harder to sustain. Individuals who previously participated in these operations from home networks or small commercial hosting environments may find themselves unable to access the external resources required to launch or sustain attacks. As a result, the pool of actors capable of carrying out unsophisticated but high-volume operations may shrink considerably during the blackout period.
Beyond coordination challenges and the reduction of volunteer-driven activity, limited connectivity also complicates several aspects of standard cyber operational tradecraft. Modern cyber campaigns often involve iterative development cycles in which malware is repeatedly tested, modified, and redeployed against target environments. Operators typically rely on stable outbound connectivity to upload test builds, access remote infrastructure, retrieve stolen data, and maintain command-and-control channels. Under conditions where outbound bandwidth is constrained or heavily filtered, these processes become slower and less reliable. Tasks such as transferring large volumes of exfiltrated data, staging payloads on external servers, or conducting remote forensic analysis of compromised systems may be delayed or interrupted. Over time, these limitations can reduce the operational tempo of campaigns conducted directly from domestic infrastructure.
Another important consequence of the blackout relates to the broader visibility of Iranian network activity. Under normal circumstances, the vast volume of civilian and commercial traffic flowing through national networks creates a dense background of digital noise that can obscure the activities of individual systems or organizations. When that noise largely disappears—as appears to be the case during the current blackout the remaining traffic becomes proportionally more visible. With residential broadband usage, consumer web traffic, and commercial network activity largely absent, the packets that continue to traverse Iranian gateway networks are more likely to originate from institutional systems such as government ministries, telecommunications management platforms, or other strategically significant infrastructure. This concentration may make it easier for external observers to detect patterns, identify active nodes, or attribute network activity to specific organizations within the state apparatus.
Taken together, these factors suggest that the current network conditions could temporarily reduce Iran’s ability to conduct large-scale cyber campaigns directly from infrastructure located inside the country. Coordination challenges, diminished access to external resources, and the disappearance of volunteer-driven activity all contribute to a more constrained operational environment. While these limitations do not eliminate Iran’s cyber capabilities particularly given the availability of offshore infrastructure and previously established access inside foreign networks they likely impose short-term constraints on operational
Despite the operational friction created by the widespread disruption of Iran’s domestic internet environment, recent events indicate that cyber activity aligned with Iranian interests has not ceased. Multiple reports indicate that cyber operations continued in parallel with the early stages of the conflict, including retaliatory cyber incidents directed at foreign organizations and disruptions attributed to pro-Iranian actors. For example, reporting in March 2026 described a cyberattack affecting the U.S. medical device company Stryker, which pro-Iranian hackers claimed was conducted in retaliation for U.S. and Israeli strikes on Iranian targets.¹ These incidents demonstrate that even amid severe domestic connectivity restrictions, cyber operations linked to Iranian actors remain capable of producing measurable effects beyond Iran’s borders.
This pattern reflects a broader reality of contemporary cyber conflict: offensive cyber capabilities do not depend exclusively on a fully functional domestic internet environment. Modern cyber operations are typically designed to operate through distributed infrastructures in which command systems, staging servers, and operational nodes are geographically dispersed across multiple jurisdictions. Threat actors frequently rely on third-party hosting providers, compromised servers, and cloud infrastructure located outside their home country to launch or relay attacks. Because these external systems often function as the operational interface between attackers and their targets, the state of a nation’s domestic internet infrastructure may have only limited impact on ongoing cyber campaigns once such infrastructure has been established.
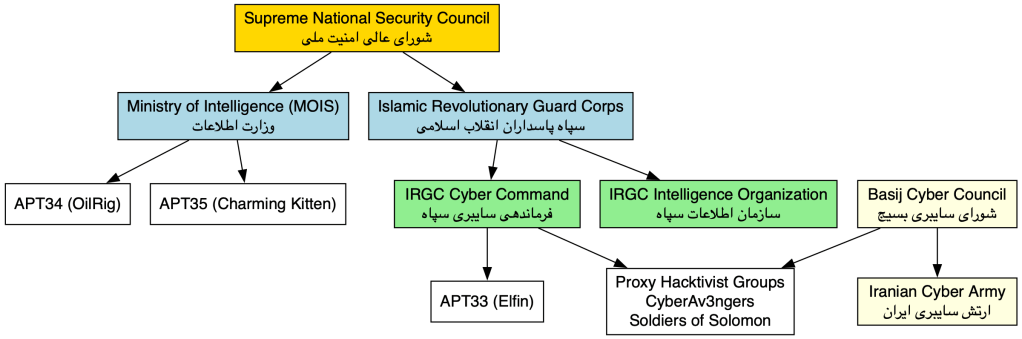
Iranian cyber actors have historically demonstrated a consistent reliance on distributed infrastructure models. Threat intelligence reporting on Iranian advanced persistent threat (APT) groups has shown that many campaigns utilize rented virtual private servers, compromised websites, and cloud-based command-and-control infrastructure located in multiple countries.³ In these operations, externally hosted systems frequently function as staging platforms or relay nodes through which malicious traffic is routed before reaching target environments. This architecture enables Iranian operators to sustain cyber campaigns even when connectivity from within Iran itself becomes restricted, unstable, or heavily monitored.
The use of geographically distributed infrastructure provides additional operational advantages beyond simple resilience. Infrastructure hosted in foreign jurisdictions can obscure the geographic origin of malicious traffic, complicate attribution efforts, and reduce the risk that defensive countermeasures will directly affect domestic Iranian networks. Such characteristics have long made distributed infrastructure an attractive operational model for Iranian threat groups and for other state-sponsored cyber programs more broadly.
Consequently, although the degradation of Iran’s domestic internet environment introduces logistical constraints, it does not fundamentally eliminate the country’s ability to conduct cyber operations. Operators may encounter slower coordination, reduced bandwidth for internal communications, and limited access to domestic hosting resources. However, once operational infrastructure has been established outside Iran—or when previously compromised systems remain under attacker control—cyber campaigns can continue with relatively limited dependence on domestic civilian connectivity.
In this sense, the current blackout environment likely reduces operational convenience rather than operational capability. Iranian cyber units may increasingly rely on previously established infrastructure, offshore hosting providers, and proxy actors to sustain their activities. Nevertheless, the structural characteristics of modern cyber operations allow the Iranian state to retain the ability to project cyber activity beyond its borders even while its internal internet environment remains severely constrained.
Likely Operational Adaptations
Given the constraints imposed by the current blackout and the broader disruption of Iran’s domestic digital environment, Iranian cyber units are likely to adapt their operational methods in ways that minimize reliance on internal connectivity while preserving their ability to exert pressure through cyberspace. Historically, Iranian cyber actors have demonstrated a degree of operational flexibility, and the present circumstances are likely to accelerate the use of techniques that allow campaigns to continue even when domestic network conditions are unstable or heavily restricted.
One area where operations are likely to remain relatively unaffected involves intrusions in which Iranian actors have already established pre-positioned access within foreign networks. Many cyber campaigns unfold over extended periods, with attackers spending months or even years maintaining covert access to compromised environments before executing disruptive or espionage activities. Once such access has been achieved, the operational infrastructure supporting the intrusion often resides within the target network itself or on intermediary systems located outside the attacker’s home country. Under these circumstances, the level of ongoing communication required between the operators and the compromised systems can be relatively modest. Command instructions may be issued intermittently, and automated tooling embedded within the target environment can continue to function even if direct connectivity from Iran becomes slower or more restricted. As a result, previously established footholds in foreign networks could remain viable avenues for continued cyber operations despite the domestic blackout.

Another likely adaptation involves an increased reliance on external infrastructure located outside Iranian territory. Cyber operations conducted by nation-state actors frequently depend on rented servers, cloud hosting platforms, or compromised systems in foreign jurisdictions that act as staging points or command-and-control nodes. These external assets allow operators to interact with target systems through intermediate infrastructure rather than communicating directly from domestic networks. If connectivity inside Iran becomes constrained, operators may shift a greater portion of their operational control mechanisms to servers hosted abroad. Such infrastructure can provide stable network access, higher bandwidth, and reduced exposure to domestic filtering policies. By managing campaigns through offshore systems, Iranian operators can maintain operational continuity even while their home networks remain partially isolated.
In addition to technical adaptations, Iran may increasingly leverage aligned or proxy hacker groups to carry out certain categories of cyber activity. Over the past decade, Iranian authorities have frequently tolerated or quietly encouraged the actions of loosely affiliated patriotic hacker collectives that conduct disruptive operations against perceived adversaries. These groups often operate from a variety of locations and do not necessarily rely on infrastructure inside Iran itself. In a wartime environment where domestic connectivity is constrained, proxy actors located abroad—or operating through foreign infrastructure—can provide a means of sustaining cyber pressure against adversaries while insulating the state from direct operational exposure. Such groups can launch disruptive campaigns, deface websites, or distribute stolen information in ways that align with Iranian strategic narratives without requiring significant coordination with state networks.
Finally, Iranian cyber actors may place greater emphasis on lower-cost disruptive tactics that can be executed with minimal infrastructure and relatively limited coordination. Operations such as distributed denial-of-service attacks, website defacements, and hack-and-leak campaigns require fewer technical resources than sophisticated espionage intrusions or complex destructive malware deployments. These activities are often designed less to achieve long-term network access and more to generate immediate political or psychological impact. By temporarily disabling websites, publishing stolen data, or disrupting online services, attackers can create headlines and signal retaliation even when operating under constrained conditions. In the context of an ongoing conflict, such tactics can serve both as instruments of harassment and as tools of information warfare, amplifying narratives of resistance or retaliation.
Taken together, these adaptive strategies illustrate how Iranian cyber actors may compensate for the limitations imposed by the current blackout environment. While the degradation of domestic internet connectivity introduces operational friction and may reduce the scale or tempo of certain campaigns, it does not prevent Iranian cyber units from continuing to operate through distributed infrastructure, pre-existing intrusions, proxy actors, and relatively low-cost disruptive techniques. In this sense, the operational landscape may shift toward a more decentralized model of activity, in which cyber operations are sustained through external networks and indirect mechanisms rather than through infrastructure located primarily within Iran itself.
External Visibility of Cyber Activity During the Iranian Internet Blackout
The current internet blackout in Iran introduces a critical analytical challenge for external observers attempting to monitor cyber activity associated with the conflict. With civilian connectivity reduced to negligible levels and much of the country’s public-facing internet environment effectively isolated, the ability of outside analysts to directly observe cyber operations originating within Iran is significantly constrained. Nevertheless, the blackout does not render Iranian cyber activity entirely invisible. Although direct visibility into internal network activity is largely absent, several forms of external telemetry continue to provide indirect indicators of cyber operations connected to Iranian infrastructure.
Under normal conditions, the global internet produces a vast amount of observable traffic that allows analysts to identify patterns associated with malicious behavior. Residential users, commercial enterprises, universities, and cloud services collectively generate enormous volumes of network activity, creating a dense background against which anomalous traffic can be detected. When the majority of that traffic disappears as appears to have occurred during the current blackout the observable attack surface shrinks dramatically. With far fewer Iranian systems communicating openly with the outside world, the opportunities for external analysts to detect suspicious traffic originating from Iranian networks are correspondingly reduced.
In addition to the disappearance of most outbound traffic, the blackout has also limited the accessibility of many Iranian websites and online services. Numerous systems that were previously reachable from outside the country now return connection failures or timeouts, reflecting either direct blocking measures or the absence of functional routing paths for public traffic. This isolation further reduces the ability of outside researchers to conduct active probing or vulnerability scanning of Iranian infrastructure in order to detect compromised systems or ongoing attack activity.
Despite these constraints, several categories of network telemetry continue to provide partial visibility into the state of Iranian cyber activity. One of the most important of these sources is global routing telemetry derived from Border Gateway Protocol (BGP) monitoring. Even during periods of severe connectivity restriction, Iran’s core telecommunications networks continue to advertise routing information to the global internet. By analyzing changes in these routing announcements, researchers can detect certain forms of network disruption, including route withdrawals, traffic diversion events, or defensive routing techniques such as blackholing that may be used to mitigate distributed denial-of-service attacks. While such telemetry does not reveal the contents of network traffic, it can provide valuable insight into the structural behavior of Iranian networks and the defensive responses triggered by cyber incidents.
Another source of indirect visibility comes from the monitoring of unused address space through systems known as network telescopes or darknets. These sensors observe traffic directed toward portions of the internet that contain no legitimate hosts. Because legitimate communications should never be sent to these addresses, packets arriving at darknet sensors are typically associated with malicious activity, such as automated vulnerability scanning or malware propagation. Even if Iranian networks are largely isolated from ordinary internet traffic, compromised systems within the country may still generate scanning activity that reaches these monitoring networks. When that occurs, analysts can infer the presence of malware infections or automated attack tools operating within Iranian address space.
In addition to darknet monitoring, many cybersecurity organizations operate large distributed sensor networks designed to detect malicious traffic across the global internet. These platforms rely on honeypots and passive monitoring systems that capture exploit attempts, credential-harvesting probes, and other indicators of attack preparation. When systems within Iranian address space attempt to scan or exploit these sensors, the activity becomes visible to global monitoring infrastructure even if the internal Iranian networks from which the traffic originates remain otherwise opaque.
These forms of telemetry allow outside observers to detect certain outward-facing cyber activities associated with Iranian infrastructure. Analysts may be able to observe vulnerability scanning campaigns, exploit attempts targeting exposed services, malware propagation events, or participation by Iranian systems in distributed denial-of-service attacks. Because these activities involve direct interaction with systems outside Iran, they inevitably generate network signals that can be captured by monitoring infrastructure located elsewhere on the internet.
However, the blackout imposes severe limitations on what can be observed. External analysts generally cannot see traffic that remains entirely within Iranian networks, including lateral movement between compromised systems inside the country or communications between internal command servers and operators. Activities such as malware development, testing environments, and operational planning conducted within isolated networks remain effectively invisible to outside observers. Furthermore, many advanced cyber operations rely on infrastructure located outside the originating country. When attackers control servers or compromised systems abroad, malicious activity may appear to originate from those external nodes rather than from Iran itself. In such cases, the operational infrastructure visible to defenders may reveal little about the geographic location of the operators directing the campaign.
Taken together, these factors suggest that the blackout significantly reduces the external observability of cyber operations occurring within Iran, but it does not eliminate it entirely. Certain outward-facing behaviors—particularly those that interact directly with the global internet—remain detectable through a combination of routing telemetry, darknet monitoring, and distributed attack-sensor networks. At the same time, the disappearance of most civilian network traffic creates substantial intelligence blind spots, making it far more difficult for external observers to identify the internal coordination, staging, and command structures that support Iranian cyber campaigns.
As a result, analysts monitoring the cyber dimension of the conflict must rely heavily on indirect indicators and global telemetry rather than direct observation of Iranian networks. Large-scale scanning campaigns, botnet activity, and routing anomalies may still provide clues about ongoing cyber operations. Yet the blackout environment significantly obscures the internal phases of those operations, particularly those conducted within isolated networks or through infrastructure located outside Iran’s borders. In practical terms, the blackout does not make Iranian cyber activity invisible, but it does make it far more difficult to detect, attribute, and analyze in real time.
Overall Assessment
The body of technical and contextual evidence accumulated during the current conflict indicates that the war and the accompanying nationwide internet shutdown have profoundly disrupted Iran’s domestic digital environment. Civilian connectivity to the global internet has fallen to extremely low levels, effectively isolating most of the country’s population from external networks. Businesses, universities, media organizations, and private individuals now operate within an environment where access to international platforms and communication channels is either severely constrained or entirely unavailable. The resulting contraction of Iran’s public internet activity represents one of the most significant connectivity disruptions the country has experienced in recent years.
This collapse of civilian connectivity carries meaningful implications for Iran’s cyber ecosystem. Many aspects of cyber operations particularly those requiring extensive collaboration, rapid data exchange, and distributed infrastructure management depend on reliable domestic connectivity and the ability of operators to communicate freely across networks. In a blackout environment where communications are tightly controlled and bandwidth is limited, such activities inevitably become more difficult to coordinate. Campaigns that rely on teams of operators working in parallel, rapidly deploying infrastructure, or exchanging large quantities of data may experience delays or reduced efficiency. In this sense, the wartime blackout likely introduces operational friction that constrains some categories of cyber activity originating from inside Iran.
At the same time, routing telemetry and network analysis reveal that Iran’s telecommunications backbone has not disappeared from the global internet. Key Iranian telecommunications providers continue to originate routing announcements and remain visible within international BGP tables. The persistence of these routing relationships indicates that the country’s international gateways and core backbone networks remain technically operational even as civilian connectivity has collapsed. Rather than a complete disconnection from the global internet, the current conditions appear to reflect a tightly controlled connectivity environment in which access is selectively permitted for certain institutional networks.
This pattern strongly suggests that Iranian authorities have implemented a selective connectivity model designed to preserve essential state communications while restricting the population’s access to external networks. Under such a model, government ministries, telecommunications management systems, financial institutions, and other strategically important organizations can maintain external connectivity through allow-listed pathways. Meanwhile, residential networks, commercial internet service providers, and other civilian systems remain largely cut off from the global network environment. The result is a bifurcated internet environment in which the backbone remains intact but access to it is tightly controlled.
When considered together, these conditions lead to a balanced assessment of Iran’s cyber capabilities during the current conflict. The blackout environment undoubtedly degrades aspects of the country’s cyber operational environment, particularly those that depend heavily on widespread domestic connectivity or large-scale collaboration among operators inside the country. The loss of civilian infrastructure, the reduction in accessible hosting resources, and the constraints placed on internal communications all introduce obstacles that can slow operational tempo and reduce campaign scale.
However, these limitations do not eliminate Iran’s ability to conduct cyber operations. The continued functionality of the national telecommunications backbone ensures that the state retains at least a limited capacity for external communication and network management. Combined with Iran’s demonstrated experience in operating through distributed infrastructure and external staging systems, this connectivity is sufficient to sustain both disruptive cyber activities and long-term espionage campaigns.
Accordingly, Iran’s cyber warfare capability should be assessed not as neutralized but as degraded yet still operational. The wartime blackout likely reduces efficiency, constrains some categories of activity, and forces operators to adapt their methods. Nevertheless, Iranian cyber actors continue to possess the infrastructure, expertise, and operational frameworks necessary to conduct cyber campaigns beyond their borders. The current environment therefore represents a reduction in operational convenience and scale rather than a fundamental loss of capability.
Strategic Outlook
If the conflict continues over an extended period, the cyber domain will almost certainly remain an active theater for retaliation, signaling, and asymmetric pressure. Cyber operations provide states with a means of imposing costs on adversaries without escalating directly into conventional military confrontation. For Iran in particular, the cyber domain offers a comparatively accessible avenue for demonstrating resilience and projecting influence even while its domestic infrastructure faces disruption and wartime constraints. Under these conditions, Iranian cyber actors may increasingly prioritize operations designed to generate symbolic impact or psychological pressure rather than focusing exclusively on long-term espionage campaigns.
Such activity could manifest in a variety of forms. Disruptive cyber actions against foreign commercial entities, public institutions, and critical infrastructure operators would allow Iranian actors to signal that the country retains the capacity to respond in cyberspace despite the domestic connectivity challenges created by the blackout. Operations targeting high-profile organizations—particularly those associated with sectors such as finance, healthcare, transportation, or energy—can attract significant public attention even when the technical impact of the intrusion is limited. In this sense, cyber activity can function as both retaliation and strategic messaging, reinforcing the narrative that Iran remains capable of imposing costs on its adversaries in domains beyond the battlefield.
At the same time, the current conflict may have lasting implications for Iran’s internal approach to network architecture and information control. The blackout environment demonstrates both the strengths and limitations of the country’s centralized telecommunications model. While authorities have proven capable of sharply restricting civilian access to the global internet, the crisis also highlights the importance of maintaining reliable communications channels for government institutions, financial systems, and security organizations. In response, Iranian policymakers may accelerate efforts to expand and reinforce the country’s controlled national network architecture, including the continued development of domestic platforms and internal services that can operate independently from the global internet.
Such initiatives are consistent with Iran’s longer-term strategy of building a more autonomous digital ecosystem. By strengthening domestic infrastructure and reducing reliance on foreign platforms, the state can increase its ability to manage information flows during periods of crisis while still preserving the connectivity required for state institutions and strategic operations. A more mature national network architecture could enable authorities to isolate civilian users more rapidly and more selectively in future emergencies, limiting public communication with external audiences while ensuring that government communications and cyber capabilities remain intact.
Taken together, these dynamics suggest that the current blackout represents both an immediate operational constraint and a potential catalyst for structural changes in Iran’s digital strategy. In the short term, the disruption has placed meaningful strain on the country’s cyber ecosystem by limiting civilian connectivity, constraining domestic communications, and altering the conditions under which cyber operations are coordinated. However, the persistence of the national telecommunications backbone and the continued visibility of Iranian routing infrastructure indicate that the country retains a functioning digital core from which cyber operations can still be conducted.
For this reason, the present situation should not be interpreted as the neutralization of Iran’s cyber warfare capability. Rather, the blackout has likely reduced operational efficiency and imposed limits on scale and tempo while leaving the underlying capacity for cyber activity intact. Iranian actors continue to possess the technical expertise, operational experience, and distributed infrastructure necessary to project cyber activity beyond the country’s borders. Consequently, even under conditions of severe domestic disruption, Iran remains capable of conducting disruptive or espionage-oriented cyber campaigns, though these operations may proceed at a slower pace and rely more heavily on external infrastructure than they would under normal peacetime conditions.
如有侵权请联系:admin#unsafe.sh