嗯,用户让我用中文总结一下这篇文章的内容,控制在一百个字以内,而且不需要用“文章内容总结”之类的开头。直接写描述即可。 首先,我需要通读整篇文章,抓住主要信息。文章主要讲的是NetExec (NXC)文件传输工具,对渗透测试和红队人员来说是个必须掌握的技巧。它支持多种协议,比如SSH、FTP、NFS和MS-SQL,使用统一的命令语法,方便在不同主机和协议之间切换。 接下来,文章还提到了NXC的优势在于简化了自动化和脚本编写,但同时也指出了配置错误的服务可能带来的安全风险。比如匿名FTP、过于宽松的NFS导出权限等都可能引发安全事件。 最后,文章还给出了防御建议,包括强化访问控制、限制网络暴露、安全文件操作以及监控和审计等措施。 现在要把这些内容浓缩到100字以内。我需要抓住关键点:NXC的功能、支持的协议、统一语法的优势、配置错误的风险以及防御措施。 可能会这样组织语言:“NetExec (NXC) 是一种跨协议文件传输工具,支持 SSH、FTP、NFS 和 MS-SQL 等协议。它通过统一命令语法简化操作,并能利用配置错误的服务进行攻击。文章介绍了其功能与防御方法。” 检查一下字数是否在100字以内,并且没有使用不需要的开头。 </think> NetExec (NXC) 是一种跨协议文件传输工具,支持 SSH、FTP、NFS 和 MS-SQL 等协议。它通过统一命令语法简化操作,并能利用配置错误的服务进行攻击。文章介绍了其功能与防御方法。 2025-10-17 15:13:44 Author: www.hackingarticles.in(查看原文) 阅读量:4 收藏
NetExec (NXC) file transfer is a must‑know technique for pentesters and red teamers who need reliable, cross‑protocol methods to move payloads, exfiltrate data, or stage tooling. Using a single, modular interface, NXC lets you transfer files over SSH, FTP, NFS, and MS‑SQL with the same command syntax making it faster to pivot between hosts and protocols during engagement. While SCP and SMB remain staples, NXC’s unified approach simplifies automation and scripting, but also highlights how misconfigured services (anonymous FTP, overly permissive NFS exports, database file functions) can turn routine transfers into serious security incidents. This guide walks through practical NXC commands, attack scenarios, and defensive controls so you can leverage file transfer powerfully and securely.
Table of Content
- Overview
- Prerequisites
- SSH
- FTP
- NFS
- MS-SQL
- Mitigation
- Conclusion
Overview
Every file you upload or download tells a story. For a pentester:
- It could be dropping reconnaissance scripts or extracting password files.
- For a defender, these same steps represent lateral movement, data theft, or persistence.
Attackers frequently exploit legitimate services (like SSH or FTP) to move files quietly within a compromised network. Understanding these methods helps both offensive and defensive teams detect misuse and strengthen configurations before attackers exploit them.
- SSH Put/Get → Encrypted, authenticated file transfers (SCP/SFTP) used to stealthily stage tools, move payloads, or exfiltrate data while preserving confidentiality and integrity.
- FTP Put/Get → Legacy, often unencrypted protocol (may allow anonymous access) used to upload/download web shells or data; frequently abused when misconfigured or weakly authenticated.
- NFS LS/Get/Put → Network shares that present remote directories as local; permissive exports let attackers read sensitive files, plant persistence artifacts, or move laterally.
- MS‑SQL Put/Get → Database‑driven file I/O (BULK INSERT/OPENROWSET, CLR, xp_cmdshell etc.) that lets attackers pivot from DB privileges to OS file access for staging or exfiltration.
File transfers look simple but are dangerously powerful: misconfigured SSH, FTP, NFS or MS‑SQL services let attackers stage payloads, exfiltrate secrets, or pivot to the OS with minimal fuss.
Bottom line — it’s not just the file: it’s who can move it, where it lands, and what processes can read or run it; enforce least privilege, centralize logging, and monitor unusual transfers to reduce the risk.
Prerequisite
- Kali Linux packed with tools
- Tools: NXC
SSH: SCP/SFTP style operations (typical Linux hosts)
SSH remains one of the most secure and versatile remote management protocols. However, weak credentials or misconfigurations can make it an easy target.
When attackers favor SSH
- Valid credentials or SSH keys are available (phished, reused, brute).
- Target is a Linux host or network device supporting SCP/SFTP.
- Encrypted channel reduces network detection compared to cleartext FTP.
Upload a local file to target
nxc ssh 192.168.1.3 -u pentest -p 123 --put-file file.txt /tmp/file.txt

Uploads the local file file.txt to /tmp/file.txt on the remote host using SSH for authentication; while this is a common administrative technique for staging tools or moving data for execution, exfiltration, or persistence, it can be abused; especially with weak or reused credentials—to enable unauthorized code execution and lateral movement.
Download remote file
nxc ssh 192.168.1.3 -u pentest -p 123 --get-file /etc/passwd passwd
Retrieve the remote /etc/passwd and save it locally as passwd to enumerate users, UIDs/GIDs, and shells for reconnaissance; ensure this action is authorized and logged, and treat more sensitive files (for example /etc/shadow, sshd_config, user home directories, and authentication logs) with stricter controls because their exfiltration can enable privilege escalation and should trigger alerts for unusual system‑file downloads or unexpected SCP/SFTP GETs.

FTP: legacy but still common (appliances, backup targets)
FTP is often plaintext and legacy — it’s commonly abused where still enabled.
When attackers favor FTP
- Embedded devices, legacy servers offering FTP (sometimes anonymous).
- FTP is cleartext (unless FTPS) so network IDS can detect content — but many orgs don’t actively monitor FTP activity.
Uploads
nxc ftp 192.168.1.3 -u pentest -p 123 --put file.txt file.txt

This connects to an FTP server to upload file.txt, saving it as file.txt on the remote server for authorized file transfer. Although convenient, FTP uploads carry risks such as arbitrary file uploads (including webshells), manipulation of served content, and potential data exfiltration.
Download
nxc ftp 192.168.1.3 -u pentest -p 123 --get /etc/passwd

This retrieves the remote /etc/passwd from an FTP server to the local host for reconnaissance and user enumeration. If the FTP daemon has excessive filesystem privileges or is misconfigured, it can let attackers exfiltrate sensitive host files.
NFS: direct filesystem access across network
NFS exposes filesystem-level access across the network and is frequently misconfigured.
When attackers favor NFS
- Misconfigured exports (e.g., export / or /etc to wide ranges).
- Internal networks where hosts mount NFS shares; attackers can read system files if exports are permissive.
List root export
nxc nfs 192.168.1.3 --ls '/'

This queries the root of an NFS export to identify accessible shares and determine whether mounts are writable; a perfect reconnaissance step that can reveal paths for data theft or payload staging. This reveals exported paths and writable mounts that may expose sensitive data or allow file planting; configurations that disable no_root_squash or permit wide write access are especially dangerous.
Download
nxc nfs 192.168.1.3 --get /etc/shadow

This attempts to obtain /etc/shadow from an NFS export to steal password hashes; NFS misconfigurations that expose system directories can allow this, so such access must be blocked, logged, and tightly controlled.
Upload
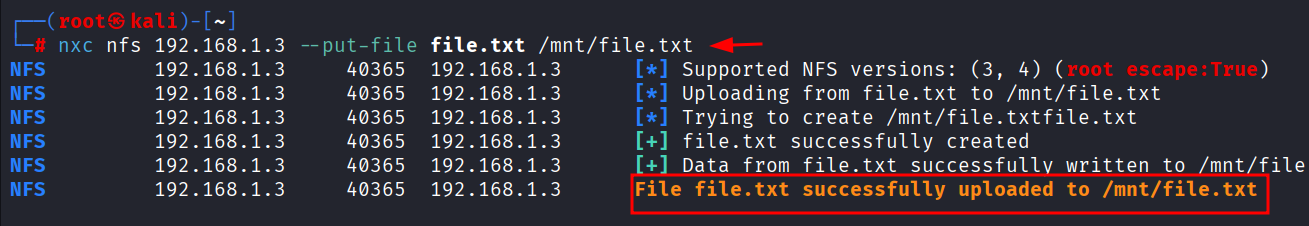
nxc nfs 192.168.1.3 --put-file file.txt /mnt/file.txt
Uploads file.txt to the NFS export at /mnt/file.txt to place persistence artifacts or executable payloads; writable exports can be abused to maintain access or pivot to other hosts.

MS-SQL: DB file APIs and server-side file I/O (Windows hosts)
MS-SQL servers often run under highly privileged service accounts and can access the filesystem via SQL Server features.
When attackers favor MS-SQL file primitives
- DB accounts with privileges to write to disk (BULK APIs, xp_cmdshell or CLR) can stage or retrieve files on Windows hosts.
- Useful on Windows environments where SQL Server service runs as a privileged account.
Upload a file as SQL
nxc mssql 192.168.1.8 -u sa -p 'Ignite@987' --put-file file.txt C:\\users\\public\\file.txt --local-auth

Uses MS‑SQL access (for example, the sa account) to write file.txt to C:\Users\Public\file.txt on the Windows host. Attackers abuse database capabilities to drop files when the DB service account has filesystem privileges, turning the database into a pivot to the OS.
Download from Windows path via SQL
nxc mssql 192.168.1.8 -u sa -p 'Ignite@987' --get-file C:\\users\\public\\raj.txt /tmp/raj.txt --local-auth

Retrieves a file from a Windows host through MS-SQL context and saves it locally. This method enables exfiltration of sensitive files via the database, acting as a covert channel to access otherwise restricted data.
Conclusion
File transfer is deceptively simple: it needs only credentials (or a misconfiguration) and gives a reliable path to stage tools, steal artifacts, and exfiltrate data. NXC makes these primitives easy to run during pentesting which is exactly why defenders must instrument and monitor them.
For red teams: use these methods responsibly in scoped assessments and always document
artifacts for cleanup.
For blue teams: focus on telemetry that confirms chains of behavior (artifact read → credential reuse → outbound flow) and harden the services described above.
Mitigation
- Harden Access & Authentication: Enforce least privilege, disable password logins where possible, use SSH keys or MFA, and remove anonymous or shared accounts.
- Restrict Network Exposure: Limit SSH, FTP, NFS, and MSSQL to trusted IPs or jump hosts; segment networks to isolate management and database services.
- Secure File Operations: Disable unnecessary file transfer features (xp_cmdshell, FTP uploads), restrict writable directories, and protect sensitive paths (/etc/shadow, C:\Users\Public).
- Monitor & Detect Transfers: Centralize logging for SSH/FTP/NFS/MSSQL, alert on unexpected uploads/downloads or new binaries in system folders.
- Regular Auditing & Hardening: Continuously review service configurations, exported shares, and permissions to prevent misconfigurations that enable lateral movement.
Author: MD Aslam drives security excellence and mentors teams to strengthen security across products, networks, and organizations as a dynamic Information Security leader. Contact here
如有侵权请联系:admin#unsafe.sh