
嗯,用户让我帮忙总结一下这篇文章的内容,控制在一百个字以内,而且不需要用“文章内容总结”或者“这篇文章”这样的开头,直接写描述。好的,首先我得仔细阅读文章,理解主要信息。 文章讲的是FBI在调查Steam平台上的一些恶意游戏。这些游戏被植入了恶意软件,导致用户的信息被盗,尤其是加密货币钱包和账户信息。FBI已经确定了几个恶意游戏,比如BlockBlasters、Chemia、Dashverse/DashFPS等等,并且他们正在联系受害者收集信息。 接下来,我需要把重点提炼出来:FBI调查Steam恶意游戏事件,这些游戏含有恶意软件,导致用户信息和加密货币被盗。他们已经识别出多个恶意游戏,并正在联系受害者。 现在要控制在100字以内,所以要简洁明了。可能的结构是:FBI调查Steam上的恶意游戏事件,这些游戏中含有恶意软件,导致用户信息和加密货币被盗。他们已识别出多个恶意游戏,并正在联系受害者。 检查一下是否符合要求:没有使用特定的开头词,直接描述内容;控制在100字以内;涵盖主要信息:FBI、Steam、恶意软件、信息和加密货币被盗、识别出的游戏、联系受害者。 看起来没问题。现在写出来: FBI正在调查Steam平台上发现的多款恶意游戏,这些游戏中植入了窃取用户敏感数据(包括加密货币钱包和账户信息)的恶意软件。已确认的恶意游戏包括BlockBlasters、Chemia、Dashverse/DashFPS等。FBI呼吁曾安装过这些游戏或受影响的用户提交相关信息,并表示将保护受害者身份隐私。 </think> FBI正在调查Steam平台上发现的多款恶意游戏,这些游戏中植入了窃取用户敏感数据(包括加密货币钱包和账户信息)的恶意软件。已确认的恶意游戏包括BlockBlasters、Chemia、Dashverse/DashFPS等。FBI呼吁曾安装过这些游戏或受影响的用户提交相关信息,并表示将保护受害者身份隐私。 2026-3-13 21:15:55 Author: www.bleepingcomputer.com(查看原文) 阅读量:12 收藏

The FBI is asking gamers who installed Steam titles containing malware to provide information as part of an ongoing investigation into eight malicious games uploaded to the gaming platform.
In a notice published today by the FBI's Seattle Division, the agency said it is attempting to identify individuals who were affected after installing one of the malicious games on Steam between May 2024 and January 2026.
"The FBI's Seattle Division is seeking to identify potential victims installing Steam games embedded with malware. The FBI believes the threat actor primarily targeted users between the timeframe of May 2024 and January 2026," reads the notice.
"In the investigation, several games have been identified to include, BlockBlasters, Chemia, Dashverse/DashFPS, Lampy, Lunara, PirateFi, and Tokenova."
"If you and/or your minor dependent(s) were victimized from installing one of these games or have information relevant to this investigation, please fill out this short form."
The questionnaire indicates that the FBI is focused on cryptocurrency theft and account hijacks after the installation of the malware, asking questions about cryptocurrency transactions, compromised accounts, and stolen funds.
The form also asks for any screenshots of communications with individuals who promoted the games, which could help investigators track the stolen cryptocurrency and trace it to those who distributed the malware.
"The FBI is legally mandated to identify victims of federal crimes it investigates. Victims may be eligible for certain services, restitution, and rights under federal and/or state law. All identities of victims will be kept confidential," the FBI told BleepingComputer.
"The website and email listed in the mass notifications sent on March 12, 2026, are official and authorized by the FBI. At this time, the FBI is unable to provide specific details beyond the information referenced on the website in the email notification to customers."
The FBI is also asking anyone who knows someone who may have been affected to encourage them to submit an inquiry to [email protected].
BleepingComputer also sent questions to Valve about the investigation, but did not receive a reply to our email.
Malware hidden in Steam games
Multiple malicious games discovered on Steam over the past two years have distributed information-stealing malware designed to harvest credentials, cryptocurrency wallets, and other sensitive data from players' devices.
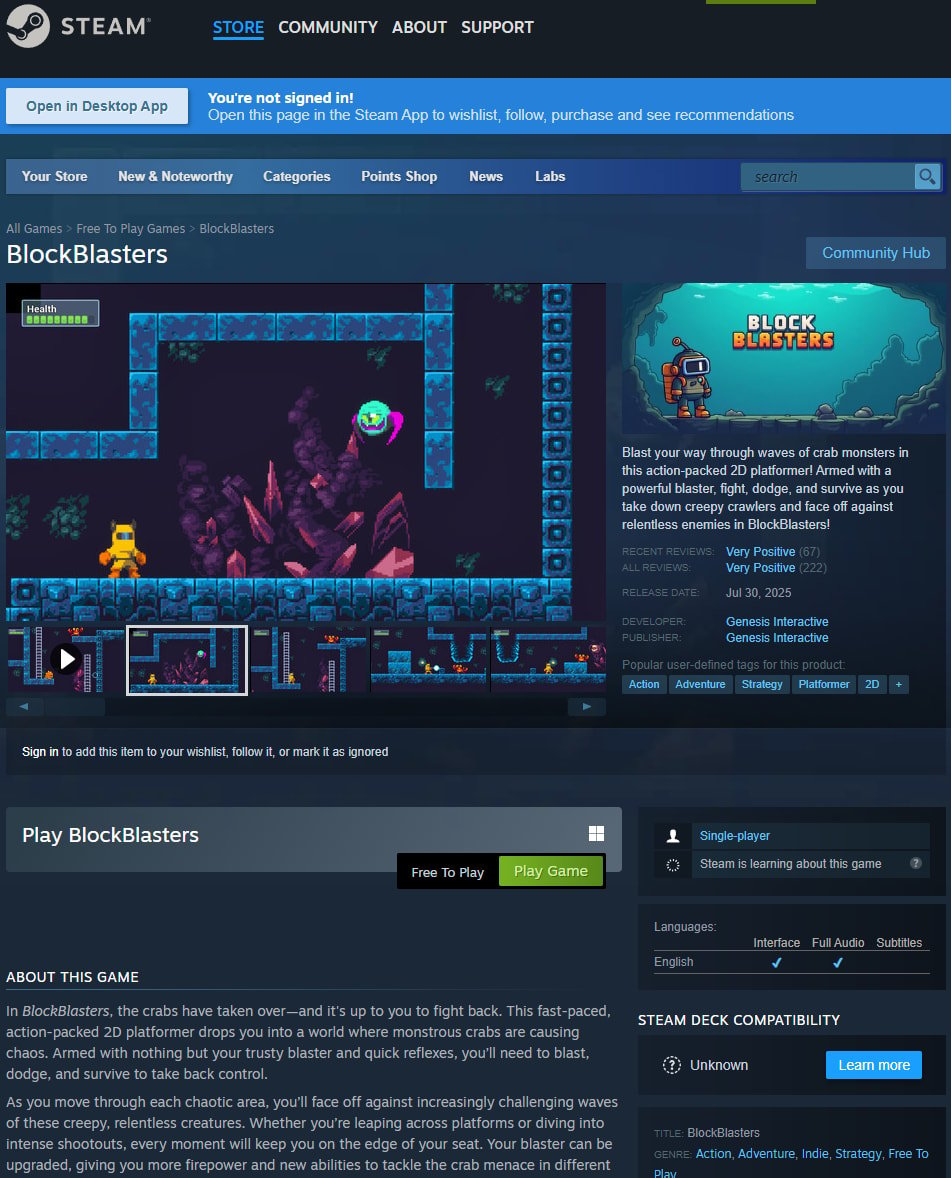
One of the most notable cases involved BlockBlasters, a free-to-play 2D platformer available on Steam from July to September 2024. While initially uploaded to Steam as a clean program, cryptodrainer malware was later added to the game.
News that the Steam game was malicious was revealed during a livestream by video game streamer Raivo Plavnieks (RastalandTV), who was raising money for cancer treatment.
After downloading the verified Steam game, the streamer reported losing more than $32,000 from his cryptocurrency wallet.
Blockchain investigator ZachXBT later estimated that attackers stole roughly $150,000 from 261 Steam accounts. Cybersecurity researcher VX-Underground later reported a higher count of 478 victims.
In the malicious Chemia survival crafting game, a threat actor known as EncryptHub added the HijackLoader malware, which downloaded the Vidar information stealer. It was later discovered that the game also installed EncryptHub's custom Fickle Stealer malware, which steals credentials, browser data, cookies, and cryptocurrency wallets.
The PirateFi game also distributed the Vidar infostealer and was available on Steam for about a week in February 2025. Up to 1,500 users may have downloaded the game before it was removed from Steam.
Steam later warned players who launched the game that malicious files may have been executed on their computers and advised them to run antivirus scans, review installed software, and consider reinstalling their operating system.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
