好的,我现在需要帮用户总结这篇文章的内容,控制在100个字以内。首先,我得仔细阅读文章,理解其主要信息。 文章讲的是Hive0163这个网络犯罪团伙使用了一种名为Slopoly的AI辅助恶意软件来进行勒索软件攻击。Slopoly是一个PowerShell后门,能够收集系统数据、执行命令,并保持持久访问。文章还提到Hive0163通过多种方式初始入侵,比如点击劫持、恶意广告等,并且他们使用的其他恶意软件和框架也被详细说明了。 接下来,我需要提取关键点:Hive0163使用AI辅助的Slopoly进行勒索攻击,Slopoly的功能包括收集数据、执行命令、保持持久性。此外,文章还提到未来AI在恶意软件中的应用可能带来的威胁。 现在我要把这些信息浓缩到100字以内,确保涵盖主要事件和影响。要注意用词简洁,避免冗余。 最后检查一下是否符合用户的要求:不需要特定的开头,直接描述内容,控制在100字内。 </think> Hive0163团伙利用AI辅助的Slopoly恶意软件进行勒索攻击,该软件可收集系统数据、执行命令并保持长期访问。研究人员发现其结构和注释表明AI生成的可能性,突显了威胁 actors 利用AI快速构建恶意软件的能力。 2026-3-13 11:36:29 Author: securityaffairs.com(查看原文) 阅读量:8 收藏
AI-assisted Slopoly malware powers Hive0163’s ransomware campaigns

The Hive0163 group used AI-assisted malware called Slopoly to maintain persistent access in ransomware attacks.
IBM X-Force researchers report that the financially motivated group Hive0163 is using AI-assisted malware named Slopoly to maintain persistent access during ransomware attacks, showing how threat actors can quickly build new malware frameworks using AI.
Hive0163 is a threat actor specializing in post-compromise activity, using multiple custom backdoors for long-term access, data exfiltration, and ransomware deployments. X-Force links the group to malware developers/operators such as Broomstick, Supper, PortStarter, SystemBC, and Rhysida ransomware, with several dynamic subclusters sharing crypters, malware frameworks, and ransomware variants. Initial access is often via ClickFix, malvertising, or brokers like TA569 and TAG-124.
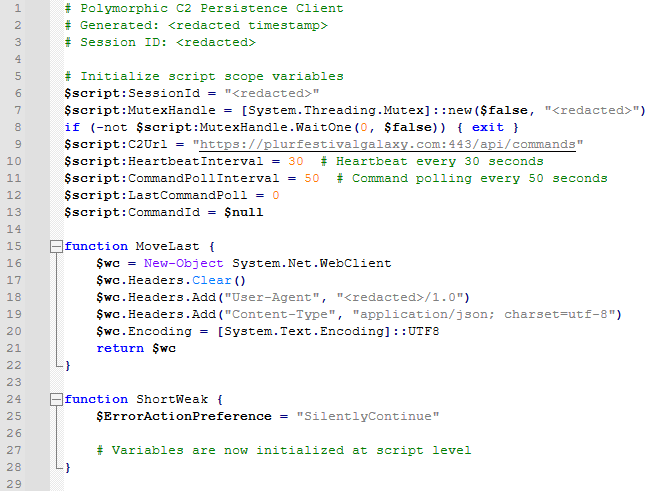
Researchers uncovered the PowerShell backdoor Slopoly during a ransomware investigation. Likely generated with an LLM, the malware acts as a C2 client that collects system data, sends heartbeat beacons to a remote server, executes commands via cmd.exe, and maintains persistence through a scheduled task.
Its structure and extensive comments strongly suggest AI-assisted development, highlighting how attackers can rapidly build operational malware.
“In early 2026, X-Force observed Hive0163 deploying a likely AI-generated malware dubbed “Slopoly” during a ransomware attack, allowing the group to maintain persistent access to the server for more than a week.” reads the report published by IBM. “Although still in the early stages, the adversarial use of AI is accelerating—and it’s poised to significantly reshape the threat landscape, forcing defenders to fundamentally rethink today’s security paradigms.”
The Windows Interlock ransomware is a 64-bit PE file deployed with the JunkFiction loader, typically in temporary folders. It supports arguments to encrypt directories (-d) or files (-f), delete itself (-del), run as a scheduled task (-s), release locked files (-r), or store session keys externally (-u). Interlock skips system directories and critical file types, uses AES-GCM per-file encryption combined with RSA-protected session keys, and leaves a ransom note (FIRST_READ_ME.txt).
The malware can stop processes via the Restart Manager API to encrypt locked files and deletes itself using an embedded DLL executed through rundll32.exe.
Researchers from IBM X-Force observed an intrusion starting with a ClickFix attack that tricked a victim into executing a malicious PowerShell command. The script deployed NodeSnake, part of a larger C2 framework used by Hive0163.
“NodeSnake is the first stage of a larger malware command-and-control (C2) framework heavily used by a threat actor tracked by X-Force as Hive0163. According to our observations, the framework spans a number of client implementations of varying capabilities in PowerShell, PHP, C/C++, Java and JavaScript for both Windows and Linux.” continues the report. “These components have widely been reported as “InterlockRAT” (Fortinet, eSentire) but despite its name, the final ransomware payloads may not be limited to Interlock only. “
NodeSnake downloaded additional payloads, including the more advanced InterlockRAT, which enables reverse shells, SOCKS5 tunneling, and remote command execution. The attackers later deployed Slopoly and tools such as AzCopy and Advanced IP Scanner to expand access and move laterally within the network.
Advancing LLMs lower software creation costs, including malware. AI acts as a force multiplier, enabling ephemeral, hard-to-attribute malware. Future threats include agentic AI and AI-integrated malware, raising risks for defenders as access to weaponized AI grows.
“Looking into the future, AI-generated malware is only the first stage in a new arms race between defenders and attackers. The second stage is the use of agentic AI, and AI-integrated malware, which allow models to make decisions during all phases of the attack chain or during development and testing of advanced C2 frameworks.” concludes the report. “These technological improvements are already being adopted in singular cases, either by highly-capable and well-resourced actors or as proof-of-concepts (PromptSpy, PromptLock, PROMPTFLUX, VoidLink). Similarly to the first stage of AI adoption, threat actors will integrate these into their attacks at varying timelines. While Hive0163 may still be in an early phase of AI adoption, the future potential of state-of-the-art AI technologies in the hands of an already highly disruptive threat actor poses an imminent risk to defenders.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Hive0163)
如有侵权请联系:admin#unsafe.sh

