
嗯,用户让我总结一篇文章的内容,控制在一百个字以内,而且不需要特定的开头。首先,我需要快速浏览文章内容,抓住主要信息。 文章讲的是一个新的恶意软件Slopoly,可能是用生成式AI工具制作的。它在一个被黑的服务器上潜伏了一周多,参与了Interlock勒索软件攻击。攻击过程从ClickFix诈骗开始,后来部署了Slopoly作为PowerShell脚本,作为C2框架的客户端。 IBM的研究人员分析了这个脚本,发现了很多AI生成的迹象,比如代码里的注释、结构化的日志、错误处理和清晰的变量名。这些在人类开发的恶意软件中很少见。他们认为这个恶意软件是由一个名为Hive0163的 financially motivated group开发的。 虽然Slopoly看起来并不复杂,但它的使用表明AI工具正在被用来加速定制恶意软件的发展。这可能帮助攻击者逃避检测。 总结的时候要抓住关键点:Slopoly是用AI生成的新恶意软件,在Interlock攻击中潜伏一周多,用于数据窃取和勒索。攻击链包括ClickFix和社会工程学。 </think> 一种新型恶意软件Slopoly可能由生成式AI工具创建,在Interlock勒索软件攻击中潜伏一周多用于数据窃取和勒索。该恶意软件以PowerShell脚本形式部署为C2框架客户端,具备系统信息收集、命令执行等功能,并通过社会工程学技术ClickFix启动攻击链。 2026-3-12 20:15:16 Author: www.bleepingcomputer.com(查看原文) 阅读量:13 收藏

A new malware strain dubbed Slopoly, likely created using generative AI tools, allowed a threat actor to remain on a compromised server for more than a week and steal data in an Interlock ransomware attack.
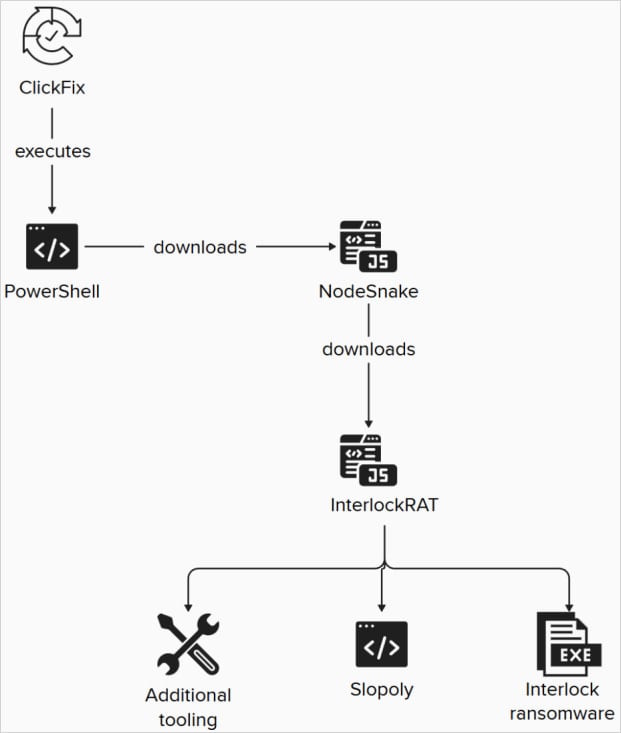
The breach started with a ClickFix ruse, and in later stages of the attack, the hackers deployed the Slopoly backdoor as a PowerShell script acting as a client for the command-and-control (C2) framework.
IBM X-Force researchers analyzed the script and found strong indicators that it was created using a large language model (LLM), but could not determine which one.
Evidence pointing to AI-assisted development includes extensive commentary in the code, structured logging, error handling, and clearly named variables. All this is rare in human-developed malware.
They attributed the attack to a financially motivated group they track as Hive0163, "whose main objective is extortion through large-scale data exfiltration and ransomware."
According to the researchers, Slopoly is rather unsophisticated, although its deployment in ransomware operators' attack chains indicates that AI tools are actively used to accelerate custom malware development, which can help evade detection.
Although comments in the Slopoly script describe it as a “Polymorphic C2 Persistence Client,” IBM X-Force did not find any feature that would allow modifying its own code during execution.
“The script does not possess any advanced techniques and can hardly be considered polymorphic, since it's unable to modify its own code during execution,” reads the IBM report.
“The builder may, however, generate new clients with different randomized configuration values and function names, which is standard practice among malware builders.”
IBM X-Force researchers believe that Slopoly was generated by a builder that inserted configuration values, such as beaconing intervals, command-and-control addresses, mutex names, and session IDs.
The malware is deployed in C:\ProgramData\Microsoft\Windows\Runtime\, and its main functions include:
- Collecting system information
- Sending a heartbeat beacon every 30 seconds to /api/commands
- Polling for commands every 50 seconds
- Executing received commands via cmd.exe
- Sending command output back to the C2 server
- Maintaining a rotating persistence.log file
- Establishing persistence through a scheduled task named “Runtime Broker”
The commands it supports allow downloading and executing EXE, DLL, or JavaScript payloads; running shell commands and returning the results; changing beaconing intervals; updating itself; or exiting its own process.
The attack IBM observed started with a ClickFix social engineering flow, and deployed multiple malware components besides Slopoly, including the NodeSnake and InterlockRAT backdoors.
Source: IBM X-Force
Interlock ransomware emerged in 2024 and was an early adopter of the ClickFix social engineering technique, and later also the FileFix variant.
The threat group has previously claimed attacks against high-profile organizations such as the Texas Tech University System, DaVita, Kettering Health, and the city of Saint Paul, Minnesota.
The Interlock ransomware payload observed in the attacks reported by IBM is a 64-bit Windows executable delivered via the JunkFiction loader.
It can execute as a scheduled task running as SYSTEM, and uses Windows Restart Manager API to release locked files, appending the ‘. !NT3RLOCK’ or ‘.int3R1Ock’ extensions on their encrypted copies.
IBM reports that Hive0163 may also have associations with the developers behind Broomstick, SocksShell, PortStarter, SystemBC, and the Rhysida ransomware operators.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
