嗯,用户让我帮忙总结一下这篇文章的内容,控制在一百个字以内,而且不需要用“文章内容总结”或者“这篇文章”这样的开头。直接写描述即可。 首先,我需要通读整篇文章,抓住主要信息。文章讲的是一个新的安卓恶意软件,叫做BeatBanker。它通过伪装成Starlink的应用程序,在模仿Google Play Store的网站上传播。一旦安装,它会劫持设备,窃取登录凭证,篡改加密货币交易,并秘密挖掘Monero币。目标主要是巴西用户,通过钓鱼页面和WhatsApp传播。攻击者还能长期监控和远程控制被感染的手机。 接下来,我需要把这些信息浓缩到100字以内。要确保包含关键点:恶意软件名称、传播方式、功能(劫持设备、窃取凭证、挖矿)、目标地区以及攻击者的能力。 然后,组织语言,使其简洁明了。比如,“BeatBanker恶意软件伪装成Starlink应用,在仿冒Google Play Store的网站传播。”接着说明它的功能,“劫持设备、窃取凭证、篡改加密交易并挖矿Monero币。”然后提到目标地区和攻击者的能力,“主要针对巴西用户,通过钓鱼和WhatsApp传播,允许攻击者长期监控和控制设备。” 最后检查字数是否在限制内,并确保没有使用不需要的开头。 </think> BeatBanker恶意软件伪装成Starlink应用,在仿冒Google Play Store的网站传播。它劫持设备、窃取凭证、篡改加密交易并挖矿Monero币。主要针对巴西用户,通过钓鱼和WhatsApp传播,允许攻击者长期监控和控制设备。 2026-3-11 19:0:23 Author: securityaffairs.com(查看原文) 阅读量:11 收藏
BeatBanker malware targets Android users with banking Trojan and crypto miner

BeatBanker Android malware spreads through fake Starlink apps on websites imitating Google Play Store, hijacking devices, stealing credentials, and mining crypto.
A new Android malware called BeatBanker spreads through fake Starlink apps distributed on websites posing as the Google Play Store. Once installed, it hijacks devices, steals login credentials, tampers with cryptocurrency transactions, and secretly mines Monero, combining banking trojan capabilities with crypto-mining.
The campaign mainly targets users in Brazil, spreading through phishing pages and sometimes via WhatsApp, allowing attackers to maintain long-term surveillance and remote control of compromised phones.
In newer attacks, operators replaced the banker component with a RAT and maintain persistence while communicating with mining pools.
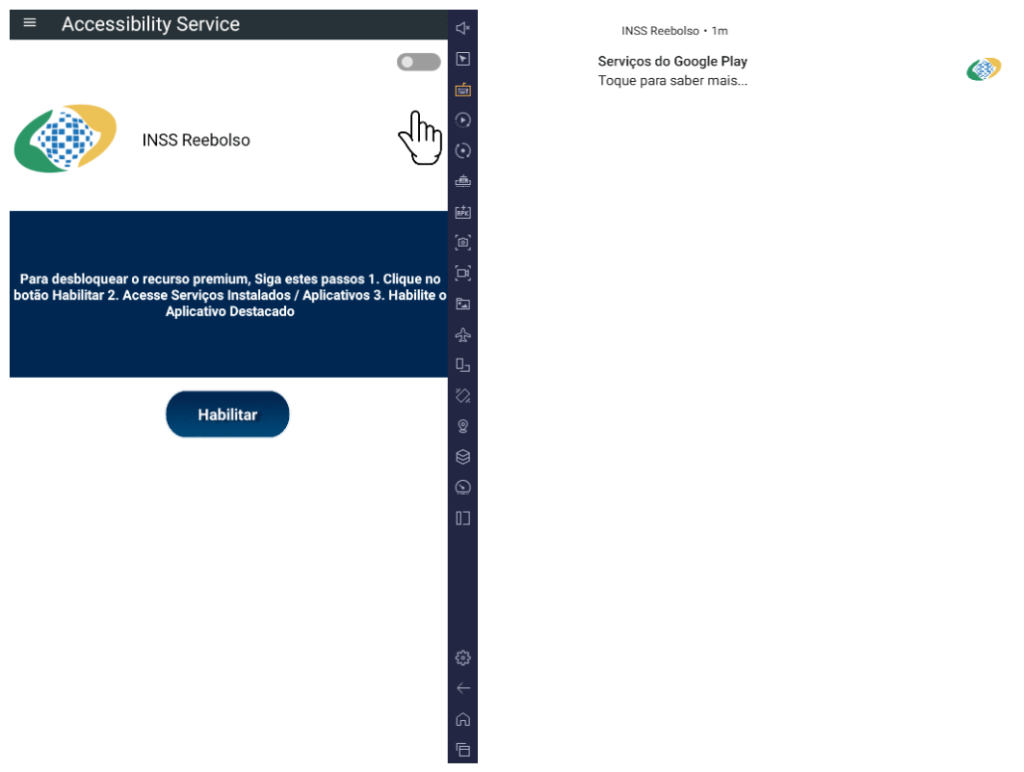
The campaign starts with a phishing site that mimics the Google Play Store and distributes a fake “INSS Reembolso” app.
The malware impersonates the official service of Instituto Nacional do Seguro Social, tricking users into installing a trojanized APK disguised as a trusted government app.
“At various stages of the attack, BeatBanker disguises itself as a legitimate application on the Google Play Store and as the Play Store itself.” states the report published by Kaspersky.

The packed APK uses a native library to decrypt and load hidden malware directly in memory, helping it evade mobile antivirus detection. It also checks device details and blocks execution in analysis environments. The app then shows a fake update page resembling the Google Play Store to trick victims into installing additional malicious payloads and maintain persistence.
After victims tap Update on a fake Google Play Store screen, the malware downloads a cryptominer based on XMRig and connects to attacker-controlled mining pools. It uses Firebase Cloud Messaging as a as its command-and-control channel. Each message triggers checks on battery level, temperature, installation date, and user activity, allowing attackers to start or stop the hidden crypto miner and keep infected devices responsive to remote commands while monitoring key device conditions.
BeatBanker maintains persistence by running a foreground service that plays a silent audio loop to avoid shutdown. It also installs a banking trojan that abuses accessibility permissions to control the device, monitor browsers, and target crypto apps such as Binance and Trust Wallet.
“BeatBanker compromises the machine with a cryptocurrency miner and introduces another malicious APK that acts as a banking Trojan. This Trojan uses previously obtained permission to install an additional APK called INSS Reebolso, which is associated with the package com.destination.cosmetics.” continues the report.
When users attempt Tether transfers, the malware overlays fake screens and silently replaces the destination wallet address with one controlled by the attackers.
Kaspersky detected new BeatBanker samples spreading through a fake Starlink app. The malware keeps earlier persistence tricks such as looped audio and fixed notifications and still deploys a crypto miner. Instead of a banking trojan, however, it now installs BTMOB RAT, a highly obfuscated remote access tool.
BTMOB, linked to malware families like CraxsRAT and CypherRAT, operates as Malware-as-a-Service and provides full control over infected devices. It can grant permissions automatically, run persistently in the background, hide notifications, capture screen-lock credentials, log keystrokes, track GPS location, and access cameras.
“BeatBanker is an excellent example of how mobile threats are becoming more sophisticated and multi-layered. Initially focused in Brazil, this Trojan operates a dual campaign, acting as a Monero cryptocurrency miner, discreetly draining your device’s battery life while also stealing banking credentials and tampering with cryptocurrency transactions.” concludes the report that includes Indicators of Compromise (IoCs). “Moreover, the most recent version goes even further, substituting the banking module with a full-fledged BTMOB RAT.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, BeatBanker Android malware)
如有侵权请联系:admin#unsafe.sh
