Our malware removal support team recently flagged a new wave of sextortion emails, with the subject line: “You pervert, I recorded you!”
If the message sounds familiar, that’s because it’s a variation of the long-running “Hello pervert” scam.
The email claims the target’s device has been infected by a “drive-by exploit,” which supposedly gave the extortionist full access to the device. To add credibility, the scammer includes a password that actually belongs to the target.
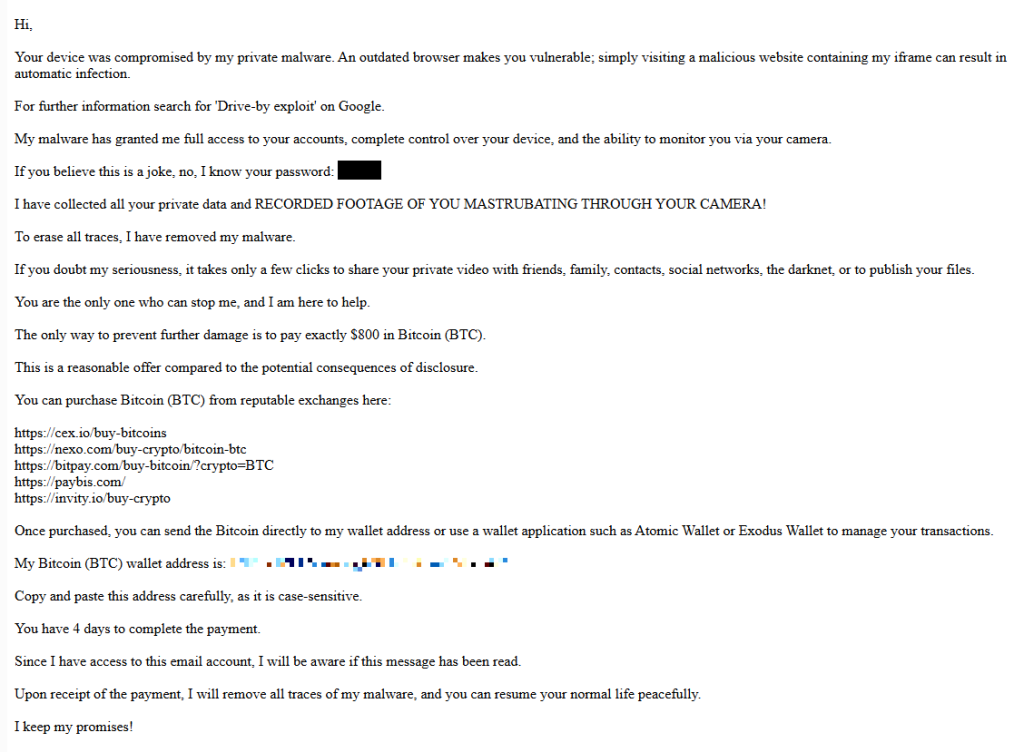
Here’s one of the emails:
Your device was compromised by my private malware. An outdated browser makes you vulnerable; simply visiting a malicious website containing my iframe can result in automatic infection.
For further information search for ‘Drive-by exploit’ on Google.
My malware has granted me full access to your accounts, complete control over your device, and the ability to monitor you via your camera.
If you believe this is a joke, no, I know your password: {an actual password}
I have collected all your private data and RECORDED FOOTAGE OF YOU MASTRUBATING THROUGH YOUR CAMERA!
To erase all traces, I have removed my malware.
If you doubt my seriousness, it takes only a few clicks to share your private video with friends, family, contacts, social networks, the darknet, or to publish your files.
You are the only one who can stop me, and I am here to help.
The only way to prevent further damage is to pay exactly $800 in Bitcoin (BTC).
This is a reasonable offer compared to the potential consequences of disclosure.
You can purchase Bitcoin (BTC) from reputable exchanges here:
{list of crypto-currency exchanges}
Once purchased, you can send the Bitcoin directly to my wallet address or use a wallet application such as Atomic Wallet or Exodus Wallet to manage your transactions.
My Bitcoin (BTC) wallet address is: {bitcoin wallet which has received 1 payment at the time of writing}
Copy and paste this address carefully, as it is case-sensitive.
You have 4 days to complete the payment.
Since I have access to this email account, I will be aware if this message has been read.
Upon receipt of the payment, I will remove all traces of my malware, and you can resume your normal life peacefully.
I keep my promises!
The message is a bit contradictory. Early on, the sender claims they have already removed the malware to “erase all traces,” but later promises to remove it after receiving payment.
Where the password comes from
I found that one particular sender using the name Jenny Green and the Gmail address [email protected] sent many of these emails to people that use the FakeMailGenerator service.
FakeMailGenerator is a free disposable email service that gives users a temporary, receive‑only inbox they can use instead of their real address, mainly to get around email confirmations or avoid spam.
As mentioned, the addresses are receive‑only, meaning they cannot legitimately send mail and the mailbox is not tied to a specific person. On top of that, there is no login. Anyone who knows the address (or guesses the inbox URL) can see the same inbox.
My guess is that the scammer searched these public inboxes for passwords and then reused those passwords in their sextortion emails.
So users of FakeMailGenerator and similar services should consider this a warning. Your inbox may be publicly accessible, show up in search results, and you may receive a lot more than what you signed up for. Definitely don’t use services like this for anything sensitive.
How to stay safe
Knowing these scams exist is the first step to avoiding them. Sextortion emails rely on panic and embarrassment to push people into paying quickly. Here are a few simple steps to protect yourself:
- Don’t rush. Scammers rely on fear and urgency. Take a moment to think before reacting.
- Don’t reply to the email. Responding tells the attacker that someone is reading messages at that address, which may lead to more scams.
- Change your password if it appears in the email. If you still use that password anywhere, update it.
- Use a password manager. If you’re having trouble generating or storing a strong password, have a look at a password manager.
- Don’t open unsolicited attachments. Especially when the sender address is suspicious or even your own.
- Don’t use disposable inboxes for important accounts. The mail in that inbox might be available for anyone to find.
- For peace of mind, turn your webcam off or buy a webcam cover so you can cover it when you’re not using the webcam.
Pro tip: Malwarebytes Scam Guard immediately recognized this for what it is: a sextortion scam.
What do cybercriminals know about you?
Use Malwarebytes’ free Digital Footprint scan to see whether your personal information has been exposed online.