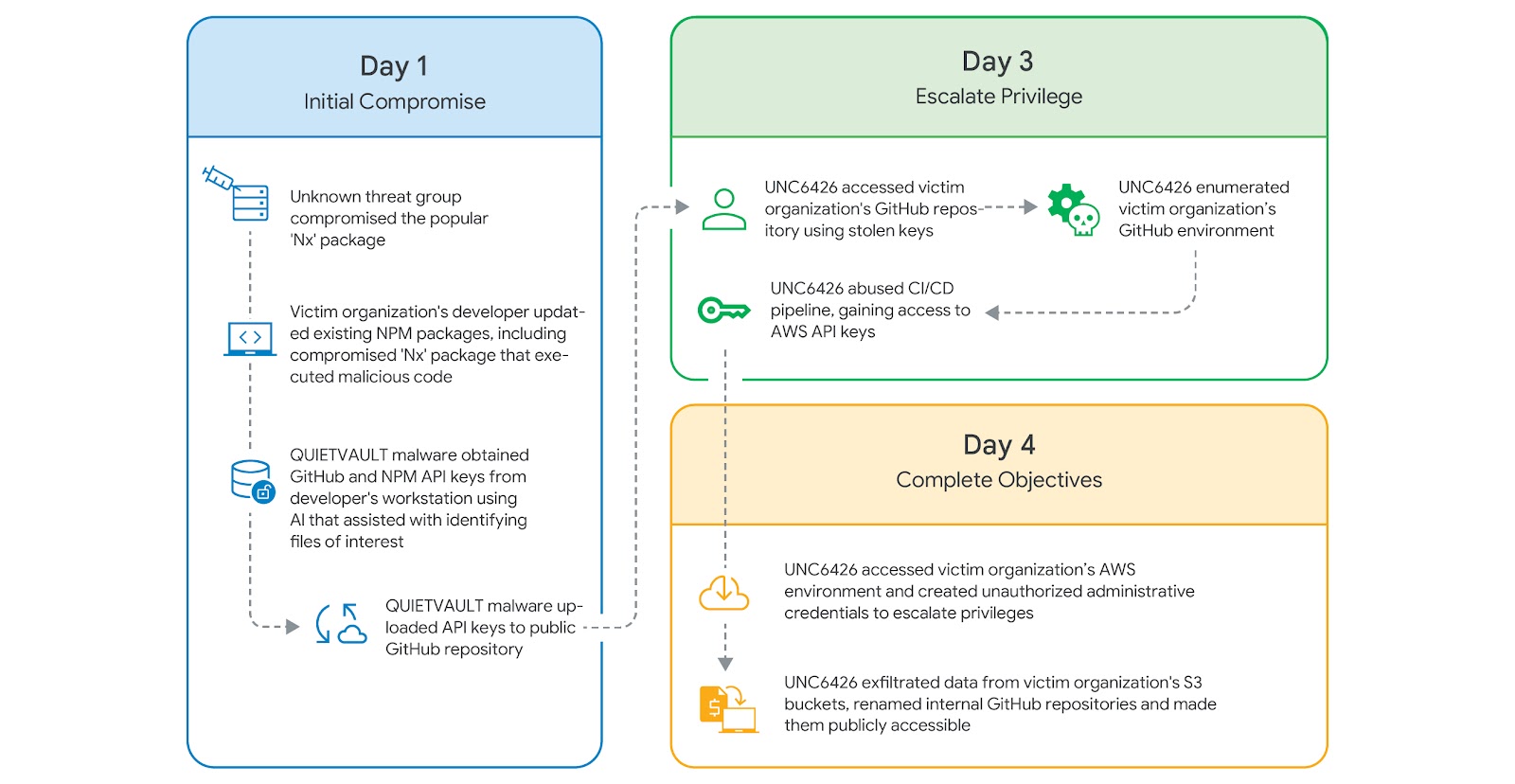
A threat actor known as UNC6426 leveraged keys stolen following the supply chain compromise of the nx npm package last year to completely breach a victim's cloud environment within a span of 72 hours.
The attack started with the theft of a developer's GitHub token, which the threat actor then used to gain unauthorized access to the cloud and steal data.
"The threat actor, UNC6426, then used this access to abuse the GitHub-to-AWS OpenID Connect (OIDC) trust and create a new administrator role in the cloud environment," Google said in its Cloud Threat Horizons Report for H1 2026. "They abused this role to exfiltrate files from the client's Amazon Web Services (AWS) Simple Storage Service (S3) buckets and performed data destruction in their production cloud environments."
The supply chain attack targeting the nx npm package took place in August 2025, when unknown threat actors exploited a vulnerable pull_request_target workflow – an attack type referred to as Pwn Request – to obtain elevated privileges and access sensitive data, including a GITHUB_TOKEN, and ultimately push trojanized versions of the package to the npm registry.
The packages were found to embed a postinstall script that, in turn, launched a JavaScript credential stealer named QUIETVAULT to siphon environment variables, system information, and valuable tokens, including GitHub Personal Access Tokens (PATs), by weaponizing a Large Language Model (LLM) tool already installed on the endpoint to perform the search. The data was uploaded to a public GitHub repository named "/s1ngularity-repository-1."
Google said an employee at the victim organization ran a code editor application that used the Nx Console plugin, triggering an update in the process and resulting in the execution of QUIETVAULT.
UNC6426 is said to have initiated reconnaissance activities within the client's GitHub environment using the stolen PAT two days after the initial compromise using a legitimate open-source tool called Nord Stream to extract secrets from CI/CD environments, leaking the credentials for a GitHub service account.
Subsequently, the attackers leveraged this service account and used the utility's "--aws-role" parameter to generate temporary AWS Security Token Service (STS) tokens for the "Actions-CloudFormation" role and ultimately allow them to obtain a foothold in the victim's AWS environment.
"The compromised Github-Actions-CloudFormation role was overly permissive," Google said. "UNC6426 used this permission to deploy a new AWS Stack with capabilities ["CAPABILITY_NAMED_IAM","CAPABILITY_IAM"]. This stack's sole purpose was to create a new IAM role and attach the arn:aws:iam::aws:policy/AdministratorAccess policy to it. UNC6426 successfully escalated from a stolen token to full AWS administrator permissions in less than 72 hours."
Armed with the new administrator roles, the threat actor carried out a series of actions, including enumerating and accessing objects within S3 buckets, terminating production Elastic Compute Cloud (EC2) and Relational Database Service (RDS) instances, and decrypting application keys. In the final stage, all of the victim's internal GitHub repositories were renamed to "/s1ngularity-repository-[randomcharacters]" and made public.
To counter such threats, it's advised to use package managers that prevent postinstall scripts or sandboxing tools, apply the principle of least privilege (PoLP) to CI/CD service accounts and OIDC-linked roles, enforce fine-grained PATs with short expiration windows and specific repository permissions, remove standing privileges for high-risk actions like creating administrator roles, monitor for anomalous IAM activity, and implement strong controls to detect Shadow AI risks.
The incident highlights a case of what has been described by Socket as an AI-assisted supply chain abuse, where the execution is offloaded to AI agents that already have privileged access to the developer's file system, credentials, and authenticated tooling.
"The malicious intent is expressed in natural-language prompts rather than explicit network callbacks or hard-coded endpoints, complicating conventional detection approaches," the software supply chain security firm said. "As AI assistants become more integrated into developer workflows, they also expand the attack surface. Any tool capable of invoking them inherits their reach."
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.