
嗯,用户让我帮忙总结一篇关于Android恶意软件BeatBanker的文章,控制在100字以内。首先,我需要仔细阅读文章内容,抓住关键点。 文章提到BeatBanker伪装成Starlink应用,通过仿冒Google Play Store的网站传播。它结合了银行木马和门罗币挖矿功能,能窃取凭证并篡改加密交易。卡巴斯基的研究人员在巴西发现这个恶意软件,最新的版本使用了BTMOB RAT远程访问木马,提供全面的设备控制功能。 此外,BeatBanker通过播放几乎听不见的MP3文件来维持持久性,避免被系统终止。它还使用XMRig矿机在设备上挖矿,并通过Firebase Cloud Messaging监控设备状态以保持隐蔽。 总结时要涵盖传播方式、功能、技术手段和防范建议。确保语言简洁明了,不超过100字。 </think> 一种新型Android恶意软件BeatBanker伪装成Starlink应用通过仿冒Google Play Store的网站传播。它结合银行木马和门罗币挖矿功能窃取凭证并篡改加密交易。最新版本使用BTMOB RAT远程访问木马实现全面设备控制,并通过持续播放MP3文件维持持久性以避免被终止。 2026-3-10 21:30:17 Author: www.bleepingcomputer.com(查看原文) 阅读量:18 收藏

A new Android malware named BeatBanker can hijack devices and tricks users into installing it by posing as a Starlink app on websites masquerading as the official Google Play Store.
The malware combines banking trojan functions with Monero mining, and can steal credentials, as well as tamper with cryptocurrency transactions.
Kaspersky researchers discovered BeatBanker in campaigns targeting users in Brazil. They also found that the most recent version of the malware deploys the commodity Android remote access trojan called BTMOB RAT, instead of the banking module.
BTMOB RAT provides operators with full device control, keylogging, screen recording, camera access, GPS tracking, and credential-capture capabilities.
Persistence via MP3
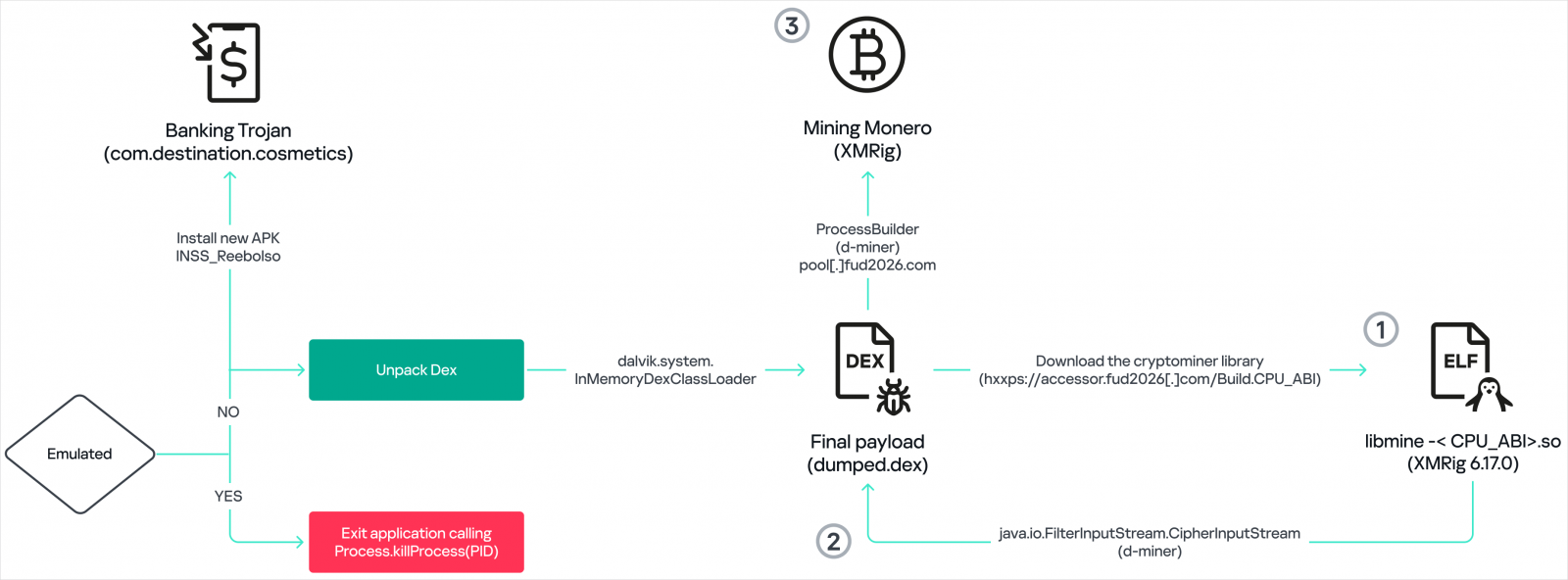
BeatBanker is distributed as an APK file that uses native libraries to decrypt and load hidden DEX code directly into memory, for evasion.
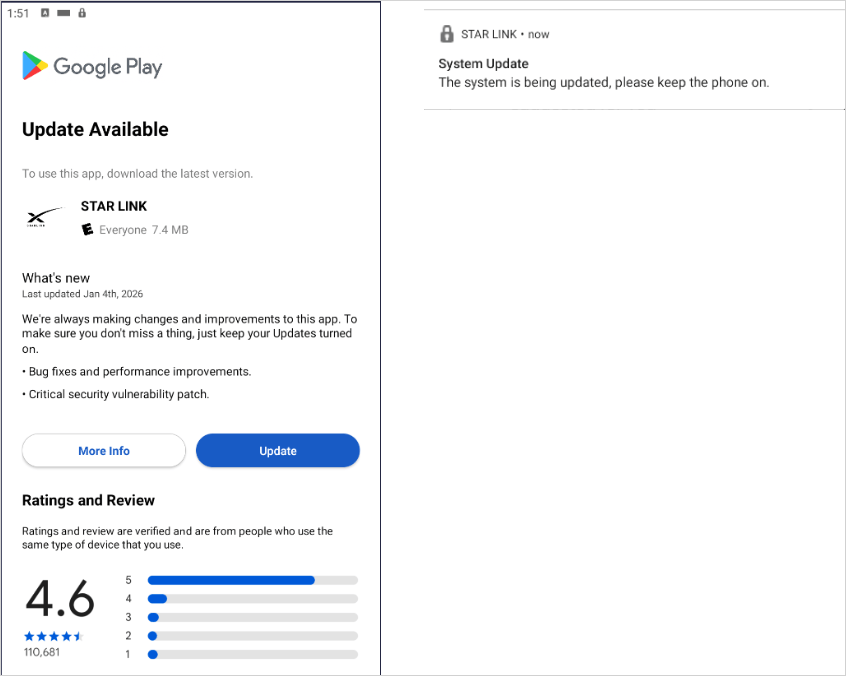
Before launching, it performs environment checks to ensure it’s not being analyzed. If passed, it displays a fake Play Store update screen to trick the victims into granting it permissions to install additional payloads.
Source: Kaspersky
To avoid triggering any alarms, BeatBanker delays malicious operations for a period after its installation.
According to Kaspersky, the malware has an unusual method to maintain persistence, which consists of continuously playing a nearly inaudible 5-second recording of Chinese speech from an MP3 file named output8.mp3.
“The KeepAliveServiceMediaPlayback component ensures continuous operation by initiating uninterrupted playback via MediaPlayer,” Kaspersky explains in a report today.
“It keeps the service active in the foreground using a notification and loads a small, continuous audio file. This constant activity prevents the system from suspending or terminating the process due to inactivity.”
Stealthy cryptocurrency mining
BeatBanker uses a modified XMRig miner version 6.17.0, compiled for ARM devices, to mine Monero on Android devices. XMRig connects to attacker-controlled mining pools using encrypted TLS connections, and falls back to a proxy if the primary address fails.
Source: Kaspersky
The miner can be dynamically started or stopped based on device conditions, which the operators closely monitor to ensure optimal operation and maintain stealth.
Using Firebase Cloud Messaging (FCM), the malware continuously sends the command-and-control (C2) server information about the device’s battery level and temperature, charging status, usage activity, and whether it has overheated.
By stopping mining when the device is in use and by limiting its physical impact, the malware can remain hidden for a longer period, mining for cryptocurrency when conditions allow it.
While Kaspersky observed all BeatBanker infections in Brazil, the malware could expand to other countries if proven effective, so vigilance and good security practices are recommended.
Android users shouldn’t side-load APKs from outside the official Google Play store unless they trust the publisher/distributor, should review granted permissions for risky ones that aren’t relevant to the app’s functionality, and perform regular Play Protect scans.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
