2026-03-10
4 min read
Every new domain, application, website, or API endpoint increases an organization's attack surface. For many teams, the speed of innovation and deployment outpaces their ability to catalog and protect these assets, often resulting in a "target-rich, resource-poor" environment where unmanaged infrastructure becomes an easy entry point for attackers.
Replacing manual, point-in-time audits with automated security posture visibility is critical to growing your Internet presence safely. That’s why we are happy to announce a planned integration that will enable the continuous discovery, monitoring and remediation of Internet-facing blind spots directly in the Cloudflare dashboard: Mastercard’s RiskRecon attack surface intelligence capabilities.
Information Security practitioners in pay-as-you-go and Enterprise accounts will be able to preview the integration in the third quarter of 2026.
Attack surface intelligence can spot security gaps before attackers do
Mastercard’s RiskRecon attack surface intelligence identifies and prioritizes external vulnerabilities by mapping an organization's entire internet footprint using only publicly accessible data. As an outside-in scanner, the solution can be deployed instantly to uncover "shadow IT," forgotten subdomains, and unauthorized cloud servers that internal, credentialed scans often miss. By seeing what an attacker sees in real time, security teams can proactively close security gaps before they can be exploited.
But what security gaps are attackers typically looking to exploit? In a 2025 study of 15,896 organizations that had experienced security breaches, Mastercard found that unpatched software, exposed services (e.g. databases, remote administration), weak application security (e.g. missing authentication) and outdated web encryption were frequent hallmarks, as seen in the graph below.
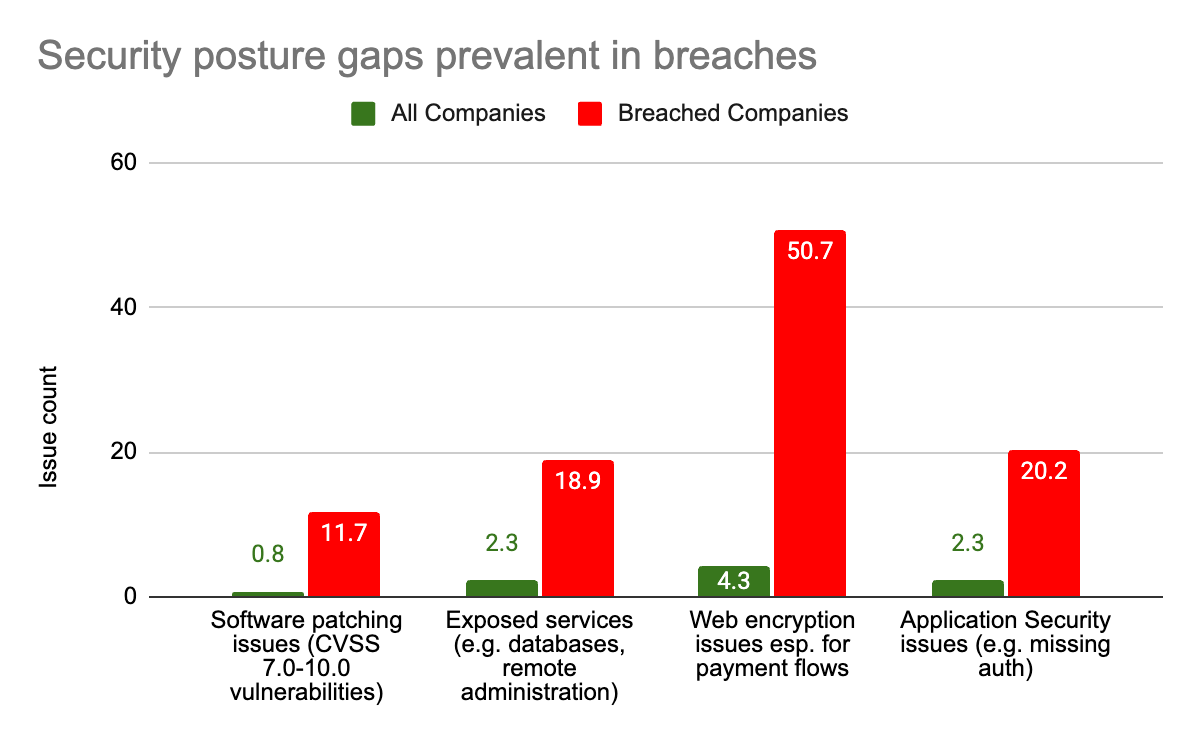
The same study also found that organizations with significant cybersecurity posture gaps in these areas were 5.3x more likely to be hit by a ransomware attack, and 3.6x more likely to suffer a data breach compared to companies that maintain good cybersecurity hygiene.
Why Cloudflare and Mastercard are partnering
This partnership combines Mastercard’s attack surface intelligence—which identifies security gaps—with Cloudflare’s ability to fix them. Organizations can use Mastercard’s data to find shadow assets, such as forgotten domains or unprotected cloud instances, and secure them by routing traffic through Cloudflare’s proxy. This allows for the immediate deployment of security controls without changing the underlying website or application.
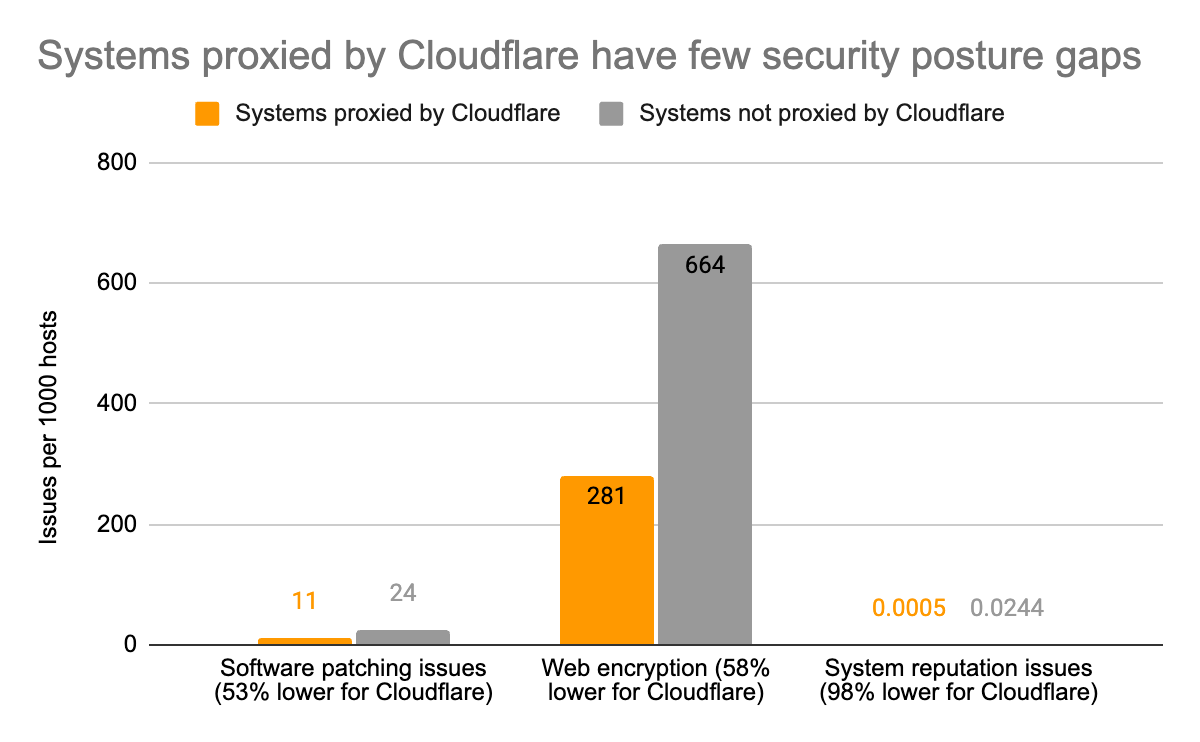
Based on a sample of approximately 388,000 organizations spanning over 18 million systems, Mastercard’s attack surface intelligence shows that systems using Cloudflare as a proxy have significantly better security hygiene than those that do not:
Software Patching: 53% fewer software vulnerabilities
Web Encryption: 58% fewer SSL/TLS issues
System Reputation: 98% fewer instances of malicious behavior (e.g. communicating with botnet command and control servers, hosting phishing sites).
The table below provides additional details on the security posture insights provided by Mastercard. These insights are generated by passively scanning publicly accessible hosts, web applications, and configurations.
| Category | Security Check | Description |
|---|---|---|
| Software Patching | Application Servers | Unpatched application server software. |
| OpenSSL | Unpatched OpenSSL. | |
| CMS Patching | Unpatched content management system software. | |
| Web Servers | Unpatched webserver software. | |
| Application Security | CMS Authentication | Enumeration of content management system administration interfaces publicly exposed to the internet. |
| High Value System Encryption | Enumeration of systems that collect sensitive data that do not have encryption implemented. | |
| Malicious Code | Enumeration of systems containing malicious code (Magecart). | |
| Web Encryption | Certificate Expiration Date | SSL certificate expired. |
| Certificate Valid Date | SSL certificate valid date not yet valid. | |
| Encryption Hash Algorithm | Weak SSL encryption hash algorithm. | |
| Encryption Key Length | Weak SSL encryption key length. | |
| Certificate Subject | Invalid SSL certificate subject. | |
| Exposed Services / Network Filtering | Unsafe Network Services | Enumeration of unsafe network services running on the system such as databases (e.g. SQL Server, PostgreSQL) and remote access services (e.g. RDP, VNC). |
| IoT Devices | Enumeration of IoT devices such as printers, embedded system interfaces, etc. |
Comprehensive domain discovery, continuous posture visibility, and remediation
Cloudflare Security Insights in Cloudflare’s Application Security suite currently identifies risks—such as DNS misconfigurations, weak web encryption, or inactive WAF rules—for any domain already proxied by Cloudflare. However, a significant security gap remains: you cannot protect domains you don’t know exist.
The integration with Mastercard will eliminate these blind spots. By continuously profiling the Internet footprint of over 12 million organizations, Mastercard identifies domains, hosts, and software stacks associated with your company, even if they aren't yet behind a Cloudflare proxy. This will allow Security Insights to surface shadow IT and unprotected hosts, enabling you to secure them with Cloudflare’s WAF and DDoS protection.
Visibility is only the first step; understanding the criticality of discovered assets is what allows security teams to prioritize findings. Each host is assigned a criticality level:
High Criticality: Assigned to hosts that collect sensitive data, require authentication, or run sensitive network services like database listeners or remote access.
Medium Criticality: Assigned to hosts running brochure websites that are adjacent to high-criticality systems, such as those residing on the same class-C network.
Low Criticality: Assigned to hosts running brochure websites that are not adjacent to any critical systems.
Below is a fictitious example of an organization with many domains that they are unaware of. Of these discovered domains, only one is currently proxied by Cloudflare. Within Security Insights, you will be able to visualize this level of detail for shadow domains and hosts.
| Domain | Protected by Cloudflare | Host (IP) | Criticality | Location | Hosting Provider |
|---|---|---|---|---|---|
| search-engine.net | Yes | portal.search-engine.net (10.XXX.XX.5) | HIGH | Springfield, United States | Cloudflare |
| zenith-industries.com | No | vpn.zenith-industries.com (10.XXX.XXX.106) | HIGH | Helsinki, Finland | CloudNode-Services |
| stratus-global.com | No | store.stratus-global.com (10.XXX.XXX.124) | HIGH | Munich, Germany | SwiftStream-Tech |
| core-logic.cl | No | extranet.core-logic.cl (10.XXX.XXX.178) | HIGH | Santiago, Chile | SecureCanopy Ltd. |
| vanguard-labs.com | No | extranet.vanguard-labs.com (10.XXX.XX.197) | HIGH | Metropolis, United States | GlobalSoft Systems |
| fusion-id.com | No | fusion-id.com (10.XXX.XXX.146) | HIGH | Prague, Czechia | EuroData-Hub |
| norden-biotech.no | No | store.norden-biotech.no (10.XXX.XX.124) | MEDIUM | Chicago, United States | SwiftStream-Tech |
| norden-biotech.se | No | store.norden-biotech.se (10.XXX.XX.124) | MEDIUM | Chicago, United States | SwiftStream-Tech |
Example of shadow domains and unprotected hosts associated with an organization
Mastercard will also allow continuous visibility into the security posture of Internet-facing systems including in areas like software patching, exposed network services (e.g., databases, remote access) and application security (e.g., unauthenticated CMSes) — complementing Cloudflare Security Insights, as shown below.
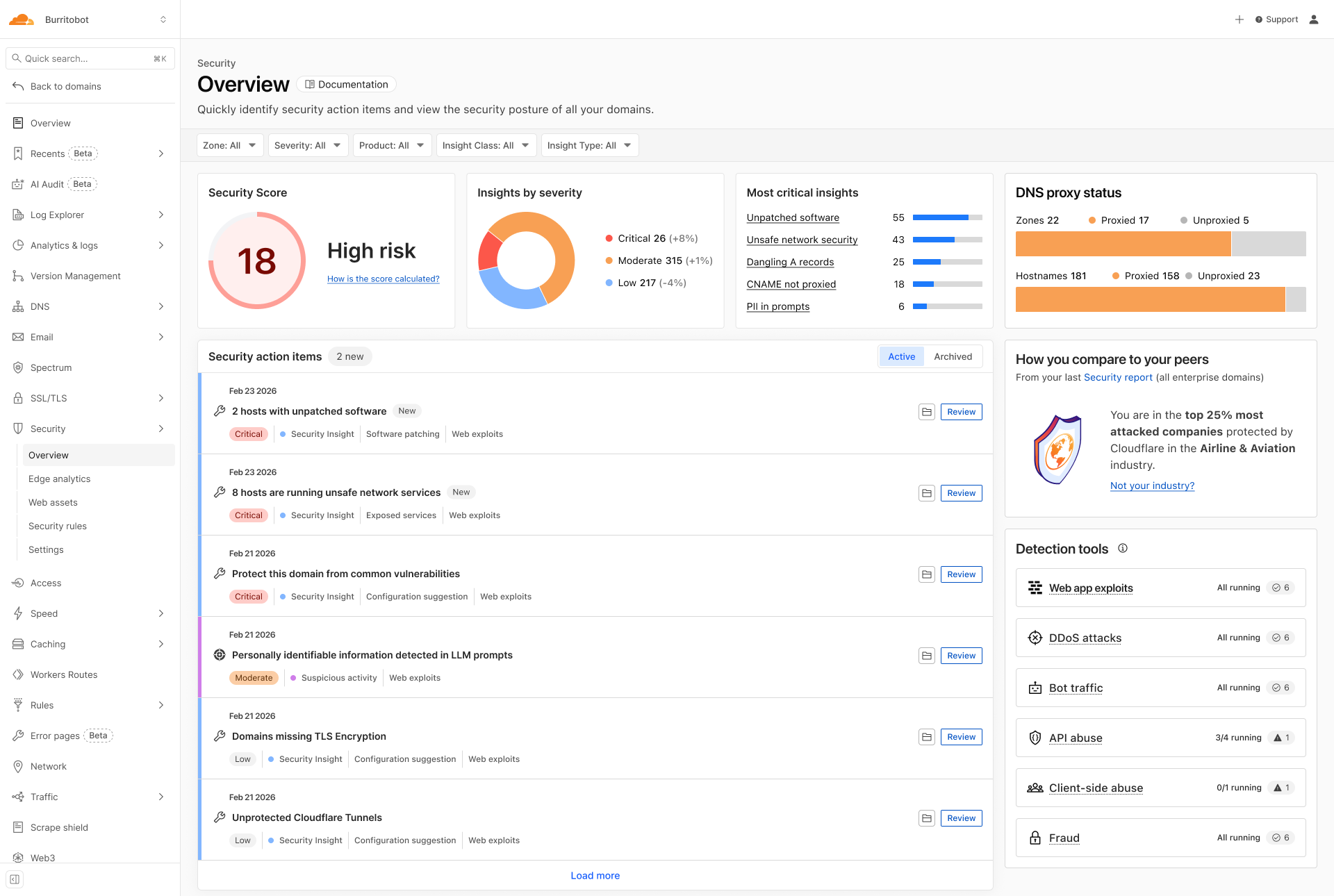
Security Insights dashboard with shadow domains, unproxied hosts, and posture findings
These insights are only useful if they lead to action. Instead of just telling you that a domain or host is at risk, Cloudflare Security Insights will guide you to fixing them. Possible steps include enabling a Cloudflare proxy (and by extension DDoS and bot protection for shadow zones and hosts), enabling security controls (such as turning on the Web Application Firewall, or WAF) and enforcing stricter TLS encryption to mitigate the specific risks identified by the scan.
What’s next: updated security insights dashboard
We are currently working on integrating Mastercard’s RiskRecon attack surface intelligence into the Cloudflare Security Insights dashboard to provide immediate visibility into shadow domains, unprotected hosts and the posture gaps associated with them.
With an increasing volume of insights, our roadmap also includes risk scoring and building AI-assisted diagnosis paths. That will mean a dashboard that doesn't just show you an insight, but proposes additional relevant correlations (such as traffic to an unpatched host) and suggests the specific WAF rule or API Shield configuration required to neutralize it.
We would love to have you join the waitlist here.
Cloudflare's connectivity cloud protects entire corporate networks, helps customers build Internet-scale applications efficiently, accelerates any website or Internet application, wards off DDoS attacks, keeps hackers at bay, and can help you on your journey to Zero Trust.
Visit 1.1.1.1 from any device to get started with our free app that makes your Internet faster and safer.
To learn more about our mission to help build a better Internet, start here. If you're looking for a new career direction, check out our open positions.