
好的,我现在需要帮用户总结一篇文章的内容,控制在100个字以内。用户的要求是直接写文章描述,不需要开头用“文章内容总结”之类的。首先,我得仔细阅读文章,抓住主要信息。 文章讲的是俄罗斯国家支持的APT28组织使用定制版的Covenant框架进行间谍活动。他们还用了BeardShell和Covenant这两个恶意软件,主要针对乌克兰政府机构。攻击利用了CVE-2026-21509漏洞,通过恶意DOC文件传播。 此外,BeardShell使用Icedrive云存储进行C2通信,并且有独特的混淆技术。Covenant经过大量修改,用于长期监视。ESET指出这些变化包括确定性标识符、修改执行流程以逃避检测,以及新的云通信协议。 总结时要包含关键点:APT28、定制Covenant、BeardShell、针对乌克兰、利用漏洞、云存储通信、混淆技术、长期监视能力。确保在100字以内准确传达这些信息。 </think> 俄罗斯国家支持的APT28组织利用定制版Covenant框架和BeardShell恶意软件,针对乌克兰政府机构展开间谍活动。攻击通过恶意DOC文件利用Microsoft Office漏洞CVE-2026-21509传播,并结合Icedrive云存储进行命令控制通信。BeardShell采用独特混淆技术,而Covenant经过大幅修改以增强长期监视能力。 2026-3-10 10:15:19 Author: www.bleepingcomputer.com(查看原文) 阅读量:7 收藏

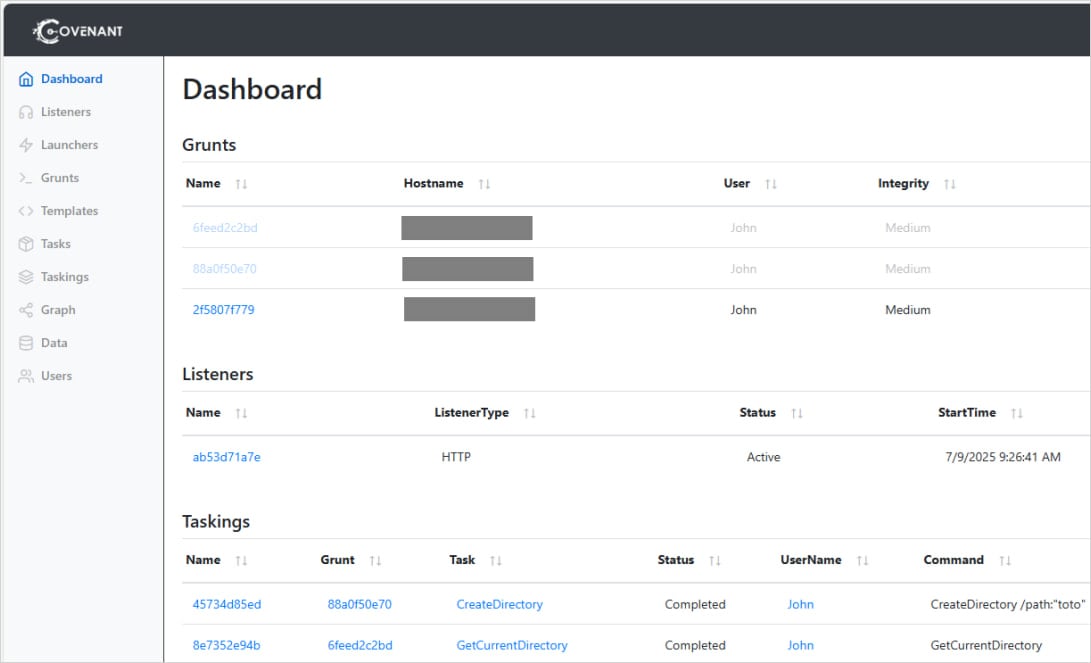
The Russian state-sponsored APT28 threat group is using a custom variant of the open-source Covenant post-exploitation framework for long-term espionage operations.
Also tracked as Fancy Bear, Forest Blizzard, Strontium, and Sednit, the APT28 hacker group is known for developing high-end implants and breaching notable entities, such as the German Parliament, multiple French organizations, government networks in Poland, and European NATO member countries.
Researchers at cybersecurity company ESET noticed that since April 2024, the Russian group has started using in attacks two implants named BeardShell and Covenant.
"This dual-implant approach enabled long-term surveillance of Ukrainian military personnel," ESET notes in a report today.
The two pieces of malware have been used recently to target central executive bodies of Ukraine in attacks that exploited the CVE-2026-21509 vulnerability in Microsoft Office via malicious DOC files.
The researchers uncovered these malware families after discovering SlimAgent, a keylogging implant deployed in a Ukrainian government system capable of keystroke capture, clipboard collection, and screenshot capture.
BeardShell is a modern implant that leverages the legitimate cloud storage service Icedrive for command-and-control (C2) communication. It can execute PowerShell commands in a .NET runtime environment and was used together with SlimAgent, according to a report from CERT-UA in June 2025.
ESET found that BeardShell also uses a unique obfuscation technique previously seen in Xtunnel, a network-pivoting tool that APT28 used in the 2010s.
In the recent attacks, the Russian threat group paired BeardShell with a heavily modified version of the open-source Covenant .NET post-exploitation framework.
The changes they introduced include deterministic implant identifiers tied to host characteristics, modified execution flow to evade behavioral detection, and new cloud-based communication protocols.
Since July 2025, the threat actor has used the Filen cloud provider with Covenant. Previously, the attacker used Koofr and pCloud services.
Source: ESET
ESET says Covenant is used as the primary implant, and BearShell serves as the fallback tool.
“Since 2023, Sednit developers have made a number of modifications and experiments with Covenant to establish it as their primary espionage implant, keeping BeardShell mainly as a fallback in case Covenant encounters operational issues, such as the takedown of its cloud-based infrastructure.” - ESET
ESET believes that APT28’s advanced malware development team returned to activity in 2024, giving the threat group new long-term espionage capabilities. The technical similarities with 2010-era malware indicate continuity in the threat group’s development team.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
