ANY.RUN’s analysts are observing a sharp increase in phishing activity abusing Microsoft’s OAuth Device Code flow, with more than 180 phishing URLs detected in just one week.
This technique represents a shift from credential phishing to token-based account takeover, making detection significantly harder for many SOC teams.
Key Takeaways
- OAuth Device Code phishing is rising rapidly. Campaigns abusing Microsoft’s Device Authorization Grant are increasing, with hundreds of phishing URLs appearing in short timeframes.
- Account takeover can occur without credential theft. Victims authenticate on legitimate Microsoft pages, yet attackers still receive OAuth tokens that grant account access.
- The attack abuses legitimate authentication flows. Threat actors initiate the device authorization process themselves and trick victims into approving it.
- Token abuse replaces password theft. Access tokens and refresh tokens allow attackers to operate within Microsoft 365 without needing stolen credentials.
- Encrypted HTTPS traffic hides attack signals. Because activity happens on legitimate domains and encrypted channels, detection using traditional indicators becomes harder.
- Automatic SSL decryption improves detection speed. ANY.RUN Sandbox extracts SSL keys from process memory to decrypt HTTPS traffic, revealing hidden scripts and network activity that enable faster investigations and reduced MTTD and MTTR.
How the Attack Works
In this campaign, attackers abuse Microsoft’s device login process, which is normally used to sign in on devices that cannot display a full login page.
The attacker first initiates a login request with Microsoft. This generates two values:
- user_code — a short, human-readable code (e.g., EL4BGRHUZ) displayed on the fake page as a “verification code;”
- device_code — an internal session identifier held only by the attacker, never shown to the victim. This is the ‘claim ticket’ the attacker uses to poll Microsoft’s token endpoint.
The victim is then shown the user_code on a phishing page, often disguised as a document verification step (for example, a fake DocuSign notification). The page instructs the user to copy the code and enter it at microsoft[.]com/devicelogin.
From the user’s perspective, everything appears legitimate. They are redirected to a real Microsoft page, where they enter their credentials and complete MFA.
However, by entering the verification code, the user is unknowingly approving a login request that was initiated by the attacker. While the victim sees only the user_code, the attacker uses the associated device_code to collect authentication tokens from Microsoft once the approval is completed.
Microsoft then issues access tokens to the attacker’s session, allowing them to access the victim’s Microsoft 365 account. Because the login happens through legitimate Microsoft infrastructure, no credentials are stolen on the phishing page and no fake login form is required.
Why This Attack Poses a Critical Risk and Is Harder for SOC Teams to Detect
OAuth Device Code phishing changes how account compromise happens. This campaign represents a structural shift:
- The victim interacts with legitimate Microsoft domains;
- Credentials and MFA are entered on authentic pages;
- The attack runs entirely over encrypted HTTPS;
- Traditional phishing indicators may not trigger.
As a result, token abuse replaces password theft. Detection relies heavily on visibility into encrypted network traffic and behavioral artifacts rather than domain reputation alone.
For SOC teams, this means:
- Delayed detection: Account compromise may only be noticed after suspicious activity appears.
- Longer investigations: Analysts must reconstruct token-based access rather than analyze credential theft.
- Higher incident impact: Attackers can operate inside Microsoft 365 immediately after token issuance.
For organizations, this creates a critical risk: attackers can immediately access corporate email, internal documents, and shared resources, impersonate employees in business email compromise schemes, and potentially maintain persistent access through refresh tokens, turning a single phishing interaction into data exposure, financial fraud, or broader account compromise.
OAuth Device Code Phishing Example: Full Attack Analysis
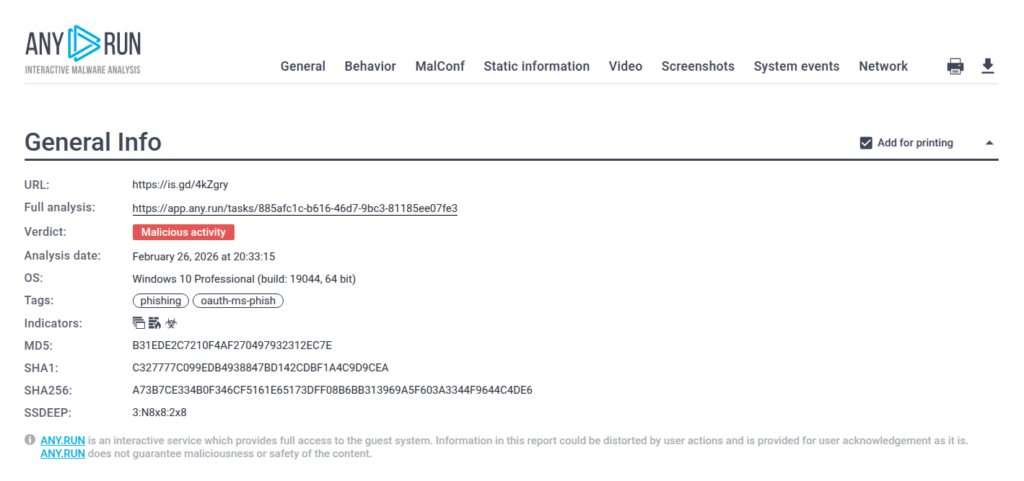
View sample analysis in ANY.RUN Interactive Sandbox
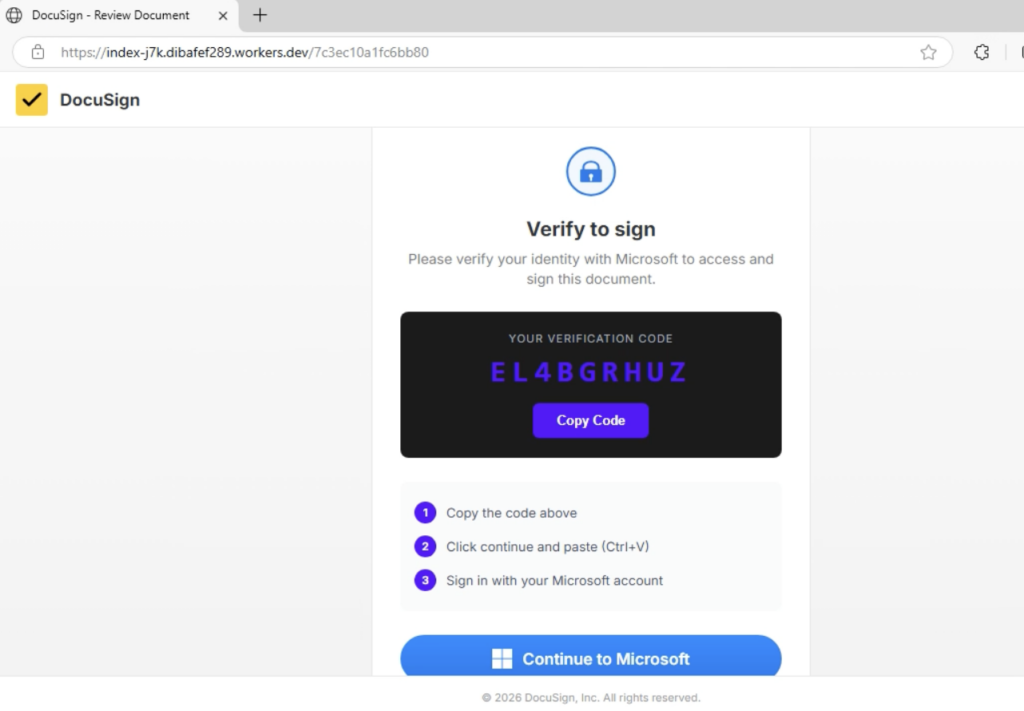
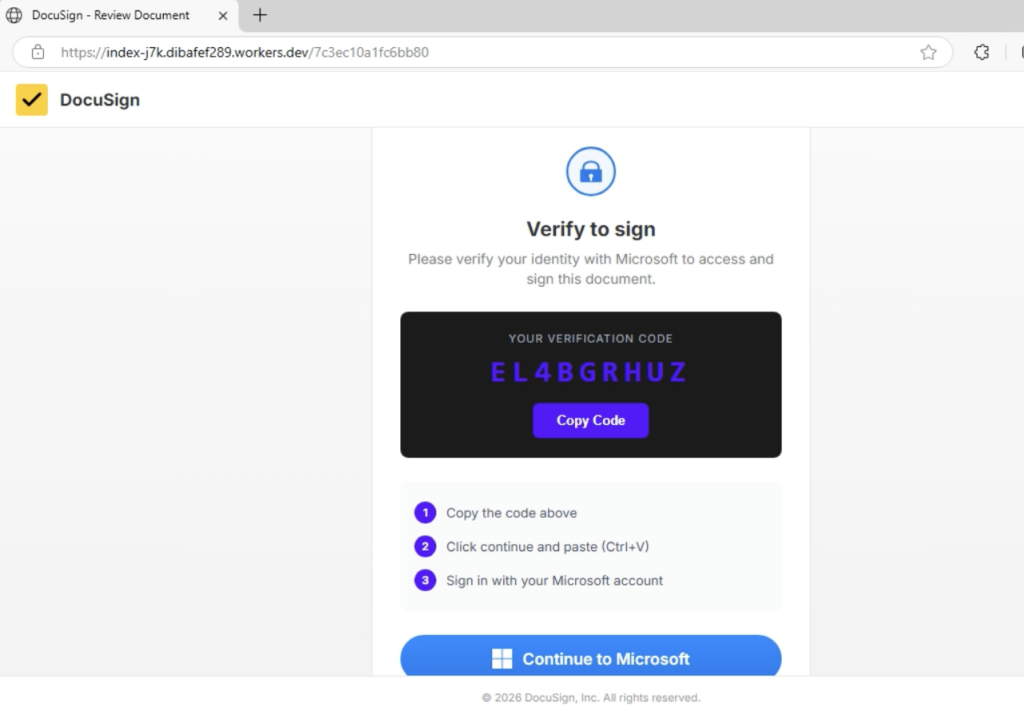
The attack often begins with a landing page impersonating DocuSign, prompting the user to “Review Document.” The victim is shown a verification code and instructed to copy it.
Key red flag: this is not a real DocuSign signing workflow. It is a scripted sequence:
- Copy the verification code,
- Click “Continue to Microsoft”,
- Paste the code into Microsoft’s device login page.
The address bar typically shows a *.workers.dev domain instead of a legitimate DocuSign domain.
A Microsoft window then opens at login.microsoftonline.com/…/deviceauth, showing the form “Enter code to allow access.” The user enters the same code they were shown on the fake page.
This action takes place on a legitimate Microsoft domain, even displaying Microsoft’s own warning: “Do not enter codes from sources you don’t trust.”
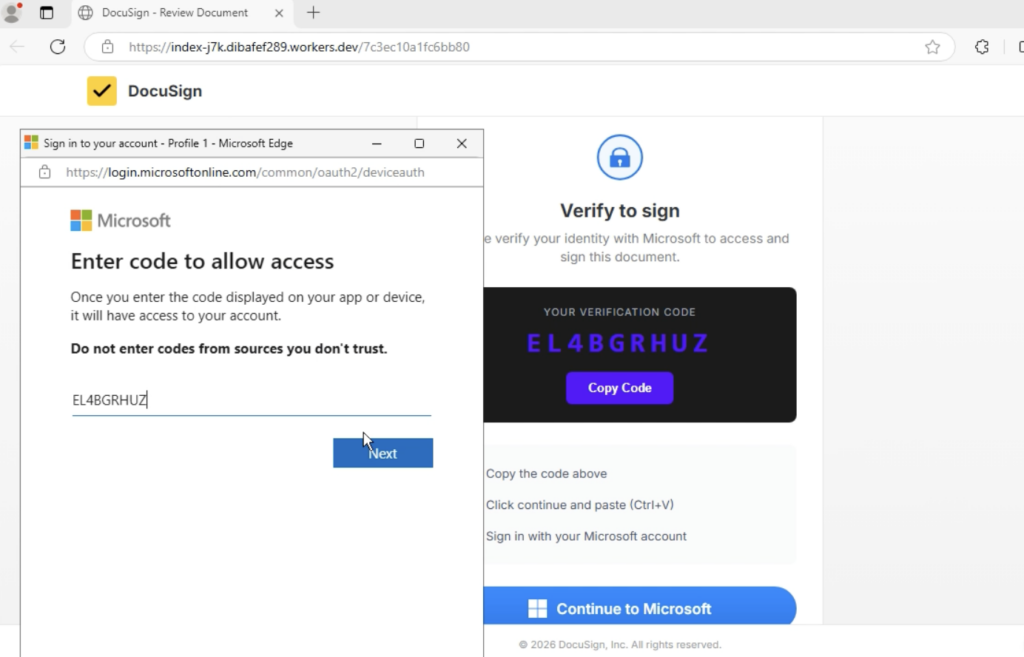
The following screen states: “You’re signing in to Microsoft Office on another device…” From the victim’s perspective, the process still appears legitimate. In reality, they are approving access for an external client controlled by the attacker, not verifying the document they originally clicked.
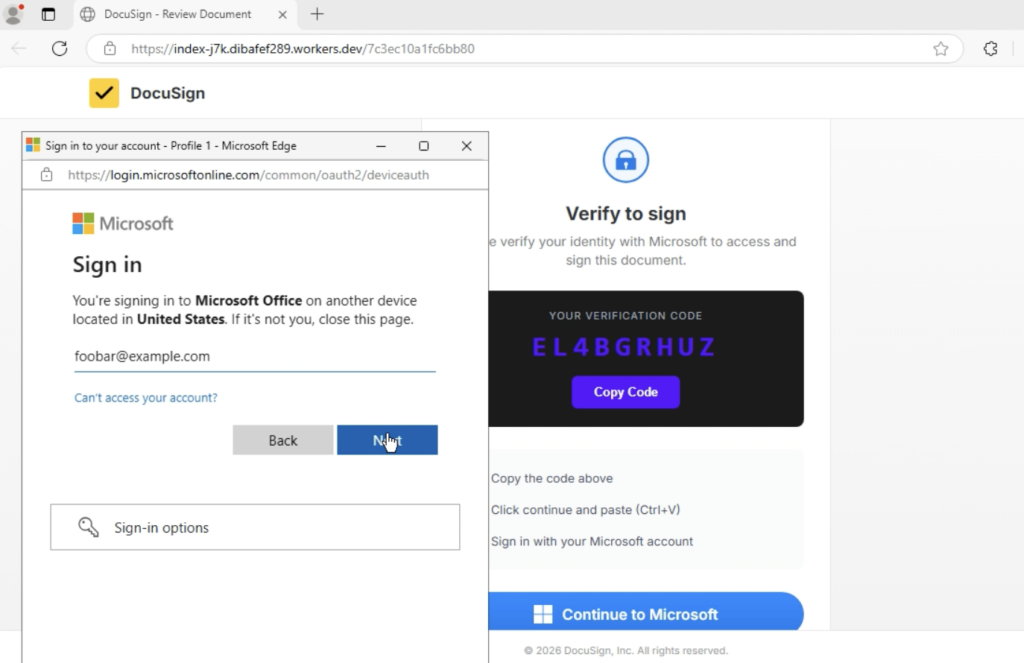
The key point is: the user never enters their password on a fake site. Instead, they are guided through legitimate Microsoft infrastructure and manually transfer a code.
How Automatic SSL Decryption Ensures Instant Detection
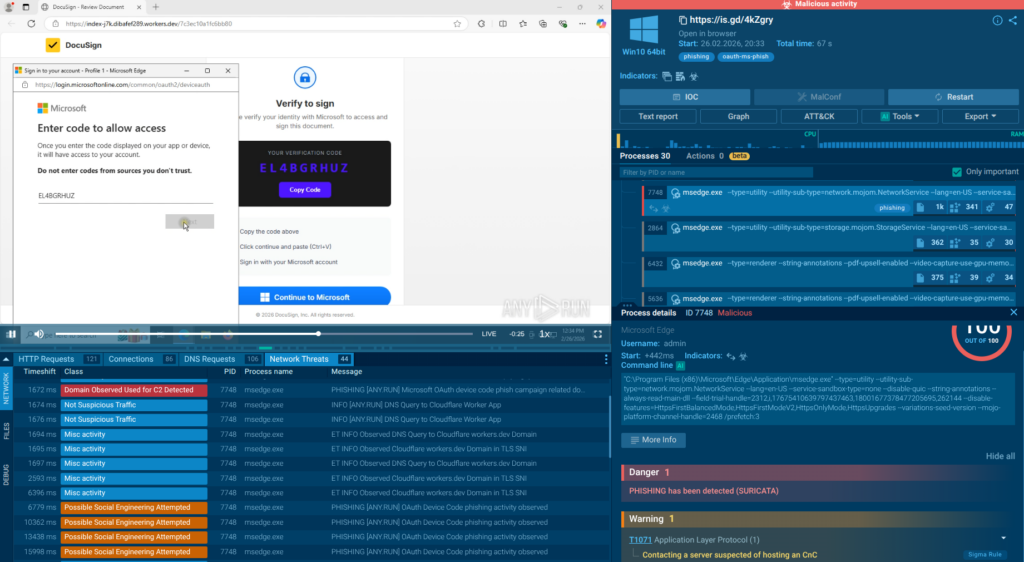
From an investigation standpoint, these phishing pages often rely on JavaScript loaders and encrypted HTTPS traffic to hide the real workflow from traditional scanners.
This is where SSL decryption in the ANY.RUN Sandbox becomes critical. By extracting TLS encryption keys directly from process memory and decrypting HTTPS traffic during execution, the sandbox reveals the hidden scripts, API requests, and attacker infrastructure involved in the phishing flow.
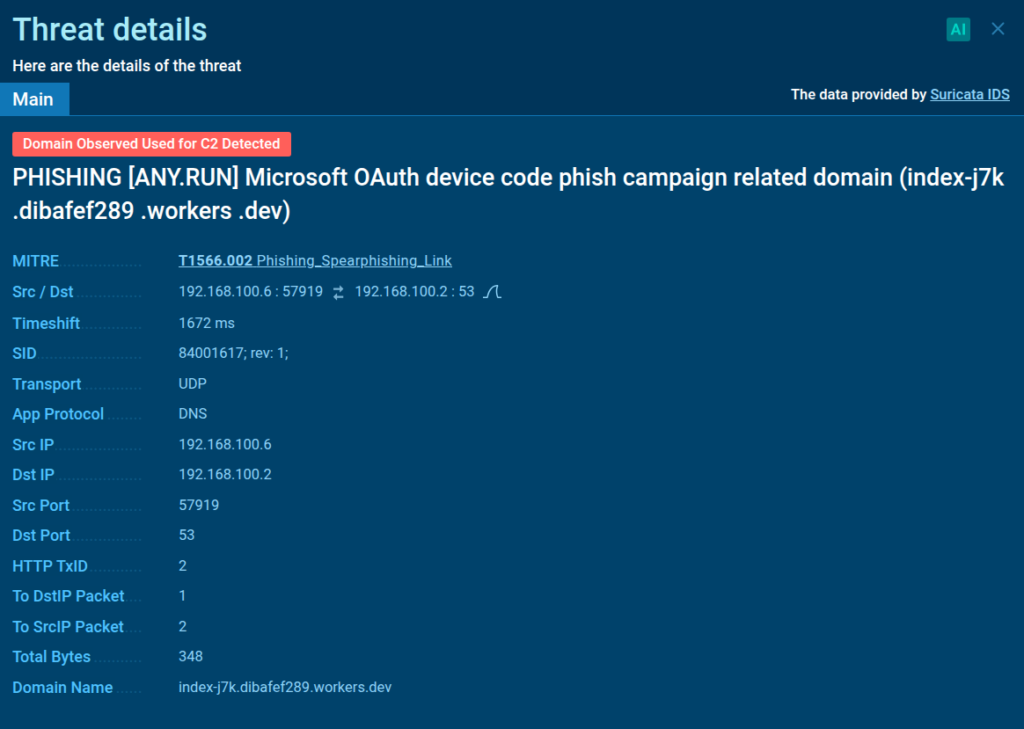
In this case, SSL decryption exposed the malicious JavaScript responsible for orchestrating the device authorization process and revealed high-confidence network indicators used by the phishing kit. Among them were specific API requests such as /api/device/start and /api/device/status/, along with a distinctive X-Antibot-Token header used in communication with the backend.
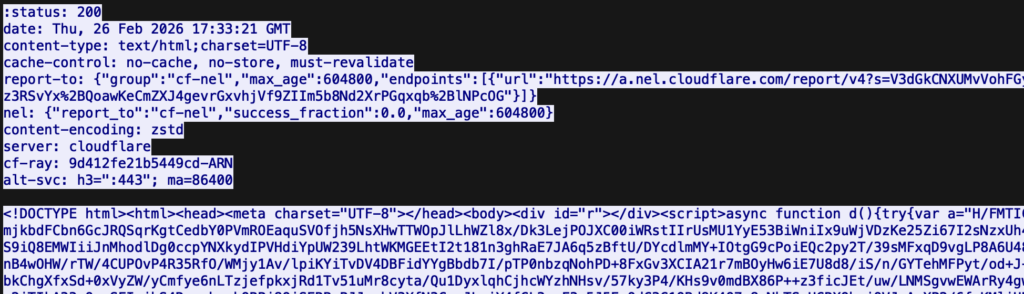
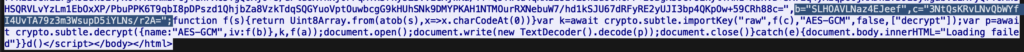
When these artifacts appear in HTTP requests to non-legitimate hosts, they become high-signal network IOCs that analysts can use to detect related phishing infrastructure and pivot to other campaign assets during investigation.
Protecting Business from Device Code Phishing Attacks
Because OAuth Device Code phishing abuses legitimate authentication flows and trusted infrastructure, traditional phishing detection often fails. Preventing account takeover requires strengthening the SOC processes responsible for early detection, fast triage, and proactive hunting.
Security leaders can reduce exposure by improving three key SOC processes.
Expand Threat Coverage with Real-Time Intelligence
Early visibility is critical for detecting phishing infrastructure before users interact with it. Without fresh threat signals, SOC teams often discover campaigns only after accounts are already compromised.
ANY.RUN’s Threat Intelligence Feeds help organizations improve monitoring by delivering continuously updated indicators derived from live sandbox investigations performed by thousands of security teams worldwide.
For SOC operations, this means:
- Earlier detection of emerging phishing infrastructure
- Faster identification of campaigns targeting similar industries
- Higher-quality detection signals entering SIEM, EDR, and network monitoring tools
For the business, earlier signals reduce the likelihood of successful account takeover and lower the probability of incidents escalating into financial fraud or data exposure.
Accelerate Triage to Drive Down MTTD
When a suspicious link or domain appears in an alert, SOC teams must quickly determine whether it is part of a real attack campaign. Slow validation creates backlogs, analyst fatigue, and delayed response.
ANY.RUN’s Interactive Sandbox helps analysts investigate suspicious URLs and files in a controlled environment where the full phishing workflow becomes visible.
With automatic SSL decryption, the sandbox extracts encryption keys directly from process memory and reveals the contents of HTTPS sessions without altering the traffic.
For organizations, this translates into faster investigation cycles, quicker escalation decisions, and reduced dwell time, limiting the impact of compromised accounts.
Improve Threat Hunting and Campaign Correlation
Even after a phishing page is discovered, identifying related infrastructure across the campaign is essential for preventing further compromise.
ANY.RUN’s Threat Intelligence Lookup allows analysts to quickly verify whether indicators are linked to known campaigns and explore related artifacts across previous investigations.
This supports SOC teams by enabling them to:
- connect alerts to active phishing campaigns
- identify related domains, files, and infrastructure
- prioritize investigations based on real attack activity
For security leaders, this improves operational efficiency and ensures that analyst time is focused on the threats most likely to impact the business.
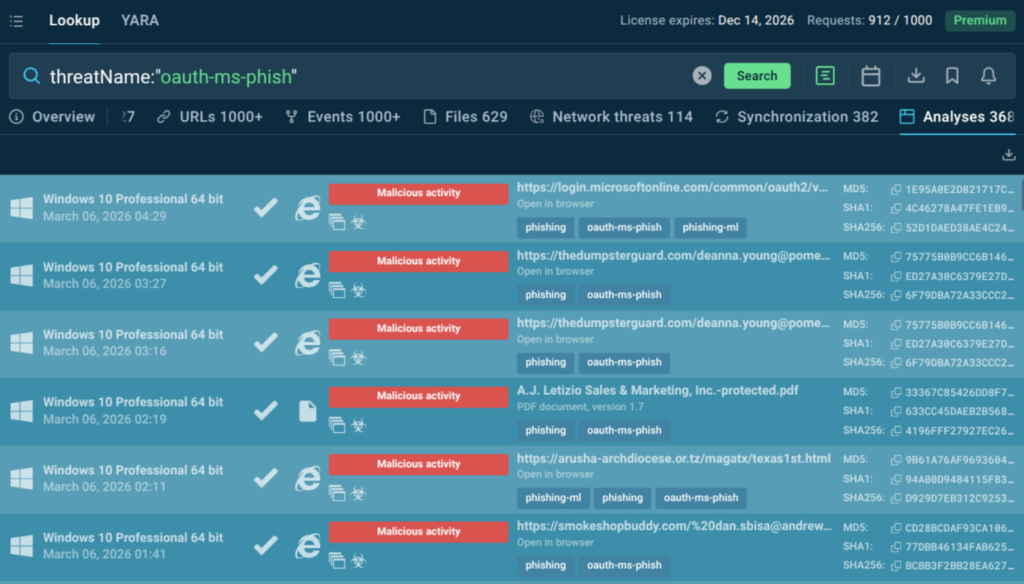
For example, indicators associated with this campaign can be queried directly in TI Lookup using the threat name:
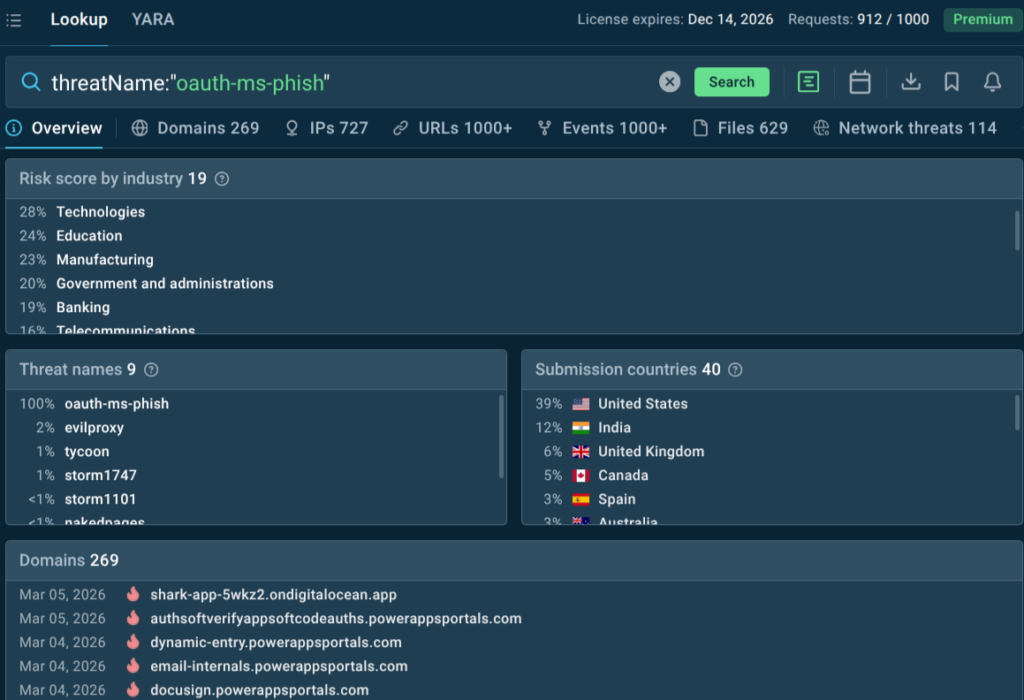
TI Lookup instantly shows the attack landscape.
Recently, the industries most at risk include Technology, Education, Manufacturing, and Government & Administration; primarily in the United States and India, though other countries are also affected.
There are also complete sandbox analyses of these attacks with detailed IOCs and TTPs that the SOC analysts can use to build strong detection rules and prevent similar attacks in the future.
This approach helps CISOs move beyond reactive security and establish a proactive defense strategy that aligns with business priorities: minimizing operational disruption, reducing incident response costs, and protecting sensitive corporate identities.
Conclusion
OAuth Device Code Phishing represents an evolution in account takeover tactics. It bypasses traditional credential harvesting and exploits trust in legitimate authentication flows. The compromise happens through approved token issuance rather than stolen passwords.
Defending against it requires deep visibility into encrypted sessions, behavioral pivoting, and rapid confirmation workflows.
With automatic SSL decryption in ANY.RUN Sandbox, SOC teams gain the ability to see inside encrypted phishing infrastructure without disrupting traffic. What was previously hidden becomes actionable intelligence.
About ANY.RUN
ANY.RUN supports over 15,000 organizations across industries such as banking, manufacturing, telecommunications, healthcare, retail, and technology, helping them build stronger and more resilient cybersecurity operations.
With our cloud-based Interactive Sandbox, security teams can safely analyze and understand threats targeting Windows, Linux, and Android environments in less than 40 seconds and without the need for complex on-premise systems. Combined with TI Lookup, YARA Search, and TI Feeds, we equip businesses to speed up investigations, reduce security risks, and improve teams’ efficiency.
IOCs:
- singer-bodners-bau-at-s-account[.]workers[.]dev
- dibafef289[.]workers[.]dev
- ab-monvoisinproduction-com-s-account[.]workers[.]dev
- subzero908[.]workers[.]dev
- sandra-solorzano-duncanfamilyfarms-net-s-account[.]workers[.]dev
- tyler2miler-proton-me-s-account[.]workers[.]dev
- aarathe-ramraj-tipgroup-com-au-s-account[.]workers[.]dev
- andy-bardigans-com-s-account[.]workers[.]dev
- dennis-saltertrusss-com-s-account[.]workers[.]dev
- rockymountainhi[.]workers[.]dev
- workspace1717-outlook-com-s-account[.]workers[.]dev
- aiinnovationsfly[.]com
- astrolinktech[.]com
FAQ
What is OAuth Device Code phishing?
It is a phishing technique that abuses the OAuth Device Authorization Grant. Instead of stealing credentials, attackers trick victims into approving a login request initiated by the attacker, which results in OAuth tokens being issued to them.
Why don’t victims notice the attack?
Victims authenticate on legitimate Microsoft pages and complete MFA normally. Since no fake login form is used, the process appears trustworthy.
What are the main signs of this phishing technique?
Typical indicators include verification codes shown on phishing pages, instructions to visit microsoft[.]com/devicelogin, and suspicious device authorization prompts such as “You’re signing in on another device.”
Which industries are most at risk?
Campaign analysis shows targeting of technology companies, educational institutions, financial organizations, and government agencies, although any Microsoft 365 user can be affected.
Why is this attack difficult for SOC teams to detect?
The attack leverages legitimate authentication infrastructure and encrypted HTTPS traffic. Without deep inspection of network activity, the malicious flow blends into normal login behavior.
How does SSL decryption help detect these attacks?
SSL decryption exposes hidden JavaScript and encrypted traffic within phishing pages, allowing analysts to observe real network requests, identify IoCs, and reconstruct the attack chain.
How can organizations reduce the risk?
Organizations should combine threat intelligence, strong identity controls, security awareness, and dynamic malware analysis tools such as ANY.RUN Sandbox to quickly detect phishing infrastructure and extract behavioral indicators.