
好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内,并且不需要特定的开头。首先,我得通读全文,抓住主要信息。 文章讲的是CISA(美国网络安全和基础设施安全局)发现Ivanti的Endpoint Manager(EPM)软件存在一个高危漏洞CVE-2026-1603,并且这个漏洞正在被积极利用。CISA要求美国联邦机构在三周内修复系统。 接下来,Ivanti的EPM是一个跨平台的端点管理解决方案,适用于Windows、macOS等多个系统。这个漏洞允许远程攻击者在无需用户交互的情况下绕过认证,窃取凭证数据。Ivanti已经在一个月前发布了补丁,修复了这个漏洞以及另一个SQL注入问题。 虽然CISA标记了这个漏洞为被利用,但Ivanti表示尚未收到任何客户被攻击的报告。目前有超过700个暴露在互联网上的EPM实例,主要在美国。 CISA将此漏洞加入其已知被利用的漏洞目录,并要求联邦机构在3月23日前完成修复。尽管Ivanti尚未发现该漏洞被利用的证据,但威胁行为者经常针对EPM漏洞发起攻击。 总结下来,重点是高危漏洞、影响范围、修复要求以及Ivanti的回应。我需要把这些信息浓缩到100字以内,确保涵盖所有关键点。 </think> CISA警告Ivanti EPM软件存在高危漏洞CVE-2026-1603,可被远程攻击者利用进行跨站脚本攻击窃取凭证。该漏洞已被标记为野外活跃利用,要求美国联邦机构三周内修复。尽管Ivanti尚未收到 exploitation报告,已有超700个暴露实例。 2026-3-10 11:45:16 Author: www.bleepingcomputer.com(查看原文) 阅读量:6 收藏

CISA flagged a high-severity Ivanti Endpoint Manager (EPM) vulnerability as actively exploited in attacks and ordered U.S. federal agencies to patch systems within three weeks.
Ivanti's EPM software is an all-in-one endpoint management solution for managing client devices across Windows, macOS, Linux, Chrome OS, and IoT platforms.
Tracked as CVE-2026-1603, this security flaw can be exploited by remote threat actors without privileges to bypass authentication and steal credential data in low-complexity cross-site scripting attacks that require no user interaction.
Ivanti patched the vulnerability one month ago, when it released Ivanti EPM 2024 SU5, which also addresses an SQL injection flaw that allows remote, authenticated attackers to read arbitrary data from the database.
While CISA has now tagged CVE-2026-1603 as exploited in the wild, Ivanti said it received no reports of exploitation when BleepingComputer reached out for confirmation on Monday.
"We are not aware of any customers being exploited by these vulnerabilities prior to public disclosure. These vulnerabilities were disclosed through our responsible disclosure program," Ivanti says in the original advisory.
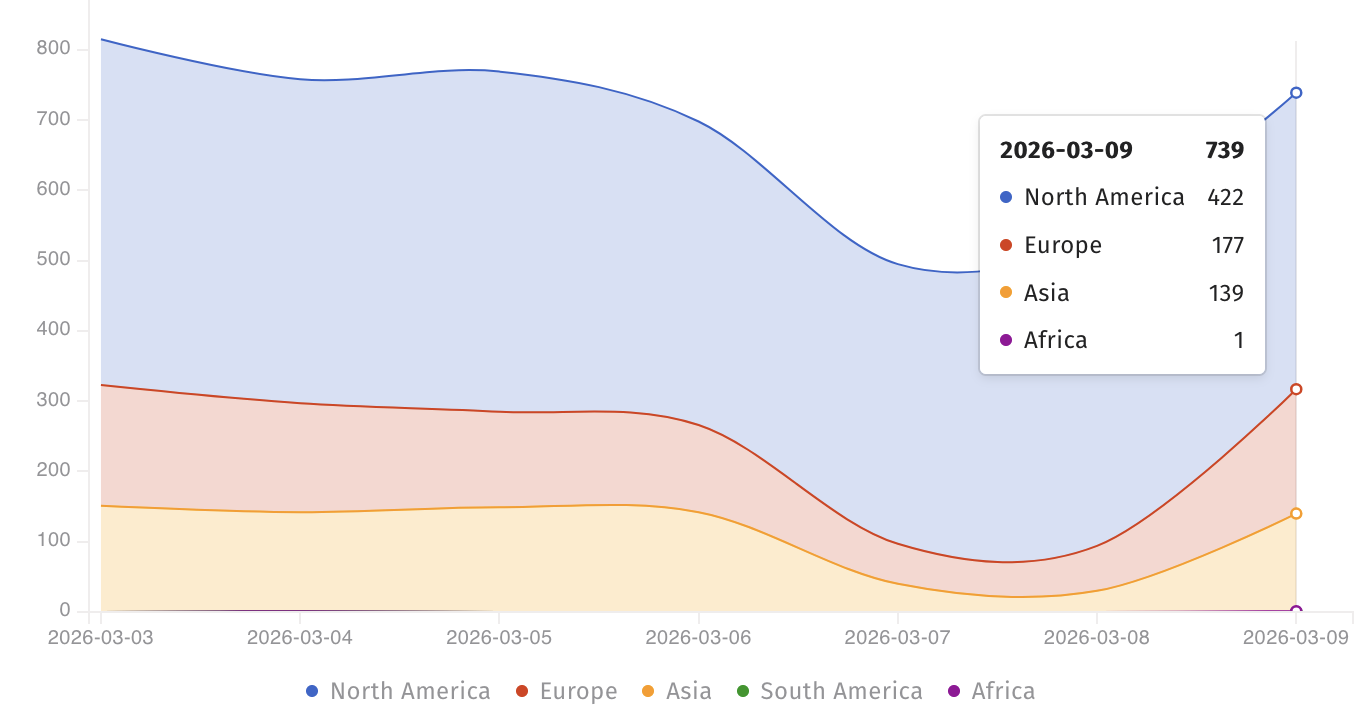
At the moment, the Shadowserver threat monitoring platform tracks over 700 Internet-facing Ivanti EPM instances, most of them in North America. However, there is no information on how many of them are still vulnerable to CVE-2026-1603 attacks.
Although it didn't provide any details on attacks exploiting this flaw, CISA added it to its Known Exploited Vulnerabilities (KEV) Catalog on Monday, warning that such security bugs are "frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise."
The U.S. cybersecurity agency has also ordered Federal Civilian Executive Branch (FCEB) agencies to patch their systems within three weeks, by March 23, as mandated by a binding operational directive (BOD 22-01) issued in November 2021.
While Ivanti has yet to find evidence of active CVE-2026-1603 exploitation, threat actors often target Ivanti EPM vulnerabilities in attacks.
One year ago, CISA warned federal agencies to secure their networks against three other EPM flaws (CVE-2024-13159, CVE-2024-13160, and CVE-2024-13161) that were exploited in the wild.
CISA also ordered U.S. government agencies to patch another actively exploited EPM flaw (CVE-2024-29824) in October 2024.
Ivanti provides system and IT asset management products to more than 40,000 companies through a network of more than 7,000 partners worldwide.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
