The Russian state-sponsored hacking group tracked as APT28 has been observed using a pair of implants dubbed BEARDSHELL and COVENANT to facilitate long‑term surveillance of Ukrainian military personnel.
The two malware families have been put to use since April 2024, ESET said in a new report shared with The Hacker News.
APT28, also tracked as Blue Athena, BlueDelta, Fancy Bear, Fighting Ursa, Forest Blizzard (formerly Strontium), FROZENLAKE, Iron Twilight, ITG05, Pawn Storm, Sednit, Sofacy, and TA422, is a nation-state actor affiliated with Unit 26165 of the Russian Federation's military intelligence agency GRU.
The threat actor's malware arsenal consists of tools like BEARDSHELL and COVENANT, along with another program codenamed SLIMAGENT that's capable of logging keystrokes, capturing screenshots, and collecting clipboard data. SLIMAGENT was first publicly documented by the Computer Emergency Response Team of Ukraine (CERT-UA) in June 2025.
SLIMAGENT, per the Slovakian cybersecurity company, has its roots in XAgent, another implant used by APT28 in the 2010s to facilitate remote control and data exfiltration. This is based on code similarities discovered between SLIMAGENT and previously unknown samples deployed in attacks targeting governmental entities in two European countries as far back as 2018.
It's assessed that the 2018 artifacts and the 2024 SLIMAGENT sample originated from XAgent, with ESET's analysis uncovering overlaps in the keylogging between SLIMAGENT and an XAgent sample detected in the wild in late 2014.
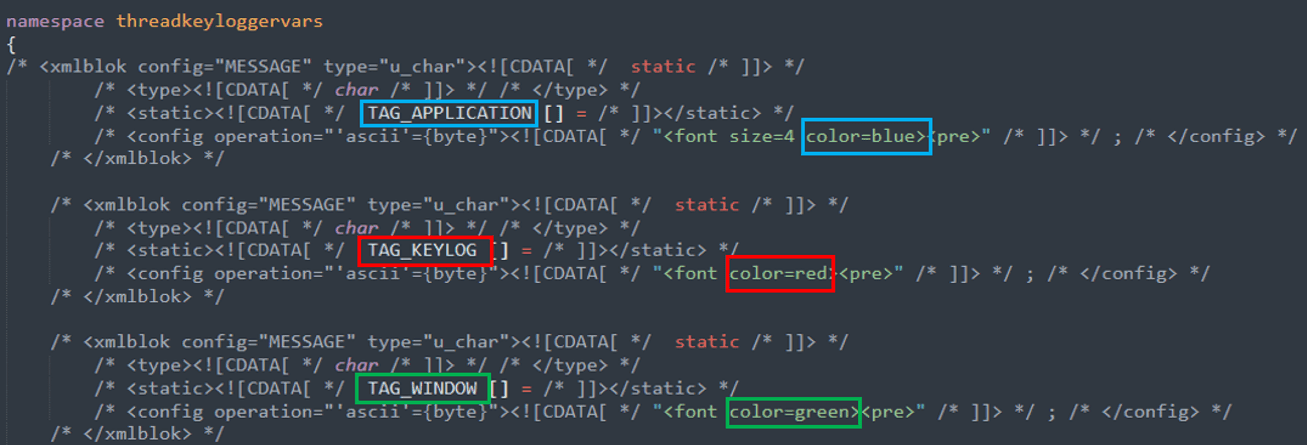
"SLIMAGENT emits its espionage logs in the HTML format, with the application name, the logged keystrokes, and the window name in blue, red, and green, respectively," ESET said. "The XAgent keylogger also produces HTML logs using the same color scheme."
Also deployed in connection with SLIMAGENT is another backdoor referred to as BEARDSHELL that's capable of executing PowerShell commands on compromised hosts. It uses the legitimate cloud storage service Icedrive for command-and-control (C2).
A noteworthy aspect of the malware is that it utilizes a distinctive obfuscation technique referred to as opaque predicate, which is also found in XTunnel (aka X-Tunnel), a network traversal and pivoting tool used by APT28 in the 2016 Democratic National Committee (DNC) hack. The tool provides a secure tunnel to an external C2 server.
"The shared use of this rare obfuscation technique, combined with its colocation with SLIMAGENT, leads us to assess with high confidence that BEARDSHELL is part of Sednit's custom arsenal," ESET added.
A third major piece of the threat actor's toolkit is COVENANT, an open-source .NET post-exploitation framework that has been "heavily" modified to support long-term espionage and to implement a new cloud-based network protocol that abuses the Filen cloud storage service for C2 since July 2025. Previously, APT28's COVENANT variant was said to have used pCloud (in 2023) and Koofr (in 2024-2025).
"These adaptations show that Sednit developers acquired deep expertise in Covenant – an implant whose official development ceased in April 2021 and may have been considered unused by defenders," ESET said. "This surprising operational choice appears to have paid off: Sednit has successfully relied on Covenant for several years, particularly against selected targets in Ukraine."
This is not the first time the adversarial collective has embraced the dual-implant strategy. In 2021, Trellix revealed that APT28 deployed Graphite, a backdoor that employed OneDrive for C2, and PowerShell Empire in attacks targeting high-ranking government officials overseeing national security policy and individuals in the defense sector in Western Asia.
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.