
好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,抓住主要信息。 文章讲的是黑客通过Microsoft Teams联系金融和医疗行业的员工,假装是IT部门,诱导他们使用Quick Assist授予远程访问权限。然后部署了一种新的恶意软件A0Backdoor。攻击者使用了社会工程学,先发送垃圾邮件,再通过Teams联系员工。他们还利用了恶意MSI安装程序和DLL侧载技术来传播恶意软件。 接下来,恶意软件通过DNS流量与C2服务器通信,隐藏在MX查询中,以逃避检测。攻击目标包括加拿大的金融机构和全球的医疗组织。研究人员推测这可能与BlackBasta勒索软件团伙有关。 现在我需要把这些信息浓缩到100字以内。重点包括:攻击手段(Teams联系、Quick Assist)、恶意软件(A0Backdoor)、技术细节(MSI安装程序、DLL侧载)、通信方式(DNS MX查询)以及目标行业。 最后,确保语言简洁明了,直接描述内容,不使用总结性的开头。 </think> 黑客利用Microsoft Teams伪装成公司IT人员联系金融和医疗行业员工,诱导其授予远程访问权限并部署名为A0Backdoor的新恶意软件。攻击者通过社会工程学手段发送垃圾邮件,随后提供"帮助"以获取信任,并借助Quick Assist远程会话和恶意MSI安装程序传播威胁。该恶意软件利用DLL侧载技术隐藏自身,并通过DNS MX记录与命令控制服务器通信以规避检测。 2026-3-9 23:0:22 Author: www.bleepingcomputer.com(查看原文) 阅读量:11 收藏

Hackers contacted employees at financial and healthcare organizations over Microsoft Teams to trick them into granting remote access through Quick Assist and deploy a new piece of malware called A0Backdoor.
The attacker relies on social engineering to gain the employee's trust by first flooding their inbox with spam and then contacting them over Teams, pretending to be the company's IT staff, offering assistance with the unwanted messages.
To obtain access to the target machine, the threat actor instructs the user to start a Quick Assist remote session, which is used to deploy a malicious toolset that includes digitally signed MSI installers hosted in a personal Microsoft cloud storage account.
According to researchers at cybersecurity company BlueVoyant, the malicious MSI files masquerade as Microsoft Teams components and the CrossDeviceService, a legitimate Windows tool used by the Phone Link app.
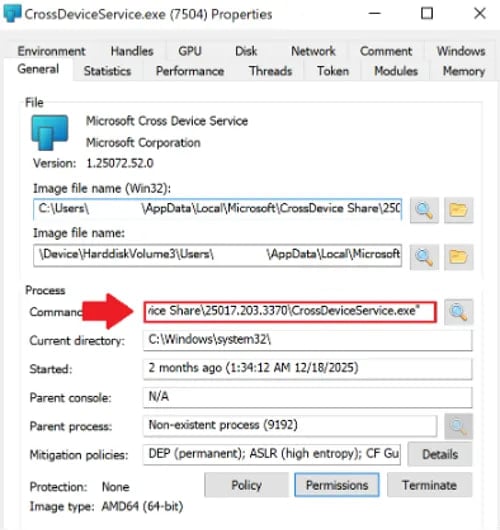
Source: BlueVoyant
Using the DLL sideloading technique with legitimate Microsoft binaries, the attacker deploys a malicious library (hostfxr.dll) that contains compressed or encrypted data. Once loaded in memory, the library decrypts the data into shellcode and transfers execution to it.
The researchers say that the malicious library also uses the CreateThread function to prevent analysis. BlueVoyant explains that the excessive thread creation could cause a debugger to crash, but it does not have a significant impact under normal execution.
The shellcode performs sandbox detection and then generates a SHA-256-derived key, which it uses to extract the A0Backdoor, which is encrypted using the AES algorithm.
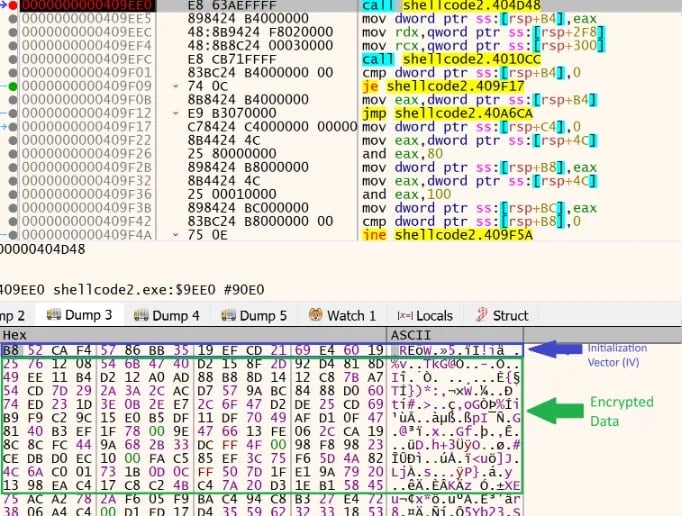
Source: BlueVoyant
The malware relocates itself into a new memory region, decrypts its core routines, and relies on Windows API calls (e.g., DeviceIoControl, GetUserNameExW, and GetComputerNameW) to collect information about the host and fingerprint it.
Communication with the command-and-control (C2) is hidden in DNS traffic, with the malware sending DNS MX queries with encoded metadata in high-entropy subdomains to public recursive resolvers. The DNS servers respond with MX records containing encoded command data.
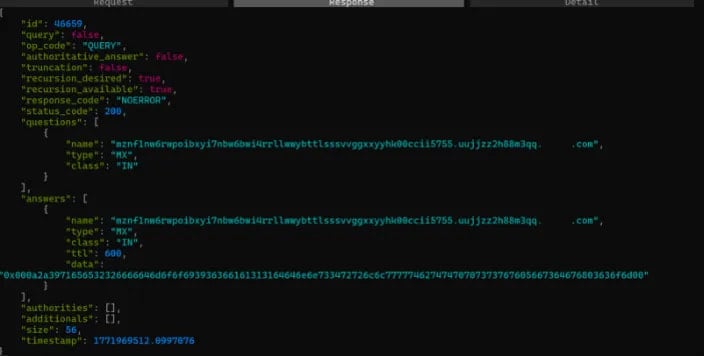
Source: BlueVoyant
“The malware extracts and decodes the leftmost label to recover command/configuration data, then proceeds accordingly,” explains BlueVoyant.
“Using DNS MX records helps the traffic blend in and can evade controls tuned to detect TXT-based DNS tunneling, which may be more commonly monitored.”
BlueVoyant states that two of the targets of this campaign are a financial institution in Canada and a global healthcare organization.
The researchers assess with moderate-to-high confidence that the campaign is an evolution of tactics, techniques and procedures associated with the BlackBasta ransomware gang, which has dissolved after the internal chat logs of the operation were leaked.
While there are plenty of overlaps, BlueVoyant notes that the use of signed MSIs and malicious DLLs, the A0Backdoor payload, and using DNS MX-based C2 communication are new elements.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
