嗯,用户让我用中文总结这篇文章,控制在100字以内,而且不需要特定的开头。首先,我得通读全文,抓住主要信息。 文章讲的是荷兰情报机构警告说,与俄罗斯有关的黑客正在全球范围内攻击政府和军事官员的Signal和WhatsApp账户。他们通过伪装成Signal支持或利用“链接设备”功能来获取验证码,从而劫持账户。目标包括荷兰政府雇员、记者等。荷兰情报建议用户提高警惕,监测群组聊天中的可疑活动,并提供应对措施。 接下来,我需要将这些要点浓缩到100字以内。要确保涵盖主要事件:俄罗斯黑客攻击Signal和WhatsApp账户,目标是政府和军事人员,方法是利用合法功能如QR码和链接设备,以及荷兰情报的建议。 最后,组织语言,确保简洁明了。避免使用复杂的结构,直接陈述事实。 </think> 俄罗斯相关黑客正针对全球政府及军事官员的Signal和WhatsApp账户发起攻击,通过伪装成技术支持或利用“链接设备”功能获取验证码以劫持账户。荷兰情报机构警告称目标包括本国政府雇员及记者等,并建议用户警惕可疑活动以防范此类攻击。 2026-3-9 14:54:23 Author: securityaffairs.com(查看原文) 阅读量:14 收藏
Russia-linked hackers target Signal, WhatsApp of officials globally

Russia-linked hackers are targeting Signal and WhatsApp accounts of government and military officials worldwide, warns Dutch intelligence.
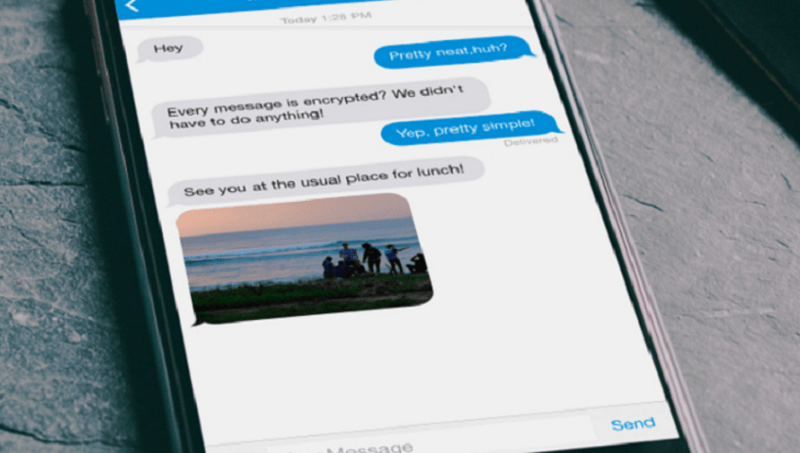
Dutch intelligence agencies (MIVD and AIVD) warn of a global campaign by Russia-linked threat actors aiming to compromise Signal and WhatsApp accounts. The operation targets government officials, civil servants, and military personnel, highlighting growing cyber risks to sensitive communications among national security actors.
“Russian state hackers are engaged in a large-scale global cyber campaign to gain access to Signal and WhatsApp accounts belonging to dignitaries, military personnel and civil servants. The Dutch intelligence and security services MIVD and AIVD can confirm that targets and victims of the campaign include Dutch government employees.” reads the alert by Dutch intelligence agencies. “The Dutch services also believe that other persons of interest to the Russian government, such as journalists, may possibly be targeted by this campaign.”
Russian cyber spies are tricking users into revealing verification codes to hijack Signal and WhatsApp accounts. They impersonate Signal Support or exploit the “linked devices” feature, gaining access to messages and chat groups, potentially exposing sensitive information from government and military targets.
Dutch intelligence warns that Russia targets Signal for its strong end-to-end encryption, aiming to access sensitive government communications. Officials stress that apps like Signal and WhatsApp should not be used for classified or confidential information.
The government experts pointed out that attackers don’t exploit app vulnerabilities but abuse legitimate features of Signal and WhatsApp. Only individual accounts are targeted, not the platforms themselves, officials say.
Dutch intelligence agencies recommend Signal users to carefully monitor their group chats for signs of compromised accounts. If a contact appears twice under the same or slightly altered name, this may indicate a compromised account or a victim-created account. Users should report suspicious cases to their organization’s information security team and verify the accounts through alternative channels such as email or phone. Group administrators should remove any unauthorized accounts, after which legitimate members can rejoin. Actor-controlled accounts may change display names, e.g., to “Deleted account,” or join via a shared Group Link, triggering notifications. Users should remain vigilant for unfamiliar members and unusual account behavior. If there is any suspicion that the group administrator has been compromised, it is recommended to leave the chat group and create a new one to ensure the security and integrity of communications within the group.
“To increase resilience against this Russian campaign, MIVD and AIVD have published a Cyber Advisory explaining how to identify and respond to attacks. The advisory also give instructions for Signal users on how to identify potentially compromised contacts.” concludes the alert.
In February 2025, Google Threat Intelligence Group (GTIG) researchers warned of multiple Russia-linked threat actors targeting Signal Messenger accounts used by individuals of interest to Russian intelligence. The experts speculated that the tactics, techniques, and procedures used to target Signal will be prevalent in the near term, and they will also be employed in regions outside Ukraine.
Russian hackers exploited Signal’s “linked devices” feature, they used specially crafted QR codes to link victims’ accounts to attacker-controlled devices, and then spy on them.
“The most novel and widely used technique underpinning Russian-aligned attempts to compromise Signal accounts is the abuse of the app’s legitimate “linked devices” feature that enables Signal to be used on multiple devices concurrently. Because linking an additional device typically requires scanning a quick-response (QR) code, threat actors have resorted to crafting malicious QR codes that, when scanned, will link a victim’s account to an actor-controlled Signal instance.” reads the report published by GTIG. “If successful, future messages will be delivered synchronously to both the victim and the threat actor in real-time, providing a persistent means to eavesdrop on the victim’s secure conversations without the need for full-device compromise.”
Russian hackers used malicious QR codes disguised as Signal resources to hijack accounts, targeting military apps and even linking captured devices to their servers.
In some phishing attacks, attackers frequently masked malicious QR codes as legitimate Signal resources, such as group invites, security alerts, or as legitimate device pairing instructions from the Signal website.
In some spear-phishing attacks, attackers embedded the QR codes in phishing pages crafted to appear as specialized applications used by the Ukrainian military.
APT44 (Sandworm) enables Russian forces to link captured Signal accounts to their servers, using battlefield devices for further exploitation.
The alleged Russia-linked cyberespionage group UNC5792 (which partially overlaps with a threat actor tracked as UAC-0195 by CERT-UA) was spotted modifying Signal group invites in phishing campaigns to trick recipients into linking their accounts to attacker-controlled devices.
Researchers also reported that Russian and Belarus-linked threat actors were able to steal Signal database files from Android and Windows devices using scripts, malware, and command-line tools fordata exfiltration.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Signal)
如有侵权请联系:admin#unsafe.sh