好的,我现在需要帮用户总结这篇文章的内容,控制在100个字以内。首先,我得通读整篇文章,抓住主要信息。 文章主要讲的是伊朗关联的黑客攻击以色列和海湾国家的IP摄像头,目的是获取军事情报和评估战损情况。Check Point的研究人员观察到这些攻击活动,涉及多个漏洞,包括CVE-2017-7921等多个CVE编号。这些漏洞已经被修复了。 接下来,我需要将这些信息浓缩成一句话。要包含攻击者、目标国家、攻击目的以及涉及的技术细节。同时,要确保不超过100个字。 可能的结构是:伊朗黑客攻击以色列和海湾国家的IP摄像头,利用多个漏洞获取军事情报和评估战损情况。 检查一下字数:这句话大约有35个字,符合要求。再确认一下关键点是否都有涵盖:攻击者、目标、目的、技术手段。 看起来没问题。这样用户就能快速了解文章的核心内容了。 </think> 伊朗关联的黑客针对以色列及海湾国家的IP摄像头发起攻击,利用多个已修复漏洞获取军事情报并评估战损情况。 2026-3-7 10:20:36 Author: securityaffairs.com(查看原文) 阅读量:25 收藏
Iran-linked hackers target IP cameras across Israel and Gulf states for military intelligence

Researchers observed Iran-linked actors targeting IP cameras across Israel and Gulf countries, likely to support military intelligence and battle damage assessment.
According to the Check Point Cyber Security Report 2026, cyber operations are increasingly used to support military activity and battle damage assessment (BDA). During the Israel-Iran tensions, researchers from Check Point Software Technologies observed a surge in attacks targeting IP cameras across Israel and Gulf countries, including the UAE, Qatar, Bahrain, and Kuwait, as well as Lebanon and Cyprus. The activity, attributed to Iran-linked actors, relied on VPN and VPS infrastructure to scan devices, mainly Hikvision and Dahua Technology cameras, for known vulnerabilities.
“During the ongoing conflict, we identified intensified targeting of IP cameras from two manufacturers starting on February 28, originating from infrastructure we attribute to Iranian threat actors.
The targeting extends across Israel, Qatar, Bahrain, Kuwait, the UAE, and Cyprus – countries that have also experienced significant missile activity linked to Iran. On March 1st, we additionally observed camera-targeting activity focused on specific areas in Lebanon.” states Check Point Software Technologies.”
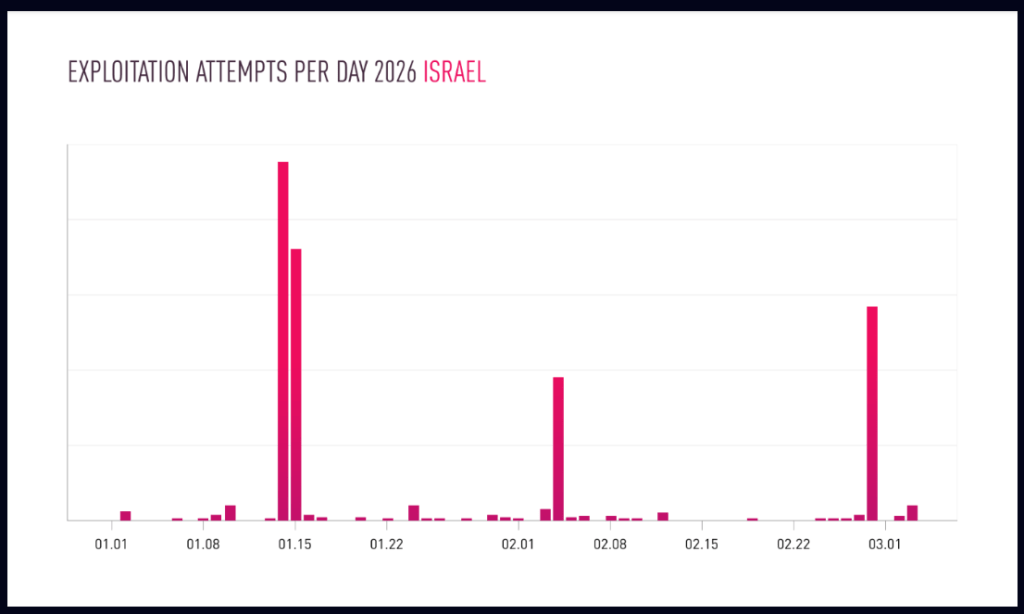
“We also observed earlier, more targeted activity against cameras in Israel and Qatar on January 14–15. These dates surround with Iran’s temporary closure of its airspace, reportedly amid expectations of a potential U.S. strike.”
Researchers believe the goal was reconnaissance and real-time monitoring to support intelligence gathering and potential military targeting.
Threat actors targeted the following vulnerabilities in Hikvision and Dahua devices:
| CVE | Vulnerability |
|---|---|
| CVE-2017-7921 | An improper authentication vulnerability in Hikvision IP camera firmware |
| CVE-2021-36260 | A command injection vulnerability in the Hikvision web server component |
| CVE-2023-6895 | An OS command injection vulnerability in Hikvision Intercom Broadcasting System |
| CVE-2025-34067 | An unauthenticated remote code execution vulnerability in Hikvision Integrated Security Management Platform |
| CVE-2021-33044 | An authentication bypass vulnerability in multiple Dahua products |
The experts state that Chinese manufacturers have patched all the above issues.
Researchers analyzed exploitation attempts for CVE-2021-33044 and CVE-2017-7921 linked to infrastructure attributed to Iran.
In October 2021, experts warned that proof-of-concept (PoC) exploit code was available for two authentication-bypass vulnerabilities in Dahua cameras, tracked as CVE-2021-33044 and CVE-2021-33045. A remote attacker can exploit both vulnerabilities by sending specially crafted data packets to the vulnerable cameras.
Since early 2026, scanning activity targeting IP cameras has surged across Israel and several Middle East countries, often aligning with geopolitical tensions such as protests in Iran, U.S. military visits to Israel, and fears of potential strikes.


Similar patterns appeared during the June 2025 Israel-Iran conflict, when compromised cameras were likely used for reconnaissance and battle damage assessment, including a case involving a camera near Israel’s Weizmann Institute before a missile strike.
“One of the best-known cases occurred when Iran struck Israel’s Weizmann Institute of Science with a ballistic missile and had reportedly taken control of a street camera facing the building just prior to the hit” concludes the report.
Defenders should reduce risks by removing public internet access to cameras and placing them behind VPN or zero-trust gateways. Organizations should change default passwords, enforce strong unique credentials, and keep device firmware updated. Cameras should run on isolated network segments with restricted outbound traffic. Security teams should also monitor for repeated login failures, suspicious remote access, and unusual outbound connections.
This week, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added Hikvision multiple products improper authentication vulnerability CVE-2017-7921 (CVSS score of 9.8) to its Known Exploited Vulnerabilities (KEV) catalog.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Iran, IP cameras)
如有侵权请联系:admin#unsafe.sh