
好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内,并且不需要特定的开头。首先,我得仔细阅读文章,理解主要内容。 文章讲的是美国网络安全和基础设施安全局(CISA)命令联邦机构修补三个iOS安全漏洞。这些漏洞被用于网络间谍和加密货币盗窃攻击,使用的是Coruna漏洞工具包。Coruna利用了23个iOS漏洞,其中一些是零日攻击。不过,这些漏洞在较新版本的iOS上不起作用,并且如果启用了Apple的反间谍保护功能,也会被阻止。 Coruna允许攻击者绕过各种安全机制,获取远程代码执行权限,并提升权限到内核级别。GTIG观察到去年多个威胁行为者使用了这个工具包,包括一个监视软件客户、一个疑似俄罗斯支持的黑客组织以及一个中国背景的金融动机威胁行为者。后者在假赌博和加密网站上部署了该工具包,用于窃取加密钱包。 CISA将三个Coruna漏洞添加到已知被利用的漏洞目录中,并要求联邦机构在3月26日前修补这些漏洞。虽然指令仅适用于联邦机构,但CISA敦促所有组织优先修补这些漏洞。 总结的时候要抓住关键点:CISA命令修补三个iOS漏洞,用于网络间谍和加密盗窃;Coruna工具包利用多个漏洞;攻击在新版本iOS无效;CISA要求联邦机构限期修补,并建议所有组织跟进。 现在需要把这些信息浓缩到100字以内,确保涵盖主要事件、影响和行动。 </think> 美国网络安全机构要求联邦机构修复三个针对iOS的安全漏洞,这些漏洞被用于网络间谍和加密货币盗窃攻击。研究人员发现攻击工具包利用23个iOS漏洞,部分为零日攻击。然而,在最新版本iOS中无效,并受隐私浏览模式和反间谍功能限制。该工具包允许绕过多种安全机制并获取高级权限。多个威胁行为者去年使用此工具包进行攻击。 2026-3-6 16:0:20 Author: www.bleepingcomputer.com(查看原文) 阅读量:10 收藏

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) ordered federal agencies to patch three iOS security flaws targeted in cyberespionage and crypto-theft attacks using the Coruna exploit kit.
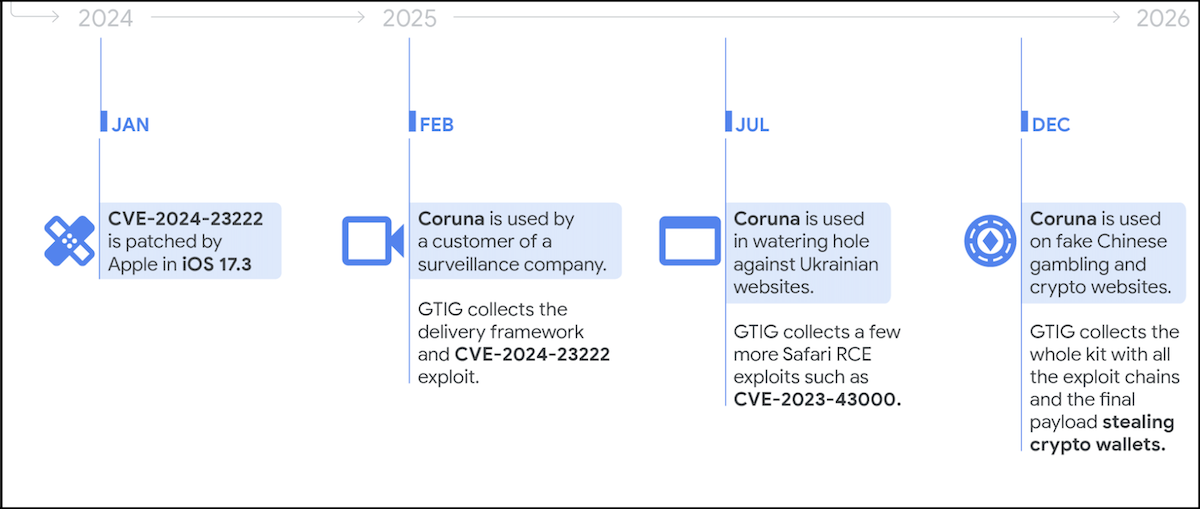
As Google Threat Intelligence Group (GTIG) researchers revealed earlier this week, Coruna uses multiple exploit chains targeting 23 iOS vulnerabilities, many of which were deployed in zero-day attacks.
However, the exploits will not work on recent versions of iOS and will be blocked if the target is using private browsing or has enabled Apple's Lockdown Mode anti-spyware protection feature.
Coruna provides threat actors with Pointer Authentication Code (PAC) bypass, sandbox escape, and PPL (Page Protection Layer) bypass capabilities, and enables them to gain WebKit remote code execution and escalate permissions to Kernel privileges on vulnerable devices.
GTIG observed the exploit kit being used by multiple threat actors last year, including a surveillance vendor customer, a suspected Russian state-backed hacking group (UNC6353), and a financially motivated Chinese threat actor (UNC6691).
The latter deployed it on fake gambling and crypto websites and used it to deliver a malware payload designed to steal infected victims' cryptocurrency wallets.
Mobile security firm iVerify also said that Coruna is an example of "sophisticated spyware-grade capabilities" that migrated "from commercial surveillance vendors into the hands of nation-state actors and, ultimately, mass-scale criminal operations."
On Thursday, CISA added three of the 23 Coruna vulnerabilities to its catalog of Known Exploited Vulnerabilities, ordering Federal Civilian Executive Branch (FCEB) agencies to secure their devices by March 26, as mandated by the Binding Operational Directive (BOD) 22-01.
"Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable," CISA warned.
"These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise."
Although BOD 22-01 applies only to federal agencies, CISA urged all organizations, including private sector companies, to prioritize patching these flaws to secure their devices against attacks as soon as possible.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
