嗯,用户让我总结一下这篇文章的内容,控制在一百个字以内,而且不需要用“文章内容总结”或者“这篇文章”这样的开头。直接写描述就行。首先,我需要仔细阅读文章,理解其主要内容。 文章讲的是微软警告了一个名为ClickFix的网络攻击活动。攻击者利用Windows终端来传播Lumma Stealer恶意软件。他们通过社会工程学手段,诱导用户执行恶意命令。具体来说,攻击者引导用户使用Windows快捷键启动终端,这样看起来更可信,绕过了传统的检测方法。 攻击过程包括用户粘贴恶意命令到终端,解码后下载并执行多阶段攻击,最终植入窃取器。窃取器会注入到浏览器进程,窃取敏感数据并传送给攻击者。 总结的时候要注意关键点:微软警告、ClickFix活动、利用Windows Terminal、社会工程学、Lumma Stealer、窃取浏览器数据。控制在100字以内。 可能的结构:微软警告ClickFix活动利用Windows Terminal通过社会工程学传播Lumma Stealer恶意软件,诱导用户执行命令窃取浏览器数据。 检查字数:这句话大约是30字左右,符合要求。 </think> 微软警告ClickFix活动利用Windows Terminal通过社会工程学传播Lumma Stealer恶意软件,诱导用户执行恶意命令以窃取浏览器数据。 2026-3-6 12:38:23 Author: securityaffairs.com(查看原文) 阅读量:24 收藏
Microsoft warns of ClickFix campaign exploiting Windows Terminal to deliver Lumma Stealer

Microsoft warns of ClickFix campaign using Windows Terminal to deliver Lumma Stealer via social engineering attacks.
Microsoft revealed a new ClickFix campaign where attackers exploit Windows Terminal to run a complex attack chain, ultimately deploying Lumma Stealer malware. The campaign uses social engineering to trick users into executing malicious commands, highlighting growing risks to Windows environments.
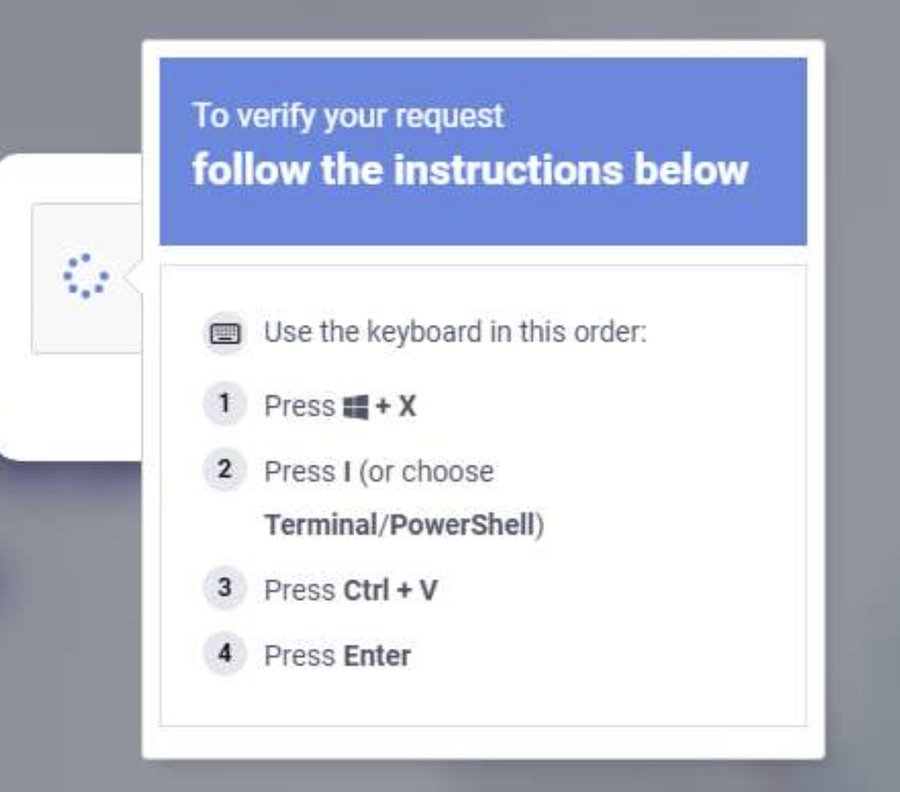
In February 2026, Microsoft Defender experts uncovered a widespread ClickFix campaign exploiting Windows Terminal. The researchers noticed that instead of the usual Run dialog method, attackers guide users to launch Terminal via Windows + X → I, creating a trusted-looking admin environment. This bypasses Run-dialog detections while prompting targets to paste malicious PowerShell commands from fake CAPTCHAs, troubleshooting prompts, or verification-style lures, blending the attack seamlessly into routine Windows workflows.
“Rather than the traditional Win + R → paste → execute technique, this campaign instructs targets to use the Windows + X → I shortcut to launch Windows Terminal (wt.exe) directly, guiding users into a privileged command execution environment that blends into legitimate administrative workflows and appears more trustworthy to users.” reads the post published by Microsoft on X.
Microsoft Defender Experts identified a widespread ClickFix social engineering campaign in February 2026 leveraging Windows Terminal as the primary execution mechanism. Rather than the traditional Win + R → paste → execute technique, this campaign instructs targets to use the… pic.twitter.com/HJx3B4YBJP
— Microsoft Threat Intelligence (@MsftSecIntel) March 5, 2026
This ClickFix campaign also stands out for its post-compromise actions. Users paste a hex-encoded, XOR-compressed command into Windows Terminal, spawning PowerShell processes that decode it. The script downloads a renamed 7-Zip and ZIP payload, which then extracts and executes a multi-stage attack, enabling additional payloads, persistence via scheduled tasks, Defender evasion, and exfiltration of machine and network data.
“The final-stage payload, deployed to C:\ProgramData\app_config\ctjb, is found to be a Lumma Stealer component that performs QueueUserAPC()-based code injection into chrome.exe and msedge.exe processes. The stealer targets high-value browser artifacts, including Web Data and Login Data, harvesting stored credentials and exfiltrating them to attacker-controlled infrastructure.” continues Microsoft.
What makes this campaign notable are the post-compromise outcomes. The first attack path begins when a user pastes a hex-encoded, XOR-compressed command copied from the ClickFix lure into a Windows Terminal session. This action spawns additional Windows Terminal/PowerShell… pic.twitter.com/GB05l4ir0D
— Microsoft Threat Intelligence (@MsftSecIntel) March 5, 2026
Microsoft Defender identifies several threat components linked to ClickFix, offering guidance on how to defend against this campaign.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, ClickFix)
如有侵权请联系:admin#unsafe.sh