嗯,用户让我总结一篇文章,控制在100字以内,而且不需要用“文章内容总结”之类的开头。首先,我得通读整篇文章,抓住主要信息。 文章讲的是一个与伊朗有关的黑客组织Dust Specter,他们通过钓鱼邮件攻击伊拉克政府官员,使用了新的恶意软件。Zscaler ThreatLabz的研究人员发现了这些攻击,并详细描述了攻击链和使用的恶意软件。 我需要把这些信息浓缩到100字以内。重点包括:伊朗关联的组织、目标是伊拉克官员、使用钓鱼邮件和新恶意软件。可能还要提到攻击链和技术细节,但要简洁。 然后,我得确保语言流畅,不使用任何专业术语过多,让读者一目了然。同时,避免开头用“这篇文章总结了...”,直接进入内容。 最后检查字数,确保不超过限制。这样用户的需求就能得到满足了。 </think> 伊朗关联的网络威胁组织Dust Specter通过伪装成伊拉克外交部的钓鱼邮件攻击该国政府官员,利用新型恶意软件如SPLITDROP、TWINTASK等进行间谍活动。研究人员发现该组织可能利用生成式AI开发恶意软件,并通过ClickFix技术诱骗受害者执行恶意代码。 2026-3-6 09:37:23 Author: securityaffairs.com(查看原文) 阅读量:16 收藏
Iran-nexus APT Dust Specter targets Iraq officials with new malware

A campaign by Iran-linked group Dust Specter is targeting Iraqi officials with phishing emails delivering new malware families.
Zscaler ThreatLabz researchers linked the Iran-nexus group Dust Specter to a campaign targeting Iraqi government officials. Threat actors impersonated the country’s Ministry of Foreign Affairs in phishing messages that delivered previously unseen malware, including SPLITDROP, TWINTASK, TWINTALK, and GHOSTFORM, through multiple infection chains.
“In January 2026, Zscaler ThreatLabz observed activity by a suspected Iran-nexus threat actor targeting government officials in Iraq.” reads the report published by Zscaler. “Due to significant overlap in tools, techniques, and procedures (TTPs), as well as victimology, between this campaign and activity associated with Iran-nexus APT groups, ThreatLabz assesses with medium-to-high confidence that an Iran-nexus threat actor conducted this operation. ThreatLabz tracks this group internally as Dust Specter. “
The researchers analyzed two attack chains used in the Dust Specter campaign targeting Iraqi officials.
Attack Chain 1 begins with a password-protected archive containing a dropper named SPLITDROP, disguised as a WinRAR application. Once executed, it decrypts and deploys two modules: TWINTASK, a worker component that executes PowerShell commands from a local file, and TWINTALK, a command-and-control (C2) orchestrator.
“Attack Chain 1 is delivered in a password-protected RAR archive named mofa-Network-code.rar. The password for this archive is: 92,110-135_118-128. A 32-bit .NET binary, disguised as a WinRAR application, is present inside this archive and starts the attack chain on the endpoint.” continues the report. “This binary functions as a dropper and ThreatLabz named it SPLITDROP because it drops two modules that we named TWINTASK and TWINTALK. “
The malware establishes persistence through registry keys and uses DLL sideloading with legitimate software such as VLC and WingetUI. TWINTALK communicates with the C2 server using randomized delays, custom URI paths, and JWT tokens to evade detection. Commands allow attackers to execute scripts, upload files, or download additional payloads.
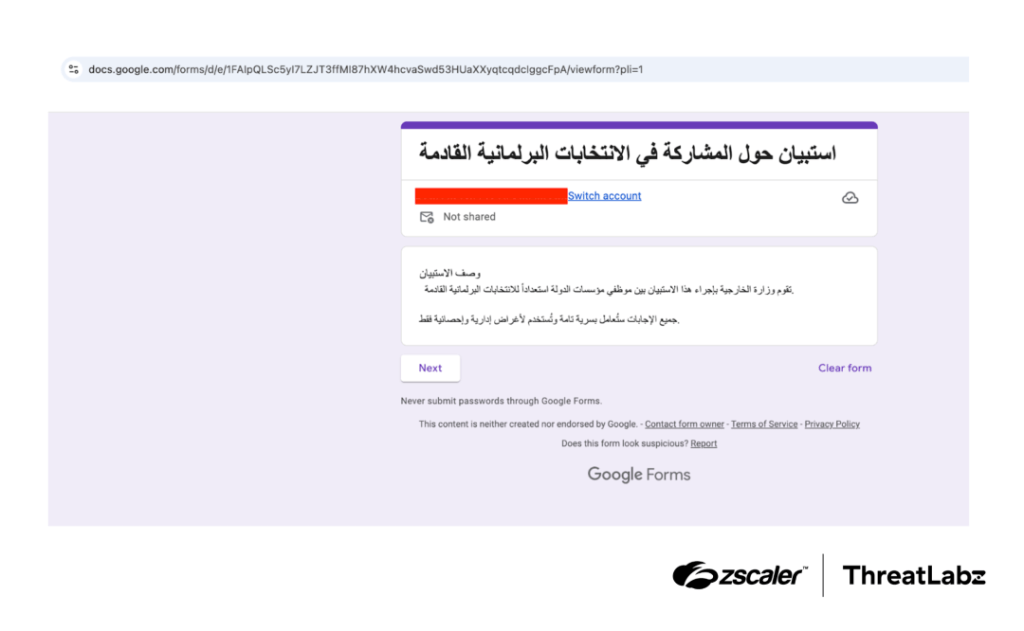
Attack Chain 2, called GHOSTFORM, consolidates the same functionality into a single binary that executes commands directly in memory, reducing filesystem traces. It also opens a fake Google Form posing as a survey from Iraq’s Ministry of Foreign Affairs to lure victims. The malware employs stealth techniques such as invisible Windows forms for delayed execution and mutex checks to avoid multiple instances.
ThreatLabz found indicators that generative AI may have been used to develop the TWINTALK and GHOSTFORM malware. During code analysis, researchers identified unusual elements such as emojis and Unicode text embedded in functions. They also observed placeholder values—like the seed 0xABCDEF—often associated with AI-generated code, suggesting automated tools may have assisted in malware development.
The campaign also used a ClickFix lure disguised as a Cisco Webex meeting page to trick victims into running malicious PowerShell commands that download and schedule malware execution.
“ThreatLabz found that the TWINTALK C2 domain, meetingapp[.]site, was also used by Dust Specter in July 2025 to host a web page disguised as a Cisco Webex meeting invitation.” states the report. “The web page included a link to download the legitimate Cisco Webex software and prompted the victim to choose the “Webex for Government” option. The web page also lures the victim into following the instructions shown in the figure below to retrieve the meeting ID.”
ThreatLabz attributes the activity to Dust Specter, an Iran-linked threat actor, citing targeting patterns, malware design, and tactics consistent with previous Iranian cyber-espionage operations.
“This campaign, attributed with medium-to-high confidence to Dust Specter, likely targeted government officials using convincing social engineering lures impersonating Iraq’s Ministry of Foreign Affairs. ThreatLabz identified previously undocumented lightweight custom .NET-based droppers and backdoors used in this operation.” concludes the report. “The activity also reflects broader trends, including ClickFix-style techniques and the growing use of generative AI for malware development.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Iran)
如有侵权请联系:admin#unsafe.sh

