好的,我现在要帮用户总结这篇文章的内容,控制在100个字以内。首先,我需要通读整篇文章,抓住主要信息。 文章主要讲的是Google的GTIG在2025年报告了90个零日漏洞被利用,比2024年的78个有所增加。这些漏洞中,近一半(43个)针对企业技术,创下历史新高。浏览器的漏洞利用降至历史低点,而操作系统漏洞被更多利用。国家行为者主要攻击边缘设备和安全设备,商业 surveillance 公司继续关注移动和浏览器链。 此外,文章提到攻击者在提升技术复杂度,使用更多链式漏洞来突破高保护组件。边缘设备如路由器仍是主要目标,因为它们缺乏检测能力。操作系统是被利用最多的类别,占39个漏洞。移动操作系统漏洞增加到15例。浏览器只占不到10%。 2025年,大多数零日攻击针对大型科技公司和安全网络公司,如Cisco、Fortinet等。攻击目标通常是远程代码执行或权限提升。商业 surveillance 公司成为最活跃的零日利用者,超过了传统国家资助的间谍组织。 最后,Google预测2026年人工智能在安全领域的使用会增加,威胁行为者会用AI加速漏洞发现和开发。 现在我要把这些信息浓缩到100字以内。重点包括:90个零日漏洞增加、企业目标增多、操作系统和移动OS被更多利用、商业 surveillance 公司活跃、AI预测等。 可能的结构是:Google报告2025年90个零日漏洞被利用,比2024年增加12个;企业技术成为主要目标;操作系统和移动OS被更多利用;商业 surveillance 公司活跃;AI预计在安全中发挥更大作用。 现在检查字数是否合适,并确保信息准确无误。 </think> Google报告称2025年发现了90个零日漏洞被利用,较2024年的78个有所上升,其中近半数针对企业系统,操作系统和移动端漏洞增多,浏览器攻击减少;商业间谍公司成为最活跃的零日使用者;预计未来人工智能将更广泛地应用于漏洞发现与防御。 2026-3-6 07:58:2 Author: securityaffairs.com(查看原文) 阅读量:16 收藏
Google GTIG: 90 zero-day flaws exploited in 2025 as enterprise targets grow

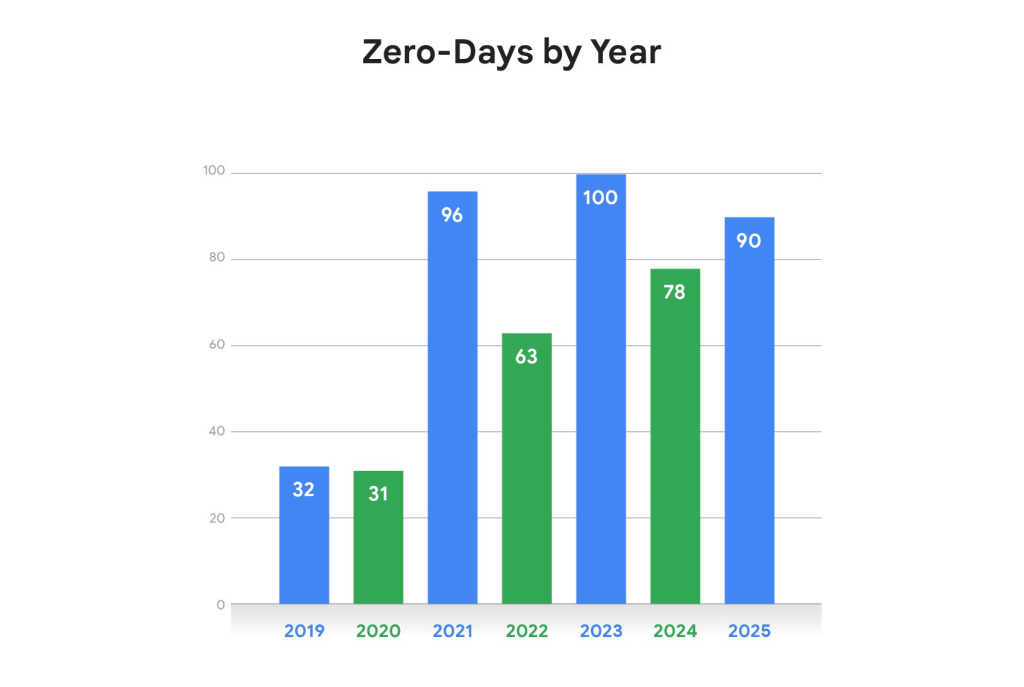
Google’s GTIG reports 90 zero-day vulnerabilities exploited in the wild in 2025, up from 78 in 2024, with a growing share targeting enterprise systems.
Google’s Threat Intelligence Group (GTIG) identified 90 zero-day vulnerabilities exploited in the wild in 2025. While slightly below the 100 observed in 2023, the number increased from 78 in 2024, with researchers noting a rising trend of attacks specifically targeting enterprise technologies and corporate infrastructure.
Nearly half of the flaws (43, or 48%) targeted enterprise technologies, marking a record share and confirming a shift toward enterprise-focused attacks. Browser exploitation declined to historic lows, while operating system flaws were increasingly abused. Nation-state actors mainly targeted edge devices and security appliances, while commercial surveillance vendors continued focusing on mobile and browser exploit chains.
“As vendor mitigations evolve and increasingly prevent more simplistic exploitation, threat actors have been forced to expand or adjust their techniques. In some cases, attackers have increased the number of chained vulnerabilities to reach desired levels of access within highly protected components.” reads the report published by Google. “Conversely, threat actors have also managed successful exploitation with fewer or singular bugs by targeting lower levels of access within a single capability, such as an application or service.”
Edge devices such as routers and security appliances remain prime targets because they typically lack EDR visibility, making intrusions harder to detect. Another 47 zero-days (52%) targeted end-user platforms. Operating systems were the most exploited category with 39 flaws, continuing an upward trend, while mobile OS exploits rose to 15 cases. Browsers accounted for less than 10% of zero-day activity, suggesting improved security hardening, though better attacker operational security may also be reducing visible exploitation.
In 2025, most exploited zero-days targeted major tech vendors due to their massive user bases across operating systems, browsers, and mobile platforms. Security and networking companies such as Cisco, Fortinet, Ivanti, and VMware were also frequent targets because of the strategic value of VPNs, virtualization, and edge infrastructure. Many attacks aimed at remote code execution or privilege escalation, often exploiting injection flaws, memory corruption, or weak access controls.
Commercial surveillance vendors (CSVs) were the most active users of zero-day exploits in 2025, surpassing traditional state-sponsored espionage groups for the first time. Firms such as Intellexa continued selling advanced spyware to government clients. However, China-linked cyber-espionage groups remained the most prolific among nation-state actors, often targeting edge and networking devices to maintain long-term access. Financially motivated groups also increased zero-day use, including ransomware operations linked to FIN11 and the Clop ransomware group. Researchers also observed sophisticated exploit chains affecting browsers, mobile devices, and enterprise appliances, including attacks on SonicWall systems that combined authentication bypass, remote code execution, and privilege escalation vulnerabilities.
Google expects AI use to grow in 2026, and threat actors will leverage it to speed up vulnerability discovery and exploit development. Defenders can use AI to strengthen security operations by identifying unknown flaws early and mitigating them before they are weaponized.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, zero-day)
如有侵权请联系:admin#unsafe.sh

