
好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,抓住关键点。 文章讲的是一个与中国有关的高级持续性威胁组织UAT-9244,自2024年起针对南美电信服务提供商展开攻击。他们利用了三种新型恶意软件:TernDoor、PeerTime和BruteEntry。这些软件分别针对Windows、Linux和网络边缘设备,能够进行远程控制、数据收集和构建代理基础设施。 接下来,我需要将这些信息浓缩到100字以内。要确保包含攻击者身份、目标地区、使用的恶意软件及其功能。同时,语言要简洁明了,避免复杂的术语。 可能的结构是:首先介绍攻击者及其目标,然后提到使用的恶意软件及其作用。这样既全面又简洁。 最后检查字数是否符合要求,并确保没有遗漏关键信息。 </think> 中国关联的网络威胁组织UAT-9244自2024年起针对南美电信服务提供商发起攻击,利用三种新型恶意软件(TernDoor、PeerTime和BruteEntry)针对Windows、Linux及网络边缘设备进行远程控制、数据收集及代理基础设施构建。 2026-3-5 23:30:22 Author: www.bleepingcomputer.com(查看原文) 阅读量:11 收藏

A China-linked advanced persistent threat actor tracked as UAT-9244 has been targeting telecommunication service providers in South America since 2024, compromising Windows, Linux, and network-edge devices.
According to Cisco Talos researchers, the adversary is closely associated with the FamousSparrow and Tropic Trooper hacker groups, but is tracked as a separate activity cluster.
This assessment has high confidence and is based on similar tooling, tactics, techniques, and procedures (TTPs), and victimology observed in attacks attributed to the threat actors.
The researchers note that while UAT-9244 shares the same target profile as Salt Typhoon, they could not establish a solid connection between the two activity clusters.
New malware targeting telco networks
The researchers found that the campaign used three previously undocumented malware families: TernDoor, a Windows backdoor; PeerTime, a Linux backdoor that uses BitTorrent; and BruteEntry, a brute-force scanner that builds proxy infrastructure (ORBs).
TernDoor is deployed through DLL side-loading, using the legitimate executable wsprint.exe to load malicious code from BugSplatRc64.dll, which decrypts and executes the final payload in memory (injected into msiexec.exe).
The malware contains an embedded Windows driver, WSPrint.sys, which is used to terminate, suspend, and resume processes.
Persistence is achieved via scheduled tasks and Windows Registry modifications, which are also used to hide the scheduled task.
Additionally, TernDoor can execute commands via remote shell, run arbitrary processes, read/write files, collect system information, and self-uninstall.
PeerTime is an ELF Linux backdoor that targets multiple architectures (ARM, AARCH, PPC, MIPS), suggesting it was designed to compromise a broad range of embedded systems and network devices used in telecom environments.

Source: Cisco Talos
Cisco Talos documented two versions for PeerTime. One variant is written in C/C++ and the other is based on Rust. The researchers also noticed Simplified Chinese debug strings in the instrumentor binary, an indicator of its origin.
Its payload is decrypted and loaded in memory, and its process is renamed to appear legitimate.
PeerTime, an ELF-based peer-to-peer (P2P) backdoor, uses the BitTorrent protocol for command-and-control (C2) communications, downloads and executes payloads from peers, and uses BusyBox to write the files on the host.
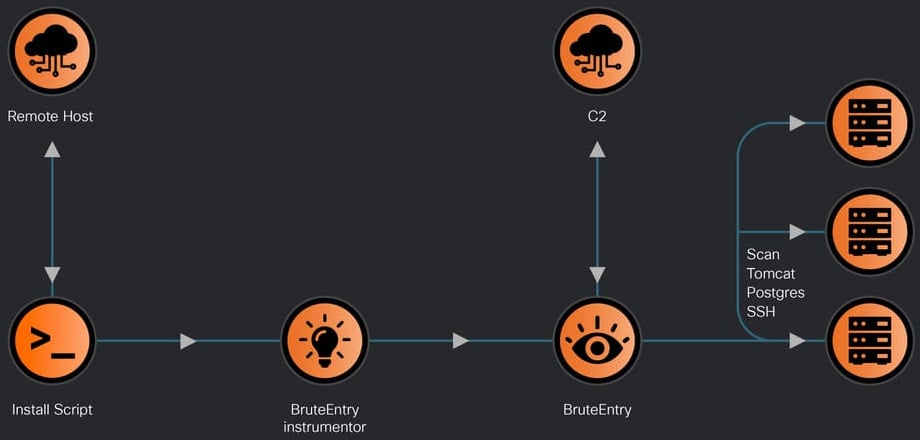
Finally, there’s BruteEntry, which consists of a Go-based instrumentor binary and a brute-forcing component. Its role is to turn compromised devices into scanning nodes, known as Operational Relay Boxes (ORBs).
Source: Cisco Talos
The attacker uses the machines running BruteEntry to scan for new targets and brute-force access to SSH, Postgres, and Tomcat. Login attempt results are sent back to the C2 with task status and notes.
In a technical report today, Cisco Talos researchers provide details on the capabilities of the three pieces of malware, how they are deployed, and achieve persistence.
Cisco Talos researchers have listed indicators of compromise (IoCs) associated with the observed UAT-9244 activity, which defenders can use to detect and block these attacks early.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
