
嗯,用户让我帮忙总结一篇文章,控制在一百个字以内,而且不需要特定的开头。首先,我需要通读整篇文章,抓住主要信息。 文章主要讲的是Google Threat Intelligence Group在2025年追踪到90个零日漏洞,比2024年增加了15%。这些漏洞中,一半是针对企业软件和设备的。零日漏洞指的是被攻击者利用、但尚未被供应商修复的安全问题。 接下来,文章提到这些漏洞主要集中在内存安全问题上,占了35%。攻击者主要针对操作系统、安全设备、网络基础设施等。微软是被攻击最多的厂商,其次是谷歌、苹果等。 还有,商业间谍软件供应商首次成为最大的零日漏洞利用者,超过了国家资助的间谍组织。此外,浏览器相关的零日漏洞有所下降,可能是因为安全增强或者攻击者使用了更隐蔽的技术。 最后,报告还提到AI工具可能会加速漏洞的发现和利用,预计2026年零日漏洞的利用会继续保持高位。 总结一下,我需要把这些关键点浓缩到100字以内。确保涵盖零日漏洞的数量、增长情况、目标类型、主要厂商以及趋势变化。 </think> Google Threat Intelligence Group报告称,2025年共追踪到90个被利用的零日漏洞,较2024年增长15%,其中近半数针对企业软件和设备。内存安全问题占35%,操作系统为最常被攻击目标。微软是被攻击最多的厂商。商业间谍软件供应商首次成为最大用户。浏览器相关漏洞减少。AI工具可能加速漏洞利用。 2026-3-5 15:15:18 Author: www.bleepingcomputer.com(查看原文) 阅读量:8 收藏

Google Threat Intelligence Group (GTIG) tracked 90 zero-day vulnerabilities actively exploited throughout 2025, almost half of them in enterprise software and appliances.
The figure is a 15% increase compared to 2024, when 78 zero-days were exploited in the wild, but lower than the record 100 zero days tracked in 2023.
Zero-day vulnerabilities are security issues in software products that attackers exploit, usually before the vendor learns about them and develops a patch. They are highly valued by threat actors because they often enable initial access, remote code execution, or privilege escalation.
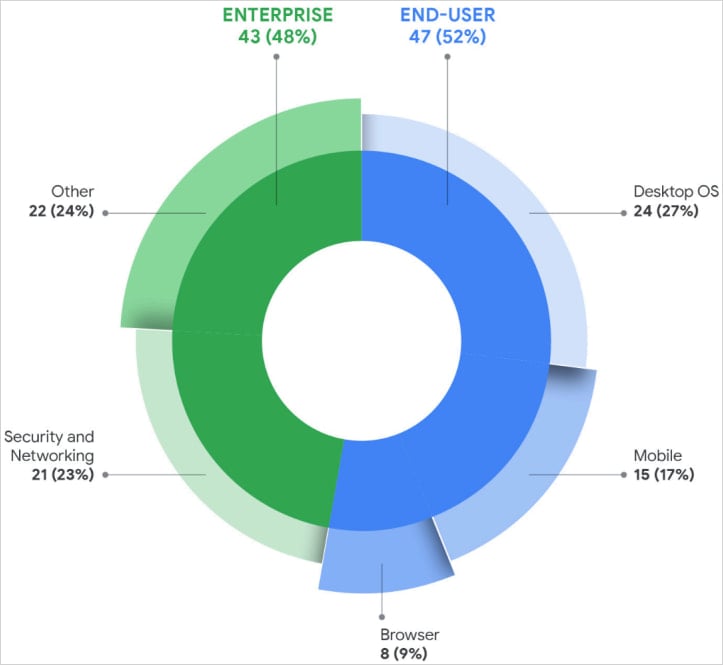
A report from GTIG today notes that of the 90 zero-days tracked as exploited in 2025, 47 of them targeted end-user platforms, and 43 targeted enterprise products.
The type of exploited flaws includes remote code execution, privilege escalation, injection and deserialization flaws, authorization bypasses, and memory corruption (use-after-free) bugs. Google reports that memory safety issues accounted for 35% of all exploited zero-day vulnerabilities last year.
The most targeted enterprise systems were security appliances, networking infrastructure, VPNs, and virtualization platforms, as these provide privileged network access and often lack EDR monitoring.
GTIG reports that bugs in operating systems were the most exploited category last year, with attacks leveraging 24 zero-day vulnerabilities in desktop OSs and 15 in mobile platforms.
Zero-day exploits in web browsers dropped to eight, a sharp decline compared to previous years.
Google’s analysts speculate this might be due to increased security hardening in this software category, though it may also be a case of threat actors using more advanced evasion tactics and being better at hiding malicious activity.
Source: Google
According to GTIG researchers, Microsoft was the top vendor targeted with zero days last year (25), followed by Google with 11, Apple with eight, and Cisco and Fortinet with four each, and Ivanti and VMware with three each.
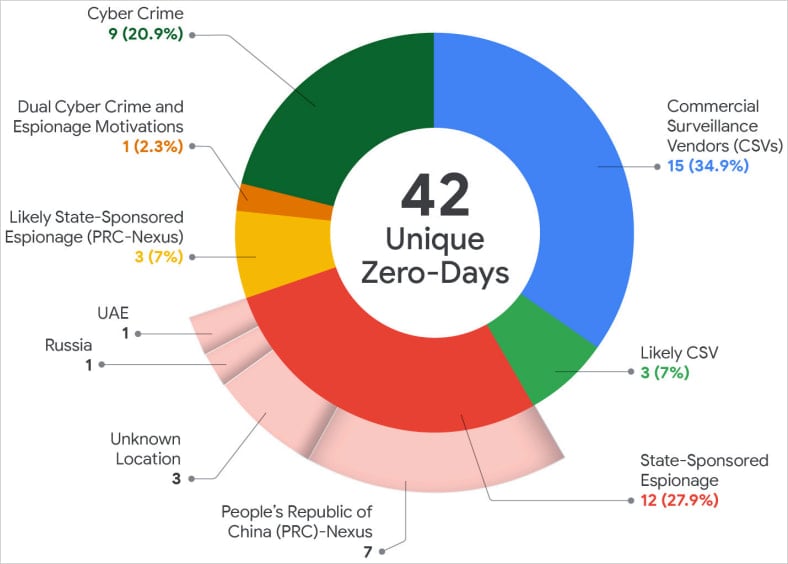
For the first time since Google started tracking zero-day exploitation, commercial spyware vendors were the largest users of undocumented flaws, surpassing state-sponsored espionage groups, which may also be deploying more effective hiding techniques.
“This continues to reflect a trend we began to observe over the last several years–a growing proportion of zero-day exploitation is conducted by CSVs and/or their customers, demonstrating a slow but sure movement in the landscape,” reads the GTIG report.
Source: Google
Google researchers say that among state-sponsored actors, China-linked espionage groups remain the most active, with 10 zero-days exploited in 2025. The attacks targeted primarily edge devices, security appliances, and networking equipment for long-term persistent access.
Another notable trend observed last year was the increase in zero-day exploitation by financially motivated actors (ransomware, data extortion), who accounted for nine of the flaws.
GTIG believes that the use of AI tools will help automate vulnerability discovery and accelerate exploit development, so exploitation of zero-day flaws in 2026 is expected to remain high.
The Brickstorm campaign is highlighted in the report as an example of how hackers are shifting their focus from source code theft to discovering flaws in future software products.
To detect and contain zero-day exploitation, Google recommends reducing attack surfaces and privilege exposure, continuously monitoring systems for anomalous behavior, and maintaining rapid patching and incident-response processes.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
