好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,理解其主要内容。 文章主要讲的是俄罗斯针对乌克兰的网络攻击活动,使用了BadPaw和MeowMeow这两种新型恶意软件。攻击方式是通过钓鱼邮件发送ZIP文件,里面包含HTA文件,伪装成乌克兰语的边境申请文件,诱导用户点击。一旦执行,就会下载BadPaw加载器,并与C2服务器通信,进而部署MeowMeow后门程序。 此外,这两种恶意软件都使用了.NET Reactor打包器来混淆代码,增加分析难度。它们还有多种防御机制,比如检查系统环境以避免被分析工具检测到。研究人员将这次攻击归因于俄罗斯支持的APT28组织。 现在我需要将这些信息浓缩到100字以内。要抓住关键点:俄罗斯针对乌克兰的攻击、使用的新恶意软件、钓鱼邮件作为入口、多阶段感染链、防御机制以及归因于APT28。 可能的结构是:俄罗斯通过钓鱼邮件用BadPaw和MeowMeow攻击乌克兰,这两者用.NET Reactor混淆代码,并有多重防御机制,如环境检查和沙箱检测。研究人员认为是APT28所为。 现在试着组织语言: “俄罗斯针对乌克兰实体发起网络攻击,利用BadPaw和MeowMeow恶意软件通过钓鱼邮件传播。这些恶意软件采用多阶段感染链,并使用.NET Reactor混淆代码以逃避检测。它们还具备环境检查功能以避免被分析工具发现。研究人员将此次攻击归因于与俄罗斯有关的APT28组织。” 这样大约100字左右。 </think> 俄罗斯针对乌克兰实体发起网络攻击,利用BadPaw和MeowMeow恶意软件通过钓鱼邮件传播。这些恶意软件采用多阶段感染链,并使用.NET Reactor混淆代码以逃避检测。它们还具备环境检查功能以避免被分析工具发现。研究人员将此次攻击归因于与俄罗斯有关的APT28组织。 2026-3-5 14:58:48 Author: securityaffairs.com(查看原文) 阅读量:10 收藏
Russian APT targets Ukraine with BadPaw and MeowMeow malware

Researchers uncovered a Russian campaign targeting Ukrainian entities with new malware families BadPaw and MeowMeow delivered through phishing emails.
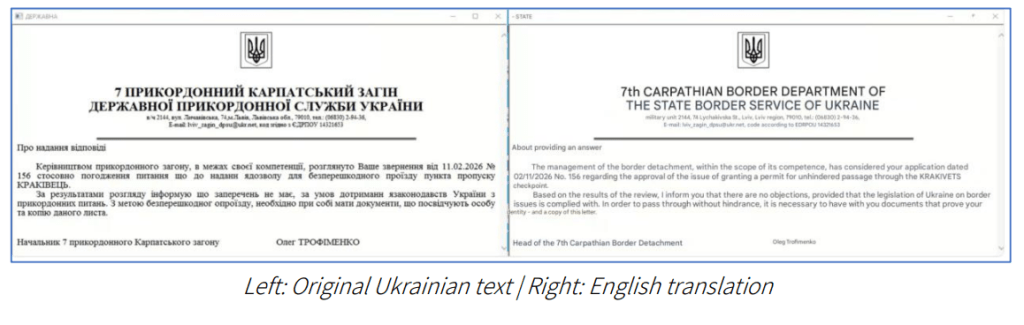
Researchers reported a phishing campaign linked to Russia that targets Ukrainian organizations using two new malware families, BadPaw and MeowMeow. The attack chain begins with a phishing email carrying a link to a ZIP archive. When opened, an HTA file displays a Ukrainian-language lure about border crossing appeals while secretly launching the infection chain.
“The attack chain initiates with a phishing email containing a link to a ZIP archive. Once
extracted, an initial HTA file displays a lure document written in Ukrainian concerning border
crossing appeals to deceive the victim.” reads the report published by ClearSky. “Simultaneously, the infection triggers the download of BadPaw, a .NET-based loader. Upon establishing command-and-control (C2) communication, the loader deploys MeowMeow, a sophisticated backdoor.”

Researchers found that both malware strains use the .NET Reactor packer to make the analysis and reverse engineering harder, showing the attackers’ intent to evade detection and maintain long-term persistence.
“An additional layer of defense employed by BadPaw is the use of .NET Reactor, a commercial protection and obfuscation tool for .NET assemblies. This packer obfuscates the underlying code to hinder static analysis and reverse engineering.” continues the report.
The malware also includes multiple defense mechanisms. Its components stay inactive unless launched with specific parameters, otherwise displaying a benign interface and executing harmless code.
The MeowMeow backdoor adds environmental checks, scanning systems for virtual machines and analysis tools such as Wireshark, ProcMon, and Fiddler. If it detects a sandbox or research environment, it immediately stops execution to avoid investigation.
Researchers at ClearSky attribute the campaign with high confidence to a Russia-linked cyberespionage group and with lower confidence to the threat actor APT28. Their assessment relies on three factors: the targeting of Ukrainian entities, Russian-language artifacts in the code, and tactics consistent with previous Russian cyber operations, including multi-stage infection chains and .NET-based loaders.
In parallel, the attack chain leads to the deployment of a .NET-based loader called BadPaw, which then establishes communication with a remote server to fetch and deploy a sophisticated backdoor called MeowMeow.
The campaign has been attributed with moderate confidence to the Russian state-sponsored threat actor known as APT28, based on the targeting footprint, the geopolitical nature of the lures used, and overlaps with techniques observed in previous Russian cyber operations.
ClearSky’s research details outline a multi-stage infection chain beginning with a phishing email sent via the Ukrainian provider ukr[.]net, a service previously abused in Russian campaigns. The email contains a link that first loads a tracking pixel to notify attackers when a victim clicks, then redirects to a shortened URL that downloads a ZIP archive.
Inside the archive is a disguised HTA file posing as an HTML document. When executed, it opens a decoy document about a Ukrainian border-crossing appeal while silently launching the malicious routine. The HTA performs anti-analysis checks by verifying the system’s installation date and aborting execution on recently installed systems, a common sandbox-evasion tactic.
“The dropped decoy document serves as a social engineering tactic, presenting a confirmation of receipt for a government appeal regarding a Ukrainian border crossing. This lure is intended to maintain the veneer of legitimacy while the HTA file executes its secondary stages in the background.” continues the report. “To evade detection and identify potential sandbox environments, the HTA file performs an environmental check by inspecting the following Registry key: HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\InstallDate By querying this value, the malware calculates the “age” of the operating system. If the system was installed less than ten days prior to execution, the malware terminates. This is a common anti-analysis technique used to avoid execution on freshly provisioned virtual machines or automated analysis sandboxes”

If conditions are met, it searches for the original archive, extracts additional components, and establishes persistence through a scheduled task. A VBS script then retrieves hidden payload data embedded within an image using steganography, extracting a PE file that researchers identified as the BadPaw loader, which ultimately deploys the MeowMeow backdoor and establishes command-and-control communication.
Researchers found Russian-language strings in the malware code, including one indicating the time needed to reach an operational state. These artifacts suggest a Russian origin and may reflect an OPSEC mistake or leftover development elements not adapted for Ukrainian targets.
“The presence of these Russian-language strings suggests two possibilities: the threat actor committed an operational security (OPSEC) error by failing to localize the code for the Ukrainian target environment, or they inadvertently left Russian development artifacts within the code during the malware’s production phase.” concludes the report.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, MeowMeow malware)
如有侵权请联系:admin#unsafe.sh