好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,抓住主要信息。 文章讲的是Google发现了一个针对iOS 13到17.2.1版本的Coruna iOS漏洞工具包。这个工具包有5个完整的攻击链,总共23个漏洞。Google的威胁情报小组跟踪了这个工具包在不同攻击中的使用情况,包括乌克兰的网络钓鱼活动和中国的金融威胁行为。 用户的要求是用中文总结,不超过100字,并且不需要特定的开头。所以我要提炼出关键点:Google发现Coruna漏洞工具包,影响iOS 13-17.2.1,包含23个漏洞和5个攻击链,用于多种网络攻击。 现在把这些信息整合成简洁的一段话,确保在字数限制内。 </think> Google发现名为Coruna的iOS漏洞工具包,针对iOS 13至17.2.1版本设备,包含23个漏洞和5个完整攻击链。该工具包被用于乌克兰网络钓鱼活动及中国金融网络攻击中。 2026-3-5 06:10:52 Author: securityaffairs.com(查看原文) 阅读量:18 收藏
Google uncovers Coruna iOS Exploit Kit targeting iOS 13–17.2.1

Google warns of the Coruna iOS exploit kit, using 23 exploits across five chains to target iPhones running iOS 13–17.2.1, but not the latest iOS.
Google’s Threat Intelligence Group has identified a powerful new iOS exploit kit called Coruna (also known as CryptoWaters) that targets Apple iPhones running iOS versions 13.0 through 17.2.1. The kit includes five full exploit chains and a total of 23 exploits.
| Codename | CVE | Type |
|---|---|---|
| buffout | CVE-2021-30952 | WebContent R/W |
| jacurutu | CVE-2022-48503 | WebContent R/W |
| bluebird | No CVE | WebContent R/W |
| terrorbird | CVE-2023-43000 | WebContent R/W |
| cassowary | CVE-2024-23222 | WebContent R/W |
| breezy | No CVE | WebContent PAC bypass |
| breezy15 | No CVE | WebContent PAC bypass |
| seedbell | No CVE | WebContent PAC bypass |
| seedbell_16_6 | No CVE | WebContent PAC bypass |
| seedbell_17 | No CVE | WebContent PAC bypass |
| IronLoader | CVE-2023-32409 | WebContent sandbox escape |
| NeuronLoader | No CVE | WebContent sandbox escape |
| Neutron | CVE-2020-27932 | PE |
| Dynamo | CVE-2020-27950 | PE (infoleak) |
| Pendulum | No CVE | PE |
| Photon | CVE-2023-32434 | PE |
| Parallax | CVE-2023-41974 | PE |
| Gruber | No CVE | PE |
| Quark | No CVE | PPL Bypass |
| Gallium | CVE-2023-38606 | PPL Bypass |
| Carbone | No CVE | PPL Bypass |
| Sparrow | CVE-2024-23225 | PPL Bypass |
| Rocket | CVE-2024-23296 | PPL Bypass |
While highly capable against iPhones running iOS 13.0 through 17.2.1versions, Coruna is ineffective against the latest iOS release, according to Google.
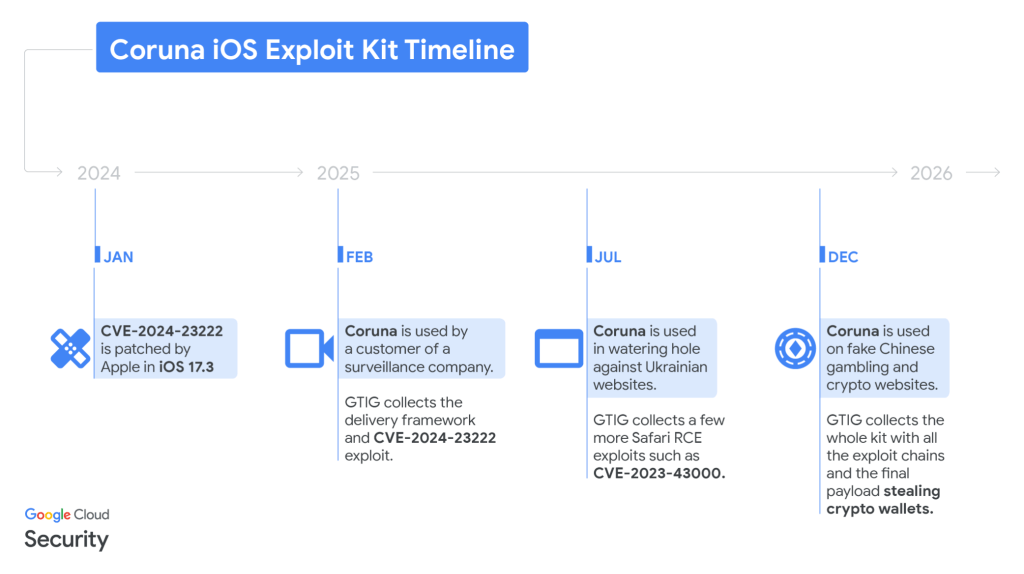
GTIG tracked the use of the exploit in highly targeted attacks by a surveillance vendor’s customer, in Ukrainian watering hole campaigns by UNC6353, and later in broad-scale attacks by Chinese financial threat actor UNC6691, showing an active market for “second-hand” zero-day exploits. Multiple threat actors now reuse and adapt these advanced techniques for new vulnerabilities.
GTIG shared the findings to raise awareness and protect users, adding identified domains to Safe Browsing.
Initial discovery occurred in February 2025 when GTIG captured a previously unseen JavaScript framework delivering an iOS exploit chain from a surveillance vendor’s customer.
“In February 2025, we captured parts of an iOS exploit chain used by a customer of a surveillance company.” reads the report published by GTIG. “The exploits were integrated into a previously unseen JavaScript framework that used simple but unique JavaScript obfuscation techniques.”
“The core technical value of this exploit kit lies in its comprehensive collection of iOS exploits, with the most advanced ones using non-public exploitation techniques and mitigation bypasses.”

The framework uses fingerprinting to detect device type and iOS version, then loads the appropriate WebKit RCE exploit and pointer authentication bypass. One recovered exploit, CVE-2024-23222, was later patched in iOS 17.3.
Government-backed attackers used the same framework in Ukrainian watering hole attacks, delivering multiple RCE exploits to select iPhone users. Later, Chinese scam websites deployed the full Coruna kit, dropping the same exploits via hidden iFrames on fake financial and crypto sites. GTIG collected hundreds of samples covering all five exploit chains and observed debug versions exposing internal exploit names, confirming the kit’s internal name as Coruna.

The Coruna exploit kit relies on a highly engineered framework that links all components through shared utilities and custom loaders. It avoids devices in Lockdown Mode or private browsing, derives resource URLs from a hard-coded cookie, and delivers WebKit RCE and PAC bypasses in clear form. After exploitation, a binary loader deploys encrypted, compressed payloads disguised as .min.js files, tailored to specific chips and iOS versions. In total, the kit includes 23 exploits covering iOS 13 through 17.2.1, with advanced mitigation bypasses and reusable modules for defeating memory and kernel protections.
“Photon and Gallium are exploiting vulnerabilities that were also used as zero-days as part of Operation Triangulation, discovered by Kaspersky in 2023. The Coruna exploit kit also embeds reusable modules to ease the exploitation of the aforementioned vulnerabilities. For example, there is a module called rwx_allocator using multiple techniques to bypass various mitigations preventing allocation of RWX memory pages in userland.” states the report. “The kernel exploits are also embedding various internal modules allowing them to bypass kernel-based mitigations such as kernel-mode PAC.”
At the end of the chain, a stager called PlasmaLoader injects into a root daemon and deploys a financially focused payload.
“The injected payload doesn’t exhibit the usual capabilities that we would expect to see from a surveillance vendor, but instead steals financial information. The payload can decode QR codes from images on disk. It also has a module to analyze blobs of text to look for BIP39 word sequences or very specific keywords like “backup phrase” or “bank account.” If such text is found in Apple Memos it will be sent back to the C2.” continues the report .”More importantly, the payload has the ability to collect and run additional modules remotely, with the configuration retrieved from http://<C2 URL>/details/show.html. “
The malware scans for crypto wallets, backup phrases, and banking data, exfiltrating sensitive information and loading additional modules from command-and-control servers. It targets numerous cryptocurrency apps, uses encrypted communications, and falls back on a custom domain generation algorithm seeded with “lazarus” to maintain persistence.
Google published Indicators of Compromise (IOCs) and Yara rules for this exploit.
(SecurityAffairs – hacking, newsletter)
如有侵权请联系:admin#unsafe.sh