2026-03-04
4 min read

We often talk about the "ideal" state, one where every device has a managed client like the Cloudflare One Client installed, providing deep visibility and seamless protection. However, reality often gets in the way.
Sometimes you are dealing with a company acquisition, managing virtual desktops, or working in a highly regulated environment where you simply cannot install software on an endpoint. You still need to protect that traffic, even when you don’t fully manage the device.
Closing this gap requires moving the identity challenge from the device to the network itself. By combining the browser’s native proxy capabilities with our global network, we can verify users and enforce granular policies on any device that can reach the Internet. We’ve built the Gateway Authorization Proxy and Proxy Auto-Configuration (PAC) File Hosting to automate this authentication and simplify how unmanaged devices connect to Cloudflare.
The problem: sometimes IP addresses aren't enough
Back in 2022, we released proxy endpoints that allowed you to route traffic through Cloudflare to apply filtering rules. It solved the immediate need for access, but it had a significant "identity crisis."
Because that system relied on static IP addresses to identify users, it was a bit like a security guard who only recognizes cars, not the people inside them. If a car (a specific IP) showed up, it was let in. But if the driver switched cars or worked from a different location, the guard got confused. This created a few major headaches:
Anonymous Logs: We knew the IP address, but we didn’t know the person.
Brittle Policies: If a user moved to a new home or office, the endpoint broke or required an update.
Manual Maintenance: You had to host your own PAC file (the "GPS" that tells your browser where the proxy is) — one more thing for your team to manage.
The solution: the Authorization Proxy
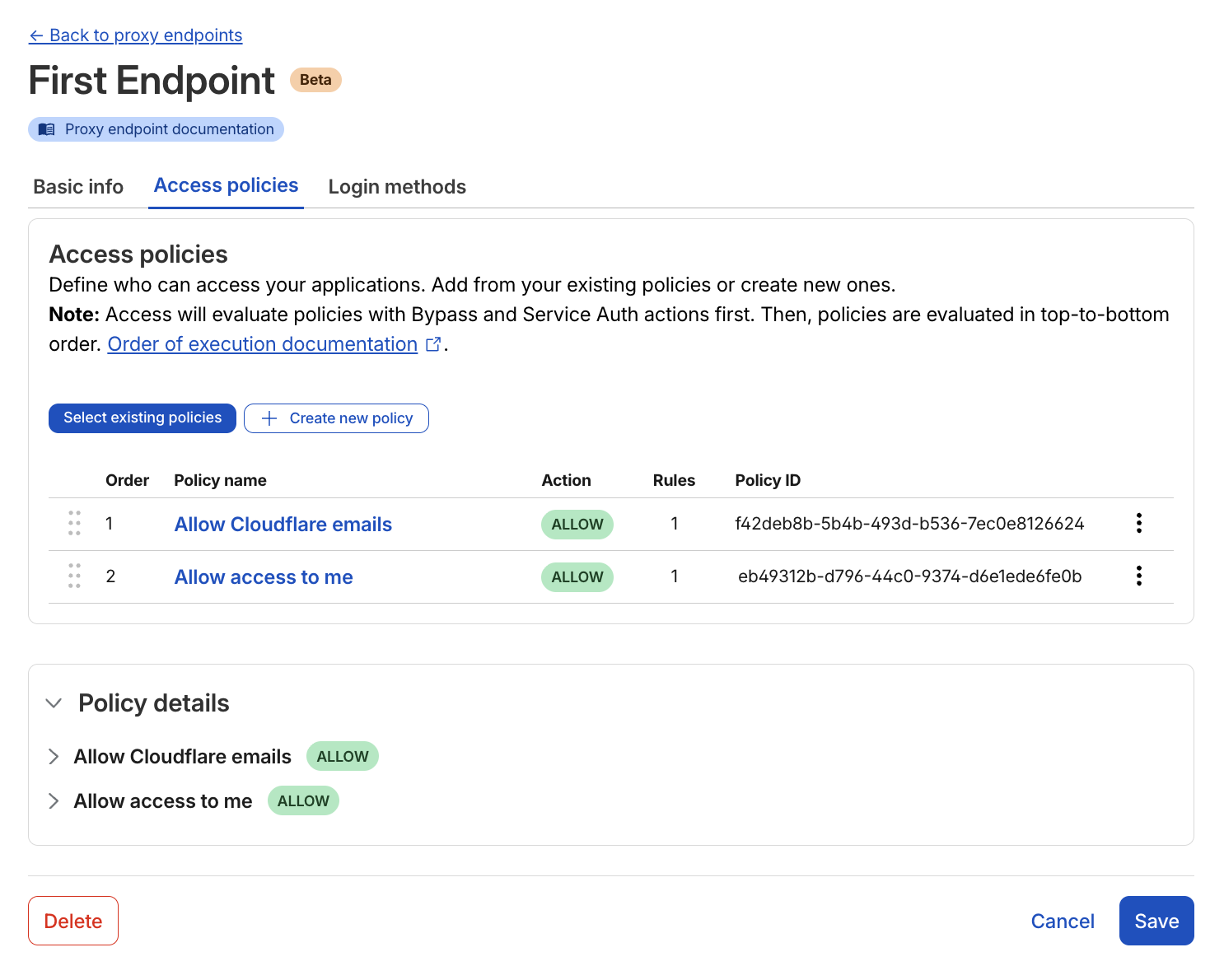
Authorization proxy Access policy setup page
The new Gateway Authorization Proxy adds a "badge reader" at the entrance. Instead of just looking at where the traffic is coming from, we now use a Cloudflare Access-style login to verify who the user is, before enforcing Gateway filtering.
Think of this as moving from a guest list based on license plates, to a system where everyone has their own badge. This brings several massive benefits:
True identity integration: Your logs related to proxy endpoints now show exactly which user is accessing which site. You can write specific rules like "only the Finance team can access this accounting tool," even without a client installed on the device.
Multiple identity providers: This is a superpower for large companies or those undergoing M&A. You can choose which identity providers to show your users. You can display one or multiple login methods (like Okta and Azure AD) at the same time. This is a level of flexibility that competitors don't currently offer.
Simplified billing: Each user simply occupies a "seat," exactly like they do with the Cloudflare One Client. There are no complicated new metrics to track.
To make this possible, we had to overcome the technical hurdle of associating a user’s identity with every request, and without a device client. Read on to see how it works.
How Authorization Proxy tracks identity
The Authorization Proxy uses signed JWT cookies to maintain identity, but there's a catch: when you first visit a new domain through the proxy, there's no cookie yet. Think of it like showing your badge at each new building you enter.
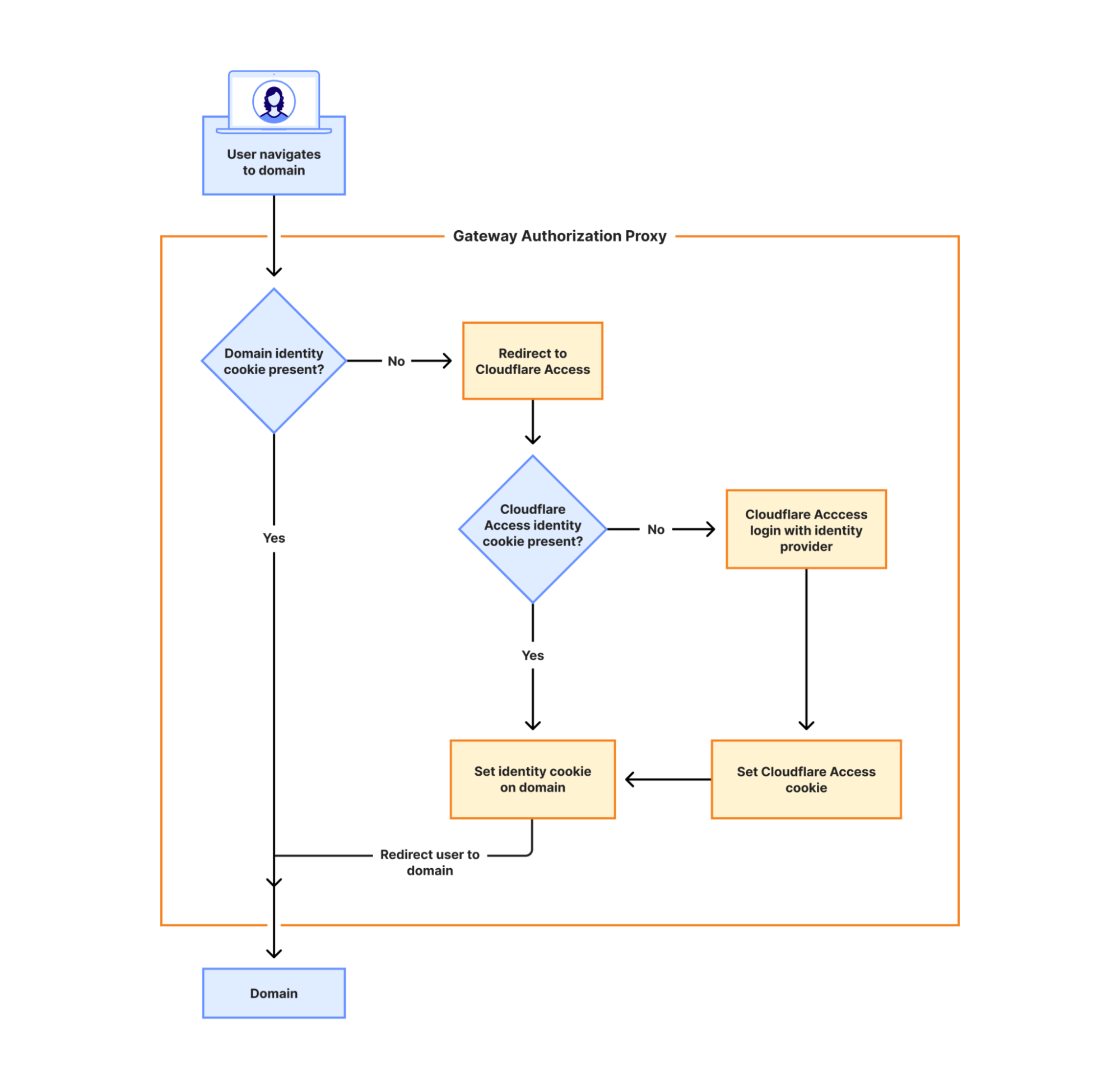
The flowchart above illustrates exactly how this authentication process works:
First visit to a domain: When you navigate to a new domain, the Gateway Authorization Proxy checks if a domain identity cookie is present. If not, you're redirected to Cloudflare Access, which then checks for an existing Cloudflare Access identity cookie. If you're already authenticated with Cloudflare Access, we generate a secure token specifically for that domain. If you're not, we redirect you to login with your identity provider(s).
Invisible to users: This entire process happens in milliseconds thanks to Cloudflare's global edge network. The redirect is so fast that users don't notice it — they simply see their page load normally.
Repeat visits are instant: Once the cookie is set, all subsequent requests to that domain (and its subdomains) are immediately authorized. No more redirects needed.
Because of this approach, we can log and filter traffic per person across all domains they access, and revoke access in an instant when needed — all without requiring any software installation on the user's device.
No more hosting your own PAC files
We are also taking the "homework" out of the setup process. You can now host your PAC files directly on Cloudflare, using Proxy Auto-Configuration (PAC) File Hosting.
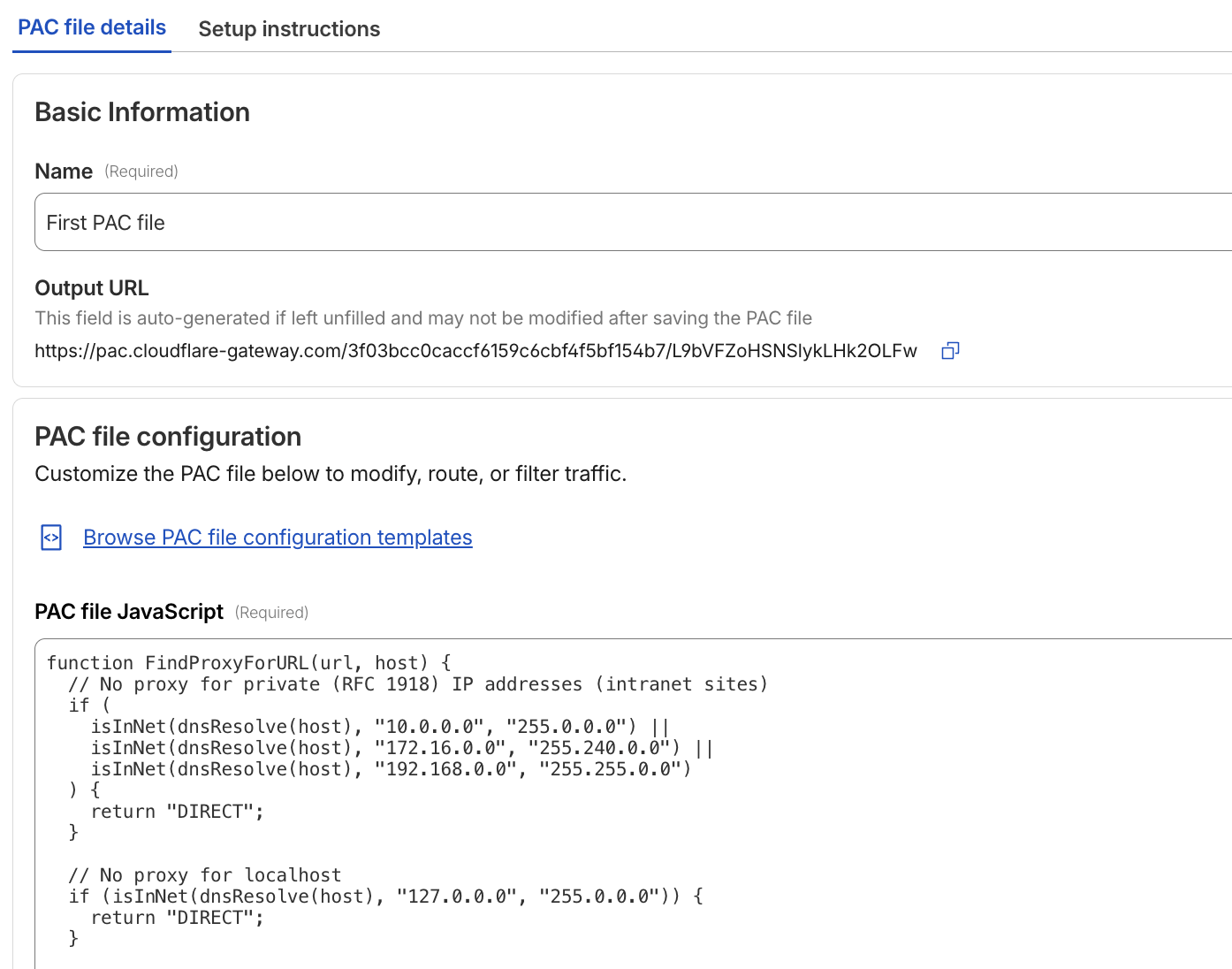
PAC file configuration page
To make it easy, we have included starter templates to get you up and running in minutes. We have also integrated our AI assistant, Cloudy, to provide summaries that help you understand exactly what your PAC file is doing, without having to read through lines of code.
Is this right for your team?
While we still recommend the Cloudflare One Client for greater control and the best user experience, the Auth Proxy is the perfect fit for specific scenarios:
Virtual desktops (VDI): Environments where users log into a virtual machine and use a browser to reach the Internet.
Mergers and acquisitions: When you need to bring two different companies under one security umbrella quickly.
Compliance constraints: When you are legally or technically prohibited from installing software on an endpoint.
What’s next?
This expands our clientless security options to connect to Cloudflare One, and we are already working on expanding our supported identity methods related to Authorization Endpoints. Look out for Kerberos, mTLS, and traditional username/password authentication to give you even more flexibility in how you authenticate your users.
The Gateway Authorization Proxy and PAC File Hosting are available in open beta today for all account types. You can get started by going to the "Resolvers and Proxies" section of your Cloudflare dashboard.
Cloudflare's connectivity cloud protects entire corporate networks, helps customers build Internet-scale applications efficiently, accelerates any website or Internet application, wards off DDoS attacks, keeps hackers at bay, and can help you on your journey to Zero Trust.
Visit 1.1.1.1 from any device to get started with our free app that makes your Internet faster and safer.
To learn more about our mission to help build a better Internet, start here. If you're looking for a new career direction, check out our open positions.
