2026-03-04
4 min read
One of our favorite ask-me-anything questions for company meetings or panels at security conferences is the classic: “What keeps you up at night?”
For a CISO, that question is maybe a bit of a nightmare in itself. It does not have one single answer; it has dozens. It’s the constant tension between enabling a globally distributed workforce to do their best work, and ensuring that "best work" does not inadvertently open the door to a catastrophic breach.
We often talk about the "zero trust journey," but the reality is that the journey is almost certainly paved with friction. If security is too cumbersome, users find creative (and dangerous) ways around it. If it’s seamless at the cost of effectiveness, it might not be secure enough to stop a determined adversary.
Today, we are excited to announce two new tools in Cloudflare’s SASE toolbox designed to modernize remote access by eliminating the "dark corners" of your network security without adding friction to the user experience: mandatory authentication and Cloudflare’s own multi-factor authentication (MFA).
Addressing the gap between installation and enforcement
When you deploy the Cloudflare One Client, you gain incredible visibility and control. You can apply policies for permitted destinations, define the Internet traffic that routes through Cloudflare, and set up traffic inspection at both the application and network layer. But there has always been a visibility challenge from when there is no user actually authenticated.
This gap occurs in two primary scenarios:
A new device: Cloudflare One Client is installed via mobile device management (MDM), but the user has not authenticated yet.
Re-authentication grey zone: The session expires, and the user, either out of forgetfulness or a desire to bypass restrictions, does not log back in.
In either case, the device is now unknown. This is dangerous. You lose visibility, and your security posture reverts to whatever the local machine allows.
Introducing mandatory authentication
To close this loop, we are introducing mandatory authentication. When enabled via your MDM configuration, the Cloudflare One Client becomes the gatekeeper of Internet access from the moment the machine boots up.
If a user is not actively authenticated, the Cloudflare One client will:
Block all Internet traffic by default using the system firewall.
Allow traffic from the device client’s authentication flow using a process-specific exception.
Prompt users to authenticate, guiding them through the process, so they don’t have to hunt for the right buttons.
By making authentication a prerequisite for connectivity, you ensure that every managed device is accounted for, all the time.
Note: mandatory authentication will become available in our Cloudflare One client on Windows initially, with support for other platforms to follow.
When one source of trust is not enough
Most organizations have moved toward single sign-on (SSO) as their primary security anchor. If you use Okta, Entra ID, or Google, you likely require MFA at the initial login. That’s a great start, but in a modern threat landscape, it is no longer the finish line.
The hard truth is that identity providers (IdPs) are high-value targets. If an attacker successfully compromises a user’s SSO session, perhaps through a sophisticated session hijacking or social engineering, they effectively hold the keys to every application behind that SSO.
Cloudflare’s independent MFA: a secondary root of trust
This is where Cloudflare’s MFA can help. Think of this as a "step-up MFA" that lives at the network edge, independent of your IdP.
By remaining separate from your IdP, this introduces another authority that has to “sign off” on any user trying to access a protected resource. That means even if your primary IdP credentials are compromised or spoofed, an attacker will hit a wall when trying to access something like your production database—because they do not have access to the second factor.
Cloudflare Access will offer a few different means of providing MFA:
Biometrics (i.e., Windows Hello, Apple Touch ID, and Apple Face ID)
Security key (WebAuthn and FIDO2 as well as PIV for SSH with Access for Infrastructure)
Time-based one-time password (TOTP) through authenticator apps
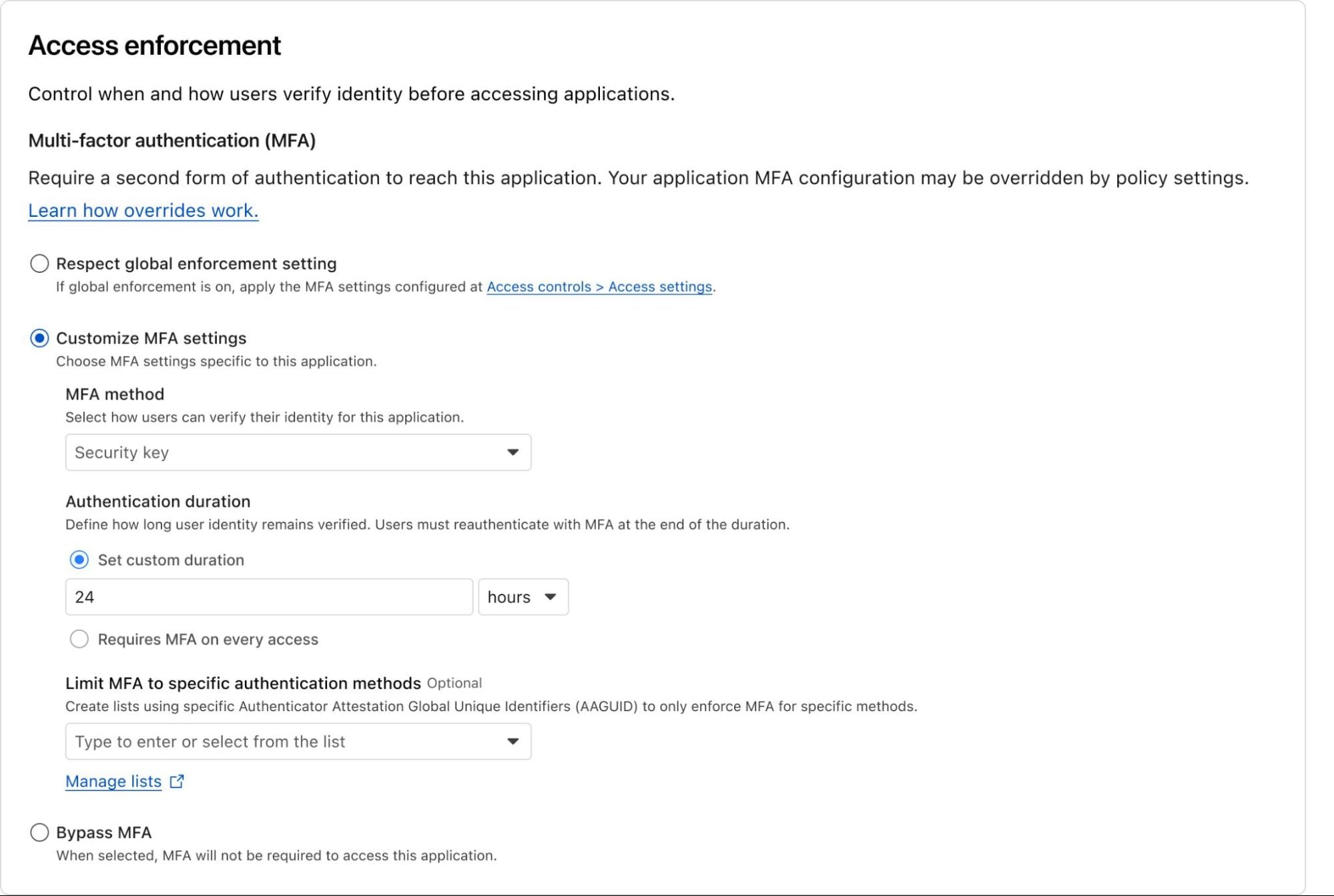
Administrators will have the flexibility to define how users must authenticate and how often. This can be configured not only at a global level (i.e., establish mandatory MFA for all Access applications), but also with more granular controls for specific applications or policies. For example, your organization may decide to allow lower assurance MFA methods for chat apps, but require a security key for access to source code.
Or, you could enforce strong MFA to sensitive resources for third-parties like contractors, who otherwise may use a personal email or social identity like LinkedIn. You can also easily add modern MFA methods to legacy apps that don’t otherwise support it natively, without touching a line of code.
End users will be able to enroll an MFA device easily through their App Launcher.
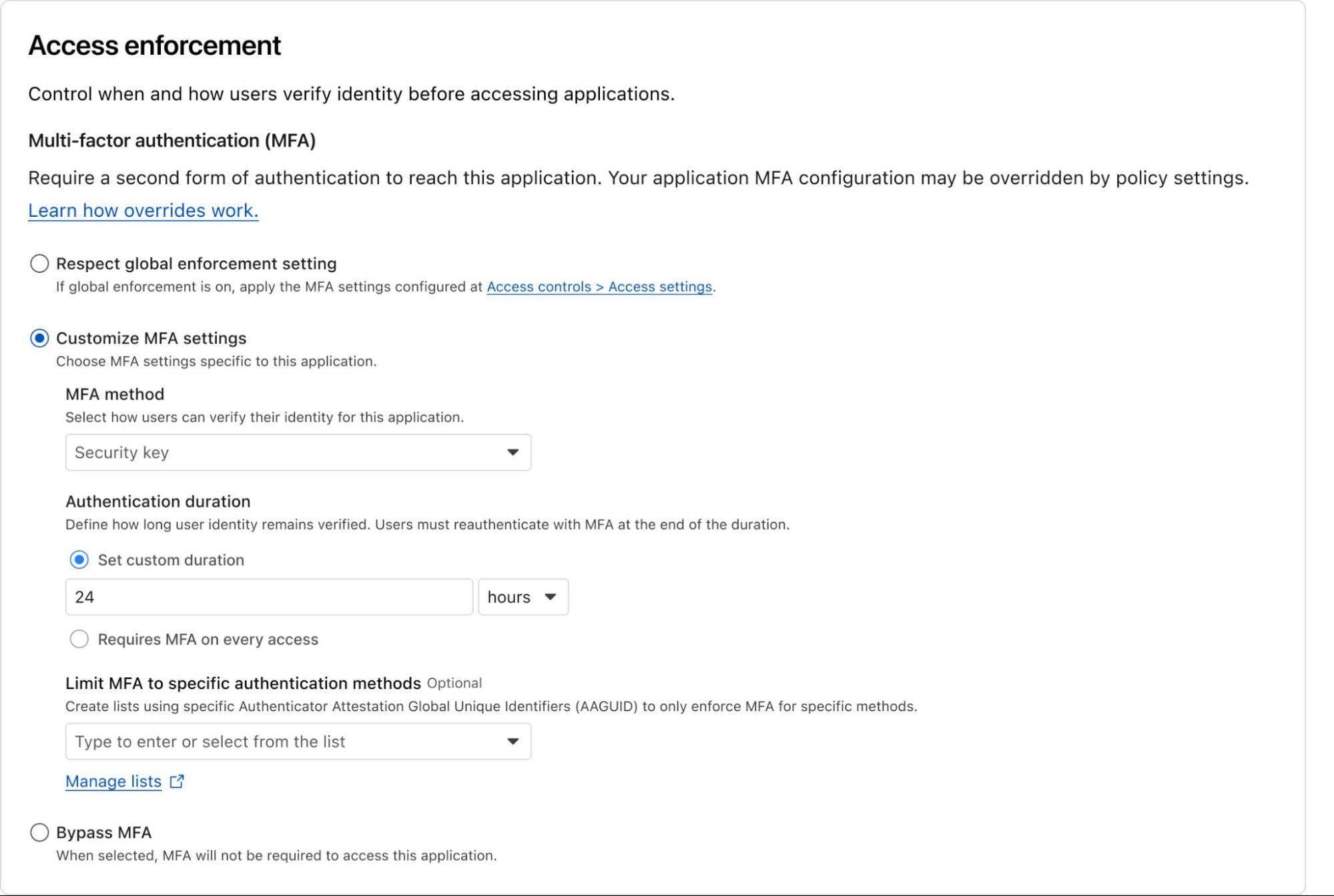
Example of what customizing MFA settings for an Access policy may look like. Note: This is a mockup and may change.
Cloudflare’s independent MFA is in closed beta with new customers being onboarded each week. You can request access here to try out this new feature!
Helping CISOs sleep at night
Security is often a game of "closing the loop." By ensuring that devices are registered and authenticated before they can touch the open Internet and by requiring an independent second layer of verification for your most precious assets, we are making the "blast radius" of a potential attack significantly smaller.
These features don't just add security; they add certainty. Certainty that your policies are being enforced and certainty that a single compromised password won't lead to a total breach.
We are moving beyond simple access control and into a world of continuous, automated posture enforcement. And we’re just getting started.
Ready to lock down your fleet? You can get started today with Cloudflare One for free for up to 50 users.
We’re excited to see how you use these tools to harden your perimeter and simplify your users’ day-to-day workflows. As always, we’d love to hear your feedback! Join us in the Cloudflare Community or reach out to your account team to share your thoughts.
Cloudflare's connectivity cloud protects entire corporate networks, helps customers build Internet-scale applications efficiently, accelerates any website or Internet application, wards off DDoS attacks, keeps hackers at bay, and can help you on your journey to Zero Trust.
Visit 1.1.1.1 from any device to get started with our free app that makes your Internet faster and safer.
To learn more about our mission to help build a better Internet, start here. If you're looking for a new career direction, check out our open positions.