
好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得通读整篇文章,抓住主要信息。 文章讲的是黑客利用OAuth的重定向机制绕过钓鱼保护,将用户引导到恶意页面。攻击目标是政府和公共部门,通过钓鱼链接让用户认证恶意应用。链接内容涉及电子签名、社保通知等常见主题,有时嵌入PDF以逃避检测。 微软的防御机制中提到,攻击者创建恶意OAuth应用,并配置重定向URI到自己的基础设施。即使URL看起来合法,也会触发静默认证错误,迫使用户重定向到攻击者的页面。有些情况下会用中间人框架劫持会话cookie,绕过多因素认证。此外,还利用ZIP文件传播恶意软件。 微软建议组织加强OAuth权限、实施身份保护和条件访问策略,并进行跨域检测。 总结时要涵盖攻击手段、目标、技术细节和防御建议。控制在100字以内,直接描述内容。 </think> 黑客利用OAuth重定向机制绕过电子邮件和浏览器的钓鱼保护,将用户引导至恶意页面。攻击针对政府和公共部门组织,通过伪装成合法请求(如电子签名、社保通知等)诱导用户授权恶意应用。攻击者滥用OAuth框架中的授权错误处理机制,触发静默认证错误并重定向用户至钓鱼页面或恶意软件下载链接。微软建议加强OAuth应用权限管理、实施身份保护和条件访问策略以应对此类威胁。 2026-3-3 21:0:27 Author: www.bleepingcomputer.com(查看原文) 阅读量:6 收藏

Hackers are abusing the legitimate OAuth redirection mechanism to bypass phishing protections in email and browsers to take users to malicious pages.
The attacks target government and public-sector organizations with phishing links that prompt users to authenticate to a malicious application, Microsoft Defender researchers say.
with e-signature requests, Social Security notices, meeting invitations, password resets, or various financial and political topics that contain OAuth redirect URLs. Sometimes, the URLs are embedded in PDF files to evade detection.
Source: Microsoft
Forcing risky redirections
OAuth applications are registered with an identity provider, such as Microsoft Entra ID, and leverage the OAuth 2.0 protocol to obtain delegated or application-level access to user data and resources.
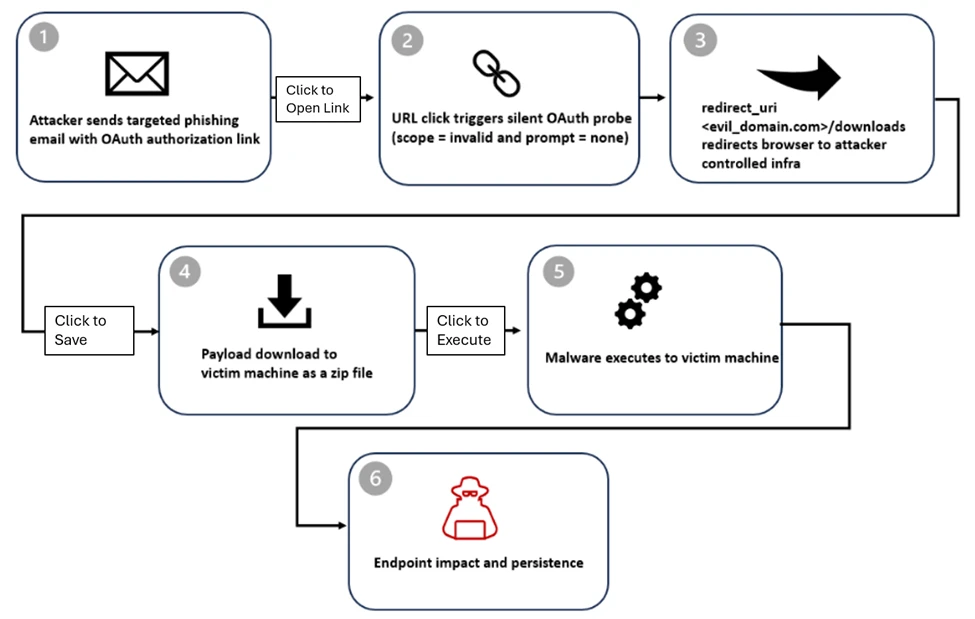
In the campaigns observed by Microsoft, the attackers create malicious OAuth applications in a tenant they control and configure them with a redirect URI pointing to their infrastructure.
The researchers say that even if the URLs for Entra ID look like legitimate authorization requests, the endpoint is invoked with parameters for silent authentication without an interactive login and an invalid scope that triggers authentication errors. This forces the identity provider to redirect users to the redirect URI configured by the attacker.
In some cases, the victims are redirected to phishing pages powered by attacker-in-the-middle frameworks such as EvilProxy, which can intercept valid session cookies to bypass multi-factor authentication (MFA) protections.
Microsoft found that the ‘state’ parameter was misused to auto-fill the victim’s email address in the credentials box on the phishing page, increasing the perceived sense of legitimacy.
Source: Microsoft
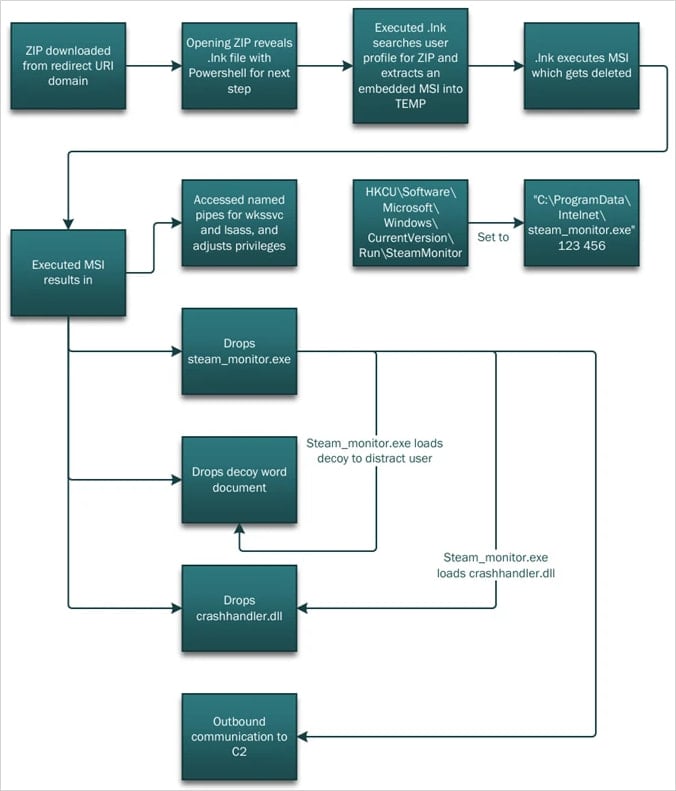
In other instances, the victims are redirected to a ‘/download’ path that automatically delivers a ZIP file with malicious shortcut (.LNK) files and HTML smuggling tools.
Opening the .LNK launches PowerShell, which performs reconnaissance on the compromised host and extracts the components required for the next step, DLL side-loading.
A malicious DLL (crashhandler.dll) decrypts and loads the final payload (crashlog.dat) into memory, while a legitimate executable (stream_monitor.exe) loads a decoy to distract the victim.
Source: Microsoft
Microsoft suggests that organizations should tighten permissions for OAuth applications, enforce strong identity protections and Conditional Access policies, and use cross-domain detection across email, identity, and endpoints.
The company highlights that the observed attacks are identity-based threats that abuse an intended behavior in the OAuth framework that behaves as specified by the standard defining how authorization errors are managed through redirects.
The researchers warn that threat actors are now triggering OAuth errors through invalid parameters, such as scope or prompt=none, to force silent error redirects as part of real-world attacks.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
