嗯,用户让我用中文帮他总结一篇文章,控制在一百个字以内,而且不需要特定的开头。首先,我得通读整篇文章,理解主要内容。 文章主要讲的是网络犯罪分子在地下经济中公开兜售被黑网站的访问权限,特别是cPanel的凭证。cPanel是一个广泛使用的网页托管控制面板,拥有大量用户。犯罪分子通过各种手段获取这些凭证,然后在地下论坛和聊天群组中以低价出售,用于钓鱼和诈骗活动。 文章还提到Flare安全研究人员分析了七天内的活动数据,显示这是一个结构化的生态系统,并且cPanel凭证的需求很高。此外,文章讨论了犯罪分子如何利用这些凭证进行大规模攻击,以及企业如何防范这些威胁。 总结时需要涵盖关键点:cPanel凭证被大量出售、用于钓鱼诈骗、地下市场的结构化运作、以及对企业的威胁。同时要控制在100字以内,语言简洁明了。 现在把这些点整合成一段话:网络犯罪分子在地下经济中大量出售被黑网站的访问权限,尤其是cPanel凭证。这些凭证被用于钓鱼和诈骗活动,并形成一个结构化的生态系统。研究显示cPanel凭证需求旺盛,犯罪分子利用多种手段获取并滥用这些凭证对企业构成严重威胁。 </think> 网络犯罪分子在地下经济中大量出售被黑网站的访问权限,尤其是cPanel凭证。这些凭证被用于钓鱼和诈骗活动,并形成一个结构化的生态系统。研究显示cPanel凭证需求旺盛,犯罪分子利用多种手段获取并滥用这些凭证对企业构成严重威胁。 2026-3-3 15:15:18 Author: www.bleepingcomputer.com(查看原文) 阅读量:5 收藏

Threat actors are openly advertising access to hacked websites as part of the underground economy. One of the most promising products is a compromised cPanel credential. They are sold in the thousands across fraudulent chat groups at commodity-level pricing and marketed as plug-and-play infrastructure for phishing and scam campaigns.
In new research, Flare security researchers analyzed activity across monitored fraudulent groups over a seven-day period, showing a structured ecosystem operating at scale.
We analyzed more than 200,000 posts referencing cPanel access, and we explained how cPanel has become a hot commodity, why it is desired by threat actors, and how it fits in the entire threat landscape.
cPanel - One Key to Control the Website
cPanel is one of the most widely used Linux-based web hosting control panels in the world. It provides a structured management layer on top of standard system services. It acts as an orchestration and automation interface for managing hosting accounts, domains, mail services, databases, DNS zones, SSL certificates, and file systems.
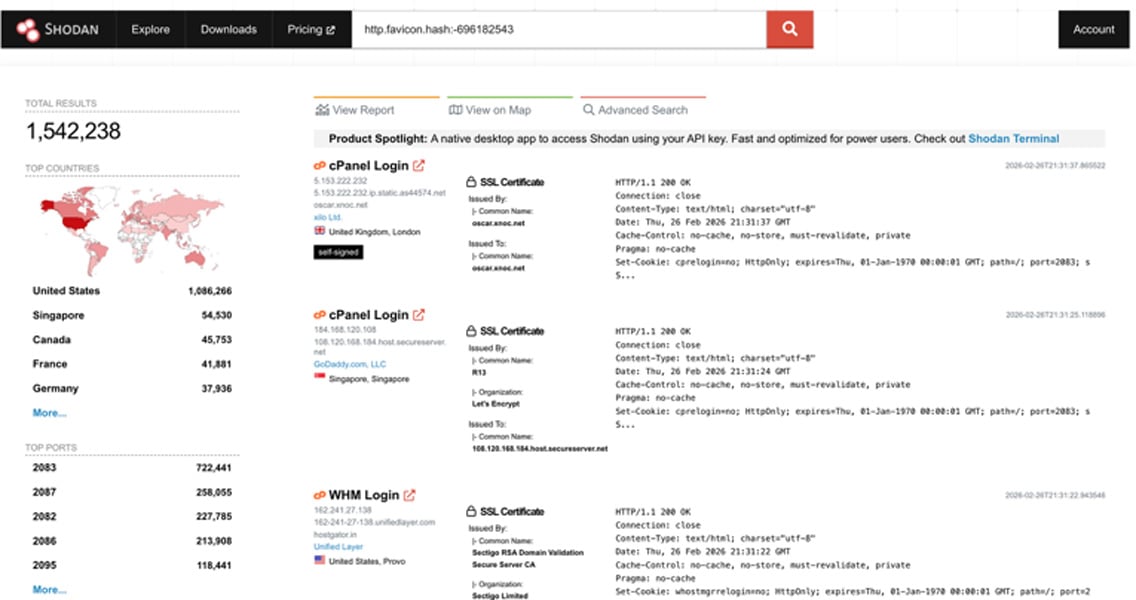
According to Shodan, there are over 1.5 million internet-connected servers with cPanel software.
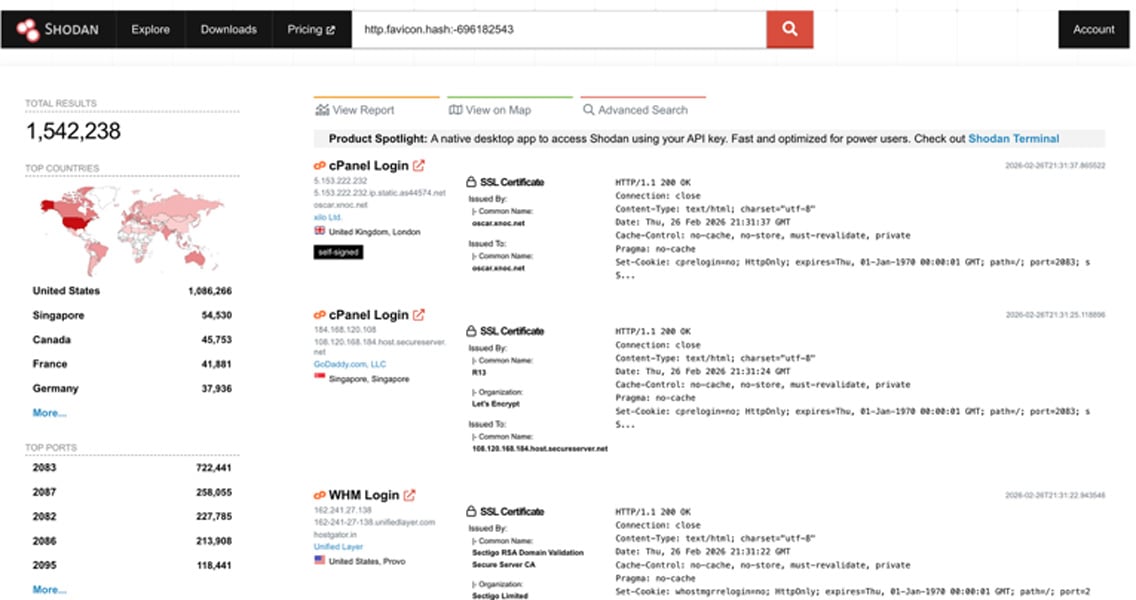
The heatmap below illustrates how cPanel is popular mainly in the U.S. (over 1 million results).

Compromised cPanels Enable Wide-Scale Attacks
Imagine you own a website, either for personal use, running a small business, or one of many in your enterprise’s web-facing assets. Once a threat actor obtains the legitimate credentials to access the management layer, it enables a wide range of capabilities:
-
Deploying backdoors for persistence
-
Creating new admin users for persistence
-
Deploying malware
-
Gaining root access on the server
-
Deploying phishing kits as a subdomain under the legitimate domain name
-
Creating SMTP accounts under the domain to disseminate phishing or spam campaigns
-
Stealing and exfiltrating invaluable data (PII, secrets) from databases
In shared hosting environments, a single cPanel can enable access to dozens of domains, and in an organizational level, it can compromise the entire web presence.
Because attackers use valid credentials, traditional security controls may not immediately flag the activity or totally miss it. Abuse may begin with quiet outbound mail or hidden file uploads before visible exploitation can be detected.
Detect Compromised Credentials in Real Time
Flare monitors underground Telegram channels where threat actors sell compromised cPanel credentials, SMTP access, and hosting infrastructure.
Get alerts when your domains, hosting accounts, or credentials appear in bulk sales before they're exploited.
cPanels are Compromised in Many Ways
Historically, threat actors have gained access to cPanel environments through a mix of credential abuse, web application compromise, and server-level exploitation.
The most common vector has been stolen or brute-forced credentials. Attackers leverage phishing campaigns, password reuse from data breaches, credential stuffing, and automated brute-force attacks against exposed cPanel login portals.
Configuration mistakes such as exposing sensitive files (config.yaml, .env) to the internet, weak passwords, or the absence of multi-factor authentication have traditionally made this an attractive entry point.
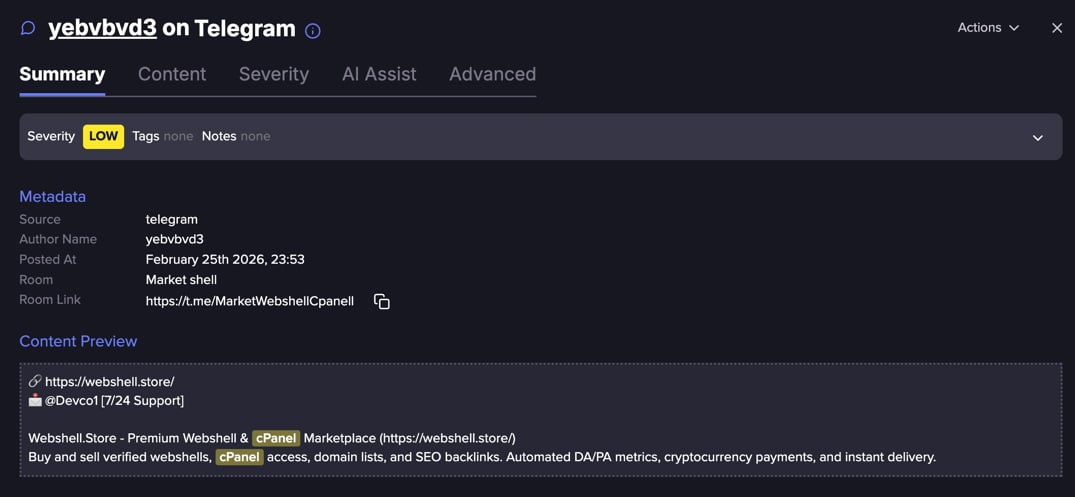
Another frequent path has been exploiting vulnerable websites hosted on the same server. Outdated CMS platforms like WordPress, Joomla, or Drupal, along with vulnerable plugins and themes, allow attackers to upload web shells or escalate privileges.
Once inside the hosting account, they may pivot laterally, harvest stored credentials, access configuration files (such as wp-config.php), or attempt privilege escalation to gain broader cPanel access.
Over time, automation has amplified these techniques, with botnets continuously scanning for exposed login panels, known CVEs, and misconfigurations to monetize access through spam, phishing infrastructure, defacement, or resale in underground markets.
Compromised cPanels are a Popular Commodity in Underground Markets
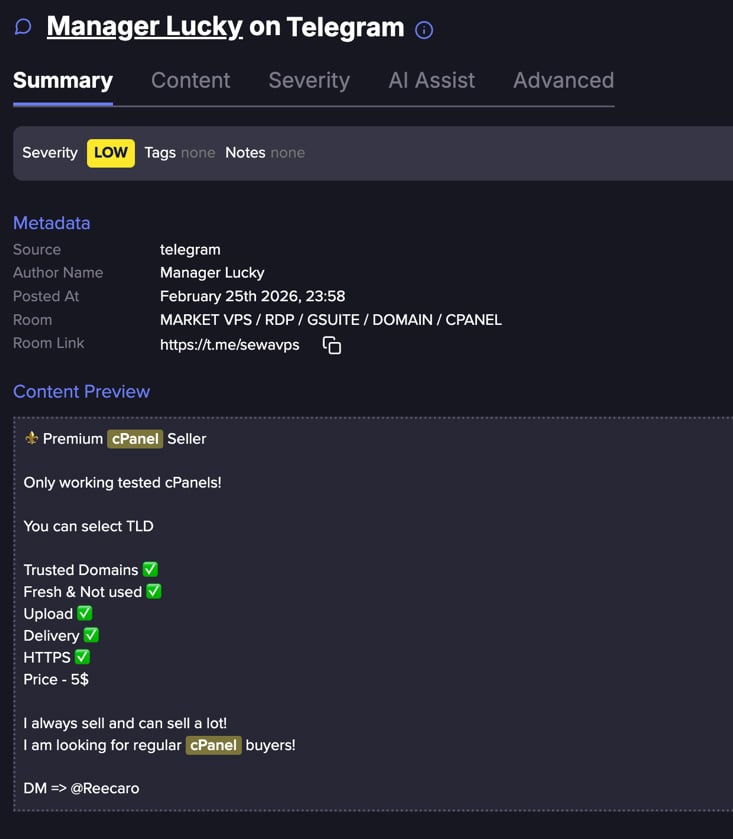
Flare researchers collected a seven day sample with over 200,000 posts. We found that 90% of the posts were duplicates.
This may indicate a highly commoditized market with hundreds of unique posts that were amplified thousands of times via various channels.
Pricing tiers differentiate quality, geography, and infrastructure reputation. Bulk discounts incentivize scale.
Flare link to post, sign up for the free trial to access if you aren’t already a customer
Commodification
Our analysis is based on thousands of distinct posts which contain explicit price references. cPanels are typically sold in bulk because, in many cases, the initial access has already been detected, credentials may have been revoked, or the access is otherwise restricted.
Buyers understand they are assuming risk, which is reflected in the pricing and volume-based sales model.
The fact that we found over 90% duplication indicates that sellers repeatedly advertise the same inventory across multiple fraudulent chat groups, likely using templated ads and automated reposting tools.
Listings frequently include marketing language such as “fresh,” “high quality,” “spam clean,” or “ready for mailing,” mirroring commercial sales tactics.
The cPanels offerings behave exactly like regular markets:
|
Quality |
Quantity |
Price |
|
Premium |
100 |
$75 |
|
Premium |
500 |
$289 |
|
Premium |
1,000 |
$645 |
|
Regular |
1,000 |
$23 |
|
Regular |
3,000 |
$42 |
|
Regular |
5,000 |
$58 |
The quality differentiation is straightforward:
-
High-trust top-level domains such as .gov or .mil carry significantly greater perceived legitimacy. As a result, phishing or scam campaigns leveraging these domains have a higher probability of success.
-
In contrast, domains like .xyz or .net are generally viewed as lower-value assets in underground markets, as they offer less inherent trust and therefore lower expected conversion rates.
-
Some posts defined premium quality panels as good SEO metrics, and reputable server providers.
-
Active SMTP server increases the price of the product. It enables the buyer to send outbound emails from a legitimate domain without immediate restrictions or blacklisting. This increases the value of the compromised cPanel as the threat actor can send phishing or spam emails directly from a trusted infrastructure, significantly improving deliverability and bypass rates.
-
Compromised cPanels of U.S. or EU-based hosting companies or domains are more expensive, particularly when the cPanel is published for phishing purposes.
Flare link to post, sign up for the free trial to access if you aren’t already a customer
Detection and Mitigation
Organizations should enable multi-factor authentication (MFA) on all hosting control panel accounts, enforce strong and unique passwords, and restrict administrative access by IP address wherever possible.
Outbound SMTP activity should be continuously monitored to detect spam abuse, while file integrity monitoring can help identify unauthorized modifications.
Tracking newly created hosting accounts, unexpected cron jobs, or configuration changes can provide early indicators of compromise.
It is equally important to monitor for credential exposure in stealer logs and underground marketplaces, as hosting credentials are frequently traded after initial infections.
CMS platforms and their plugins must be fully patched, unused services disabled, and the principle of least privilege applied across hosting environments.
Damage from Compromised cPanel Account: Account Compromise to Business Crisis
For organizations, the impact of a compromised cPanel account can be immediate and severe. Threat actors’ actions can lead to domain and IP blacklisting, leading to reputational damage and operational disruption. In more serious cases, website content may be stolen, defaced, or even encrypted and held for ransom, turning what began as a simple account compromise into a full-scale business continuity incident.
When stolen hosting credentials are increasingly treated as inventory - packaged, graded, and sold at scale across underground markets - the cybercrime economy shifts from exploit development to access brokerage, protecting hosting credentials becomes a frontline defense against being repurposed as infrastructure for phishing, spam, and fraud operations.
In this access-driven ecosystem, hosting credentials represent a high-value gateway into corporate environments. If current trends continue, automated harvesting and bulk redistribution of these credentials will further industrialize the model, lowering the barrier to entry for phishing operators seeking trusted domains and IP space.
The result is a growing supply chain of abuse - where compromised hosting accounts are no longer incidental, but strategic assets in cybercriminal operations.
Learn more by signing up for our free trial.
Sponsored and written by Flare.
如有侵权请联系:admin#unsafe.sh