Microsoft on Monday warned of phishing campaigns that employ phishing emails and OAuth URL redirection mechanisms to bypass conventional phishing defenses implemented in email and browsers.
The activity, the company said, targets government and public-sector organizations with the end goal of redirecting victims to attacker-controlled infrastructure without stealing their tokens. It described the phishing attacks as an identity-based threat that takes advantage of OAuth's standard, by-design behavior rather than exploiting software vulnerabilities or stealing credentials.
"OAuth includes a legitimate feature that allows identity providers to redirect users to a specific landing page under certain conditions, typically in error scenarios or other defined flows," the Microsoft Defender Security Research Team said.
"Attackers can abuse this native functionality by crafting URLs with popular identity providers, such as Entra ID or Google Workspace, that use manipulated parameters or associated malicious applications to redirect users to attacker-controlled landing pages. This technique enables the creation of URLs that appear benign but ultimately lead to malicious destinations."
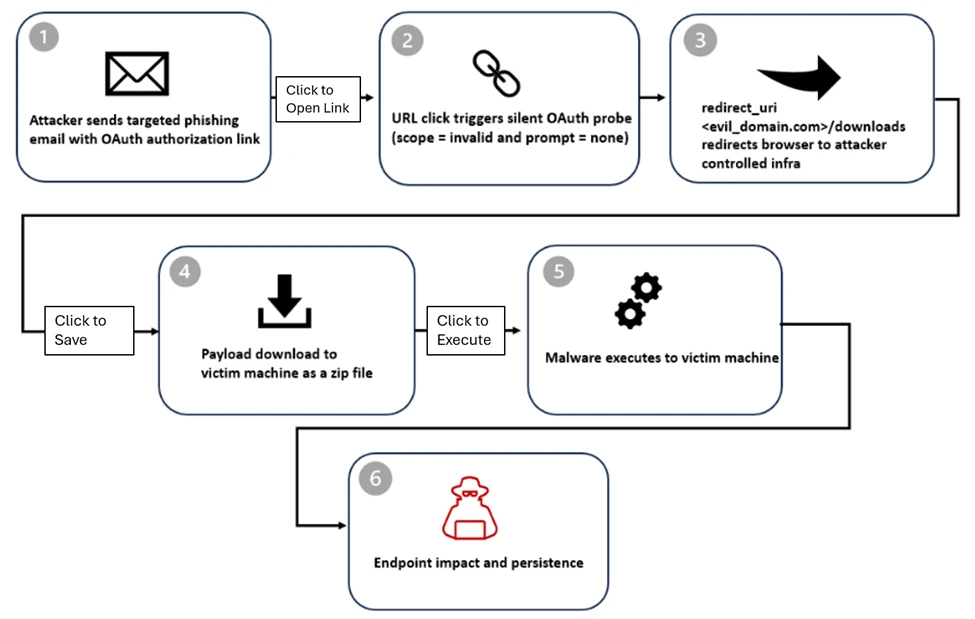
The starting point of the attack is a malicious application created by the threat actor in a tenant under their control. The application is configured with a redirect URL pointing to a rogue domain that hosts malware. The attackers then distribute an OAuth phishing link that instructs the recipients to authenticate to the malicious application by using an intentionally invalid scope.
The result of this redirection is that users inadvertently download and infect their own devices with malware. The malicious payloads are distributed in the form of ZIP archives, which, when unpacked, result in PowerShell execution, DLL side-loading, and pre-ransom or hands-on-keyboard activity, Microsoft said.
The ZIP file contains a Windows shortcut (LNK) that executes a PowerShell command as soon as it's opened. The PowerShell payload is used to conduct host reconnaissance by running discovery commands. The LNK file extracts from the ZIP archive an MSI installer, which then drops a decoy document to mislead the victim, while a malicious DLL ("crashhandler.dll") is sideloaded using the legitimate "steam_monitor.exe" binary.
The DLL proceeds to decrypt another file named "crashlog.dat" and executes the final payload in memory, allowing it to establish an outbound connection to an external command-and-control (C2) server.
Microsoft said the emails use e-signature requests, Teams recordings, social security, financial, and political themes as lures to trick users into clicking the link. The emails are said to have been sent via mass-sending tools and custom solutions developed in Python and Node.js. The links are either directly included in the email body or placed within a PDF document.
"To increase credibility, actors passed the target email address through the state parameter using various encoding techniques, allowing it to be automatically populated on the phishing page," Microsoft said. "The state parameter is intended to be randomly generated and used to correlate request and response values, but in these cases it was repurposed to carry encoded email addresses."
While some of the campaigns have been found to leverage the technique to deliver malware, others send users to pages hosted on phishing frameworks such as EvilProxy, which act as an adversary-in-the-middle (AitM) kit to intercept credentials and session cookies.
Microsoft has since removed several malicious OAuth applications that were identified as part of the investigation. Organizations are advised to limit user consent, periodically review application permissions, and remove unused or overprivileged apps.
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.