嗯,用户让我总结这篇文章,控制在100字以内,而且不需要用“文章内容总结”之类的开头。我得先通读一下文章,抓住主要信息。 文章讲的是CVE-2025-64328漏洞被利用,影响了大约900个Sangoma FreePBX实例。攻击者通过这个漏洞植入了网络壳。FreePBX是一个管理VoIP系统的开源平台,漏洞存在于Endpoint Manager模块中,CVSS评分8.6分。 攻击者利用这个漏洞执行恶意命令,保持对系统的持久访问。报告指出有400个受影响的系统在美国,其他国家也有分布。威胁组织INJ3CTOR3被怀疑参与其中,他们之前也攻击过类似的系统。 另外,FortiGuard Labs发现了名为EncystPHP的新网络壳,用于远程命令执行和维持访问。CISA在2月将此漏洞加入已知被利用的漏洞目录。 总结的时候要涵盖这些要点:漏洞名称、受影响实例数量、攻击方式、漏洞位置、影响范围、威胁组织以及后续措施。确保不超过100字。 </think> Sangoma FreePBX平台因CVE-2025-64328漏洞遭攻击,约900个实例感染网络壳。该漏洞允许攻击者执行恶意命令并维持访问。受影响系统分布全球,美国占多数。FortiGuard发现新网络壳EncystPHP用于远程控制和持久化访问。CISA已将该漏洞列入已知被利用目录。 2026-3-1 10:1:54 Author: securityaffairs.com(查看原文) 阅读量:23 收藏
CVE-2025-64328 exploitation impacts 900 Sangoma FreePBX instances

About 900 Sangoma FreePBX systems were infected with web shells after attackers exploited a command injection flaw.
Hundreds of Sangoma FreePBX instances are still infected with web shells following attacks that began in December 2025.
Sangoma FreePBX is an open-source, web-based platform for managing Asterisk-powered VoIP phone systems. Maintained by Sangoma Technologies, it allows businesses to configure extensions, call routing, voicemail, IVR menus, and SIP trunks through an easy-to-use interface.
The campaign exploited a post-authentication command injection vulnerability, tracked as CVE-2025-64328 (CVSS score of 8.6), in the endpoint manager interface, allowing attackers to execute malicious commands and maintain persistent access to compromised systems.
“FreePBX Endpoint Manager is a module for managing telephony endpoints in FreePBX systems. In versions 17.0.2.36 and above before 17.0.3, the filestore module within the Administrative interface is vulnerable to a post-authentication command injection by an authenticated known user via the testconnection -> check_ssh_connect() function.” reads the advisory. “An attacker can leverage this vulnerability to obtain remote access to the system as an asterisk user. This issue is fixed in version 17.0.3.”
The Shadowserver Foundation reports that around 900 FreePBX instances are still compromised and running web shells, likely due to exploitation of CVE-2025-64328 in the endpoint manager. About 400 affected systems are located in the United States, with dozens more in countries including Brazil, Canada, Germany, France, the UK, Italy, and the Netherlands, and smaller numbers spread across other regions.
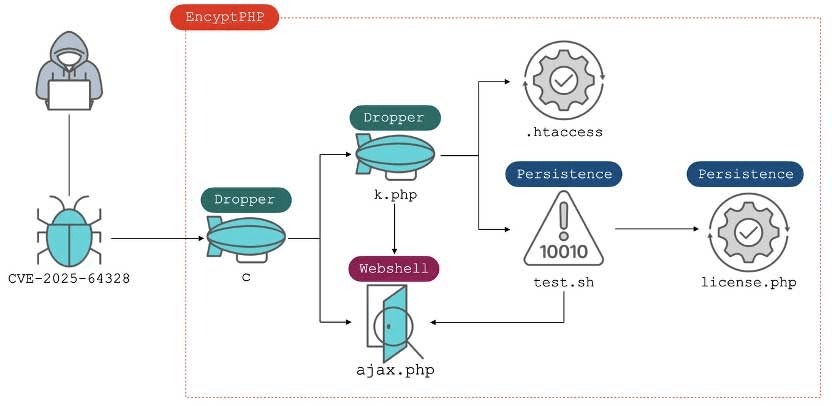
In January, FortiGuard Labs identified a new web shell dubbed “EncystPHP,” capable of remote command execution, persistence, and further web shell deployment. The attacks began in early December and exploited the flaw CVE-2025-64328. Researchers link the activity to the threat group INJ3CTOR3, known for targeting past vulnerabilities in FreePBX and Elastix systems. The campaign follows a familiar pattern: exploiting a flaw and installing a PHP web shell to maintain access.
“The web shell was delivered via CVE-2025-64328, a post-authentication command-injection vulnerability in the administrative interface of the FreePBX Endpoint Manager.” reads the analysis published by Fortinet. “The attackers downloaded the EncystPHP dropper from the IP address 45[.]234[.]176[.]202, which resolves to the domain crm[.]razatelefonia[.]pro. “
Attackers delivered the EncystPHP dropper from 45.234.176.202, exploiting CVE-2025-64328 in FreePBX. Once installed, the malware locked key files, harvested database configs, deleted cron jobs and user accounts, and removed rival web shells. It created a root-level user, reset passwords, injected an SSH key, and ensured port 22 stayed open for persistent access.
The dropper also fetched additional payloads, erased logs, removed the Endpoint Manager module, restored permissions to avoid detection, and deployed Base64-encoded web shells to maintain long-term control.
In early February, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the flaw in Sangoma FreePBX to its Known Exploited Vulnerabilities (KEV) catalog.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, CVE-2025-64328 )
如有侵权请联系:admin#unsafe.sh
