嗯,用户让我帮忙总结一下这篇文章的内容,控制在100字以内,而且不需要用“文章内容总结”或者“这篇文章”这样的开头。首先,我需要仔细阅读这篇文章,理解它的主要信息。 文章标题是“12 million exposed .env files reveal widespread security failures”,看起来是关于1200万个暴露的.env文件揭示了普遍的安全问题。作者是Pierluigi Paganini,日期是2026年2月27日。Mysterium VPN发现了1200万个IP地址暴露了.env文件,导致凭证泄露和全球范围内的安全配置错误。 接下来,文章详细说明了.env文件的作用,它们存储了数据库URL、OAuth密钥、SMTP凭证等敏感信息。如果服务器允许访问隐藏文件,攻击者可以轻松下载这些凭证,而无需利用漏洞。这会导致数据泄露、API滥用、云存储访问等问题。 研究发现,美国暴露的IP最多,其次是日本、德国等国家。问题出在配置错误上,比如缺少拒绝规则、反向代理转发敏感路径等。文章还建议组织采取措施防止这种情况发生,比如阻止隐藏文件访问、使用集中式密钥管理系统等。 用户的需求是用中文总结内容,并且控制在100字以内。所以我要提取关键点:Mysterium VPN发现1200万个IP暴露.env文件,导致凭证泄露;问题涉及全球多个国家;原因是配置错误;后果严重;建议采取措施。 现在要组织语言,确保简洁明了,并且不使用特定的开头词。可能的结构是:Mysterium VPN发现...揭示...配置错误...影响...建议... 最后检查字数是否在限制内,并确保信息准确传达。 </think> Mysterium VPN发现1200万个IP地址暴露.env文件,导致数据库密码、API密钥等敏感信息泄露,揭示全球范围内配置错误和安全卫生问题。 2026-2-27 08:2:51 Author: securityaffairs.com(查看原文) 阅读量:5 收藏
12 Million exposed .env files reveal widespread security failures
Pierluigi Paganini
February 27, 2026

Mysterium VPN found 12M IPs exposing .env files, leaking credentials and revealing widespread security misconfigurations worldwide.
Configuration mistakes rarely trigger alarms. A forgotten deny rule, an overlooked server setting, or a full project folder uploaded to production can quietly expose a company’s most sensitive secrets. In many cases, those secrets live inside simple environment files known as .env files.
Researchers at Mysterium VPN identified 12,088,677 IP addresses serving publicly accessible .env-style files.
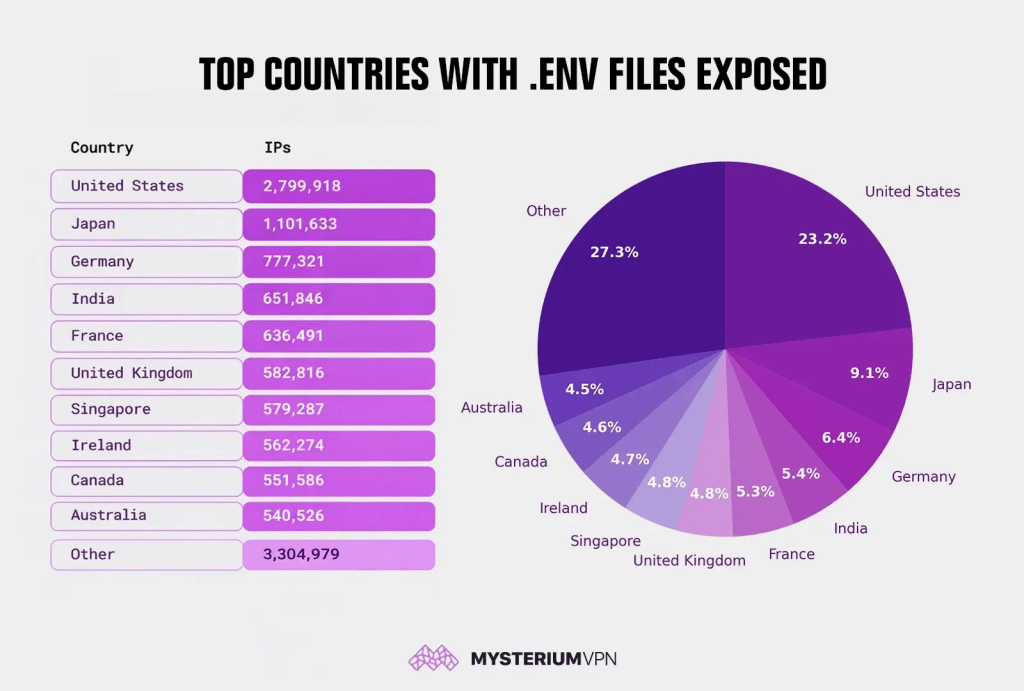
“Researchers here at Mysterium VPN identified over 12 million IP addresses with publicly accessible .env-style files, revealing credentials and tokens, including JWT signing keys, API keys, database passwords, and service tokens.” reads the report published by Mysterium VPN. “The United States leads the count with nearly 2.8 million exposed IPs, accounting for around 23% of the total IP pool. The issue is global: Japan (1.1M), Germany (777K), India (652K), France (636K), and the UK (583K) also have substantial exposures, showing that this is a global security hygiene problem.”
These files exposed database credentials, API keys, JWT signing secrets, cloud tokens, and other sensitive values. The scale reveals a widespread operational hygiene problem affecting organizations across industries and regions.
A .env file stores key-value pairs that applications load at startup. Developers use them for database URLs, OAuth secrets, SMTP credentials, cloud access keys, and third-party tokens. The format stays simple and convenient. That same simplicity creates risk. If a server allows access to hidden files, anyone can request “/.env” and download live credentials without exploiting a vulnerability.
Attackers who retrieve these secrets skip the break-in phase entirely. They log in with valid credentials, query databases, forge authentication tokens, abuse APIs, or access cloud storage. OWASP guidance stresses strict secret control, rotation, auditing, and least-privilege scoping because exposed secrets often lead directly to compromise.
The exposure spans the globe. The United States accounts for nearly 2.8 million affected IPs, followed by Japan, Germany, India, France, the UK, Singapore, Ireland, Canada, and Australia. Large cloud and hosting footprints explain part of the distribution, but the pattern points to repeated deployment and configuration mistakes across ecosystems—not a single flawed platform.

The consequences can escalate quickly. Database credentials enable data theft and privilege escalation. API keys invite financial abuse and spam campaigns. Leaked JWT secrets allow attackers to forge tokens and hijack accounts. SMTP credentials open the door to phishing from legitimate domains. Cloud storage keys can expose backups, identity documents, and internal files.
These exposures usually stem from preventable errors: missing deny rules for hidden files, reverse proxies forwarding sensitive paths, static roots pointing to entire project directories, container images embedding secrets, or forgotten backup files such as .env.bak or .env.old. Attackers routinely scan for these predictable patterns.
When teams discover an exposed .env file, they must treat the event as a full security incident. Remove public access immediately, purge caches, and rotate every secret in the file. Invalidate tokens, review logs for suspicious access, and implement automated secret scanning in repositories and CI pipelines.
Long term, organizations need layered defenses. Block hidden and backup files at the server and CDN level. Move secrets out of web-accessible directories and into centralized secret management systems with audit logs and automated rotation. Scope keys to minimal permissions, enforce network restrictions, and adopt short-lived tokens. Deploy only approved artifacts and validate that no sensitive files remain publicly reachable.
The Mysterium VPN findings highlight a systemic issue: secret exposure continues at massive scale because teams treat configuration as an afterthought. Security teams must embed secret governance into development workflows, deployment pipelines, and infrastructure baselines. Without that shift, a single overlooked file will keep turning routine deployments into full-scale breaches.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, .env files)
如有侵权请联系:admin#unsafe.sh