
好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内。用户已经提供了文章的英文内容和要求,我得先仔细阅读并理解文章的主要信息。 首先,文章讲的是Google的API密钥被嵌入到客户端代码中,比如Maps服务。研究人员发现有近3000个这样的密钥暴露在互联网上,甚至包括Google自己的组织。问题出现在Google推出Gemini AI助手后,这些API密钥也被用作认证凭证,可以访问私有数据。 接下来,开发者通常会用这些API密钥来扩展项目功能,比如加载地图、嵌入YouTube视频等。但当Gemini上线后,这些密钥突然具备了更高的权限,而开发者可能没有意识到这一点。 TruffleSecurity的研究人员警告说,攻击者可以利用这些暴露的密钥访问Gemini API服务中的私有数据,并进行付费调用,导致受害者账户产生巨额费用。这种情况已经持续了几年,直到最近才被发现。 Google在收到报告后采取了一些措施,比如检测和阻止泄露的API密钥访问Gemini,并通知开发者检查和轮换密钥。同时建议使用TruffleHog工具来检测暴露的密钥。 总结一下,文章的核心是Google API密钥的安全问题及其潜在风险。我需要将这些要点浓缩到100字以内,并且不使用“文章内容总结”之类的开头。 可能会这样组织语言:Google API密钥被嵌入客户端代码中用于服务如Maps等。研究人员发现近3000个暴露的密钥可被用于认证Gemini AI助手并访问私有数据。该问题因Gemini推出而出现,导致原本不敏感的API密钥具备更高权限。攻击者可利用这些密钥进行恶意活动并造成财务损失。Google已采取措施应对这一漏洞。 </think> Google API 密钥被嵌入客户端代码用于服务如 Maps 等。研究人员发现近 3,000 个暴露的密钥可用于认证 Gemini AI 助手并访问私有数据。该问题因 Gemini 推出而出现,导致原本不敏感的 API 密钥具备更高权限。攻击者可利用这些密钥进行恶意活动并造成财务损失。Google 已采取措施应对这一漏洞。 2026-2-26 21:0:19 Author: www.bleepingcomputer.com(查看原文) 阅读量:5 收藏

Google API keys for services like Maps embedded in accessible client-side code could be used to authenticate to the Gemini AI assistant and access private data.
Researchers found nearly 3,000 such keys while scanning internet pages from organizations in various sectors, and even from Google.
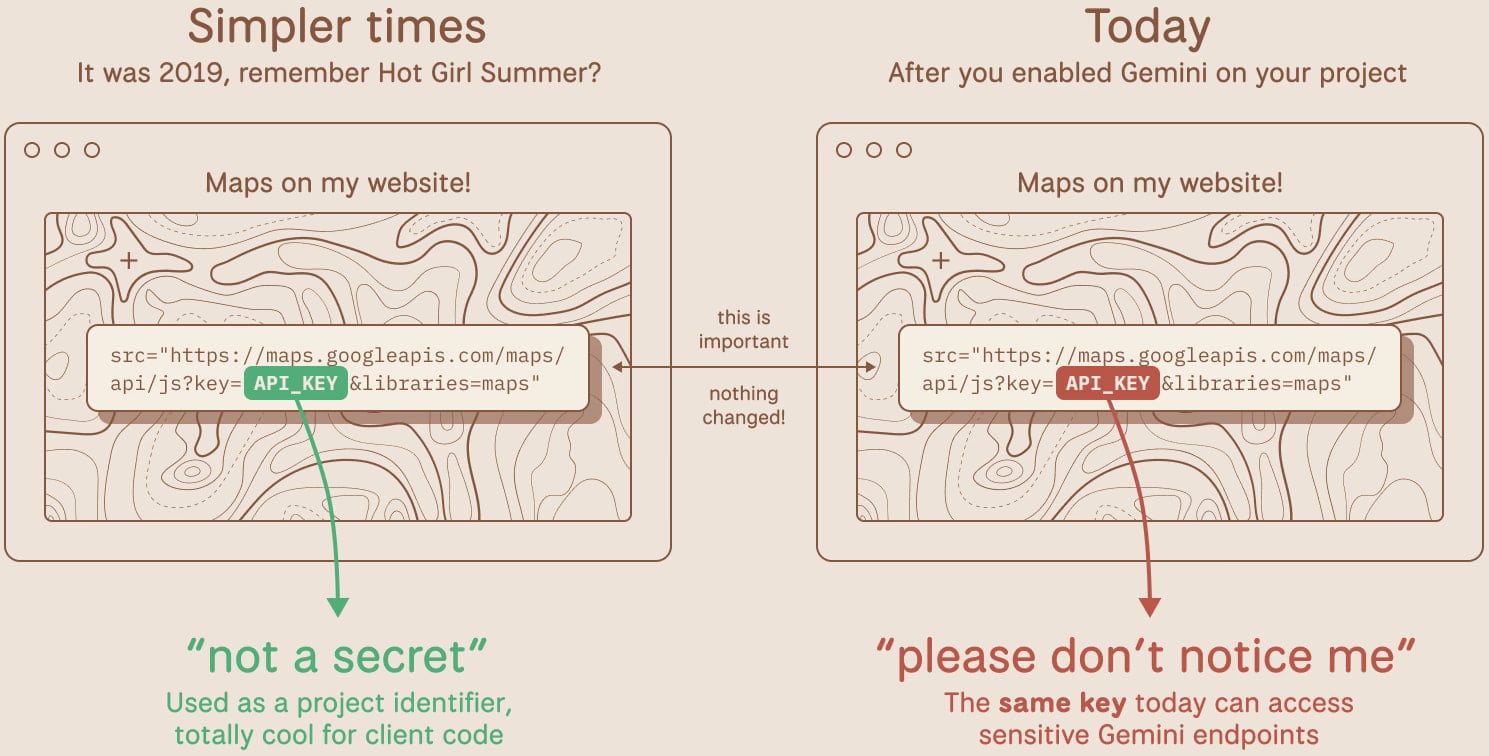
The problem occurred when Google introduced its Gemini assistant, and developers started enabling the LLM API in projects. Before this, Google Cloud API keys were not considered sensitive data and could be exposed online without risk.
Developers can use API keys to extend functionality in a project, such as loading Maps on a website to share a location, for YouTube embeds, usage tracking, or Firebase services.
When Gemini was introduced, Google Cloud API keys also acted as authentication credentials for Google's AI assistant.
Researchers at TruffleSecurity discovered the issue and warned that attackers could copy the API key from a website's page source and access private data available through the Gemini API service.
Since using the Gemini API is not free, an attacker could leverage the access and make API calls for their benefit.
"Depending on the model and context window, a threat actor maxing out API calls could generate thousands of dollars in charges per day on a single victim account," Truffle Security says.
The researchers warn that these API keys have been sitting exposed in public JavaScript code for years, and now they have suddenly gained more dangerous privileges without anyone noticing.
TruffleSecurity scanned the November 2025 Common Crawl dataset, a representative snapshot of a large swath of the most popular sites, and found more than 2,800 live Google API keys publicly exposed in their code.
According to the researchers, some of the keys were used by major financial institutions, security companies, and recruiting firms. They reported the problem to Google, providing samples from its infrastructure.
In one case, an API key acting just as an identifier was deployed since at least February 2023 and was embedded in the page source of a Google product's public-facing website.
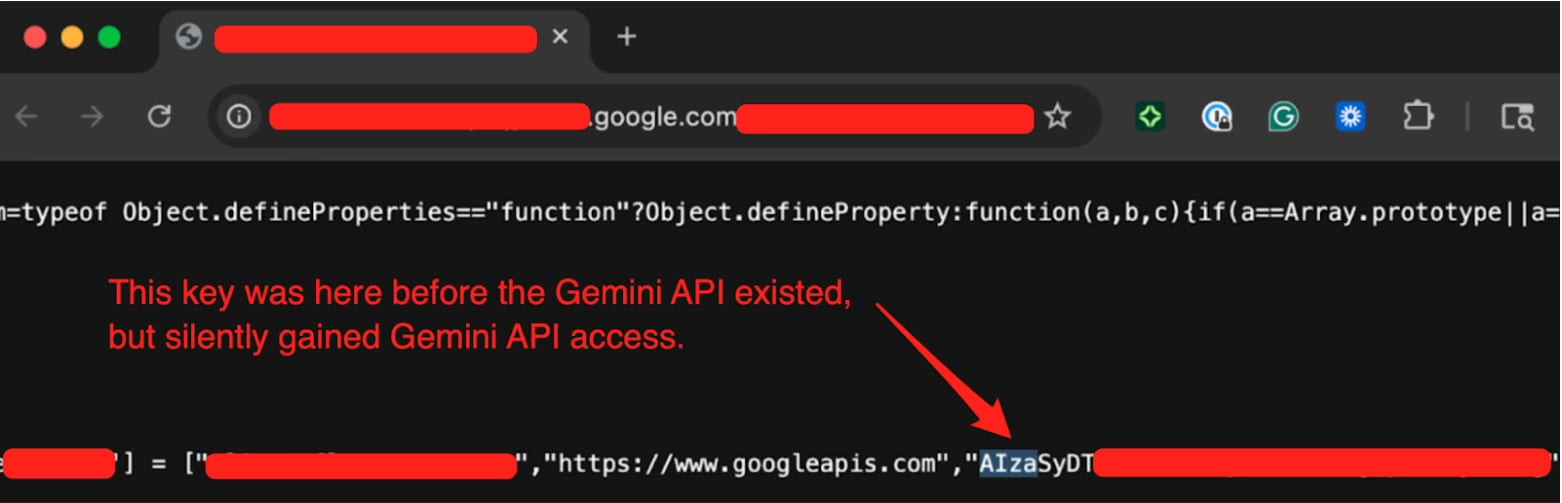
Source: TruffleSecurity
Truffle Security tested the key by calling the Gemini API's /models endpoint and listing available models.
The researchers informed Google of the problem last year on November 21. After a long exchange, Google classified the flaw as “single-service privilege escalation” on January 13, 2026.
In a statement for BleepingComputer, Google says that it is aware of the report and has "worked with the researchers to address the issue."
"We have already implemented proactive measures to detect and block leaked API keys that attempt to access the Gemini API,” a Google spokesperson told BleepingComputer.
Google stated that new AI Studio keys will default to Gemini-only scope, leaked API keys will be blocked from accessing Gemini, and proactive notifications will be sent when leaks are detected.
Developers should check whether Gemini (Generative Language API) is enabled on their projects and audit all API keys in their environment to determine if any are publicly exposed, and rotate them immediately.
The researchers also suggest using the TruffleHog open-source tool to detect live, exposed keys in code and repositories.
The future of IT infrastructure is here
Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide, learn how your team can reduce hidden manual delays, improve reliability through automated response, and build and scale intelligent workflows on top of tools you already use.
如有侵权请联系:admin#unsafe.sh

