The Conduent breach has quietly grown into one of the biggest third‑party data incidents in US history, and the real story now is how many different programs and employers are swept up in it, even for people who have never heard of Conduent.
When we first covered this incident, public filings suggested roughly 10.5 million affected individuals, heavily concentrated in Oregon and a few other states. Fresh state notifications reportedly put the total at more than 25 million people across the US, with Texas alone jumping from an early estimate of about 4 million to 15.4 million residents impacted, and Oregon holding at around 10.5 million.
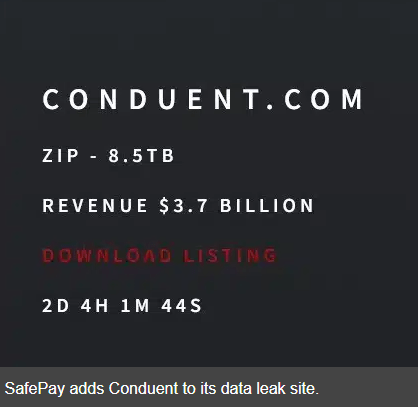
That makes this one of the largest healthcare‑related breaches on record, with attackers reportedly spending about three months in Conduent’s environment and exfiltrating around 8 TB of data.
How are so many people affected who have never heard of Conduent?
In 2019, Conduent said its systems supported services for more than 100 million people nationwide and served a majority of Fortune 100 companies plus more than 500 government entities. That shows just how broad the potential blast radius is, even if not all of those records were touched in this incident.
Conduent sits behind the scenes of a major portion of US public services and corporate back‑office work, which explains why the victim list looks so disconnected. Its platforms handle:
- State benefit programs such as Medicaid, SNAP (Supplemental Nutrition Assistance Program), and other government payment disbursements in more than 30 states.
- Mailroom, printing, and payment processing for state benefit offices and healthcare programs, including large health insurers like Blue Cross Blue Shield plans.
- Corporate services for major employers, including at least one large automotive manufacturer; nearly 17,000 Volvo Group employees are confirmed among those whose data was exposed.
Who stole what?
The cyberattack was later claimed by the SafePay ransomware gang.
The stolen data goes far beyond contact details. Notification letters and regulator filings describe:
- Full legal names, postal addresses, and dates of birth.
- Social Security numbers and other government identifiers.
- Medical information, health insurance details, and related claims data.
Because Conduent processes benefits and HR data on behalf of agencies and employers, most people affected never interacted with Conduent directly and may not even recognize the name on the envelope. If you received SNAP benefits, Medicaid coverage, other state‑administered healthcare, or worked for an organization that outsources HR or claims administration to Conduent (or one of its clients), your data may have flowed through its systems even though your “customer relationship” was with a state agency, insurer, or employer.
Why this is worse than it first looked
There are three reasons why this follow‑up story is more serious than the original:
- More people are involved: The raw numbers climbed from 10 million to 25 million as more states and corporate clients disclosed involvement, showing how opaque third‑party breaches can be at the start.
- Forever identifiers: SSNs plus medical and insurance data enable long‑tail identity theft, medical fraud, and highly targeted phishing that can haunt victims for years.
- Third-party blind spot: For many covered entities, “the breach” will never show up in their own logs because the compromise happened in a vendor’s environment they rely on but do not control.
So when an unexpected letter from Conduent arrives, it’s not a mistake. It’s a reminder that your data can be put at risk far away from the organizations you thought you were dealing with—and that the real exposure from this breach extends well beyond the numbers in any single state filing.
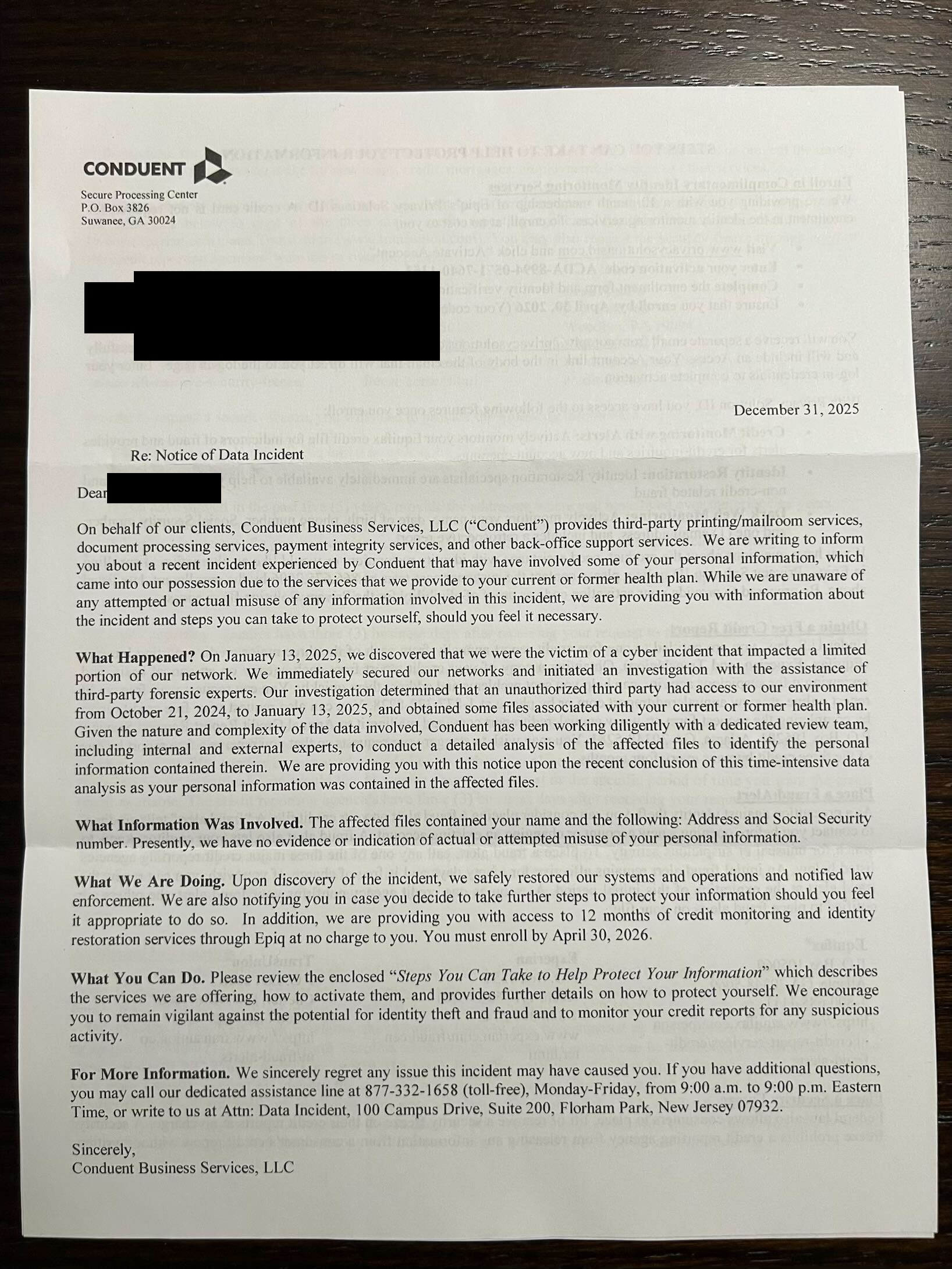
Depending on which of your data was compromised, you may receive a slightly different letter. If you receive one, you could read our guide on what to do after a data breach to understand your next steps.
We don’t just report on threats—we help safeguard your entire digital identity
Cybersecurity risks should never spread beyond a headline. Protect your, and your family’s, personal information by using identity protection.