
好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,抓住主要信息。 文章主要讲的是DarkCloud这个恶意软件,它在2026年的初始访问攻击中占据主导地位。DarkCloud由一个叫做“Darkcloud Coder”的开发者创建,价格很低,只需要30美元起。它通过窃取凭证来降低入侵门槛。 技术方面,DarkCloud使用了Visual Basic 6.0编写,编译成C/C++应用。这种旧的语言让它在检测上更隐蔽。它的功能包括跨浏览器、邮件客户端等窃取凭证和数据,并支持多种数据外发方式。 文章还提到DarkCloud的商业化运作,以及它如何通过伪装成监控软件来提供给买家一个合理的否认借口。此外,它还提到了防御建议,比如监控异常数据外发、审计凭证复用等。 总结时要涵盖:DarkCloud是什么、它的功能、技术特点、商业化运作以及威胁性。同时要控制在100字以内,避免使用总结性的开头语句。 现在开始组织语言:DarkCloud是一款低价、商业化的恶意软件,通过窃取凭证和数据进行攻击。它使用旧技术以逃避检测,并支持多种数据外发方式。伪装成监控软件使其广泛传播,成为企业网络威胁。 </think> DarkCloud是一款低价、商业化的恶意软件,通过窃取凭证和数据进行攻击。它利用旧技术以逃避检测,并支持多种数据外发方式。伪装成监控软件使其广泛传播,成为企业网络威胁。 2026-2-25 20:33:55 Author: flashpoint.io(查看原文) 阅读量:4 收藏
Infostealers continue to dominate the initial access landscape in 2026, lowering the barrier to breach through scalable credential theft. DarkCloud illustrates how low-cost, commercialized malware is reshaping the initial access landscape.
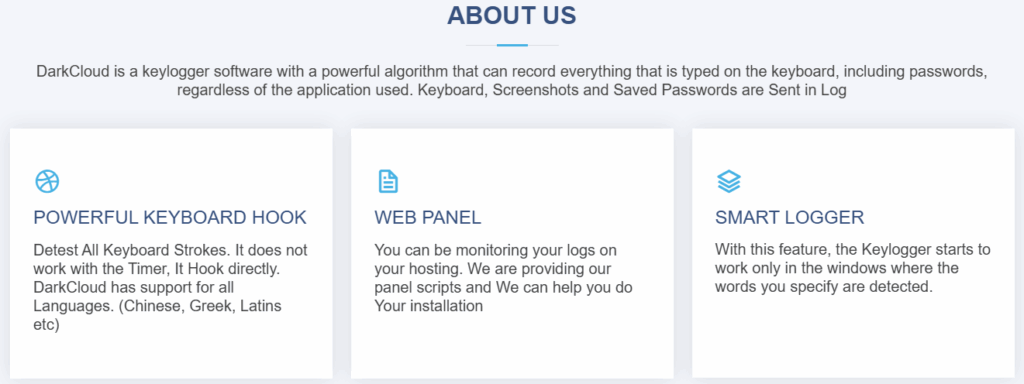
First observed in 2022 and attributed to a developer known as “Darkcloud Coder” (formerly “BluCoder” on Telegram), DarkCloud is openly sold through Telegram and a clearnet storefront with subscription tiers starting at just US$30. Despite being marketed as “surveillance software,” its technical focus is unmistakable: high-volume credential harvesting and structured data exfiltration across browsers, email clients, financial data, and contact networks.

At the technical level, DarkCloud is written in Visual Basic 6.0 and compiled into a native C/C++ application. This legacy language choice is unusual in modern malware development — and likely deliberate. By leveraging outdated but still supported runtime components, DarkCloud appears to benefit from lower detection rates while maintaining full credential theft functionality.
Despite its relatively low cost, DarkCloud should not be dismissed as unsophisticated. Flashpoint assesses it as a potent entry-level threat that can provide adversaries with the keys to an entire corporate network through harvested credentials.
The Commercialization of DarkCloud
DarkCloud represents a mature example of commodity malware-as-a-service.
It is openly sold through Telegram and a clearnet website, where it is misleadingly labeled as a keylogger. While it does include keylogging capabilities, this is only a minor component of a much broader infostealing toolkit.
Its real value proposition is credential harvesting across browsers, email clients, file transfer applications, VPN software, and more.
This dual positioning — public-facing “surveillance software” and underground stealer — provides plausible deniability while enabling large-scale credential operations.
Why Visual Basic 6.0 Matters
One of the most notable aspects of DarkCloud is its use of Visual Basic 6.0.
The payload is written in VB6 and compiled into a native C/C++ application. Microsoft no longer supports VB6 in its modern development environment, and VB6 applications rely on legacy components such as MSVBVM60.DLL for execution.
Flashpoint assesses this legacy language choice is deliberate, both for its simplicity and its potential to evade modern detection models.
In testing, Flashpoint analysts generated equivalent payloads in C/C++ and VB6. The VB6 variant produced significantly fewer detections in VirusTotal scans.
The implication is clear: older languages are not necessarily obsolete in adversary tradecraft. In some cases, they may be strategically advantageous.
Encryption and String Obfuscation
DarkCloud employs a layered string encryption scheme that complicates static and dynamic analysis.
Most internal strings are encrypted and decrypted at runtime using Visual Basic’s Rnd() pseudo-random number generator, combined with a custom seed-generation algorithm.
The process involves:
- Hex-encoded encrypted strings
- Base64-encoded keys
- Seed calculation through a custom algorithm
- Resetting the VB pseudo-random number generator to a known state
- Iterative Rnd() calls to reconstruct plaintext strings
By resetting the PRNG with a known value before applying the calculated seed, the malware ensures deterministic output during decryption.
This approach does not rely on novel cryptography, but rather on abusing legacy language behavior to frustrate reverse engineering.
Credential Theft at Scale
DarkCloud’s primary objective is credential collection.
It targets:
Email clients:
- Outlook
- eM Client
- FoxMail
- Thunderbird
- 163Mail
- MailMaster
File transfer applications:
- FileZilla
- WinSCP
- CoreFTP
Browsers:
- Google Chrome
- Microsoft Edge
- Mozilla Firefox
- Brave
- Opera
- Yandex
- Vivaldi
- (and many additional Chromium- and Firefox-based browsers)
Other applications:
- Pidgin
- NordVPN
When extracting browser data, DarkCloud steals:
- Login credentials
- Cookies
- Credit card information
Email applications are additionally scraped for contact lists. This is likely intended to seed future phishing campaigns.
DarkCloud stores collected data locally in two directories under %APPDATA%\Microsoft\Windows\Templates. One directory (“DBS”) stores copied database files, while another (“_”) stores parsed data in unencrypted text format.
This local staging enables continuous exfiltration while maintaining structured log output.
Exfiltration Methods: Flexibility for Threat Actors
DarkCloud supports four exfiltration methods:
- SMTP
- FTP
- Telegram
- HTTP
SMTP and FTP require hardcoded credentials within each binary. Email subjects include the victim machine’s hostname and username, and stolen data is transmitted as attachments.
HTTP exfiltration appears less frequently used, though the capability is present.
This flexibility allows operators to tailor deployments depending on infrastructure preferences and operational security requirements.
From BluStealer to DarkCloud
Flashpoint analysts identified notable similarities between DarkCloud’s regular expressions for credit card parsing and those found in a publicly documented project known as “A310LoggerStealer,” also referred to as BluStealer.
The regex patterns appear in identical order and format.
Combined with the developer’s prior alias “BluCoder,” Flashpoint assesses that A310LoggerStealer likely represents an earlier iteration of what became DarkCloud.
This evolution reflects a common pattern in commodity malware development: incremental refinement rather than radical innovation.
A Potent Entry-Level Threat
Despite its relatively low cost, DarkCloud should not be dismissed as unsophisticated.
Its marketing as surveillance software attempts to normalize its presence while providing plausible deniability for buyers. Technically, however, its focus is clear: large-scale credential harvesting across browsers, email clients, financial data, and contact networks.
Flashpoint assesses DarkCloud as a potent entry-level threat that can provide adversaries with the keys to an entire corporate network through harvested credentials.
In a landscape where identity is the new perimeter, even a US$30 subscription can be operationally devastating.
Defending Against Commodity Infostealers
Commodity infostealers like DarkCloud may be commercially accessible, but defending against them requires enterprise-grade vigilance.
Organizations should:
- Treat phishing-delivered ZIP/RAR attachments as high-risk initial access vectors
- Monitor for abnormal data exfiltration over SMTP, FTP, and Telegram
- Audit credential reuse across browser and email applications
- Prioritize credential rotation and incident response playbooks following suspected compromise
Infostealers like DarkCloud are not breakthrough malware families. They do not rely on zero-days or advanced exploits.
Instead, they exploit scale, accessibility, and identity exposure.
To understand how credential harvesting campaigns are evolving and to embed real-time intelligence into your detection workflows, request a demo today and see how Flashpoint intelligence strengthens your defense posture.
如有侵权请联系:admin#unsafe.sh