嗯,用户让我总结一篇文章的内容,控制在一百个字以内,而且不需要特定的开头。我得先仔细阅读文章,抓住主要信息。 文章讲的是Google、Mandiant和其他合作伙伴破坏了一个全球间谍活动,怀疑是中国的威胁行为者。他们利用SaaS API隐藏恶意流量,攻击电信和政府网络。活动从2023年开始,影响了42个国家的53个组织,可能还有更多国家被感染。 攻击者使用了一个新的后门GRIDTIDE,滥用Google Sheets API进行命令控制。GRIDTIDE通过硬编码的私钥访问Google服务账户,并在表格中进行操作。Google和其他公司采取行动终止了攻击者的云项目和API访问。 总结时要包括主要事件、参与者、攻击手段、影响范围以及应对措施。控制在100字以内,所以需要简洁明了。 </think> Google与Mandiant等合作方破坏了一起针对电信和政府网络的全球间谍活动,该活动由疑似中国威胁行为者实施,利用SaaS API隐藏恶意流量。攻击影响42国53组织,并部署名为GRIDTIDE的新后门滥用Google Sheets API进行隐蔽C2通信。 2026-2-25 17:0:29 Author: www.bleepingcomputer.com(查看原文) 阅读量:6 收藏

Google’s Threat Intelligence Group (GTIG), Mandiant, and partners disrupted a global espionage campaign attributed to a suspected Chinese threat actor that used SaaS API calls to hide malicious traffic in attacks targeting telecom and government networks.
The campaign has been active since at least 2023 and has impacted 53 organizations in 42 countries, with suspected infections in at least 20 more countries.
The initial access vector is unknown, but the researchers note that the threat actor, which Google tracks internally as UNC2814, has previously gained access by exploiting flaws in web servers and edge systems.
.jpg)
Source: Google
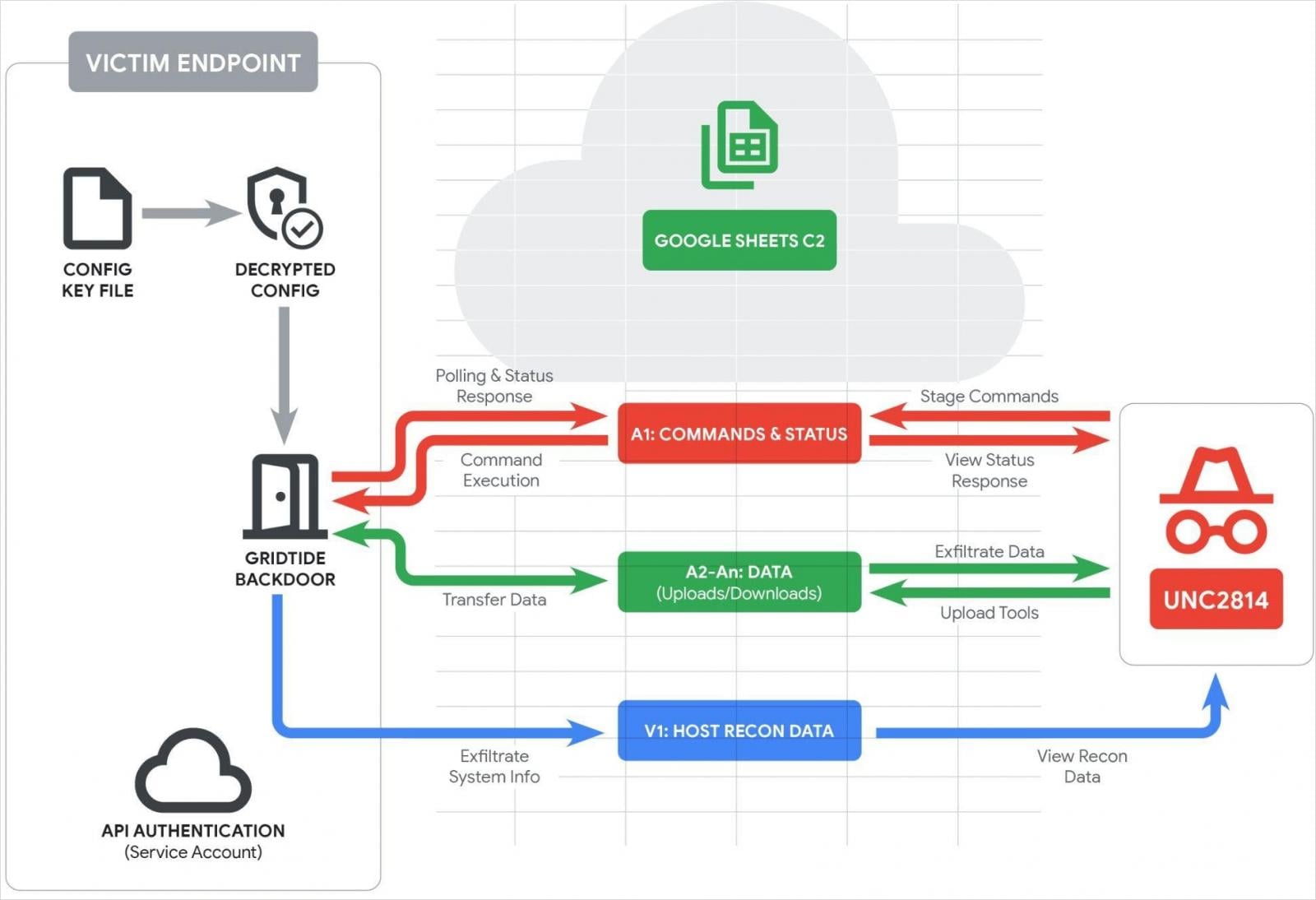
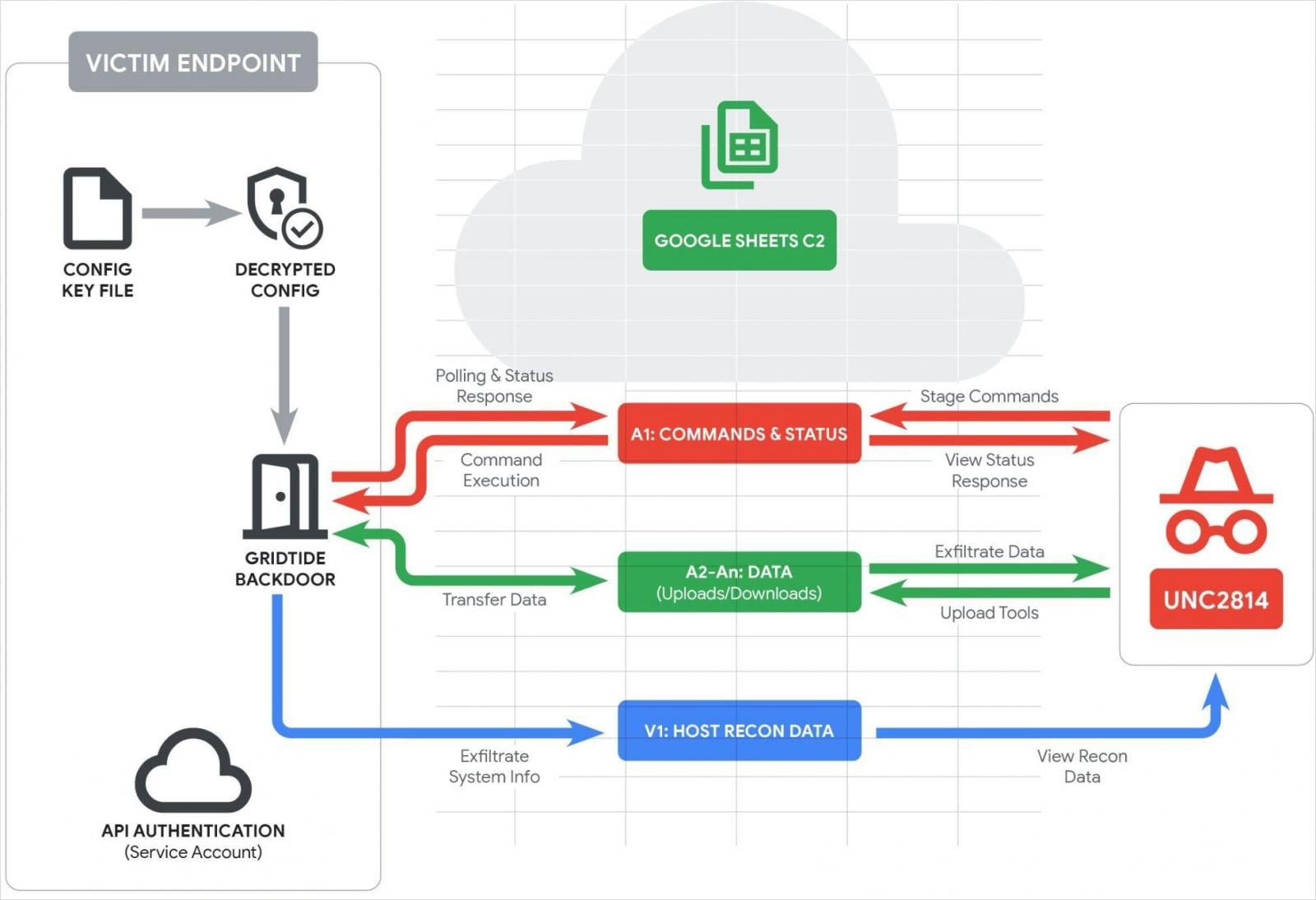
Google says that in the recently disrupted campaign, the actor deployed a new C-based backdoor named ‘GRIDTIDE,’ which abuses the Google Sheets API for evasive command-and-control (C2) operations.
GRIDTIDE authenticates to a Google Service Account using a hardcoded private key, and upon launch, it sanitizes the spreadsheet by deleting rows 1-1000 and columns from A to Z.
It then performs host reconnaissance, collecting the username, hostname, OS details, local IP, locale, and timezone, and logging the data in cell V1.
The first cell in the spreadsheet, A1, is the command/status cell, which GRIDTIDE polls constantly to receive instructions.
If any exist, the malware overwrites them with a status string. If empty, the malware retries every second for 120 times, then switches to random 5-10-minute checks to reduce noise.
The commands supported by GRIDTIDE are:
- C – execute Base64-encoded bash commands, write output to the sheet
- U – upload: take data in A2:A<arg_2> and reconstruct/write file at encoded filepath <arg_1>
- D – download: read local file <arg_1> on endpoint, send contents in ~45 KB fragments into A2:An
The A2-An cells are used for writing the command output, exfiltrated files, and uploading tools.
Google reports that GRIDTIDE’s exchanges with the C2 rely on a URL-safe base64 encoding scheme that evades detection by web monitoring tools and blends with normal traffic.
Source: Google
In at least one case, Google confirmed that GRIDTIDE was deployed on a system that contained sensitive personally identifiable information (PII). However, the researchers did not directly observe data exfiltration.
Google, Mandiant, and partners took coordinated action to disrupt the campaign by terminating all Google Cloud projects controlled by UNC2814, disabling known infrastructure, revoking Google Sheets API access, and disabling all cloud projects used in C2 operations. Current and historical domains were sinkholed.
Organizations impacted by GRIDTIDE were notified directly, and support was offered to clean the infections.
Google has listed detection rules at the bottom of the report, as well as indicators of compromise (IoCs).
Even though the disruption to the campaign was comprehensive, Google expects UNC2814 to resume activity using new infrastructure in the near future.
The future of IT infrastructure is here
Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide, learn how your team can reduce hidden manual delays, improve reliability through automated response, and build and scale intelligent workflows on top of tools you already use.
如有侵权请联系:admin#unsafe.sh

