嗯,用户让我总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我需要快速浏览文章内容,抓住主要信息。 文章讲的是OpenClaw,一个AI自动化框架,最初是开发者为了方便自己和他人而开发的。它允许用户通过插件管理邮件、日程等任务。但后来它引发了关于AI热潮和网络安全的讨论。 文章提到OpenClaw从一个小众项目变成了安全研究和地下论坛的话题。虽然有很多讨论,但实际的大规模攻击还没出现。主要风险是供应链攻击,恶意插件可能窃取凭证或执行恶意代码。 总结的时候要涵盖这些点:OpenClaw的功能、引发的讨论、安全风险以及当前状态。确保在100字以内,语言简洁明了。 </think> OpenClaw 是一个 AI 驱动的自动化框架,允许用户通过插件管理邮件、日程和系统任务。尽管其初衷是简化工作流程,但其快速发展引发了关于 AI 潮流和网络安全的广泛讨论。尽管地下论坛中对其关注较高,但目前尚未形成大规模犯罪利用。主要风险在于供应链攻击和恶意插件可能导致凭证窃取和权限滥用。 2026-2-25 15:15:17 Author: www.bleepingcomputer.com(查看原文) 阅读量:9 收藏
OpenClaw started as a side project of a developer who wanted to make his (and others) life easier with AI assistance. Clean mailbox, control schedule, organize thoughts and hear some music while his bot is doing all the dirty jobs for him.
With vibe coding Peter Steinberger developed OpenClaw. Kudus for that. But since then apart from changing its name twice it created a massive chatter around two topics. The AI hype and its cyber security implications.
This project has rapidly moved from a niche automation framework discussed in developer communities to a topic appearing across security research feeds, Telegram channels, forums, and underground-adjacent chatter. Alongside it, names like ClawDBot and MoltBot have appeared in the same narrative space, often framed as malicious derivatives, companion tooling, or botnet-like ecosystems.
However, when Flare looked at aggregated telemetry across open sources, social platforms, and fringe underground discussions, a more nuanced story emerges.
The data suggests a real supply-chain security risk, but one that has not yet been fully weaponized into a mass-exploitation ecosystem. Instead, the conversation appears largely driven by security research amplification, platform hype cycles, and early-stage experimentation.
What OpenClaw Is: AI Automation Framework With Plugin Marketplace
OpenClaw is an AI-powered automation framework that allows users to manage emails, schedules, and system tasks through modular "skills"—user-installable plugins that execute commands on behalf of users.
The platform architecture includes:
- Local or remote agent nodes that run automation tasks
- A skills marketplace (ClawHub) where users download plugins
- API integrations for external services (SSH, cloud platforms, productivity tools)
- Centralized orchestration through gateway components
Conceptually, OpenClaw behaves less like a single application and more like a lightweight automation operating environment. That architectural model is powerful and also creates a large attack surface.
The moment execution logic becomes modular and user-installable, the platform inherits the same risks historically seen in:
- Browser extension ecosystems
- Package managers (npm, PyPI, RubyGems)
- IDE plugin stores
- CI/CD automation marketplaces
OpenClaw's skills ecosystem is where most of the real security discussion currently lives.
This project has rapidly moved from a niche automation framework discussed in developer communities to a topic appearing across security research feeds, Telegram channels, forums, and underground-adjacent chatter.
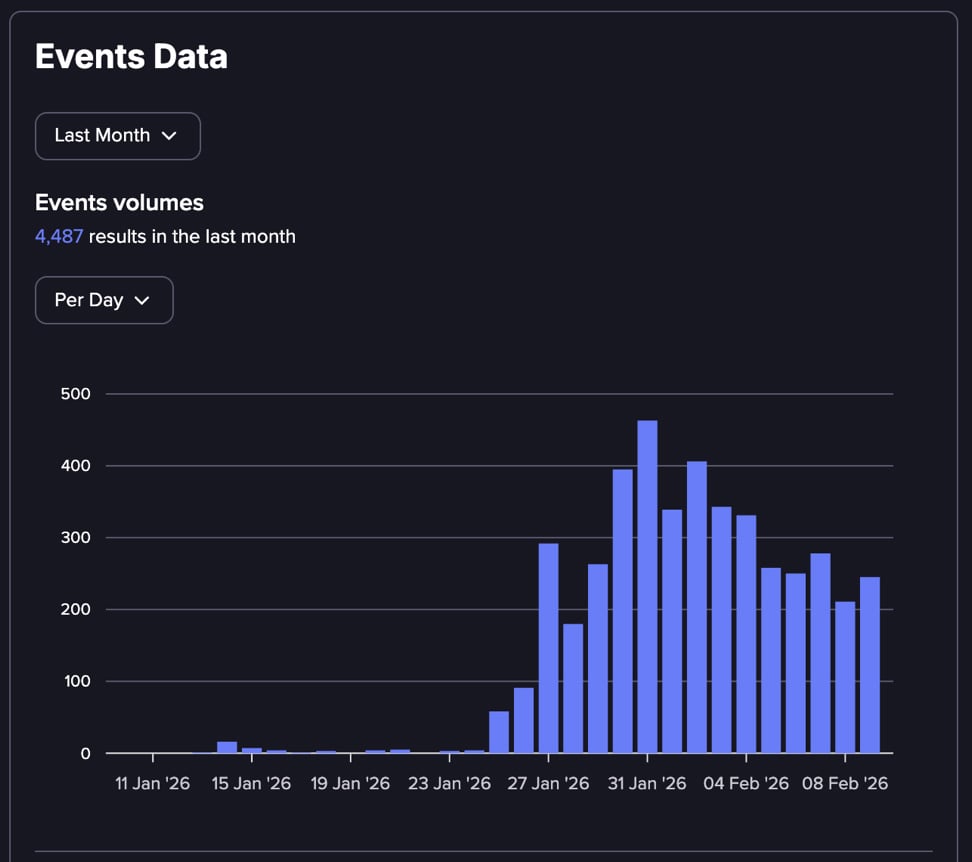
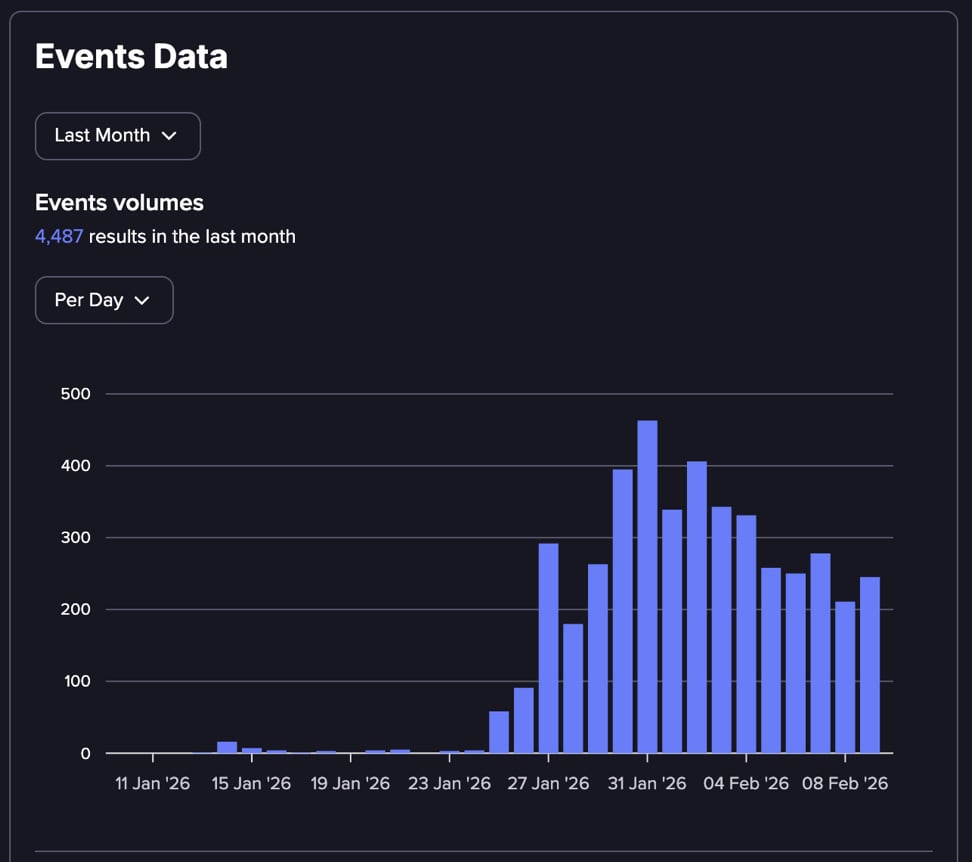
Clawdbot (the original name) was released in November 2025, but the real hype began during January 2026, as reflected in Flare's threat monitoring platform:
Alongside it, names like ClawdBot and MoltBot have appeared in the same narrative space, often framed as malicious derivatives, companion tooling, or botnet-like ecosystems.
However, when examining aggregated telemetry across open sources, social platforms, and underground discussions, a more nuanced story emerges. The data suggests a real supply-chain security risk, but not yet a fully weaponized, mass-exploitation ecosystem. Instead, the conversation appears largely driven by security research amplification, platform hype cycles, and early-stage experimentation.
Critical Security Flaws Enable Remote Code Execution and Credential Theft
Security researchers identified multiple critical vulnerabilities that made OpenClaw an attractive target for supply chain attacks:
Confirmed Critical Vulnerabilities:
CVE-2026-25253 (One-click RCE): Malicious links can steal authentication tokens and trigger remote code execution without requiring skill installation—attackers can compromise systems through a single click.
Malicious Skill Supply Chain: Hundreds of poisoned skills uploaded to ClawHub delivering infostealers, remote access trojans (RATs), and backdoors disguised as legitimate automation tools.
No Skill Sandboxing: Skills execute with full agent and system permissions, allowing malware to access credentials, files, and network resources without restriction.
Prompt Injection Attacks: Malicious content can manipulate AI agents into executing attacker-controlled workflows through natural language commands, bypassing traditional software vulnerabilities.
Token and OAuth Abuse: Attackers leverage stolen or inherited authentication tokens to trigger legitimate API actions, making malicious activity appear authorized.
Common Deployment Misconfigurations:
-
Agents running with root or excessive system privileges
-
Publicly exposed OpenClaw instances with weak authentication
-
Skills dynamically pulling and executing remote code
-
Shadow deployments operating outside security team visibility
Emerging Attack Patterns:
-
Credential-stealing skills
-
Instruction/reasoning hijacking
-
Multi-stage kill chains
Once executed, these malicious skills harvest credentials, session cookies, and sensitive data from the compromised system, packaging them into stealer logs distributed through underground markets.
Underground Forums Show Limited Exploitation Despite High Discussion Volume
Flare's analysis of underground discussions reveals an emerging threat landscape that hasn't yet reached mass criminal operationalization:
Dataset Analysis
Across 2,764 collected records from underground forums and Telegram channels:
-
OpenClaw mentions: 3,072
-
ClawDBot mentions: 1,365
-
MoltBot mentions: 864
-
ClawHub marketplace references: 90
However, breaking down the discussion types shows:
-
Skills security discussions: 193 mentions
-
ClawHub ecosystem references: 110 mentions
-
Infostealer references: 53 mentions
-
Botnet orchestration: 8 mentions
-
DDoS infrastructure: 7 mentions
What This Distribution Reveals
If OpenClaw were already weaponized at scale for mass exploitation, underground forums would typically show:
-
Active tool sales and access broker offerings
-
Botnet panel discussions and leaked administration interfaces
-
Established monetization threads with pricing structures
-
Commercial exploitation services
Instead, the conversation consists primarily of:
-
Security research reports and technical analysis
-
Platform risk speculation and proof-of-concept discussions
-
Early-stage experimentation without commercial operations
-
Tool confusion across different communities (ClawDBot vs MoltBot naming)
This supply chain poisoning approach mirrors tactics seen in traditional infostealer distribution campaigns, where attackers disguise malware as legitimate software to compromise user systems at scale.
The One Area That Is Real: Supply Chain Skill Abuse
The strongest confirmed risk pattern currently visible is:
-
Malicious skill distribution.
-
Execution inside trusted automation context.
-
Payload run - Credential / session / data exfiltration.
This is enough to be dangerous, even without botnet-scale weaponization.
Automation frameworks collapse the distance between initial access and privileged execution. If a malicious skill lands inside a trusted agent, the attacker effectively inherits the permissions of the automation environment.
Why Security Researchers Are Driving the Conversation
The most likely explanation for the current OpenClaw hype cycle is timing. OpenClaw sits at the intersection of three major trends:
-
Agentic automation platforms
-
Plugin marketplace trust models
-
AI-assisted workflow execution
Security researchers tend to detect these risks early, before criminal ecosystems fully monetize them.
Conclusion: High Risk Potential, Early Exploitation Stage
The combined dataset suggests that OpenClaw is not currently showing signs of mass criminal operationalization at scale.
Instead, what we see is:
-
A real supply-chain risk surface (skills ecosystem)
-
Heavy research-driven discussion volume
-
Early experimentation and PoC-level malicious capability
-
Strong narrative amplification across social and fringe underground channels
The security community is talking about OpenClaw more than threat actors are currently exploiting it. Having said that, this is not a reason to ignore it. Historically, this phase often precedes real weaponization by weeks or months.
The lesson from OpenClaw is less about one framework and more about a broader shift.
Automation platforms with plugin ecosystems are becoming high-value targets long before organizations realize they have deployed them at scale.
Learn more by signing up for our free trial.
Sponsored and written by Flare.
如有侵权请联系:admin#unsafe.sh