好的,我现在需要帮用户总结一篇文章,控制在100字以内。用户的要求是直接写文章描述,不需要特定的开头。 首先,我快速浏览文章内容。文章主要讲的是 Lazarus APT 组织使用 Medusa 勒索软件攻击中东的一个目标。Lazarus 是朝鲜支持的黑客组织,之前也参与过其他勒索软件活动。这次攻击还涉及美国的医疗机构,但没有成功。 接下来,我需要提取关键信息:Lazarus 部署 Medusa 攻击中东组织,Medusa 是勒索软件即服务,由 Spearwing 运营,涉及多起攻击。此外,Lazarus 还试图攻击美国的医疗机构但未成功。 然后,我要把这些信息浓缩到100字以内。确保涵盖主要事件、组织名称、攻击目标以及相关背景。 最后,检查语言是否简洁明了,没有多余的信息。确保总结准确传达文章的核心内容。 </think> 朝鲜支持的Lazarus APT组织使用Medusa勒索软件攻击中东一家未具名机构,并试图入侵美国医疗机构但未成功。Medusa由Spearwing运营,已关联366起攻击。Lazarus近年来转向勒索软件活动以资助间谍活动。 2026-2-25 08:18:36 Author: securityaffairs.com(查看原文) 阅读量:20 收藏
Lazarus APT group deployed Medusa Ransomware against Middle East target
Pierluigi Paganini
February 25, 2026

North Korea’s Lazarus Group used Medusa ransomware in an attack on an unnamed Middle East organization, researchers report.
The North Korea-linked Lazarus APT Group, also known as Diamond Sleet and Pompilus, has been spotted deploying Medusa ransomware against an unnamed organization in the Middle East, according a new report from the Symantec and Carbon Black Threat Hunter Team.
“North Korea has long been involved in ransomware attacks and has been previously associated with the Maui and Play ransomware families. However, the Symantec and Carbon Black Threat Hunter Team has uncovered evidence North Korean actors using Medusa in an attack on a target in the Middle East.” reads the report published by Symantec and Carbon Black Threat Hunter Team. “The same attackers also mounted an unsuccessful attack against a healthcare organization in the U.S.”
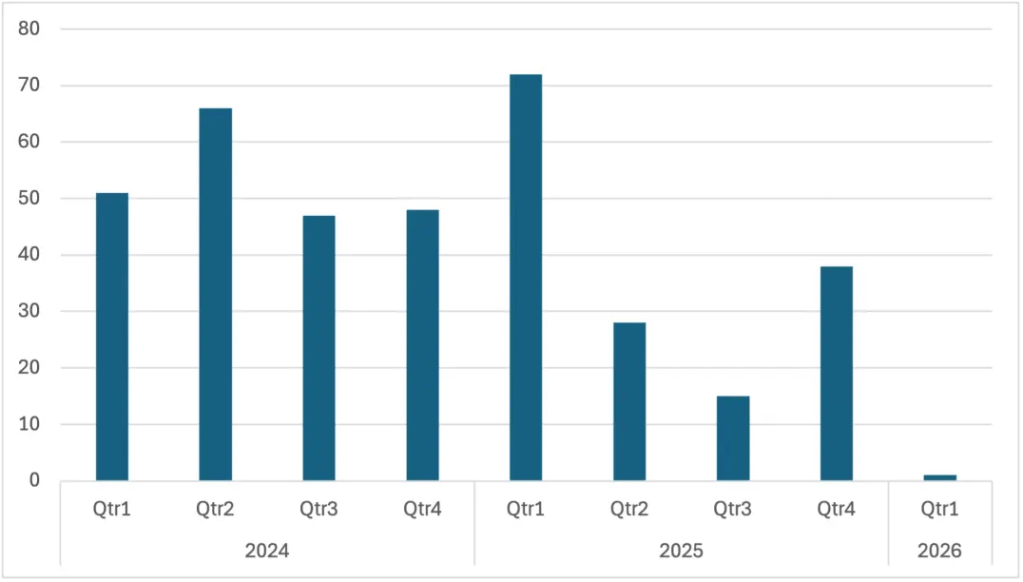
Medusa, a ransomware-as-a-service launched in 2023 and operated by the Spearwing group, allows affiliates to deploy the malware in exchange for a share of ransom payments. It has been linked to over 366 claimed attacks. Since early November 2025, its leak site has listed four U.S. healthcare and non-profit victims, including a mental health nonprofit and a school for autistic children. Average ransom demands reached $260,000.
North Korea’s Lazarus subgroup Stonefly (aka Andariel) has shifted from traditional espionage to ransomware-driven extortion in recent years. Its role became public in July 2025, when U.S. authorities indicted alleged member Rim Jong Hyok over attacks on American hospitals. Prosecutors said ransomware proceeds funded espionage targeting defense, tech, and government sectors in the U.S., Taiwan, and South Korea. Despite charges and a $10 million reward, activity continued, including financially motivated intrusions in 2024 and reported collaboration with the Play ransomware group.
In current campaigns, Lazarus deploys tools such as Comebacker, Blindingcan, ChromeStealer, Mimikatz, and other custom malware. While the Medusa attacks are attributed to Lazarus, it remains unclear which subgroup is responsible, as the toolset overlaps with groups like Pompilus.
“The switch to Medusa demonstrates that North Korea’s rapacious involvement in cybercrime continues unabated.” concludes the report that provides Indicators of Compromise (IoCs). “North Korean actors appear to have few scruples about targeting organizations in the U.S. While some cybercrime outfits claim to steer clear of targeting healthcare organizations due to the reputational damage it may attract, Lazaurs doesn’t seem to be in any way constrained.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Lazarus Group)
如有侵权请联系:admin#unsafe.sh
