
好的,我现在需要帮用户总结一篇文章,控制在100字以内。首先,我得仔细阅读文章内容,抓住关键点。 文章主要讲的是一个叫做1Campaign的网络犯罪服务。它能让攻击者运行恶意的Google广告,并且这些广告能长时间在线而不被安全研究人员发现。这个服务还能隐藏恶意内容,只显示给潜在受害者,而研究人员和扫描器看到的是正常的页面。 接着,文章提到这个服务已经运营了至少三年,由一个叫DuppyMeister的人管理。它提供了一个用户友好的仪表盘,让攻击者可以监控和设置他们的活动。此外,1Campaign还能根据地理位置、ISP和设备特征来过滤访问者,只让目标地区的用户看到恶意内容。 还有,系统会给每个访问者分配一个欺诈风险评分,评分高的会被自动拦截。比如来自微软、谷歌等云服务提供商的访问者会被标记为高风险并阻止访问。 最后,文章建议用户不要轻易点击推广链接,并检查URL确保安全。 现在我需要把这些信息浓缩到100字以内。重点包括:1Campaign是什么、它的功能(隐藏恶意内容、过滤访问者)、开发者是谁、运营时间以及对用户的建议。 可能的结构是:介绍服务名称和功能,说明其如何隐藏恶意内容,开发者和运营时间,以及对用户的建议。 现在试着组织语言: “1Campaign是一个网络犯罪服务,允许攻击者运行长时间在线的恶意Google广告,并隐藏内容仅显示给潜在受害者。该服务由DuppyMeister管理,已运营至少三年,并提供仪表盘和过滤工具以避开安全检测。” 这样大约在70字左右,符合要求。 </think> 1Campaign是一个网络犯罪服务,允许攻击者运行长时间在线的恶意Google广告,并隐藏内容仅显示给潜在受害者。该服务由DuppyMeister管理,已运营至少三年,并提供仪表盘和过滤工具以避开安全检测。 2026-2-24 21:45:17 Author: www.bleepingcomputer.com(查看原文) 阅读量:4 收藏

A newly identified cybercrime service known as 1Campaign is enabling threat actors to run malicious Google Ads that remain online for extended periods while evading scrutiny from security researchers.
1Campaign is a cloaking service that passes Google’s screening process and shows malicious content only to real potential victims. Security researchers and automated scanners are served benign white pages.
The operation has been active for at least three years and is managed by a developer using the name ‘DuppyMeister,’ according to a report from data security company Varonis.
“The tool passes Google's screening, filters out security researchers, and keeps phishing and crypto drainer pages online for as long as possible, funneling real users to attacker-controlled sites,” the researchers say.
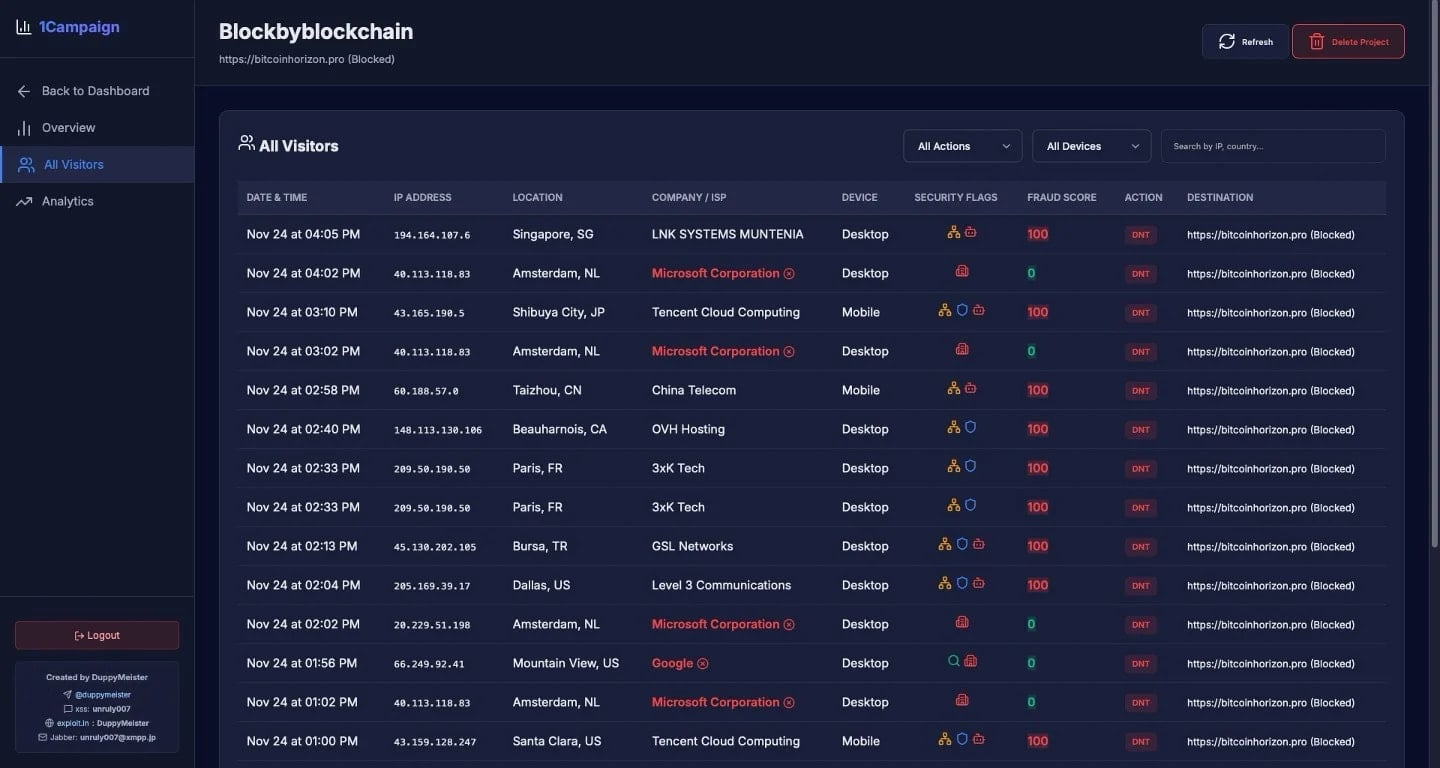
1Campaign provides “customers” with a user-friendly dashboard where they can get an overview of their operations and set the parameters for their campaigns.

Source: Varonis
The platform can filter visitors in real time, directing traffic to landing pages based on predefined criteria, including geography, internet service provider (ISP), and device characteristics.
The researchers say that this targeted approach allows attackers to concentrate on users in regions where the phishing lure is relevant, while filtering out traffic from countries with a higher likelihood of security scrutiny or scanning activity.
In one instance, Varonis observed aggressive filtering that blocked 99.4% of 1,676 visitors accessing the malicious ads. This translates into a success rate of just 0.6%, or 10 visitors.
Source: Varonis
The system evaluates each visitor and assigns a fraud risk score between 0 and 100. This reflects the likelihood of non-genuine visitors, and is derived from checking infrastructure details such as cloud providers, data centers, VPNs, and security vendors.
"Visitors from Microsoft Corporation, Google, Tencent Cloud Computing, OVH Hosting, and other cloud providers are automatically flagged with high fraud scores and blocked," Varonis says in a report today.
Based on IP address ranges, ISP, and behavioral patterns, the system can also determine if the malicious ads are accessed by security scanners.
Varonis has observed traffic linked to 1Campaign being distributed in the United States, Canada, the Netherlands, China, Germany, France, Japan, Hungary, and Albania.
The cybercrime platform also offers a Google Ads launcher tool that helps operators launch both malicious and benign campaigns. The developer claims that this tool enables bypassing Google’s policy limitations and impersonating legitimate brands in ads.
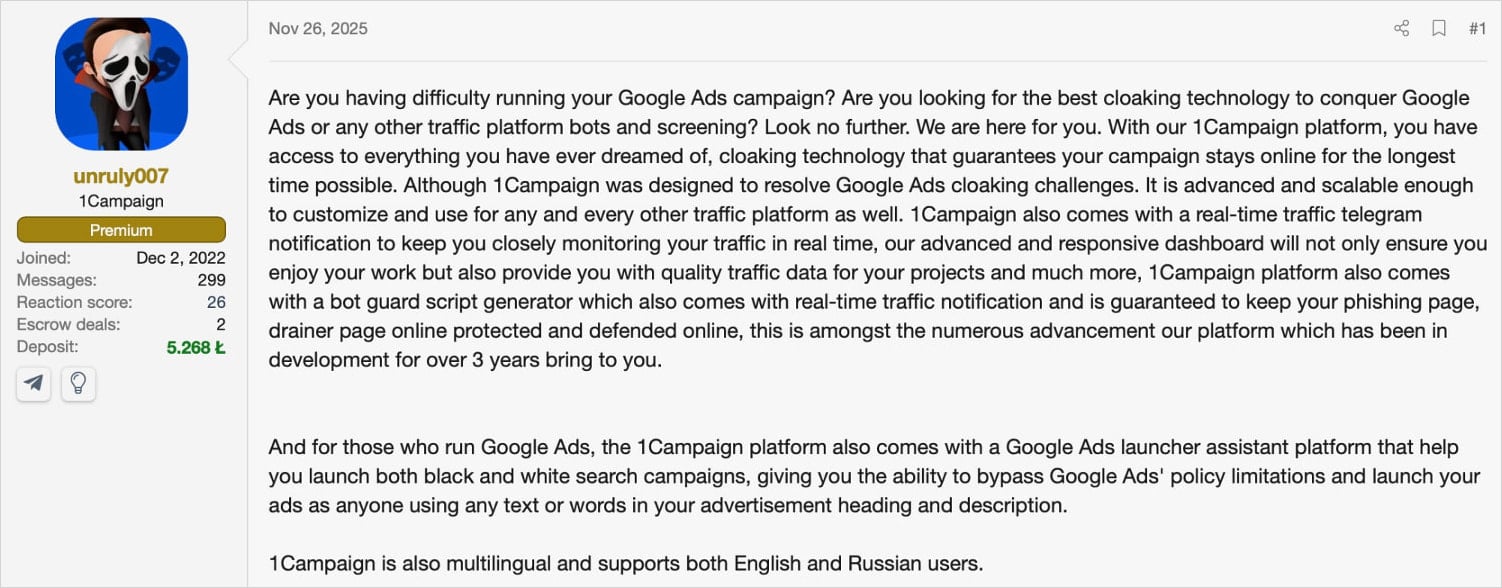
Despite Google introducing multiple safeguards, its ad platform is still used to promote fraud, malware, and crypto-drainers. 1Campaign stands out, though, as it is designed specifically to launch malicious ads that pass Google's automatic inspection and likely survive until victims report them or the campaign is reported manually.
Such a cloaking system makes static URL scanning less effective. Varonis says that using realistic browser fingerprints and patterns that mimic human interaction would render better analysis and detection results.
For automated detection, Varonis recommends rotating through a diverse IP pool and user-agent configurations to avoid consistent fingerprinting.
Users are advised to avoid promoted search results, or at least treat them with suspicion, and bookmark official software distribution channels.
Double-checking the URL in the address bar is also recommended before entering account credentials or other sensitive information.
The future of IT infrastructure is here
Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide, learn how your team can reduce hidden manual delays, improve reliability through automated response, and build and scale intelligent workflows on top of tools you already use.
如有侵权请联系:admin#unsafe.sh

